Poison ransomware (virus) - Quick Decryption Solution
Poison virus Removal Guide
What is Poison ransomware?
Poison ransomware is a type of malware designed to extort money from you
Locking personal files on the computer is bad enough, but asking for money to unlock them became a familiar phenomenon all over the world. Poison ransomware is another addition to an ever-expanding list of new cryptomalware strains which first showed up in the middle of October of 2021.
After the virus manages to break into a Windows machine, it immediately begins its malicious activities, infecting the whole system or even network, if the PC is connected to one, immediately. These modifications are required in order for malware to fulfill its main goal – to lock all pictures, documents, videos, and other types of files. This process can be a bit longer than the infection one, as it highly depends on the size of the files susceptible to encryption.
At this time, malware renders all files useless, stripping them off their original icons and locking them with a secure algorithm. While data can no longer be accessed or modified, it does not mean that it is corrupted. Poison ransomware creates a complex, unique key that is sent to the attackers' servers immediately. This key is then used to blackmail users into paying money for file retrieval.
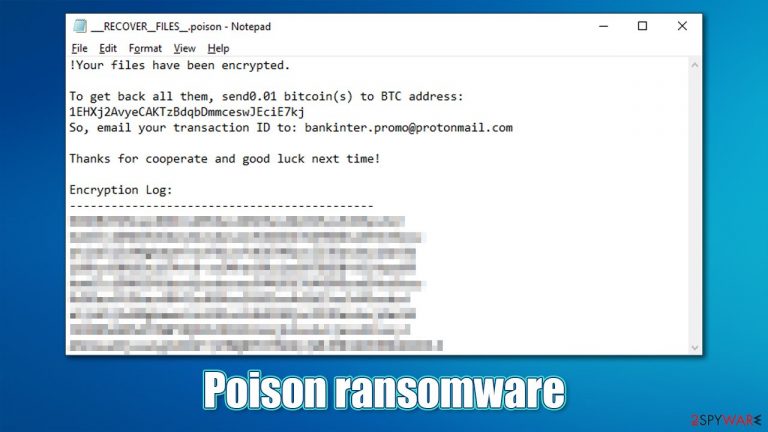
To make victims aware of what just happened, malware authors leave a ransom note ___RECOVER__FILES__.poison.txt, which is placed on the desktop and any other folders where locked files are located. The ransom note is brief but informative; it claims that users need to process payment of 0.01 BTC into the 1EHXj2AvyeCAKTzBdqbDmmceswJEciE7kj Bitcoin wallet and then an email with the transaction ID sent to ankinter.promo@protonmail.com.
| Name | Poison ransomware |
|---|---|
| Type | Ransomware, file-locking malware, cryptovirus |
| File extension | .poison is appended at the end of each file name |
| Ransom note | ___RECOVER__FILES__.poison.txt and a pop-up window titled “!Ups” |
| Contact | bankinter.promo@protonmail.com |
| Ransom size | 0.01 BTC, to be transferred to 1EHXj2AvyeCAKTzBdqbDmmceswJEciE7kj Bitcoin wallet |
| File Recovery | If no backups are available, recovering data is almost impossible. Nonetheless, we suggest you try the alternative methods that could help you in some cases – we list them below |
| Malware elimination | Manual virus removal is not recommended, as it might be difficult for regular users. Instead, SpyHunter 5Combo Cleaner or other anti-malware tools should be used |
| System fix | Malware can seriously tamper with Windows systems, causing errors, crashes, lag, and other stability issues after it is terminated. To remediate the system and avoid its complete corruption, we recommend scanning it with the FortectIntego repair tool |
Poison virus is a new ransomware strain, and no connections have been found with other ransomware families. Nonetheless, man new and experimental ransomware shows up after some members leave a larger cybercriminals group to increase profits from the illegal activities. Likewise, new people within the cybercriminal world can also be starting their own businesses.
In the case of the latter, there are no established principles that the group works by, hence there could be bugs within the ransomware encryption codes or the returned decrytpion tools might fail to work. This is why it is not advised by experts[1] to trust hackers behind ransomware and send them the money they require. The full ransom note reads:
!Your files have been encrypted.
