Search.searchtmpn4.com (Easy Removal Guide) - Chrome, Firefox, IE, Edge
Search.searchtmpn4.com Removal Guide
What is Search.searchtmpn4.com?
Search.searchtmpn4.com – a browser hijacker that is often bundled with freeware
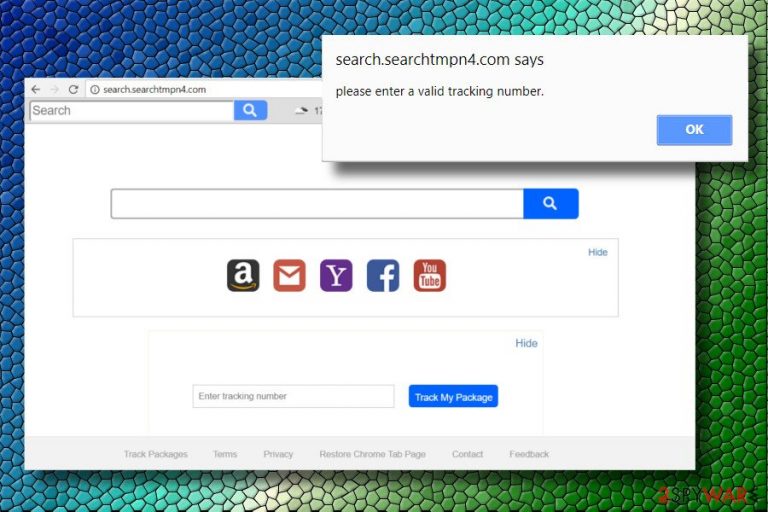
Search.searchtmpn4.com is a search site has been developed by Polarity Technologies Ltd. This company is infamous for the development of thematic web browser extensions that offer services, including but not limited to file converting, currency tracking, video streaming.
In addition to the provision of allegedly more effective searches, it should enable users to track packages. However, even though such a service seems useful, do not count on this search site because it's another marketing-related tool used to maximize third parties' profit.
| Name | Search.searchtmpn4.com |
|---|---|
| Type | Browser hijacker |
| Related extension | Track Packages by Polarity Technologies Ltd |
| Symptoms | A new extension installed on the web browser; homepage and new tab changed; search results are filled with sponsored links |
| Removal | Terminate the related browser extension and clean your web browsers; scan your machine with security software |
| System fix | After you delete adware or malware, your computer might start malfunctioning. If that happens, you can fix virus damage with FortectIntego repair tool |
Search.searchtmpn4.com URL has already been included in the list of potentially unwanted programs.[1] Such classification indicates that it's capable of installing without requiring users' permissions directly and hijacks Chrome, Firefox, IE, Edge, and other web browsers right after that.
Apart from a forceful replacement of the default start page, search engine, new tab URL, the app can initiate suspicious activities for the sake of web traffic modification. Despite the fact what search query its users type in, it may return adapted results that contain links to affiliated websites in priority.
Do not fall for believing that it generates actual Yahoo search results. Yahoo is a legitimate provider that is often used as an engine for browser hijackers, and the top results provided come from the latter. To check that, you can access a genuine Yahoo search and type the same query as you entered in the searchtmpn4.com search tab. You will see that the results do not coincide.
Those who cannot stand pop-up ads, misleading survey prompts, scam alerts, fake software updates,[2], and other content that pose a risk of getting the system infected with malware or exposing personal data or risk of being leaked should initiate PUP removal asap.
Polarity Technologies collaborates with third parties and allows them to inject whatever commercial content they want into the search results. While affiliate marketing is a known practice being applied for promoting websites, the fact that Track Packages search does not monitor advertisements and other displayed content is worrying because some links may expose you to unsafe content or hacked websites.
