PwndLocker ransomware (Virus Removal Instructions) - updated Mar 2020
PwndLocker virus Removal Guide
What is PwndLocker ransomware?
PwndLocker ransomware – a now decryptable malware that targets enterprise networks and asks for exceedingly high ransoms
PwndLocker ransomware[1] is the cryptovirus that locks files for the purpose of maximizing odds of ransom extortion. The malware strain is relatively new – it first entered the scene at the end of December 2019, targeting the city, business, and corporation networks and asking for ransoms that exceed 75 BTC in some cases ($170,000 – $660,000). The ransom payments also depend on the size of the organization or municipality. In one of such attacks – on Lasalle County in Illinois – the authors of the PwndLocker virus asked for 50 BTC for the decryptor, which is not going to be paid.[2] Luckily, security researcher Fabian Wosar from Emsisoft discovered a flaw that could help victims of PwndLocker to recover their data without paying huge extortion sums.[3]
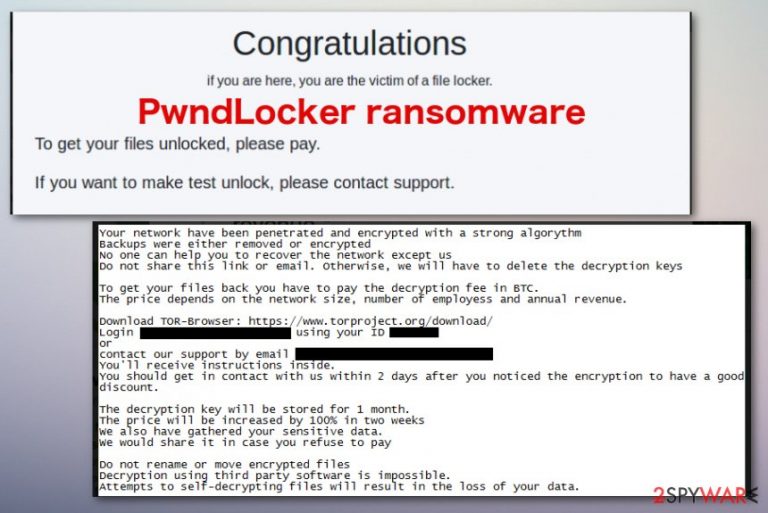
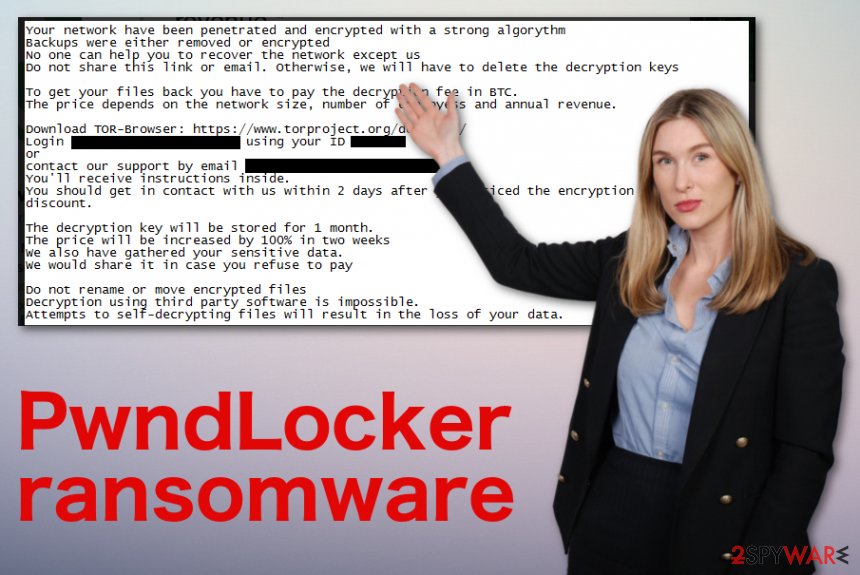
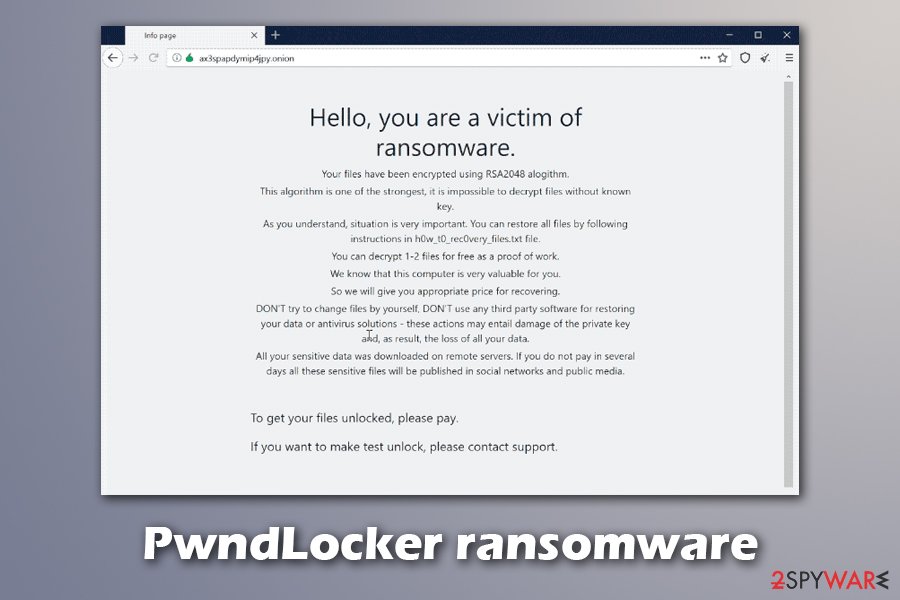
PwndLocker ransomware virus starts with the encryption process as any other malware of this kind – it encrypts documents, databases, and other data with a secure algorithm AES, and appends a marker to each of the files (.pwnd or .key). To explain the situation, threat actors provide a ransom note H0w_T0_Rec0very_Files.txt – it asks victims to connect to the support panel via the Tor network or contact the attackers via the provided email. Allegedly, the PwndLocker ransomware decryptor is deleted after a month, and the ransom size doubles after two weeks. To make matters worse, cybercriminals threaten to publish highly sensitive company information if case the demands are not met – a new terrifying trend among ransomware makers that was started by a gang behind Maze ransomware.[4]
| Name | PwndLocker ransomware |
|---|---|
| Type | Cryptovirus |
| File marker | .pwnd and .key are known extensions that this threat uses for marking affected files on the infected systems |
| Ransom amount | PwndLocker ransomware is known to ask for exceptionally high ransoms ($170,000 – $660,000 in BTC). The sum usually depends on the size of the organization |
