Ragnarok ransomware (Free Guide) - Decryption Steps Included
Ragnarok virus Removal Guide
What is Ragnarok ransomware?
Ragnarok ransomware is the threat that marks encoded data with a .thor file extension after encryption
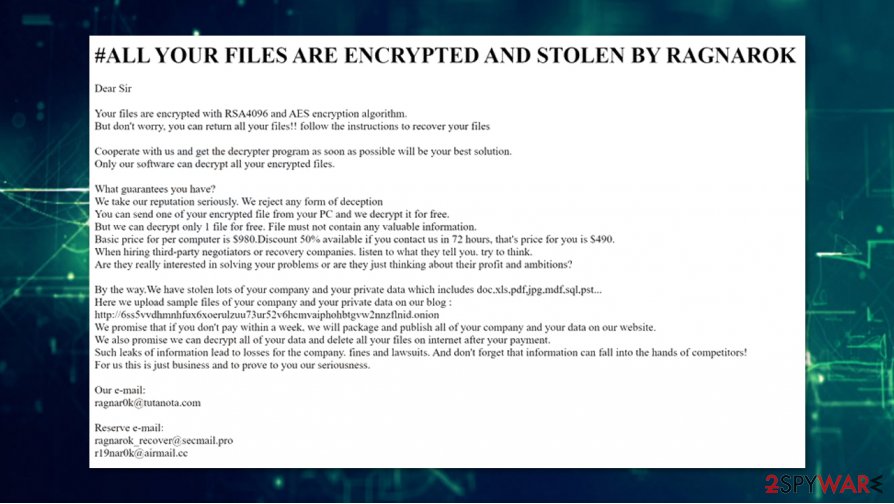
Ragnarok ransomware is the cryptovirus that encrypts audio, video, image files, documents, databases, archives, and other common file types, so developers have a reason to demand large payments for the alleged file recovery. The ransomware delivers a note called “!!Read_me_How_To_Recover_My_Files.html” – it provides more details to victims and asks them to contact the attackers via ragnar0k@tutanota.com ragnarok_recover@secmail.pro, or r19nar0k@airmail.cc emails.
All the Ragnarok virus encrypted files are modified with an extension and a unique identifier. For example, a file “picture.jpg” is transformed into “picture.jpg.T1FURFU.thor,” and can no longer be accessed by victims. Just as it is the case with any other ransomware, the attackers demand a ransom of $980, with a 50% discount available if contacted within 72 hours of the infection. Unfortunately, no free decryption tools are currently available for this malware.
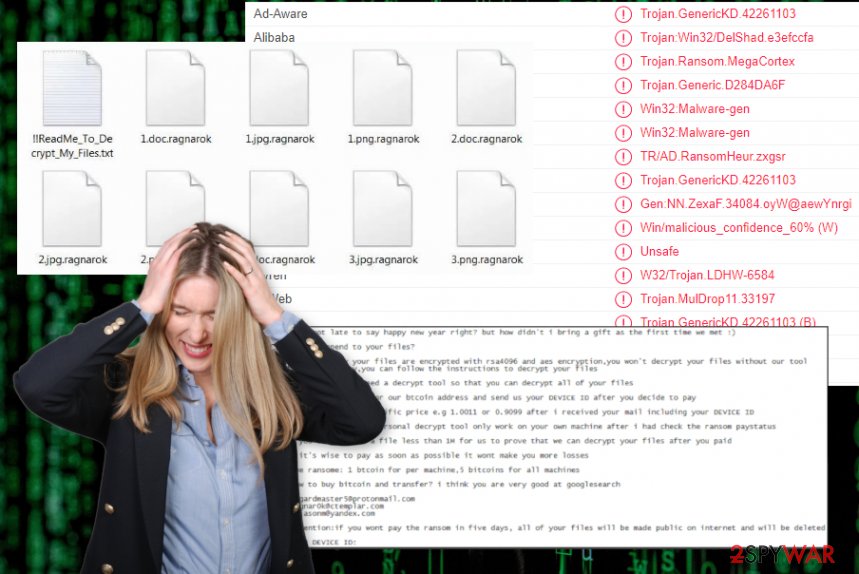
The initial version of the Ragnarok files virus was deployed in mid-January 2020 when a researcher Karsten Hahn[1] reported seeing the strain being involved in attacks against companies and their customers.[2] It appended .ragnarok_cry or .ragnarok extensions, although later variants use names of other known mythological Nordic gods, e.g., Odin. Malware is also known for its ability to avoid infecting users and companies from countries such as China, Kazakhstan, Russia, Ukraine, Moldova, and others.