To get back all them, send0.01 bitcoin(s) to BTC address: 1EHXj2AvyeCAKTzBdqbDmmceswJEciE7kj
So, email your transaction ID to: bankinter.promo@protonmail.comThanks for cooperate and good luck next time!
Encryption Log:
Looking at it, it seems like crooks are trying to be approachable and “nice” within the last sentence. This is one of the tactics employed by ransomware authors; as we observed in other malware strains, ransom notes are threatening and even put up a timer before the decryption key is allegedly deleted from the crooks' server.
In any case, it is up to you whether you want to risk your money and pay the required Bitcoin, although be warned – you might lose your files and money. While it is true that there is no working decryption tool that would guarantee a file recovery, you could try several alternative methods we list below. But before that, you need to remove Poison ransomware from your device.
Delete malware from your system
After the ransomware is done with encrypting all files, its main job is done. Hence, some infections simply self-delete as soon as the data-locking process is complete, although this is not a rule, and some malware continues running in the background due to various reasons. For example, it might continue locking all the incoming data (if such is placed on the infected PC), or stealing personal information in the background. Besides, malware is commonly spread in bulks, so there might be a dangerous virus installed as well.
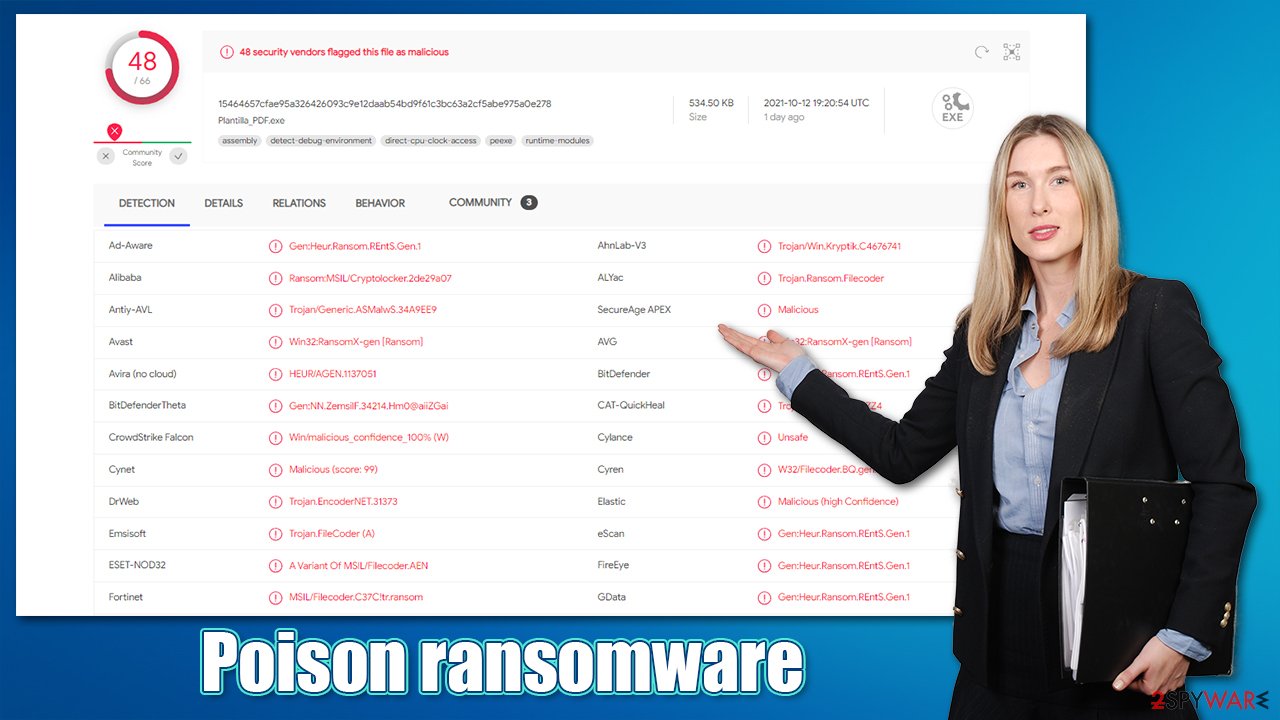
Thus, it is vital to use security software to remove the Poison virus from your system, along with any other additional threats. Download SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable anti-malware and perform a full system scan to eliminate all the malicious components at once. In fact, security software is your number one weapon against ransomware infections, as it can stop it before it manages to encrypt files. According to Virus Total, this virus can be detected under the following names:[2]
- Gen:Heur.Ransom.REntS.Gen.1
- Trojan.Ransom.Filecoder
- A Variant Of MSIL/Filecoder.AEN
- Ransom:MSIL/Cryptolocker.PDH!MTB
- Msil.Trojan.Gen.Ejex
- Ransom.FileCryptor, etc.
