Trojan Spyware Alert – Error Code: #0x564897 scam (virus) - Free Instructions
Trojan Spyware Alert – Error Code: #0x564897 scam Removal Guide
What is Trojan Spyware Alert – Error Code: #0x564897 scam?
“Trojan Spyware Alert – Error Code: #0x564897” is a fake Microsoft tech support scam
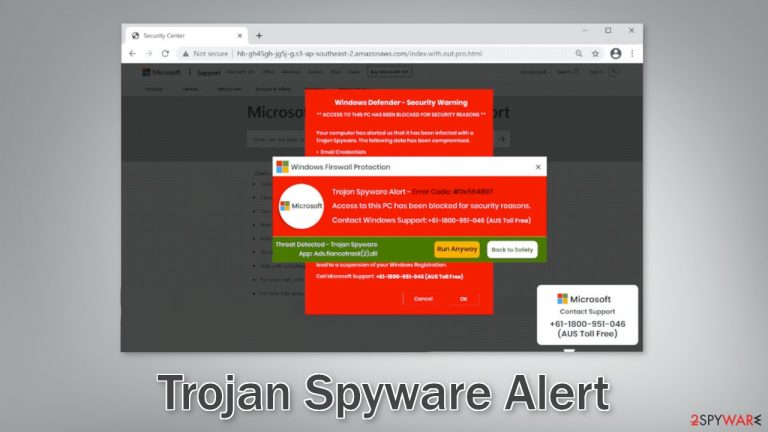
“Trojan Spyware Alert – Error Code: #0x564897” is a fake message that tries to convince users their system is in great danger. The site starts displaying multiple pop-ups that say their computer has been locked to intimidate them. The scam tries to make people believe that Windows Defender, Windows Firewall, and Microsoft have detected a malware[1] infection and they need to contact technical support to remove it.
It is obvious that Microsoft has nothing to do with this fraudulent campaign and scammers are using the well-known brand to make it seem legitimate. Users are then provided with a number that they have to contact. On the call, scammers will try to gain remote access to the device. They can then perform fake system scans, uninstall legitimate security tools, install dubious antivirus software or infect their machine with malware, like trojans, and ransomware.
A particularly worrying thing is that scammers often install RATs (Remote Access Trojans)[2] which provide the ability to access the machine without the users' knowledge for an unlimited amount of time. Fraudsters can gain control over users' personal files, like photos, videos, documents, and later blackmail them. The opportunities are limitless once you give crooks full access to your machine.
| NAME | Trojan Spyware Alert – Error Code: #0x564897 |
| TYPE | Online scam; adware |
| SYMPTOMS | A page appears bombarding users with multiple pop-ups that say their system is in danger and blocked so they need to contact Microsoft Support |
| DISTRIBUTION | Shady websites, deceptive ads, bundled software |
| DANGER | Scammers can lure out personal information, convince victims to pay for bogus security software or infect their systems with malware |
| ELIMINATION | Check your browser for malicious extensions and scan your machine with anti-malware tools |
| FURTHER STEPS | Use FortectIntego to get rid of any remaining damage and clear your browser |
The pop-up message
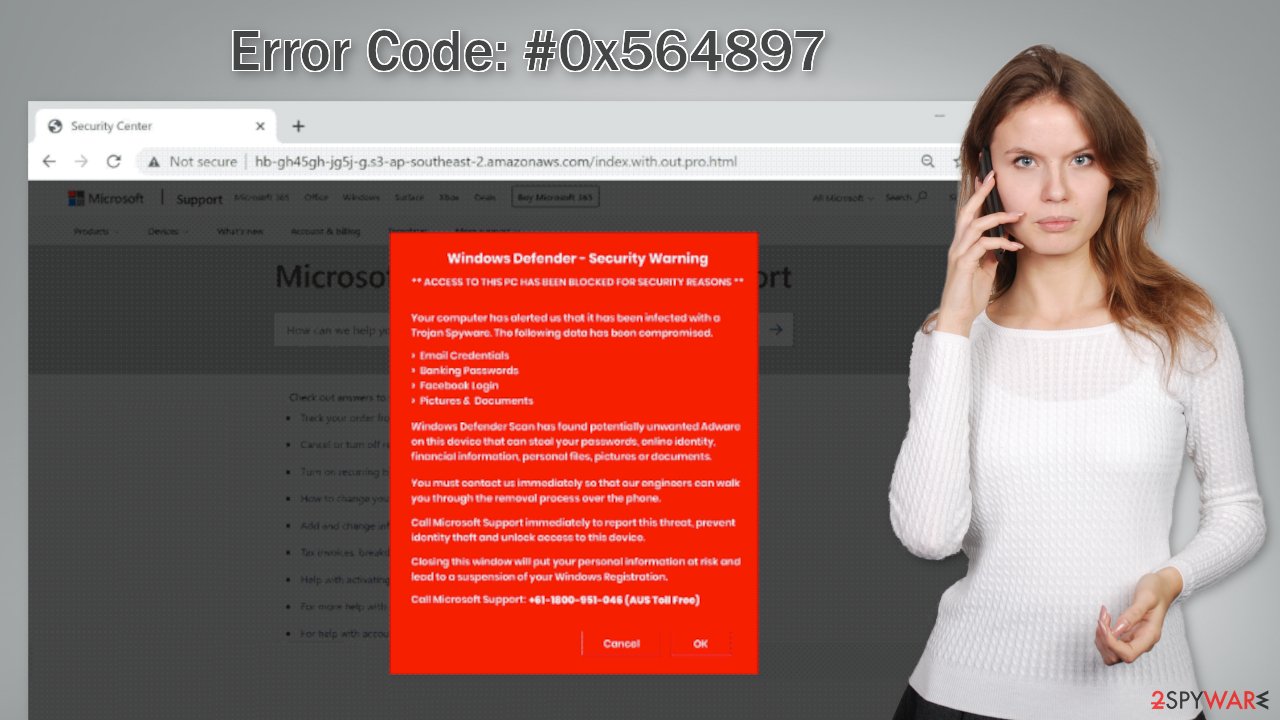
Below you can see a message in one of the pop-ups from the scam website:
Windows Defender – Security Warning Alert
** ACCESS TO THIS PC HAS BEEN BLOCKED FOR SECURITY REASONS **
Your computer has alerted us that it has been infected with a Trojan Spyware. The following data has been compromised.
Email Credentials
Banking Passwords
Facebook Login
Pictures & DocumentsWindows Defender Scan has found potentially unwanted Adware on this device that can steal your passwords, online identity, financial information, personal files, pictures or documents.
You must contact us immediately so that our engineers can walk you through the removal process over the phone.
Call Microsoft Support immediately to report this threat, prevent identity theft and unlock access to this device.
Closing this window will put your personal information at risk and lead to a suspension of your Windows Registration.
Call Microsoft Support: +61-1800-951-046 (AUS Toll Free)
The message states that Microsoft has been alerted about an adware infection and as a result, blocked the machine. Scammers list the things that could be compromised and rush users to contact the provided number so the threat could be dealt with. You should never believe this or similar messages. Microsoft can never block your Windows computer even if it is infected with malware or viruses.
Crooks use various scare tactics to prevent people from exiting the site, saying that it can result in further damage. In reality, if you stumble upon a page like this, you should close it immediately and not interact with it. Ending the browser session in the Task Manager is also recommended to stop the page from reappearing when you open the browser again.
Look for malicious browser extensions
This tech support scam page could have appeared because you have a malicious extension added to your browser. Web-based applications can gain control over your browser and change important settings. Then the app can start generating pop-ups, banners, and causing redirects to shady websites. We suggest you go to your browser settings and remove the plugins you have added one by one to see if you notice any difference.
You should also take care of your browsers by clearing them from any tracking technologies that could have been deployed by suspicious sites. Cookies and cache are normally used to personalize the user experience by showing people relevant results and suggestions catered to their hobbies.
However, cookies[3] can also be used by fraudsters to make a profit. They can be sold to advertising networks or other third parties and used to target you with bogus ads even more. Besides that, fraudsters then gain access to information like your IP address,[4] geolocation, websites you visit, links you click on, and things you purchase online.
Since some researchers have observed that the “Trojan Spyware Alert – Error Code: #0x564897” scam was promoted via the Amazon AWS service which has been known to display shady pop-ups and redirect users to suspicious sites, you should definitely clean your browsers.
You can use a maintenance tool like FortectIntego that can do it all – stop the tracking, and delete the already collected data, since it is stored on your device. It can also fix serious system errors, corrupted files, and registry issues which is especially helpful after a virus infection.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the window's top-right).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.

MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

MS Edge (legacy)
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Scan your machine with professional security tools
We previously discussed all the ways you could have ended up on the “Trojan Spyware Alert – Error Code: #0x564897” scam site using the Internet. Unfortunately, there are other ways it could have gotten to you. For example, adware is a type of PUP (potentially unwanted program)[5] that can generate commercial content, like pop-ups, banners, and redirects on a machine without the users' knowledge.
There is a big possibility that you have adware or another type of PUA installed in your machine that is redirecting you to pages from unsafe advertising networks. Such programs often get inside the operating system with freeware. Freeware[6] distribution sites use software bundling to make a profit, which means they include additional programs in the installers that monetize user activity.
In order to prevent this from happening, use only official web stores and developer websites. Even though it might get costly, you may save in the long run by not having your system damaged or falling into the traps of Internet scams. You can also choose the “Custom” or “Advanced” installation method so no steps would be hidden from you. It is very important to check the file list and untick the boxes next to any unnecessary programs if there are any.
The adware removal part can be tricky as it is often disguised as a “handy” tool to make it harder to identify. It could look like an antivirus, system optimizer, media player, you name it, so the best solution is to use professional security tools that can scan your machine and detect suspicious processes in the background.
SpyHunter 5Combo Cleaner and Malwarebytes are great options because they are proven and trusted anti-malware tools. They can detect most threats hiding in your machine, and eliminate them completely. Manual removal can sometimes result in the renewal of infection as users fail to eliminate all the related files that are hidden in various folders. However, if you still want to do this yourself, you can proceed with the guide below:
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till the uninstallation process is complete and click OK.

How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Malware. Wikipedia, the free encyclopedia.
- ^ What is a Remote Access Trojan (RAT)?. Proofpoint. Data Security.
- ^ Chris Maus. What Are Cookies and Are They Dangerous?. Qkey. Payment Security Providers.
- ^ What is an IP Address – Definition and Explanation. Kapsersky. Home Security.
- ^ Chris Hoffman. PUPs Explained: What is a “Potentially Unwanted Program”?. Howtogeek. Technology Magazine.
- ^ Tales From the SOC: Dealing with the Dangers of Freeware. Infosecurity. Cybersecurity Blog.