| Name | Ragnarok ransomware |
|---|---|
| File marker | .ragnarok_cry, .ragnarok, .rgnk, .odin |
| Ransom note | How_To_Decrypt_My_Files.txt, !!Read_me_How_To_Recover_My_Files.html |
| Contact email | asgardmaster5@protonmail.com, ragnar0k@ctemplar.com, ragnarok_master@protonmail.com, ragnarok@rape.lol, yawkyawkyawk@cock.li, ragnar0k@tutanota.com, ragnarok_recover@secmail.pro, r19nar0k@airmail.cc |
| Distribution | Threat gets delivered via spam email campaigns with infected email attachments and by exploiting various vulnerabilities that allow attackers to get into targeted systems and execute needed malicious processes |
| Symptoms | The virus gets on the machine and encrypts various files in common types like photos, videos, documents. Then files get marked and the ransom note delivered with an encouraging message to pay up |
| Danger | Ransomware can freely run in the background, affect functions, processes and disable some functions of the system to keep the persistence. Also, ransomware behavior involves blackmailing and often leads to loss of money or personal data |
| Elimination | To delete Ragnarok ransomware, you need a proper anti-malware tool. Such software can detect threats and clean the machines |
| Repair | Malware can affect processes and damage important files besides the encryption, so get a PC repair tool or a system optimizer and run it to fix such damage. Try FortectIntego |
The name of this Ragnarok ransomware virus was in the headlines of news sources when it was discovered that specific vulnerability in the Citrix Application Delivery Controller allowed attackers to execute the arbitrary code and install malware on the targeted network. The company released patches for their software and the particular CVE-2019-1978 flaw, but many potential victims may not get the patch for their software or might already be affected by the cryptovirus, so you if you might be one of them, take actions immediately.
Ragnarok ransomware infection spreads with the help f payload droppers that initiate the installation of the threat when the malicious script gets triggered by enabling the macro viruses or when the other malware injects already infected machine with a payload of cryptovirus. Once it gets on the machine t can run in the background and change needed system settings or disable/ install programs and functions. However, the first and the most dangerous, noticeable feature if this type of malware is encryption.
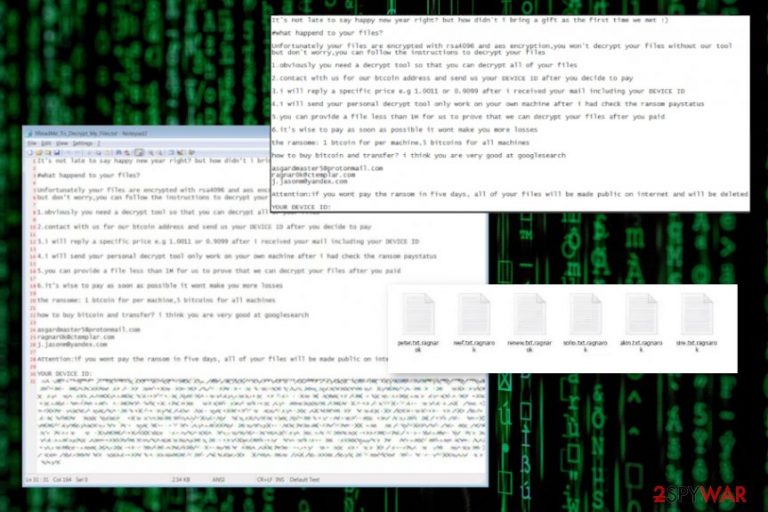
Ragnarok ransomware changes the original code of the chosen data by relying on the encryption algorithms that allow the virus to make files useless and unopenable. When that is done, the virus shows instructions in the form of a text file, in this case, named How_To_Decrypt_My_Files.txt that presents the following message to victims:
#what happend?
Unfortunately your files are encrypted, To decrypt your files follow the instructions
1. you need a decrypt tool so that you can decrypt all of your files
2. contact with us for our btc address if you want decrypt your files or you can do nothing just wait your files gona be deleted
3. you can provide a file which size less than 3M for us to prove that we can decrypt your files after you paid
4. it is wise to pay in the first time it wont cause you more lossesDEVICE ID:
—————————-
–
—————————-you can send your DEVICE ID to mail address below
asgardmaster5@protonmail.com
Even though all the claims seem convincing and the message scares you into consideration to pay these criminals, there is no reason to pay extortionists, especially, when money is the only aim of such malicious actors. You should remove Ragnarok ransomware instead and try to recover the system back to normal to restore those encrypted files using third-party programs or some system functions that could help.
The best way to react after you got affected by a threat like Ragnarok ransomware is to gather some of those encrypted files alongside other data related to this infection and store on an external drive, in case, decryption tool will be released by some experts[3] or malware researchers. Then you should get a tool falling into the anti-malware software category and scan the system fully.
Ragnarok ransomware removal cannot be that difficult, especially when AV detection is pretty high for the payload of this particular cryptovirus. That means that most of the anti-malware available to this day can find the threat and remove it from the machine, you just need to choose the proper program and run a full system scan. Then follow the suggested steps and clean the system from malware traces.
Unfortunately, Ragnarok ransomware is not the threat that only encrypts files ad awaits for payment transfers to come. Extorsiotinsts want victims to pay for the alleged restoration of files but there are more changes the threat manages to do in the background of the system to keep running on the device.
Ragnarok ransomware can make entries in the Windows registry, launch and repress processes in the system, inject other malware directly or open backdoors for remote access. There are many versions of secondary payload that ransomware can execute behind the victim's back and do that successfully while the person is focusing on recovering those encoded files. Some files can get deleted to keep fewer data recovery methods for the person.
