RotorCrypt ransomware / virus (Removal Guide) - Oct 2018 update
RotorCrypt virus Removal Guide
What is RotorCrypt ransomware virus?
RotorCrypt is a file locking virus which was recently spotted using with .!@#$%^&-()_+.1C file extension
RotorCrypt is a cryptovirus that was first spotted in 2016 and since then is known as ransomware[1] that uses obnoxious file extensions and ransom notes. Unsurprisingly, the malware is closely related to Rotor virus, as the name suggests. Since its initial release, cybercriminals have presented countless versions of the virus, using spam email campaigns, exploits, weak passwords and similar means for distribution. The latest variant of RotorCrypt ransomware was discovered by the independent researcher on 10th of October. It uses .!@#$%^&-()_+.1C file extension and drops a ransom note INFO.txt, which is written in the Russian and only information stated is two contact email addresses: inkognitoman@tutamail.com and inkognitoman@firemail.cc.
| Name | RotorCrypt |
| Type | Ransomware |
| Alternatively known as | Rotor virus, Ransom.FileCryptor, Trojan-Ransom.Win32.Rotor.b, Win32/DH{gVIDgQ5+gUaBDw?} |
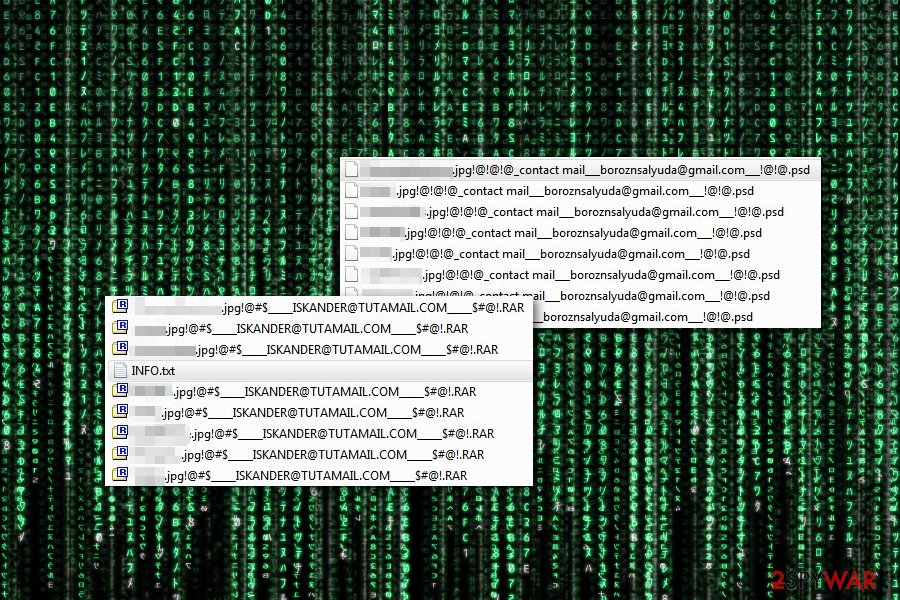
| Extensions used to mark encrypted files | Encrypted files can be found by looking at these extensions: .SPG, .PGP, .tar, .c400, .c300, .crypto, .mail, .psd, .RAR, . !@!@!@_contact mail___boroznsalyuda@gmail.com___!@!@.psd and !@#$_____ISKANDER@TUTAMAIL.COM_____$#@!.RAR; .!@$#-unlock-email_______zepro190@gmail.com________#$!…ES_HELPs, .!@#$%^&-()_+.1C |
| Ransom size | 7 BTC in early versions; 1-3 BTC in later versions |
| Detection and elimination | Use security software to get rid of malicious files. We recommend FortectIntego and SpyHunter 5Combo Cleaner |
| Decryptable | No. At the moment, files encrypted by this ransomware can be recovered only with the help of third-party programs or from back up |
RotorCrypt ransomware spreads via malicious spam emails as an obfuscated “dead rdp.exe” file. However, different versions of the virus might have differently named payloads. Furthermore, malware mainly targets Russian-speaking users[2], and once it gets into their computers, it starts data encryption process. It is known to target the following file types:
.1cd, .avi, .bak, .bmp, .cf, .cfu, .csv, .db, .dbf, .djvu, .doc, .docx, .dt, .elf, .epf, .erf, .exe, .flv, .geo, .gif, .grs, .jpeg, .jpg, .lgf, .lgp, .log, .mb, .mdb, .mdf, .mxl, .net, .odt, .pdf, .png, .pps, .ppt, .pptm, .pptx, .psd, .px, .rar, .raw, .st, .sql, .tif, .txt, .vob, .vrp, .xls, .xlsb, .xlsx, .xml, .zip
Different versions of RotorCrypt virus seems to be using RSA encryption[3] and can append one of the file extensions listed below. Cyber criminals design long and complicated suffixed that include contact email address:
- .-.DIRECTORAT1C8@GMAIL.COM.roto>
- .-.DIRECTORAT1C@GMAIL.COM.roto>
- .-.directorat1c@gmail.com.roto
- .-.CRYPTSb@GMAIL.COM.roto>