Note: ransomware might tamper with security software and prevent it from working. If that happens, ever to the instructions at the bottom of this post to access Safe Mode and scan the system from there to bypass malware's malicious features.
Attempt to recover .poison files with these methods
As previously mentioned, sending money to ransomware creators can be risky. It also motivates them to infect more victims to acquire more money, hence the illegal business prospers. Instead of doing that, you should try using the following methods to recover the locked files. There are two things you should make sure of before proceeding:
- You scanned your PC with security software and malware is no longer present on it
- You made backups of locked files.
During the recovery process listed below, encrypted files might get corrupted permanently, so it is vital to keep them on a separate medium. You can use a USB flash drive or similar external storage device; also, using remote cloud services can also be very convenient – we provide instructions on how to backup files on OneDrive and Google Drive below.
Use recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
Wait for a decryptor
Most fully-working ransomware use encryption algorithms such as AES or RSA to lock up data securely. This means that the decryption key can only be retrieved from cybercriminals' servers, although, obviously, they are not willing to give it up for free and ask for money in exchange for it.
Luckily, some ransomware is far from perfect and has bugs[3] within their encryption process, which allows security experts to create a working decryption tool, providing it for victims for free. Alternatively, law enforcement has previously seized the servers of malware authors, which allowed them to release keys to the public. Thus, use the following links to find a decryption tool, although you should keep in mind that it might take time before a working one is available, if at all.
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

Take care of your system health
Regardless of whether the above methods helped you to restore files or not, you should not neglect your Windows system. After malware infection, it might start malfunctioning – crashing, lagging, fail to launch applications, returning errors, and much more. Thus, we strongly recommend you follow the below instructions to repair your system instead of reinstalling it altogether.
- Download FortectIntego
- Click on the ReimageRepair.exe

- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process

- The analysis of your machine will begin immediately

- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.

By employing this tool, you would not have to worry about future computer issues, as most of them could be fixed quickly by performing a full system scan at any time. Most importantly, you could avoid the tedious process of Windows reinstallation in case things go very wrong due to one reason or another.
Getting rid of Poison virus. Follow these steps
Access Safe Mode to remove malware from Windows
If malware is not letting you use antivirus in normal mode, access Safe Mode and perform a full system scan from there.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.
- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.

Once you reach Safe Mode, launch SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable antivirus, update it with the latest definitions, and perform a full system scan to eradicate malware and all its malicious components.
Create data backups to avoid file loss in the future
One of the many countermeasures for home users against ransomware is data backups. Even if your Windows get corrupted, you can reinstall everything from scratch and retrieve files from backups with minimal losses overall. Most importantly, you would not have to pay cybercriminals and risk your money as well.
Therefore, if you have already dealt with a ransomware attack, we strongly advise you to prepare backups for future use. There are two options available to you:
- Backup on a physical external drive, such as a USB flash drive or external HDD.
- Use cloud storage services.
The first method is not that convenient, however, as backups need to constantly be updated manually – although it is very reliable. Therefore, we highly advise choosing cloud storage instead – it is easy to set up and efficient to sustain. The problem with it is that storage space is limited unless you want to pay for the subscription.
Using Microsoft OneDrive
OneDrive is a built-in tool that comes with every modern Windows version. By default, you get 5 GB of storage that you can use for free. You can increase that storage space, but for a price. Here's how to setup backups for OneDrive:
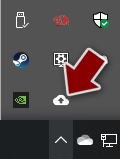
- Click on the OneDrive icon within your system tray.