| Ransom note | H0w_T0_Rec0very_Files.txt is the file that appears after encryption to inform victims about the attack. Also, an additional message from virus developers appears on the desktop and as a program window that offers to pay and unlock files this way |
| Encryption method | Malware uses a symmetric algorithm AES[5] to lock files on the network |
| Distribution | Because the threat targets corporations, it is highly likely that it is distributed via unprotected RDP connections, targeted phishing emails, exploits, and similar methods |
| File recovery | Users can now recover the encrypted data for free – as long as they can retrieve an executable that is used to infect the network (unfortunately, it is not always possible). Once it is retrieved, victims can contact Emsisoft for help |
| Elimination | PwndLocker ransomware removal requires more attention from security experts when the large network is affected. The best way to clean the system from cush cryptovirus is anti-malware tools based on malware detection[6] |
| Repair | You need to consider the ransomware as one of the more dangerous threats, so PC repair tools like FortectIntego are needed to fix virus damage that can affect your machine even when the virus itself is terminated |
Bitcoin is the preferred cryptocurrency that PwndLocker ransomware developers would like to get from their victims so in the ransom note file H0w_T0_Rec0very_Files.txt criminals listed places where you can create the wallet and exchange dollar or another currency in the most popular crypto.
According to the ransom message, when you access the particular account that criminals provide you, you can contact them and receive further payment instructions. You need to follow the steps in PwndLocker ransom note in two days or less, as the following note states:
Your network have been penetrated and encrypted with a strong algorythm
Backups were either removed or encrypted
No one can help you to recover the network except us
Do not share this link or email, otherwise, we will have to delete the decryption keys
To get your files back you have to pay the decryption fee in BTC.
