RedFox ransomware (Removal Guide) - Jul 2018 update
RedFox virus Removal Guide
What is RedFox ransomware?
Redfox ransomware – a cryptovirus which is spread as RaaS and can be purchased on the Internet
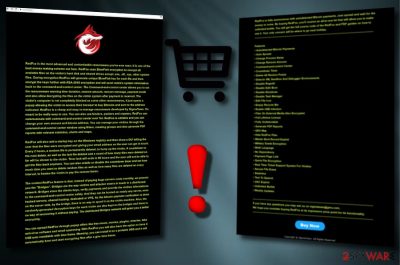
RedFox ransomware is a malicious virus which encrypts most important data on its victim's computer right after infiltrating it. It is spread as a RaaS (also known as Ransomware as a Service),[1] so its developers are giving a chance for hacker-wannabes to earn money by spreading this malware around and, in case of success, cutting some part of the ransom for themselves. At the moment, it is sold for 0.1 in bitcoin cryptocurrency. However, keep in mind that dealing with hackers is highly dangerous, no matter which side you are in. The RedFox virus is encrypting files by appending .redfox extension to each of them. Additionally, it drops a ransom note where the owners of this program are presenting themselves as the SigmaTeam.
| Name | RedFox |
|---|---|
| Type | Ransomware/Cryptovirus[2] |
| Spreads as | RaaS (Ransomware as a Service) |
| Extension | .RedFox, e.g. beautifulhouse.png turns to beautifulhouse.png.redfox |
| Ransom note | The name is different in each ransomware because different cybercriminals create their own ransom notes |
| Distribution ways | Spam, malicious online websites. |
| ELIMINAtion | FortectIntego is the best help for the cryptovirus elimination. |
According to IT professionals[3], this cryptovirus can be spread in various ways – by spam, fraudulent websites, and similar techniques typically used for malware distribution. Once installed and encrypts target files, the virus drops a ransom note which demands the ransom in exchange for encrypted files' decryption. The virus also announces that computer is infected by RedFox ransomware and all files cannot be used because of the specific encryption algorithm. It also says that the only way to restore encrypted files is by obtaining the decryption key which can be purchased straight from the cybercriminals by paying a demanded ransom.
However, be careful and do not pay the required fee. Many desperate users do, and, as a result, find themselves scammed. To avoid such consequences, you need to remove RedFox ransomware virus from your computer system permanently by using an anti-malware program. We recommend downloading FortectIntego or any other similar tool. It will show you some guidance, how to get rid of the cyber threat. Additionally, you can move to the recovery of your files.
It is known that RedFox ransomware has been spread via sigmateam[dot]neocities[dot]org web domain. Note that we do NOT recommend visiting it because such sites are highly dangerous and can infect you with malware. Hackers have been promoting their software by highlighting these features:
- Autodetected Bitcoin Payments
- Change Ransom Amount
- Command-and-control Center
- Countdown Timer
- Delete All Restore Points
- Disable Safe Boot
- Disable Shutdown
- Disable Task Manager
- Empty Recycle Bin
- Enable USB Infection
- GEO Map
- Hide RedFox Files
- Multi-Language
- No Dependency
- Payment Page Link
- Unlimited Builds
- Weekly Updates
As you can see, this ransomware-type virus might cause numerous problems when inside the computer system. Make sure you keep yourself protected by installing reputable anti-spyware. If you found yourself infected with this malware, take needed actions and proceed with the Redfox ransomware removal as quickly as possible to avoid unwanted consequences.

Ransomware distribution is mainly implemented thru spam
The cryptovirus (as a way to earn money) is actively promoted on its official website which we do not recommend visiting as you can get infected with ransomware. Additionally, you can easily get it on your system while browsing on dubious pages and downloading fake programs' versions from indirect links.
To continue, ransomware can also spread through spam emails. This is one of the most common ways how Crypto-viruses are distributed. Typically, spam emails look like just regular messages, so there is no surprise that they trick hundreds of users worldwide. Once the victim is tricked into clicking on the provided link or download the attached document, the system gets infected.[4]
If you want to avoid ransomware getting into your system, notice that you have to be cautious and pay attention while browsing on the web. Dangers are all around you, so, most importantly, be accurate and do not click on dubious links, and suspicious-looking shortcuts.
Furthermore, install software only from trustworthy sources, and opt-out of all unnecessary components to stop ransomware, adware and similar unwanted software. Also, avoid opening spam, better delete such fake email messages permanently and stay safe. Last but not least, consider installing an antivirus. It will protect your computer system by performing regular scans and detecting threats before they manage to get into the system. If some infections do occur, the antivirus program will guide you through the whole virus removal process.
Use anti-malware help to eliminate RedFox ransomware from your computer
To remove Redfox ransomware, you will need to download a professional anti-malware program. We suggest using one of these apps that have been tested by our professionals: FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes. These tools will help you repair the damage caused by the cryptovirus. However, they cannot recover data encrypted by RedFox virus. Recovery instructions that could be used to unlock encrypted data are displayed below this article.
However, we should also warn you that RedFox virus removal may not go as smooth as you expect as this is a serious ransomware threat which is trying to prevent its elimination. To disable your malware and prevent it from further harmful actions, follow any of these methods:
Getting rid of RedFox virus. Follow these steps
Manual removal using Safe Mode
Reboot your system to Safe Mode with Networking to disable RedFox from interrupting your scanner:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove RedFox using System Restore
Try using the System Restore feature to disable the harmful ransomware's activity and scan your computer system:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of RedFox. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove RedFox from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by RedFox, you can use several methods to restore them:
Use Data Recovery Pro to fix your infected data
If you don't have backups of your locked data, try using this decryption tool to recover files encrypted by the RedFox ransomware.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by RedFox ransomware;
- Restore them.
Use Windows Previous Version feature to restore individual files
This tool would work only if the System Restored function was enabled. If you are sure that it was, try encrypting individual files with this program.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Use ShadowExplorer if your files are locked
If the Shadow Volume copies were not removed by the cyber threat, you should be able to get your data back with the help of this tool.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
There is no official RedFox decrypter discovered yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from RedFox and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ The Barkly Team. Ransomware-as-a-Service is Booming: Here's What You Need to Know. Barkly Blog. Security news, tips, and trends.
- ^ Crypto-ransomware. F-Secure. Tech info.
- ^ Losvirus ES. Tech tips from the lips of IT experts.
- ^ How Does Ransomware Spread. Cybersight. Latest IT information.





