- Select Help & Settings > Settings.
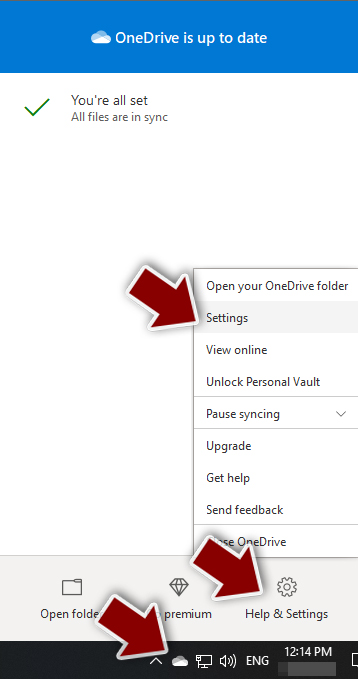
- If you don't see your email under the Account tab, you should click Add an account and proceed with the on-screen instructions to set yourself up.
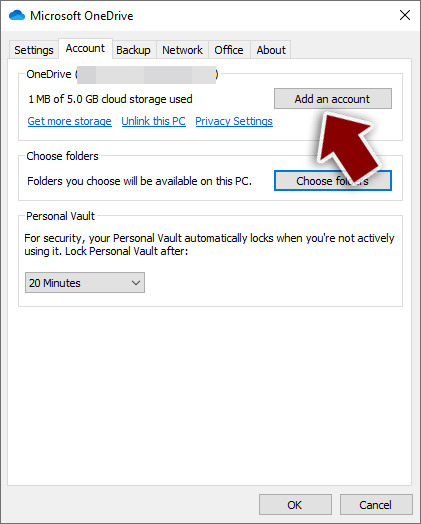
- Once done, move to the Backup tab and click Manage backup.
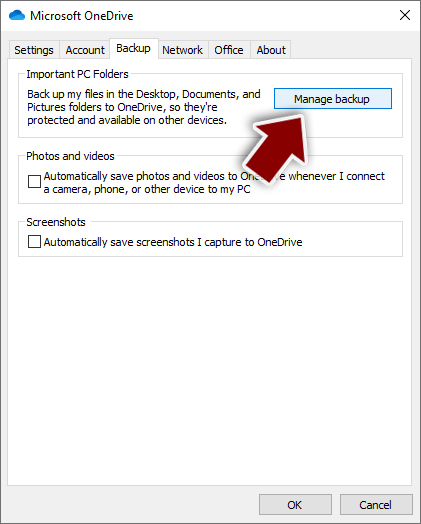
- Select Desktop, Documents, and Pictures, or a combination of whichever folders you want to backup.
- Press Start backup.
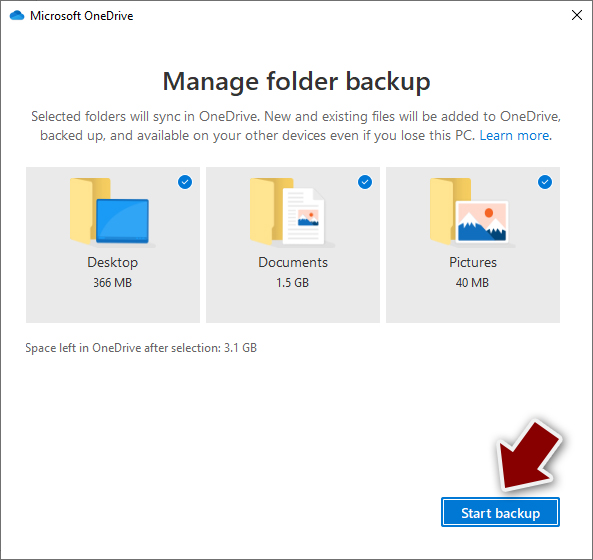
After this, all the files that are imported into the above-mentioned folders will be automatically backed for you. If you want to add other folders or files, you have to do that manually. For that, open File Explorer by pressing Win + E on your keyboard, and then click on the OneDrive icon. You should drag and drop folders you want to backup (or you can use Copy/Paste as well).
