Read-before-the-rest.com ads (spam) - Chrome, Firefox, IE, Edge
Read-before-the-rest.com ads Removal Guide
What is Read-before-the-rest.com ads?
Read-before-the-rest.com displays fake messages to trick users
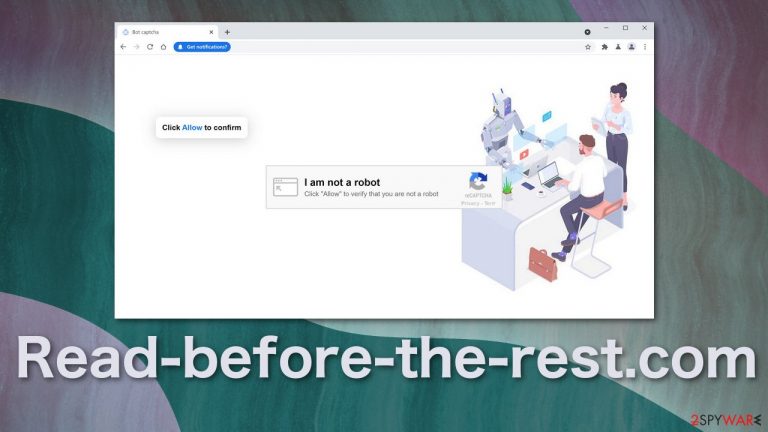
Read-before-the-rest.com is a dubious website created by shady individuals that want to generate revenue from pay-per-click advertising.[1] The page shows false messages trying to trick users into agreeing to receive push notifications from the site. These are used to deliver pop-up ads straight to users' screens.
Because the creators of the page do not care about user safety and security, the ads are not filtered in any shape or form, so among legitimate ads, you might see ones created by scammers, which raises many concerns. Social engineering methods[2] have been widely adopted by shady individuals, and it is easy to manipulate people. Many might not know if the ad is a scam and click on it.
Dangerous pages opened from links in the notifications can lead to users providing their personal information, which can result in monetary losses and identity fraud[3] or them downloading potentially unwanted programs or even malware. The sad truth is that fraudsters do not even need to have hacking capabilities anymore because the manipulation tactics they use make users let in uninvited guests themselves.
| NAME | Read-before-the-rest.com |
| TYPE | Push notification spam; adware |
| SYMPTOMS | Pop-up ads start appearing in the corner of the screen, sometimes even when the browser is closed |
| DISTRIBUTION | Shady websites, deceptive ads, freeware installations |
| DANGERS | Links embedded in the notification prompts can lead to dangerous websites created by scammers, which put users at risk of suffering from monetary losses |
| ELIMINATION | You can block push notifications via browser settings or remove adware by scanning your machine with anti-malware tools |
| FURTHER STEPS | Use FortectIntego to eliminate any remaining damage, fix errors, and optimize performance |
Manipulation tactics fraudsters use to make people subscribe
Push notifications are based on a subscription model, so users need to grant the website permission themselves to start receiving them. The trick is, the messages that pages like Read-before-the-rest.com display:
Type Allow to verify that you are not a robot
Click Allow to watch the video
Download is ready. Click Allow to download your file
Press Allow to verify that you are not a robot
As you can see, some of the messages remind of a captcha verification process where users are required to write letters from the picture, tick a box, or pick photographs that have a certain object in them. But that is not what these websites have. Most often, they just display the text and a picture of a robot. The authors have configured the site settings to make the browser ask users that visit the web page for the first time to display a prompt that says the website wants to send push notifications.
Under the text, in the box, users have 2 options – “Allow” or “Block.” The thing is that people do not come to Read-before-the-rest.com on their own through the search results. The site is advertised in various other shady sites full of deceptive ads and redirects. If users are careless and click on random buttons and ads, they might have been directed to this page and think that it belongs to the previous page they were on and need to perform a check to access the content they were looking for.
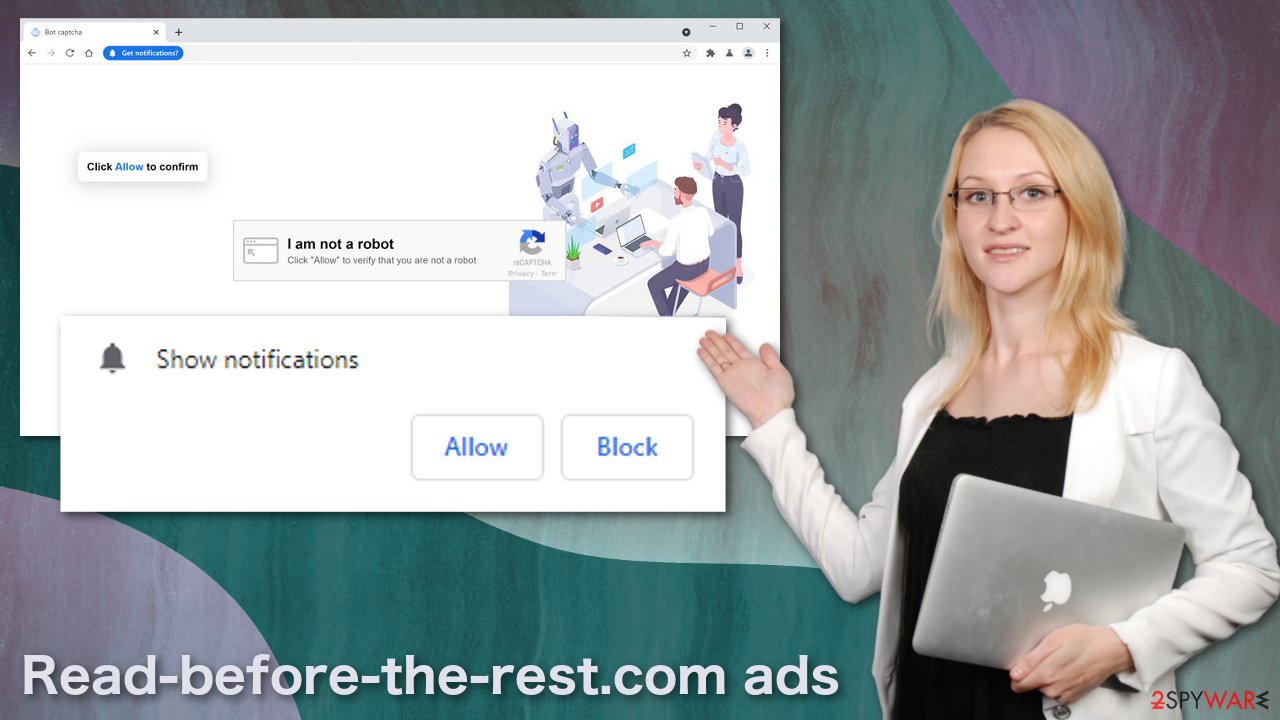
Of course, after clicking the “Allow” button, nothing happens, or users get redirected to another similar site. There is nothing more to explore on the site as it only has that one page and settings configured to send push notifications containing ads. The page creators receive a cut every time you click on it.
End the subscription
As we talked about before, push notifications are subscription-based, which means that you can terminate them anytime. Doing that should be easy via browser settings:
Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.

- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).

Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click Settings button next to it.

- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

Safari:
- Click on Safari > Preferences…
- Go to Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

MS Edge:
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.
- Toggle the switch to the left to turn notifications off on Microsoft Edge.

MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Internet Explorer:
- Open Internet Explorer, and click on the Gear icon at the top-right on the window.
- Select Internet options and go to Privacy tab.
- In the Pop-up Blocker section, click on Settings.
- Locate web address in question under Allowed sites and pick Remove.

After you get rid of those intrusive pop-ups, you should take care of your browsers because of the shady pages you visited. They could still be tracking your browsing activity and selling it to advertising networks. You can let FortectIntego do the job for you automatically. This repair tool can fix any remaining damage and delete cookies and cache as well as improve the machine's performance.
The growing problem of adware
If you get redirected to pages similar to Read-before-the-rest.com quite often and see an increased amount of commercial content like pop-ups, banners, surveys, and similar, that might mean you are infected with adware which is a PUP capable of placing ads on your device and generating revenue from it.
The most likely way it gotten on your system is through bundled software.[4] Those who download freeware from unofficial sites should be more careful because these pages seemingly provide a free service, but they are not doing it for free. Free software distributors thought of other ways to monetize customers – by including additional programs in the installer that are programmed to perform tasks in the background.
Most of the users do not notice them and do not know about them because they rush through the installation process. That is why we recommend using only official sources and app stores for installing software, but we know that is not always possible, so you should at least should be more careful about it by implementing certain habits in your daily routine:
- Always choose the “Custom” or “Advanced” installation method
- Do not rush and go through all the steps
- Read the Terms of Use and Privacy Policy
- Untick the boxes next to programs or files that seem unrelated and not needed
Having professional security software on your device is also very helpful. If you download one of these applications, it is hard to detect them because they can be disguised as anything. SpyHunter 5Combo Cleaner and Malwarebytes can scan your device and automatically detect suspicious programs as well as prevent such infections in the future by warning you.
If you know for sure you have been infected with a PUA and know the name of it; you can follow manual instructions for Windows and macOS below this article.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Read-before-the-rest.com ads. Follow these steps
Uninstall from Windows
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Read-before-the-rest.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Pay-Per-Click Advertising: What Is PPC & How Does It Work?. WordStream. Advertising Solutions.
- ^ 9 Examples of Social Engineering Attacks. TerranovaSecurity. Cyber Security Awareness. Phishing.
- ^ Online Identity Theft. WebRoot. Cybersecurity Resources. Tips.
- ^ Liam Tung. Google: Unwanted bundled software is way more aggressive than malware. ZDNet. Security.
