Reliablepcmatter.com ads (fake) - Free Instructions
Reliablepcmatter.com ads Removal Guide
What is Reliablepcmatter.com ads?
Reliablepcmatter.com ads attempt to mislead users about their computer security and make them purchase software
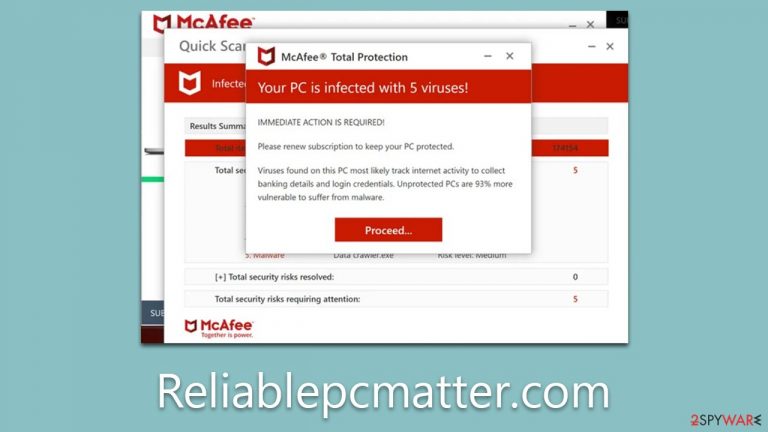
Reliablepcmatter.com is a deceptive website created by cyber felons to extract money from unsuspecting individuals. Users often land on this site either via involuntary redirection caused by adware or through being deceived into clicking a counterfeit link from another website. To enhance its facade of legitimacy, the scam impersonates a malware detection process performed by McAfee antivirus software and, within a short span of time, presents false, distressing results that appear genuine.
In truth, this is a commonplace deceit strategy utilized by a multitude of fraudulent websites. The intention of the creators of Reliablepcmatter.com is to convince users to believe that their systems are plagued with viruses and, subsequently, persuade them to buy antivirus software licenses and enroll for additional services because a seemingly trustworthy vendor has identified malware on their computer systems. This is a quintessential example of scareware, a scheme intended to manipulate people's apprehension of malicious software.
| Name | Reliablepcmatter.com |
| Type | Scam, phishing, redirect, fraud, fake alert |
| Scam content | Claims that the antivirus software license has expired and that the computer is exposed to various malware |
| Distribution | Redirects from other malicious websites, adware |
| Risks | Loss of finances due to fake subscriptions; redirects to other malware-laden, scam websites; installation of potentially unwanted or malicious software |
| Removal | Interacting with the scam content is dangerous, as scammers may promote fake versions of antivirus software. Instead, use reputable tools for your system safety |
| Other tips | Use FortectIntego to clean your system from data trackers and fix any damage done by adware or other malicious software |
Scam scheme explained
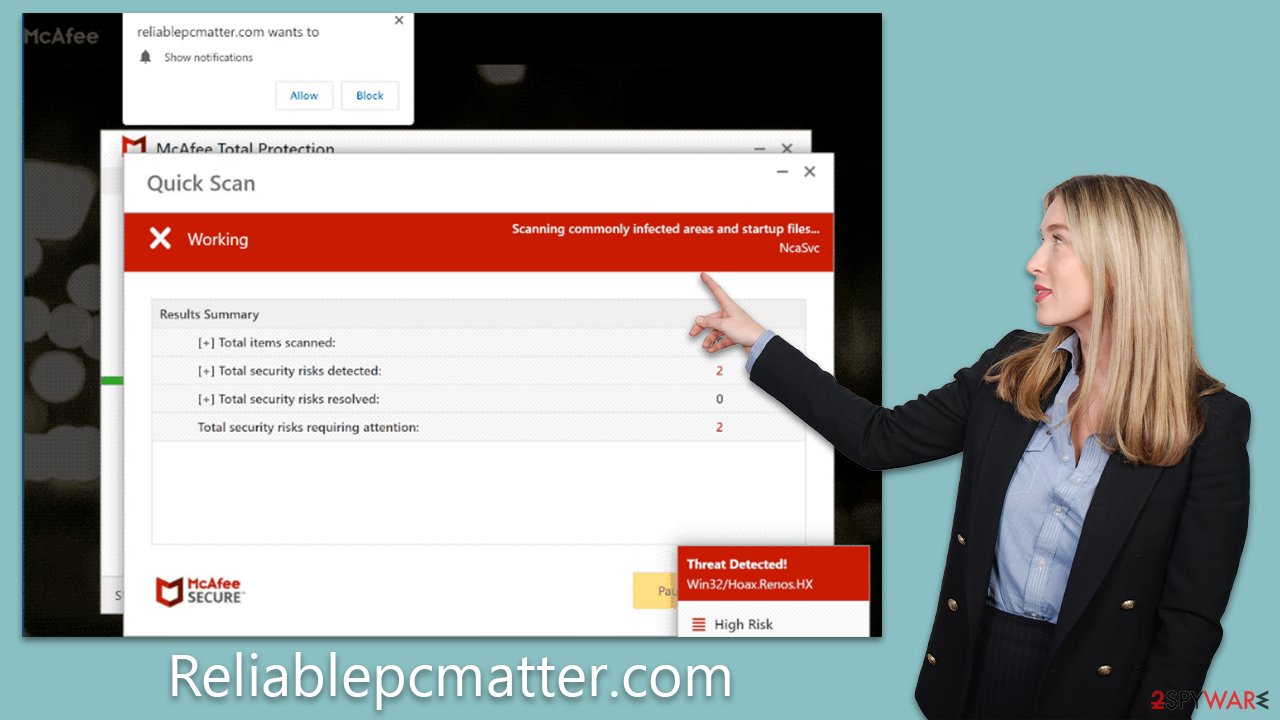
Upon accessing Reliablepcmatter.com, users are initially greeted by a series of pop-up windows that imitate a system scan conducted by the popular security vendor McAfee. Subsequently, they are confronted with an alert proclaiming their system to be teeming with numerous viruses, and to add to the urgency, that their subscription has lapsed, pressuring them to renew promptly to defend their computer from additional viruses and malware.
Nonetheless, this alert is a meticulously engineered deception crafted to incite fear in users and drive them to impulsively purchase the software license. Those who fall into the trap are directed to a webpage where they can acquire the software, thereby financially supporting the fraudsters operating the counterfeit Reliablepcmatter.com site, who gain a commission with every completed transaction.
The pathways leading to the software purchase may not be genuine and could result in the download and installation of potentially undesired or even harmful software onto the user's systems. Moreover, Reliablepcmatter.com might also attempt to coerce users into enabling push notifications, potentially resulting in the reception of intrusive pop-ups at any given moment when the browser is active. This article provides comprehensive information on how to discontinue these notifications and effectively eradicate adware from your system.