Using Google Drive
Google Drive is another great solution for free backups. The good news is that you get as much as 15GB for free by choosing this storage. There are also paid versions available, with significantly more storage to choose from.
You can access Google Drive via the web browser or use a desktop app you can download on the official website. If you want your files to be synced automatically, you will have to download the app, however.
- Download the Google Drive app installer and click on it.

- Wait a few seconds for it to be installed.
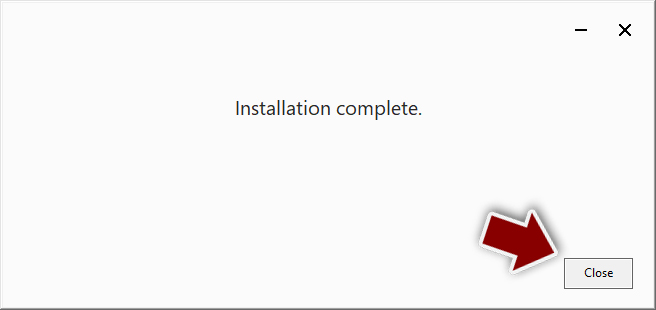
- Now click the arrow within your system tray – you should see Google Drive icon there, click it once.
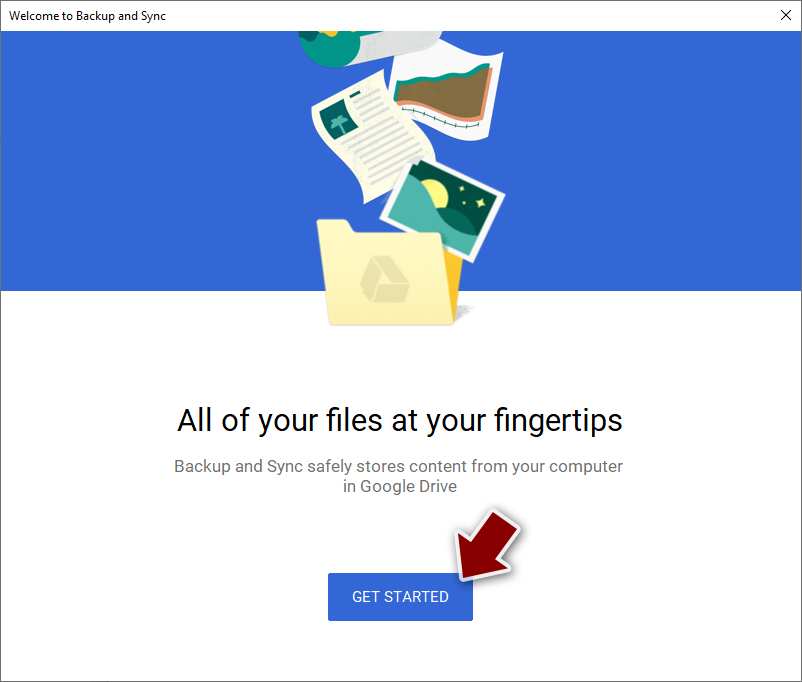
- Click Get Started.
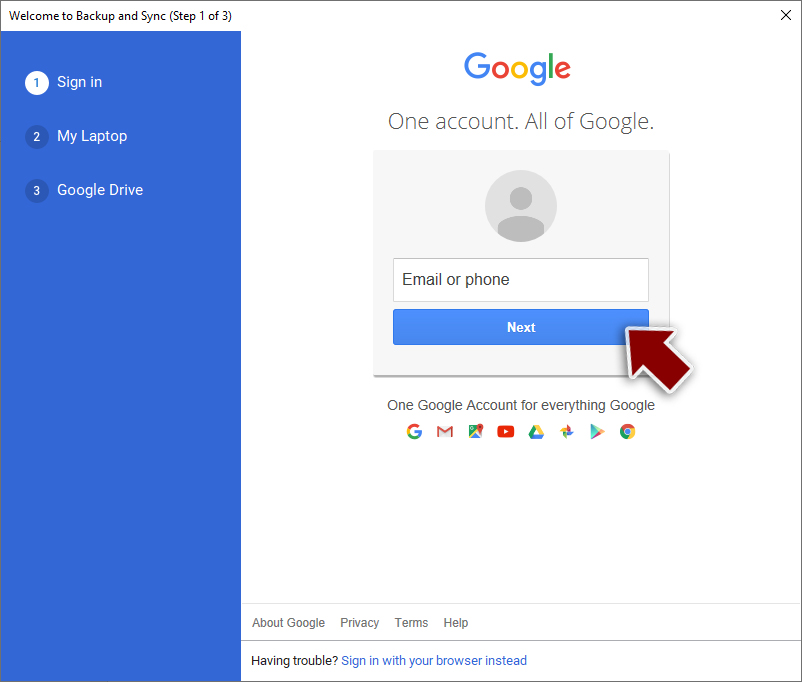
- Enter all the required information – your email/phone, and password.