The price depends on the network size, number of employess and annual revenue.
Download TOR-Browser: https://www.torproject.org/download/
Login ***** using your ID ***
or
contact our support by email ***
You'll receive instructions inside.
You should get in contact with us within 2 days after you noticed the encryption to have a good discount.
The decryption key will be stored for 1 month.
The price will be increased by 100% in two weeks
We also have gathered your sensitive data.
We would share it in case you refuse to pay
Do not rename or move encrypted files
Decryption using third party software is impossible.
Attempts to self-decrypting files will result in the loss of your data.
You shouldn't consider paying criminals and remove PwndLocker ransomware from the system instead. Nevertheless, it is also important to backup the encrypted data, as threat termination might permanently damage it. While there is a new tool from Emsisoft available that could help you recovery your fails , its recovery from backups is the best way to avoid the devastating consequences of PwndLocker virus infection.
Besides locking data, PwndLocker is also known to cause several substantial changes to the Windows machines that get infected. Upon infiltration, the malware will proceed with the following system changes:
- Kills a variety of processes by running a taskkill.exe command (MS Office documents, web browsers, etc.);
- Disables Windows services related to BackupExec, Oracle, Microsoft SQL Server, and many others;
- Deletes Shadow Volume Copies by applying “vssadmin.exe delete shadows /all /quiet” command to prevent data recovery;
- Turns off anti-malware software that protects networks from malware intrusion, etc.
After the system is prepared for the encryption process, PwndLocker ransomware will target the most commonly-used file types, although it will skip data located in some of the folders (such as Windows NT, Recycle Bin, All Users, Microsoft, WindowsApps, etc.).
Since PwndLocker ransomware removal can get difficult due to termination of security software, although this step can usually be bypassed when entering Safe Mode with Networking – below we provide the instructions on how to access it.
PwndLocker ransomware is not the threat that only focuses on locking images, documents, video, audio files, or databases. It deletes various files and adds programs or damages existing data to make the machine more affected and malware persistent. Unfortunately, when malware hits enterprises, anti-malware tools may not be enough for the whole network, so you should rely on IT specialists who can manage the cybersecurity for you.
However, as for everyday computer users that have encountered PwndLocker ransomware on their machines, you should get a program like FortectIntego that could repair damaged registry entries or affected OS files for you.
PwndLocker decryptor is now available
Files can hold crucial information, especially when it comes to businesses and organisations. Besides, databases and documents also sometimes hold sensitive information of clients, putting their privacy and security at risk. In other words, infection of PwndLocker ransomware could be devastating to any company so much so that it would sometimes close its doors forever.
Luckily, there are security experts and ransomware hunters who are constantly working with new samples and create decryption tools that could help victims to recover data for free. Thanks to these efforts, PwndLocker ransomware is now decryptable, although there are a few “buts” for this to be successful.
Security expert Fabian Wosar discovered a flaw within PwndLocker virus' code. However, there is no a regular decryption tool that could be run on the system so far – users need to send a message to Wosar which also includes an executable file that was used to infect the network. Unfortunately, this file is usually deleted after the encryption process of data is complete.
Nevertheless, you may use ShadowExplorer or similar tools to recover the required file. When looking for it, you should check locations that it is usually stored at, including the following folders:
- %AppData%
- %Temp%
- C:\User
Ransomware targets the ones who can pay quickly
Malware in this cryptovirus category can spread using various methods. In most cases, stealthy techniques get employed for such distribution campaigns, especially when a virus targets large businesses and companies. Various organizations receive emails on a daily basis, and when the network connects many employees and users it becomes extremely dangerous to open the questionable file or an email itself.
Malicious macros, in most cases, get injected on Microsoft files like Word, Excel documents, PDF files. Once you receive the email with the attached file, you should consider the legitimacy of the sender and the notification itself before you go for the attachment.
Opening such a document leads to the form of enabling additional content – macros or direct payload drop. This is the way that malware gets on the machine or the whole system of machines. Trojans, malware, worms, and other viruses can get on the device this way and spread ransomware as a secondary payload.
Also, file with direct cryptovirus can get installed after you click the Enable or Allow button. Avoid any emails from shipping companies, shopping sites, and similar services, when you are not expecting to get any information from them.