It's essential to remain vigilant when interacting with such websites. The scare tactics employed are designed to exploit your fear and push you into hasty decisions. Instead, always seek professional advice if you suspect that your system might be compromised. Remember, real security providers will never scare you into purchasing their products, and any such attempt should be considered a red flag. Always take time to validate the authenticity of the information presented to you, and never hastily give out personal or financial information.
Check your system for adware
Despite the fact that the system checks run by Reliablepcmatter.com scam are entirely fabricated (providing the same output to each user), it remains critical to conduct authentic system scans to ensure there isn't any malevolent or potentially unwanted software operating covertly.
If you have downloaded anything from Reliablepcmatter.com, your device could be at risk of adware infection. Even if you haven't downloaded anything, it's still prudent to perform a check, as users might have been exposed to phishing attempts due to this program's presence on their systems.
To ensure that the most insidious, surreptitious infections are eliminated promptly, it's crucial to perform a comprehensive system scan using a reputable anti-malware tool like SpyHunter 5Combo Cleaner or Malwarebytes. Furthermore, you can manually search for installed unwanted programs, but remember, these may not always be visible on the list of installed applications. Following these steps will help identify and remove all instances of adware and malware.
Subsequently, it's crucial to cleanse your browser caches – cookies, and other trackers could be employed to monitor your activities. This can be accomplished by executing a scan with FortectIntego repair tool or by adhering to these specific steps:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Getting rid of push notifications
If you have inadvertently permitted push notifications from Reliablepcmatter.com, there's a high likelihood that you will begin to receive intrusive pop-up alerts that could disrupt your ongoing activities on your computer. These notifications can potentially contain links leading to malicious sites, and thus, it's absolutely crucial that you refrain from interacting with them under any circumstances.
These pop-ups aren't just irritating; they pose a real security risk. By clicking on the links they provide, you may unintentionally download harmful software or provide sensitive information to unscrupulous individuals. Therefore, it's vital to take immediate action to stop these notifications from appearing.
To eliminate these bothersome pop-ups, you need to block the originating website through your browser settings. Each browser has its own specific way to manage website notifications, but generally, you can find these settings in the privacy or security section. By locating Reliablepcmatter.com in these settings, you can block all notifications, effectively ending the bombardment of pop-ups. If you need full instructions, follow these steps:
Google Chrome
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and choose Block. This should remove unwanted notifications from Google Chrome.

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