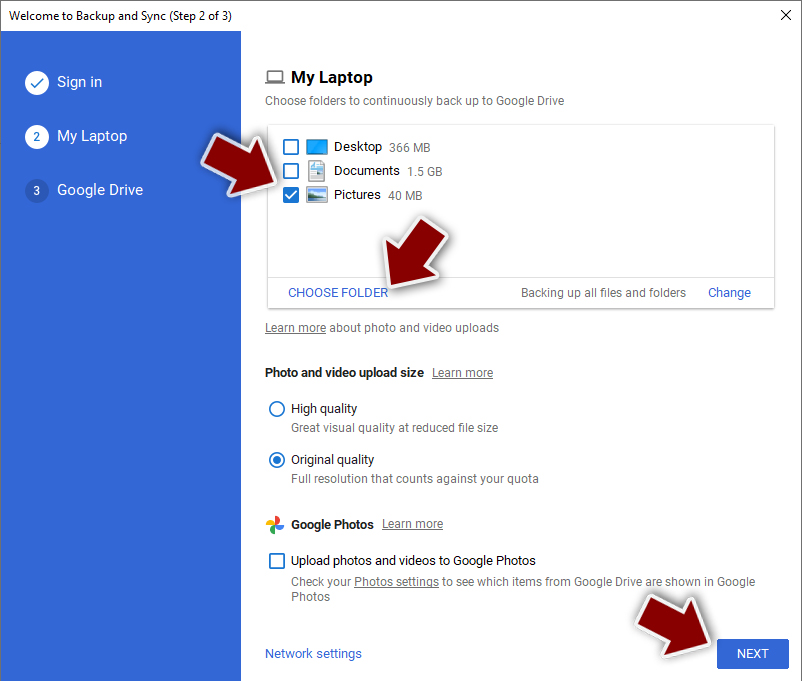
- Now pick what you want to sync and backup. You can click on Choose Folder to add additional folders to the list.
- Once done, pick Next.
- Now you can select to sync items to be visible on your computer.
- Finally, press Start and wait till the sync is complete. Your files are now being backed up.
Report the incident to your local authorities
Ransomware is a huge business that is highly illegal, and authorities are very involved in catching malware operators. To have increased chances of identifying the culprits, the agencies need information. Therefore, by reporting the crime, you could help with stopping the cybercriminal activities and catching the threat actors. Make sure you include all the possible details, including how did you notice the attack, when it happened, etc. Additionally, providing documents such as ransom notes, examples of encrypted files, or malware executables would also be beneficial.
Law enforcement agencies typically deal with online fraud and cybercrime, although it depends on where you live. Here is the list of local authority groups that handle incidents like ransomware attacks, sorted by country:
- USA – Internet Crime Complaint Center IC3
- United Kingdom – ActionFraud
- Canada – Canadian Anti-Fraud Centre
- Australia – ScamWatch
- New Zealand – ConsumerProtection
- Germany – Polizei
- France – Ministère de l'Intérieur

If your country is not listed above, you should contact the local police department or communications center.
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Dieviren. Dieviren. Cybersecurity advice and malware insights.
- ^ 15464657cfae95a326426093c9e12daab54bd9f61c3bc63a2cf5abe975a0e278. Virus Total. File and URL analysis.
- ^ Software bug. Wikipedia. The free encyclopedia.