- !-==kronstar21@gmail.com=–.crypt>
- !==helpsend369@gmail.com==.crypt>
- !__crypthelp12@gmail.com_.crypt
- !___prosschiff@gmail.com_.crypt>
- !____moskali1993@mail.ru___.crypt>
- !______sufnex331@gmail.com______.crypt
- !______bigromintol971@gmail.com______.crypt
- !_______GASWAGEN123@GMAIL.COM____.crypt
- !_________pkigxdaq@bk.ru_______.crypt
- !______________DESKRYPTEDN81@GMAIL.COM.crypt
- !____GLOK9200@GMAIL.COM____.tar
- !____cocoslim98@gmail.com____.tar
- !_____GEKSOGEN911@GMAIL.COM____.c300
- !_____DILINGER7900@GMAIL.COM_____.GRANIT
- !____hamil8642@gmail.com___.GRANIT
- .edgar4000@protonmail.com____.granit
- !______DILIGATMAIL7@tutanota.com______.OTR
- !______PIFAGORMAIL@tutanota.com______.SPG
- _______PIFAGORMAIL@tutanota.com_____.rar
- !_____INKASATOR@TUTAMAIL.COM____.ANTIDOT
- !-=solve a problem=-=grandums@gmail.com=-.PRIVAT66
- !==solve a problem==stritinge@gmail.com===.SENRUS17
- !_____FIDEL4000@TUTAMAIL.COM______.biz
- !____________DESKRYPT@TUTAMAIL.COM________.rar
- !____________ENIGMAPRO@TUTAMAIL.COM_______.PGP
- !___________ANCABLCITADEL@TUTAMAIL.COM__________.PGP
- !==SOLUTION OF THE PROBLEM==blacknord@tutanota.com==.Black_OFFserve!
- !decrfile@tutanota.com.crypo
- ! ,–, Revert Access ,–, starbax@tutanota.com ,–,.BlockBax_v3.2
- !________INKOGNITO8000@TUTAMAIL.COM_________.SPG
- !_______INKOGNITO7000@TUTAMAIL.COM_______.SPG
- !@#$%___________ PANAMA1@TUTAMAIL.com%$#@.mail
- !@!@!@_contact mail___boroznsalyuda@gmail.com___!@!@.psd
- !@#$_____ISKANDER@TUTAMAIL.COM_____$#@!.RAR
Victims are supposed to contact crooks via provided email and wait for their instructions what should they do next. There's no secret that users are suggested to purchase the specific data recovery tool.[2] Victims can purchase the tool or, in other words, pay the ransom. The first version of RotorCrypt virus urged to transfer 7 Bitcoins, which is now equal to more than 61 000 USD. Newer versions reduced the ransom, which now ranges from 1 to 3 Bitcoins.
RotorCrypt ransomware might be related to Rotor virus. Indeed, their names are familiar, but they also use the same data encryption strategy and do not leave a clear explanation about file decryption possibilities.
Usually, the creators of ransomware provide detailed instructions how to purchase Bitcoins and transfer money using anonymous Tor browser. However, initially criminals did not find this activity necessary, which is why victims are not presented with a ransom note left by Roto Crypt virus that would explain what happened to your files. Newer versions are known for providing more, but still not sufficient, information:
Good day
Your files were encrypted/locked
As evidence can decrypt file 1 to 3 1-30MB
The price of the transcripts of all the files on the server: 7 Bitcoin
Recommend to solve the problem quickly and not to delay
Also give advice on how to protect Your server against threats from the network
(Files sql mdf backup decryption strictly after payment)!