Nevertheless, altering those parts of the system yourself can be as damaging as the changes the virus does on the machine, so we don't recommend searching for manual solutions with virus damage as well as with the termination of this infection. To tackle those affected parts and damaged data, get a tool that can run a scan on the system and find changes that Ragnarok ransomware did. FortectIntego could be the tool that finds and fixes damaged files for you. Then you can be sure that ransomware is not going to renew itself and that your recovered files are safe. 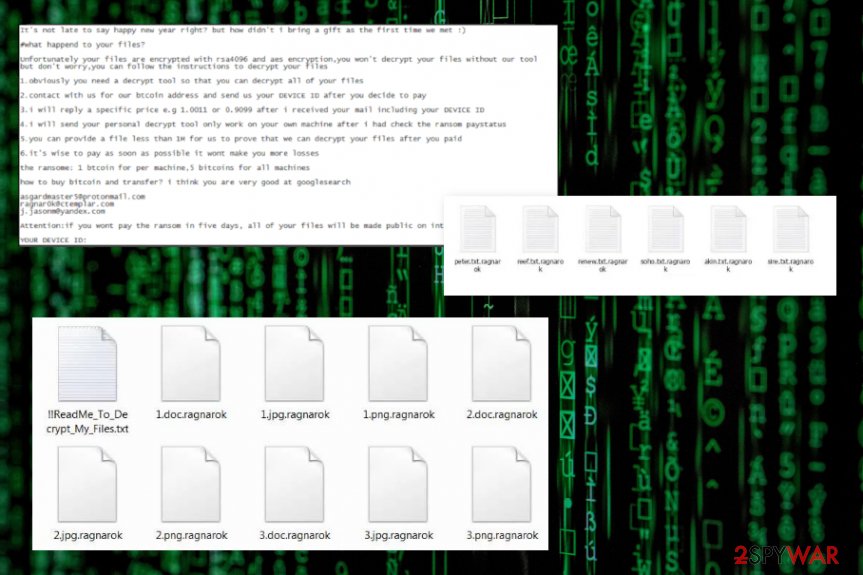
Pay attention to details and avoid malware infiltrations
When you get emails on the daily, you should consider every one of them as potential spam and pay attention to the sender and the topic before you even get to open the notification. If you are not expecting to get financial information-related emails from a company or service, you should never open such a message.
Malicious actors use company names, services, government agencies to trick people that they have received an order or receipt details, payment information and so on, so the victim falls for the scam. Once the message is opened and the file attached to the email downloaded the only step left is to enable macros or visit the linked URL. Users often go straight to the suggested step and do that without thinking.
You need to look out for any misspelled company names, typos or grammar mistakes and letters from companies you don't have a relation with. This is how you can avoid serious infections. Also, keeping the system virus free with a proper anti-malware or security tool.
Prepare for file recovery be eliminating Ragnarok ransomware completely
Ragnarok ransomware virus may disable your AV tools like Windows Defender and other security programs, so it is easier to perform malicious operations, so you may need to enter the Safe Mode with networking to fully detect and remove the threat from the machine. You can find instructions on that below.
When you enter the safe mode, you can freely run the anti-malware tool of your choice and remove Ragnarok ransomware using the software designed to detect malicious threats and indicate the dangerous behavior. SpyHunter 5Combo Cleaner or Malwarebytes could be the programs that we recommend using, but feel free to select a reliable program yourself.
The only tip from us for the best Ragnarok ransomware removal would be choosing trustworthy professional tools. You cannot remove such malware yourself, so the less damage is left the better. AV tools remove malware from the machine and the applications designed to optimize the performance like FortectIntego can fix the damage and repair additional system changes that malware caused.
Getting rid of Ragnarok virus. Follow these steps
Manual removal using Safe Mode
Reboot the machine in Safe Mode with Networking to eliminate Ragnarok ransomware completely with your AV tool
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Ragnarok using System Restore
Try System Restore feature as a method of Ragnarok ransomware removal
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Ragnarok. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Ragnarok from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Ragnarok, you can use several methods to restore them:
Data Recovery Pro is a great alternative for file recovery procedures
Try this program for encrypted or accidentally deleted files and get your data back
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Ragnarok ransomware;
- Restore them.
Windows Previous Versions feature is the method helping to restore encoded files
When System Restore gets enabled, you can use Windows Previous Versions and recover files encrypted by Ragnarok ransomware
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer is the possible solution for file recovery
When ransomware is not damaging Shadow Volume Copies, you can restore encrypted files using ShadowExplorer
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
There is no official tool for Ragnarok ransomware decryption
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Ragnarok and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Matt Bromiley, Christopher Glyer, Andrew Thompson. Nice Try: 501 (Ransomware) Not Implemented. Fireeye. Threat researcher reports.
- ^ Karsten Hahn. Ragnarok report. Twitter. Social media platform.
- ^ Virusai. Virusai. Spyware related news.







