Peoplethrowdid.top ads (Free Instructions)
Peoplethrowdid.top ads Removal Guide
What is Peoplethrowdid.top ads?
Peoplethrowdid.top is a rogue website that tries to deceive visitors by showing them misleading messages

Peoplethrowdid.top is a browser-based scam that some users might encounter abruptly while browsing the internet on Google Chrome, Mozilla Firefox, MS Edge, or any other web browser. This is usually a result of a redirect after clicking a booby-trapped link on a high-risk website, as well as a malicious script that could be hiding anywhere.
Upon entry, users can be shown a variety of different misleading and entirely fake messages, which seek to trick users into performing actions that would benefit the scam authors. For example, a commonly used “You've made the 9.68-billionth search” scam implies that Google has selected a user to receive a “thank you gift” due to alleged pure luck. This is a very common technique used by phishing attempts, where users are promised an expensive gift for free.
If you have accidentally entered Peoplethrowdid.top scam site, you should immediately leave it and not interact with buttons and not download any software. Simply keep in mind that, whatever is said there, is all fake. Nonetheless, users who are commonly redirected to misleading websites and encounter ads everywhere could also be potentially affected by adware – a type of potentially unwanted program.[1] Thus, we will provide information on how to deal with the scam and PUPs in several sections below.
| Name | Peoplethrowdid.top |
|---|---|
| Type | Scam, phishing, adware, redirect |
| Goal | Make people provide personal information, subscribe to useless services, download malicious software or subscribe to push notifications |
| Distribution | Redirects from other malicious websites, adware |
| Dangers | Those who have malicious software installed on their systems are more likely to encounter dangerous websites, resulting in financial losses, malware infections, etc. |
| Removal | To remove unwanted apps manually, you can follow our removal guide below. If the unwanted ads and other disruptive behavior does not stop, you should scan your computer with SpyHunter 5Combo Cleaner security software and delete all threats automatically |
| Other tips | Cleaning web browsers is one of the secondary things you should do after PUP/malware removal to secure your privacy. You can use FortectIntego to do it quickly |
As we already mentioned, users might encounter the Peoplethrowdid.top site completely accidentally, although the risk of that increases when insecure websites are being visited. For example, illegal video streaming websites are known to incorporate various fake “Download” and “Play” buttons, which redirect users to malicious websites when clicked. The same issue plagues torrents, gambling, X-rated, and similar high-risk sites.
Therefore, we strongly recommend staying away from torrents, software cracks, and similar dangerous websites. Not only can they lead to redirects to phishing messages, but they might also host malware such as Jjtt ransomware.
Once on the page, users might be surprised by the initial message, as they could be told that they have won an expensive item such as the newest iPhone, and all they have to do is fill in some information in order to retrieve it. The main goal of such scams is to extort sensitive user data, such as a home address, email, or even credit card details. All this information can later be sold to cybercriminals or monetized in other ways.
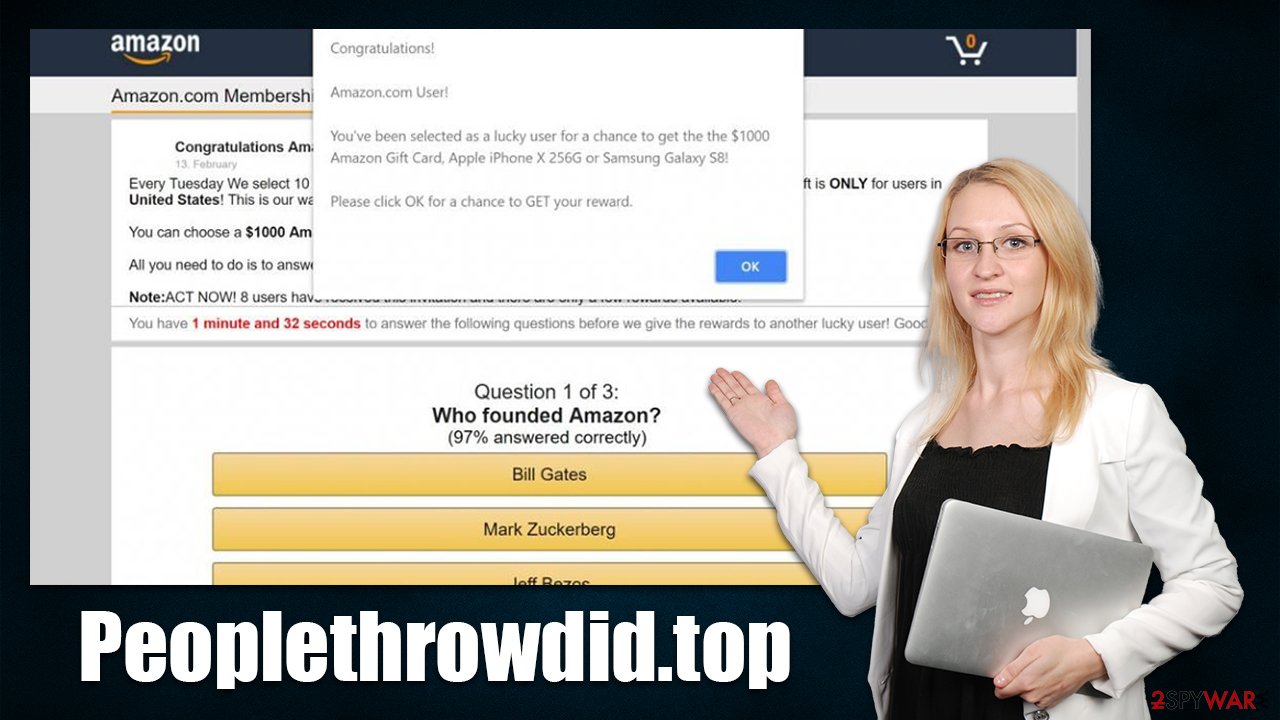
When dealing with a questionable message, always check the URL address of the page that displays it. For example, if you are told by seemingly Microsoft that your system is infected by a virus and a Windows error code is shown, it becomes clear that the message is fake as soon as you look at the web address. Only trust official websites whenever you see claims from seemingly trustworthy companies such as Amazon, Google, Apple, etc.