If you have encountered this malware, do not waste your time and initiate RotorCrypt removal. Virus elimination will not bring back your files, but you will be able to try additional data recovery options.

After the attack, victims have to realize to contact criminals by an email address appended to the corrupted filename. There’s no doubt that they will tell that paying the ransom is the only solution to get back access to the files. But we do not recommend contacting criminals and wasting your money because you might end up with both data and money loss.
Remove RotorCrypt from the computer with the help of a strong anti-malware program, such as FortectIntego, SpyHunter 5Combo Cleaner. or any other reputable security software. Keep in mind that virus might block access to the program and prevent it from scanning the system. In this case, follow our step-by-step guide presented at the end of the article. Different security programs detect this computer infection under different names, for instance, Ransom.FileCryptor, Trojan-Ransom.Win32.Rotor.b, Win32/DH{gVIDgQ5+gUaBDw?}, etc.
Latest RotorCrypt variants
Several versions of RotorCrypt ransomware, detected in the beginning of 2018, are known for appending the .!==SOLUTION OF THE PROBLEM==blacknord@tutanota.com==.Black_OFFserve or !decrfile@tutanota.com.crypo file extension to the locked files. However, at the beginning of March 2018, significant changes in RotorCrypt virus coding scheme has been noticed – the new variant appends a ! ,–, Revert Access ,–, starbax@tutanota.com ,–,.BlockBax_v3.2 extension, which contains an atypical number of spaces.
In June and July 2018, researchers have reported about four new versions of the virus that append the following extensions to the targeted data:
- !@#$%___________PANAMA1@TUTAMAIL.com%$#@.mail
- !@!@!@_contact mail___boroznsalyuda@gmail.com___!@!@.psd
- !@#$_____ISKANDER@TUTAMAIL.COM_____$#@!.RAR
- !@$#-unlock-email_______zepro190@gmail.com________#$!…ES_HELPs

However, the following scheme does not change much. Victims can contact cybercriminals using one of the provided email addresses (panama1@tutamail.com, boroznsalyuda@gmail.com or iskander@tutamail.com) and find out the ransom size. So far 53 out of 65 AV engines detect[4] the malicious payload of this RotorCrypt version.
RotorCrypt ransomware showed up again in October 2018, after few months of break. The latest variant yet again uses an obnoxious file extension – .!@#$%^&-()_+.1C. A brief ransom note INFO.txt, written in Russian, only mentions two email addresses to contact malware authors. There are no mentions about the size of ransom or any other information provided. As usual, we recommend not to contact cybercrooks and remove RotorCrypt ransomware instead, using security tools like FortectIntego or SpyHunter 5Combo Cleaner.
Ransomware payload is being spread via malicious spam emails
RotoCrypt virus is distributed via malicious email attachments. It’s the most popular way to spread malware. Unfortunately, many computer users are too curious and open suspicious spam emails. However, opening an email is not the worst part. Usually, emails are not dangerous, but links and documents attached to them might be infected. Once users open Word or PDF file, the malicious GWWABPFL.EXE file, ins.exe, dead rdp.exe or other obfuscated files might be dropped on the system.
However, malicious email attachments are not the only one distribution technique, security specialists from Bedynet.ru[5] says. Malware might get inside when victims install bogus software or fake updates. Some variants of ransomware also use exploit kits[6] and look for flaws in computer’s security.
If you want to avoid RotorCrypt or other file-encrypting viruses, you have to be careful online and doubt every single message you receive in your inbox.[7] Before opening any email attachment, you have to double check the information about the sender. Crooks might pretend to be from reputable or governmental institutions; therefore, you should contact the organization directly and ask about the issue.
