RaRansomware (Virus Removal Guide) - Free Instructions
RaRansomware Removal Guide
What is RaRansomware?
RaRansomware – a cyberthreat that encrypts users' files, but is not fully developed yet
RaRansomware is a crypto-locker that recently emerged in the cybersecurity scene. The virus uses a combination of AES-128 and the RSA-1028 ciphers[1] to encrypt data and appends a set of five different letters to each of the affected files. For example, a picture.jpg would be turned into picture.KUAJW or picture.EGENH after encryption. Alternatively, it can add .XVNAW file extension to the target data. However, the ransom note stays the same with both variants – the .html file is called RaRansomware – recovery instructions. It seems like the virus fails to delete Shadow Volume Copies, making the data recovery possible without paying the ransom.
| SUMMARY | |
| Name | RaRansomware |
| Type | Ransomware |
| Encryption algorithm | AES-128 and RSA-1028 |
| File extension | .[random 5 letters]; .xvnaw |
| Ransom note | RaRansomware – recovery instructions.html |
| Distribution | Spam emails, malicious websites, unprotected RDP, etc. |
| Detection and elimination | Use FortectIntego or Malwarebytes |
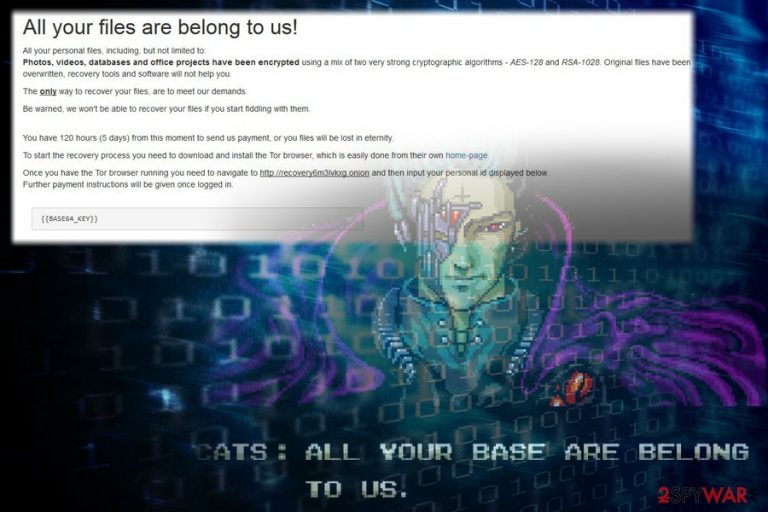
Security researchers noted[2] that the ransom note initially fails to load correctly. Nevertheless, after the machine restart, victims can read the instructions just fine. The message from RaRansomware authors states the following:
All your files are belong to us!
All your personal files, including, but not limited to:
Photos, videos, databases and office projects have been encrypted using a mix of two very strong cryptographic algorithms – AES-128 and RSA-1028. Original files have been overwritten, recovery tools and software will not help you.
The only way to recover your files, are to meet our demands.
Be warned, we won't be able to recover your files if you start fiddling with them.
You have 120 hours (5 days) from this moment to send us payment, or you files will be lost in eternity.
To start the recovery process you need to download and install the Tor browser, which is easily done from their own home-page.
Once you have the Tor browser running you need to navigate to hxxp://recovery6m3lvkxg.onion and then input your personal id displayed below.
Further payment instructions will be given once logged in.
Hackers seem to be familiar with the popular internet meme “All your base are belong to us”[3] and are gladly using it in their note, which adds a bit of humor to the whole thing. Sadly, not everybody is laughing, as victims whose files are encrypted are in that danger of losing them permanently. Or at least it might seem so…
If you got your files encrypted by this cyber threat, do not panic. We suggest you remove RaRansomware virus from your computer first and then proceed with the data recovery. As we already mentioned, the malware attempts to delete Shadow Volume Copies but fails, making file decryption possible without paying the ransom.