What to do after encountering the Peoplethrowdid.top scam
Generally speaking, accessing a website that shows a misleading or fake message does not result in a computer being automatically infected. The more significant part is the way users act once they land on such a page. For example, if the scam message asked people to enter their password or create a new “account,” they might be exposing it to potentially dangerous parties.
In such a case, it is vital to change your password on all the accounts it was used. If you have provided your email or phone, be aware that you might be a target of phishing attacks, so be careful when receiving unknown emails or calls.
Automatic installation of malware might happen under certain circumstances, for example, if the victim has vulnerable software[2] installed on their system. While this instance is relatively rare, there could be adware or another type of unwanted/malicious software already installed on your device, especially if you see more ads than usual and encounter misleading and fake websites on a regular basis.
Therefore, the first thing we recommend is running a full system scan with powerful anti-malware software, such as SpyHunter 5Combo Cleaner or Malwarebytes. It can ensure that all malware and most aggressive adware is deleted from your system automatically. This step is particularly important if you downloaded some software from fake websites such as Peoplethrowdid.top.
Check for unwanted programs
While it is more rare, adware programs that cause Peoplethrowdid.top redirects could be installed on the system level. If you are not entirely sure, you could skip this step; if you are confident and aware of which apps could be potentially unwanted, proceed with the following steps on your operating system to eliminate them:
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Mac
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
Uninstall malicious extensions
More often than not, adware comes in the form of a browser extension. Add-ons are versatile and are easy to produce, which provides the potential to rebrand easily to avoid bad reputation or some forms of security software detections. If you have many extensions installed on your system and you are not sure which one could be causing trouble, we recommend getting rid of all of them and then reinstating them one by one.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Clean browsers
Regardless of whether you found potentially unwanted or malicious unwanted programs on your system, cleaning web browser caches is important. Cookies, web beacons,[3] and other tracking technologies can be used in order to continue delivering users fake and misleading advertisements on various websites. The same goes for PUPs such as adware, they can gather user data even after they are deleted, as trackers are stored locally.
Another reason to remove cookies and other web data are due to the increased risk of a very dangerous session hijacking attack. Essentially, by hijacking cookies, malicious parties could take over sessions and access personal user accounts.
The easiest way to clean browsers is by employing FortectIntego utility, which would also repair any malware or adware damage done to the system and fix any unrelated issues as well. Alternatively, you can follow the instructions below and clean the caches manually:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Note: if you use Internet Explorer (which we highly discourage due to security reasons), you will find all the relevant instructions below.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Chris Hoffman. PUPs Explained: What is a “Potentially Unwanted Program”?. How-To Geek. Site that explains technology.
- ^ Thomas Holt. What Are Software Vulnerabilities, and Why Are There So Many of Them?. Scientific American. Science Magazine.
- ^ Web beacon. Wikipedia. The free encyclopedia.