Moreover, you should protect your computer by installing a reputable antivirus program and don’t forget to update it regularly. It's important to keep all your programs updated. The easiest way to keep software updates is to let applications download updates automatically. Lastly, you should not browse in high-risk websites, click on clickbait ads or suspicious links. 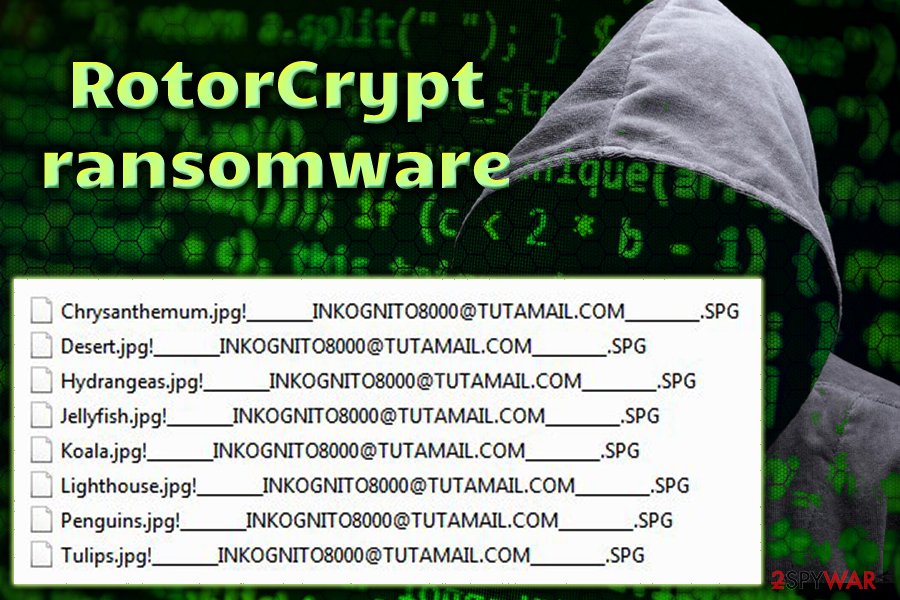
RotorCrypt elimination guide
Ransomware is hard to remove, so you should not consider eliminating the virus manually. In order to remove RotorCrypt safely, you should rely on a professional malware removal program. Keep in mind that free tools are weak and cannot effectively remove this computer infection. Thus, you should install in professional computer's security and choose FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
After successful RotorCrypt removal, you can restore corrupted files from data backups. However, if you do not have them, try our additional data recovery methods presented at the end of the article. Though, we want to warn that you should not have high expectations, as chances to restore files are not high.
Getting rid of RotorCrypt virus. Follow these steps
Manual removal using Safe Mode
If you cannot install a preferred removal tool, reboot your computer to Safe Mode with Networking first. For that, you should follow these steps:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove RotorCrypt using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of RotorCrypt. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove RotorCrypt from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your computer is infected with RotoCrypt, do not consider contacting the crooks and paying the ransom. After virus elimination, recover your files from backups or use alternative methods provided below.
If your files are encrypted by RotorCrypt, you can use several methods to restore them:
Using Data Recovery Pro to recover encrypted files
Data Recovery Pro might be a helpful tool to recover files encrypted by RotoCrypt ransomware. We cannot assure that this method will be effective and decrypt all of your files, but you should give it a try.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by RotorCrypt ransomware;
- Restore them.
Recover files using Windows Previous Versions feature
This method allows restoring individual files after ransomware attack. In order to use this method, follow the instructions below.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Taking advantage of a ShadowExplorer
If ransomware hasn't deleted Volume Shadow Copies, you can try using this method and recover at least some of your files.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
RotoCrypt decryptor is not available yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from RotorCrypt and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Alison DeNisco Rayome. Report: Malicious email attacks jump 85% in Q3, ransomware reigns supreme. TechRepublic. The site delivers a unique blend of original content by IT professionals.
- ^ Derek Brink. Ransomware and Cyber Extortion: What You Need to Know and Do. Security Intelligence. Analysis & Insight on Information Security.
- ^ RSA Encryption. Wolfram MathWorld. The Web's Most Extensive Mathematics Resource.
- ^ 3637c9f27d8599d1c79a1de6f4eb2bf2795f831d43d9d4b0c821e73bdbebafcf. Virus Total. File analysis.
- ^ Bedynet. Bedynet. Malware Removal Guides.
- ^ Omri Toppol. Exploit Kit: What It Is and How To Protect Yourself. LogDog. Cyber security and anti-hacking news.
- ^ Ian Paul. Three warning signs that email is malicious. PCWorld. News, tips and reviews from the experts on PCs, Windows and more.





