Terminate all parts of the PwndLocker ransomware virus by scanning the system fully
Before you for the PwndLocker ransomware removal, you need to consider all the options. It is possible that researchers could develop the decryption tool after a while or when the vulnerability of encryption gets exposed. Base on such things, you can try to keep some virus-related files and encrypted data on external devices for later use.
However, you still need to remove PwndLocker ransomware from the system if you want to use the machine ever again. Any traces of the encryption-based threat can trigger secondary file locking and other malicious activities on the device, so it is not advised to use a computer that still has some sort of malware on it.
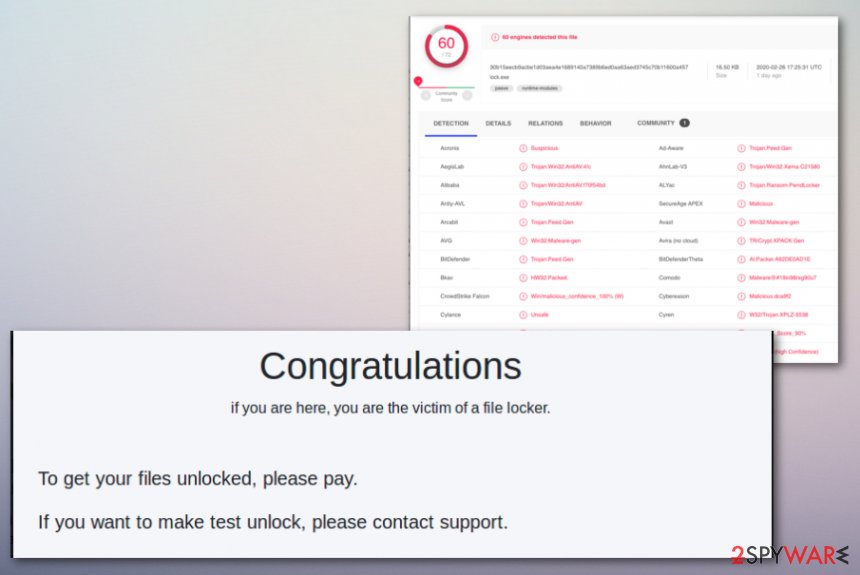
PwndLocker ransomware virus can get detected by many anti-malware tools, so choose SpyHunter 5Combo Cleaner or Malwarebytes and run it on the machine. Once the scan is done, you should receive the list of malicious files, indicated files, and similar issues. Then, then the best step is to follow suggestions and delete all possible intruders and malware.
Getting rid of PwndLocker virus. Follow these steps
Manual removal using Safe Mode
Reboot the machine in Safe Mode with Networking to remove PwndLocker ransomware from the machine
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove PwndLocker using System Restore
System Restore feature can help with the virus termination by recovering the system in a previous state
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of PwndLocker. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove PwndLocker from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by PwndLocker, you can use several methods to restore them:
Data Recovery Pro can help with affected files after a ransomware attack
You can rely on Data Recovery Pro for files encrypted by PwndLocker ransomware or data deleted accidentally
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by PwndLocker ransomware;
- Restore them.
Windows Previous Versions is the alternate method for data recovery
When System Restore gets enabled, Windows Previous Versions can recover individual files for you
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer for help when data backups are not availiable
However, this is not working when Shadow Volume Copies get deleted by the PwndLocker ransomware itself
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Contact Emsisoft for PwndLocker ransomware decryption
Once you found the main executable that was used to infect your network, you should contact Emsisoft – the firm will help you get back your data for free.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from PwndLocker and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Vitali Kremez. PwndLocker ransomware. Twitter. Social media platform.
- ^ LaSalle County Government Continuing to Battle Apparent Ransomware Issues. WSPY News. News site.
- ^ Mathew J. Schwartz. PwndLocker: Free Decryptor Frees Crypto-Locked Data. Bankinfosecurity. Bank information security news.
- ^ ‘Maze’ ransomware threatens data exposure unless $6m ransom paid. Naked Security. Sophos security blog.
- ^ Advanced Encryption Standard. Wikipedia. The free encyclopedia.
- ^ Ransomware detection rate. VirusTotal. Online malware scanner.