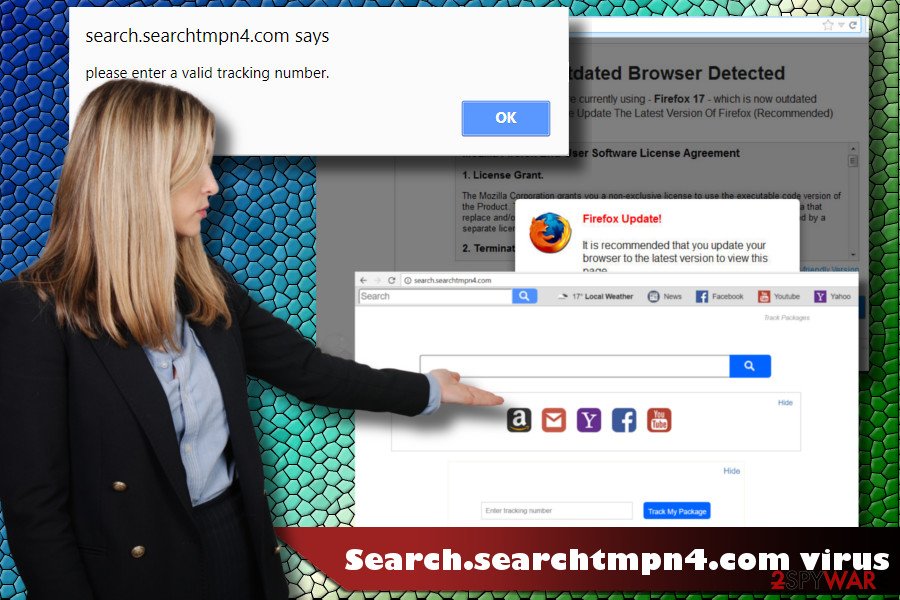
If your web browser has already been hijacked, Virukset.fi[3] security researchers recommend you remove the PUP from the system immediately. Otherwise, it will not only inject cookies and web beacons into your web browser but can also “Allow first-party publisher or Partner Cookies to be installed in your browser.” Third parties may try to gather not only search data but also sensitive information, such as email address, your name, geo-location, IP address, etc.
You can pick up one of the options to uninstall it from the system – either delete it manually (removal tutorial provided at the bottom of this article) or automatically. The latter method requires the installation of a reputable anti-malware tool. Our top pick tools are FortectIntego and SpyHunter 5Combo Cleaner.
Custom and Advanced freeware installation can save people from browser's hijack
People who prefer Quick or Basic freeware installation methods are at great risk of getting tricked into installing browser hijackers and other PUPs. Those who ask why probably did not hear about “bundling.” The term bundling refers to the software distribution technique, which allows combining free applications with web browser extensions, add-ons, plug-ins, etc.
Such software dissemination cannot be suspended because it's legitimate. People are informed about “optional downloads,” but there's a catch. They will not find a warning about attachments when relying on Quick or Basic installation methods. The success of freeware installation depends on the user's carefulness, so each time you decide to install a new app, make sure to follow these steps:
- Pick up a reliable download source (preferably official website);
- Download the application you need and select Advanced/Custom installation method;
- Read EULA and Privacy Policy;
- Look for optional components. Usually, they are disclosed misleadingly – small font, at the bottom of the window, marked by default;
- Remove check marks saying that you agree with the installation of extensions and plugins.
Eliminate searchtmpn4 virus to restore your web browser's settings
Browser hijacker removal will protect your Search Data and block malicious content that third parties may seek to visit. PUP elimination can be initiated manually. For this purpose, you should open Control Panel and get rid of all suspicious entries.
However, cybersecurity experts recommend people use a reliable anti-malware tool to remove searchtmpn4.com and similar PUPs. That's because they tend to spread in packages with other untrustworthy tools and inject related components in various system's locations. Consequently, the removal of the primary file may not stop suspicious activities on the web browser.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Search.searchtmpn4.com. Follow these steps
Uninstall from Windows
Less experienced PC users may not be aware of the methods applicable for PUP elimination. If your PC has been hijacked for the first time, you can use this guide as a help:
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Google Chrome reset is prerequisite to get rid of unwanted programs and delete misleading search engine.
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Search.searchtmpn4.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting browser hijacker
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Kevin Townsend. The Battle With "Potentially Unwanted" Programs in the Enterprise. Security Week. Information security news.
- ^ Jonathan Poole. Android Users: Beware of Fake Security Updates. Top Ten Reviews. The largest and most comprehensive product review sites.
- ^ Virukset. Virukset. Virus and Spyware news.