As the ransom note states, users have only five days to fulfill cybercriminals' demands. According to RaRansomware authors, users should download TOR browser from the official site and navigate to hxxp://recovery6m3lvkxg.onion in order to receive further instructions.
Cybersecurity experts[4] noted that the trend of using TOR browser increased over the past few years, as it ads an extra layer of security and anonymity. Additionally, crooks avoid using an email address which, in some cases, might be traced. However, do not associate with bad actors, as nothing good will come out of it.
Just think about it, RaRansomware ransomware creators managed to lock up your files in deceptive ways, don't you think they might try something fishy again? For example, they might send you a malware-ridden file which will inject your PC with other viruses, such a keylogger or crypto-mining malware. What is more, it indicates that you are willing to pay, and increases chances of future attacks.
All in all, this crypto-virus does lock your files, that has many bugs which make it less dangerous. Nevertheless, we suggest you take it seriously regardless and take care of RaRansomware removal using powerful security software. We recommend using FortectIntego or Malwarebytes, but you can also pick any other legitimate tool of your liking.

Avoid ransomware viruses – be careful online
Ransomware and cryptomining malware have been the most prominent and dangerous malicious software in recent years, capable of destroying not only personal files but also affecting reputable worldwide organizations, such as the British NHS, Cockrell Hill Police Department, and even various international banks, causing millions of dollars in damages and disrupting operation.
Therefore, you should think twice before carelessly opening questionable spam emails, visiting suspicious file-sharing sites or using the same passwords for multiple accounts. The key to online safety is cautiousness, and it is worth investing time and money into it, as it can lead to devastating consequences in some cases. Of course, if none of the information on your PC is important to you, you might as well ignore all the warnings.
Users should also be aware that crooks often abuse software vulnerabilities to get the malicious payload into the targeted device. Software developers often release updates that patch the weak spots, preventing from hackers to do their malicious deeds. Thus, patching software on time is essential.
Finally, if you do not possess anti-malware software, you need to install it straight away. Without security tools, your machine is extremely vulnerable to various online infections.
Terminate RaRansomware using security software
Ransomware viruses may be tricky to delete sometimes, as they use several evasion methods, such as denying security software operation, deleting its main executable after establishment, etc. Nevertheless, you can bypass malware's evasion techniques by entering Safe Mode with Networking. It is a diagnostic startup mode which only launches the absolutely necessary drivers and services to start the OS, thus, limiting the capabilities of malware.
Nevertheless, the Safe Mode might be not necessary to remove RaRansomware virus (it depends on its capabilities). Therefore, firstly scan your machine in normal mode, and see how it goes.
If RaRansomware removal is successful, proceed with file recovery. Below you will see several third-party programs you can use (we advise to take a great interest into ShadowExplorer, as, if the malware failed to remove Shadow Volume copies, it is a perfect tool to recover your data).
Getting rid of RaRansomware. Follow these steps
Manual removal using Safe Mode
To delete RaRansomware without problems, enter Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove RaRansomware using System Restore
You can use System Restore to eliminate the malware:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of RaRansomware. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove RaRansomware from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.We strongly suggest trying third-party software for file recovery. Do not contact hackers as they are likely to attack you in the future, knowing that you are willing to pay.
If your files are encrypted by RaRansomware, you can use several methods to restore them:
Use Data Recovery Pro to get access to your files
You can try using Data Recovery Pro, as it was proven to be useful when dealing some ransomware-infected files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by RaRansomware ransomware;
- Restore them.
Try Windows Previous Versions Feature
This method can only be used if you had System Restore function enabled before the virus attack.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer can be the answer
As the virus fails to eliminate Shadow Volume Copies, we strongly advise you picking this tool for file recovery.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No official decryptor have been created yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from RaRansomware and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Encryption Algorithm. Technopedia. Site that helps to understand technology.
- ^ Karsten Hahn. RaRansomware. Twitter. Social Network.
- ^ All your base are belong to us. Wikipedia. The Free Encyclopedia.
- ^ Viruset. Viruset. Cybersecurity news and articles.







