Remove Rackcdn.com Mac virus
Rackcdn.com Removal Guide
What is Rackcdn.com?
Rackcdn.com is the intruder that creates issues with the performance with repeating redirects

Rackcdn.com is a rogue site that was misused by hackers to cause frustration and trick users into contacting fake tech support sites to make them reveal their personal information.[1] The website is not the main program that should be removed from the system, all the redirects, fake alerts, pop-up ads, and this website are results of the adware-type program that already runs on the computer without your permission.
These browser-based threats can heavily affect the time online for mac users because the operating system is generally secure, but there are sites that manage to trigger scammy messages, tamper with the browsing activities and lead to serious issues with the machine.
Unfortunately, most of Rackcdn.com-related adware has been causing redirects, showing the message identical to other technical support scams like Your system is infected with 3 viruses on the screen and promoting such fake tools as Mac Cleanup Pro. The message looks legitimate enough for people to believe the statement that the device is infected with spyware. However, the PUP that causes these redirects and other content is the only intruder you need to remove from the computer.
| Name | Rackcdn.com |
|---|---|
| Type | Adware/scam |
| Category | Potentially unwanted program |
| Tactics | Social engineering/ technical support scam[2] |
| Redirects to | ssl.cf6.rackcdn.com, which displays Your system is infected with 3 viruses |
| Distribution | Software bundles, deceptive advertising websites |
| Affects | MacOS devices and compatible browsers |
| Elimination | Anti-malware tool is required for the thorough infection removal |
Although the message that appears on the screen states about malware infections and spyware you need to remove, the only intruder that requires cleaning is a deceptive scam that causes all the intrusive behavior and questionable activity on your system. It is controlled by adware-based PUP.
Unfortunately, potentially unwanted programs come silently, and the initial infiltration cannot be noticed when Rackcdn.com enters the PC via deceptive site or freeware installation setup. Although you can avoid such infiltration, symptoms of the PUP appear after the infection.
These sites that show up out of nowhere with all the security-related messages often push fake updates, software, or tools. Stay away from installing such applications from random pop-ups or banners:
- Adobe Flash Player;
- Video Player;
- Java updates.
Once Rackcdn.com enters the system, it starts delivering various content regarding online offers, discounts, and other advertising material. This campaign involves advertising content because PUP developers are commercial content creators, and they can access various information about the user via visits on the ad-supported pages or banners and pop-up ads.
Malvertising campaigns, when particular information about the user is used to create personalized advertisements rely on IP addresses, location, browsing queries, and other data collected via these PUPs and other cyber intruders. This is a common technique when ad-supported sites use tracking cookies and other methods to receive valuable browsing data.
Additional adware symptoms involve:
- banners and in-text ads injected on the websites you commonly visit;
- random text turned into hyperlinks;
- pop-ups recommending tools and software updates;
- other unwanted programs get installed without users' permission.
The primary Rackcdn.com purpose is to create redirects and display deceptive content to trick people into installing the rogue system or anti-malware tools. The message scaring people about malware is created for that same purpose. However, the technical support scam can lead to more severe issues regarding damage to a computer or even privacy issues and identity theft.
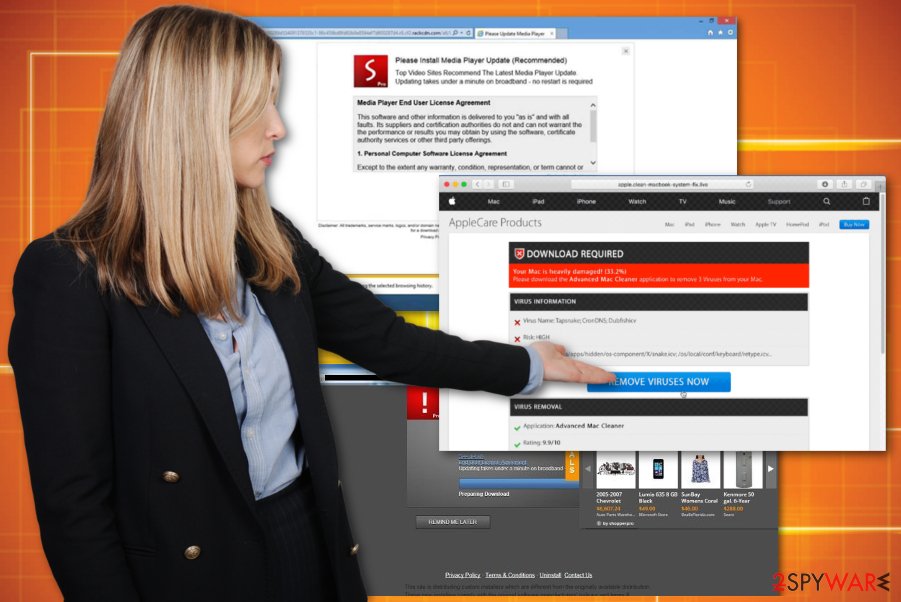
Experts[3] note that Rackcdn.com and other fake system alerts stating about viruses on the machine offers to call the technical support number or scan the device using the provided program. Unfortunately, when you call the number attackers can ask to give the remote access to your computer, which leads to direct malware installations.
You need to remove the infection once it appears on the screen and redirects you to this message about malware because keystroke loggers can get installed to collect banking information, passwords or logins when you try to pay for the alleged service. This is what leads to privacy issues or even identity theft.
Remember that Rackcdn.com removal requires professional anti-malware tools because the intruder categorizes as a potentially unwanted program and cyber threat, so it adds other files and applications to alter the settings of your machine. We also recommend cleaning the system thoroughly with a tool like FortectIntego, so virus damage can be terminated.
Installing questionable programs or updating your software from suspicious sources can lead to more than the installation of rogue tools
Such potentially unwanted programs get delivered via deceptive methods like fake system tool promotions, freeware installation setups, other applications. However, the primary technique used to spread these cyber intruders involves software bundles and freeware sites or services.
P2p services, networks, other sites where you can download software for free and internet pages in general, deliver such applications when you are not paying enough attention not only to the trustworthiness of the source but the installation process itself.
No matter how reliable is the source you get your programs from is, you should pay attention to the installation that happens and choose Advanced or Custom options to see all the applications included on the setup. When you go for Quick installations, all the pre-packed potentially unwanted programs get installed automatically.
End the ongoing redirections to random websites and terminate Rackcdn.com PUP
All the messages about your infected machine and commercial content, keeping you from accessing wanted sites are results of the Rackcdn.com virus. Exiting the website or pop-up window, removing the browser extension or any other tool is not enough to eliminate the PUP.
To stop intrusive behavior and make your device running as fast as before, you need to remove the threat alongside other installed programs or added files fully. Since you need to find all of them hidden all over the machine, the best tip we can give is to use automatic antivirus tools for the job.
The automatic Rackcdn.com removal is recommended because, during a full system scan that professional anti-malware tools can run, all cyber intruders get detected and deleted from the system. Such tools can also indicate and fix other issues, like virus damage or system errors.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Rackcdn.com. Follow these steps
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Rackcdn.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Technical support scams. Wikipedia. The free encyclopedia.
- ^ Tim Hannon. Social Engineering Scams Are The Easiest Way to Hack Into Your Mac. Soundsupport. Computer basics.
- ^ Virusai. Virusai. Spyware related news.












