Searchdefenderlive.com (Removal Instructions) - Free Guide
Searchdefenderlive.com Removal Guide
What is Searchdefenderlive.com?
Searchdefenderlive.com is a potentially unwanted program that claims to increase the safety of the web browsing but instead hijacks browsers and displays ads
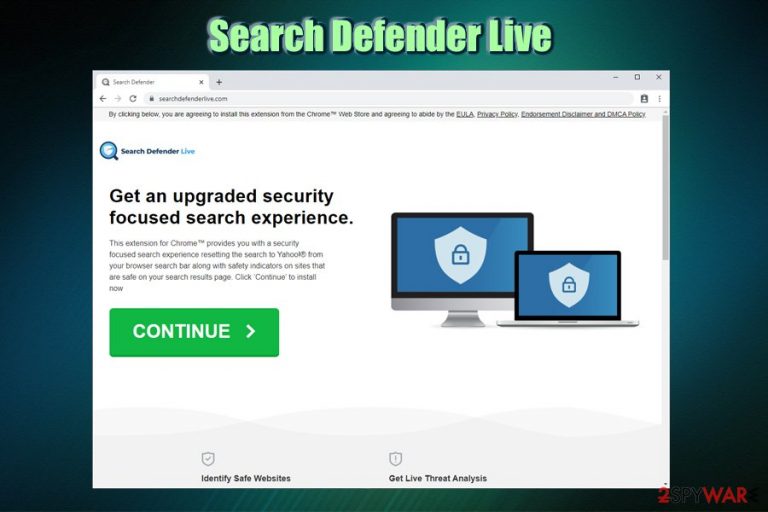
Searchdefenderlive.com is one of many browser hijackers that claims to focus on online security – and many users are concerned about it due to numerous data breaches and increased malware activity worldwide. However, these “security” tools are often PUPs themselves and do not provide the functionality they claim to. Instead, users are shown pop-ups, flashing windows, pop-unders, banners, and other ads during their browsing sessions.
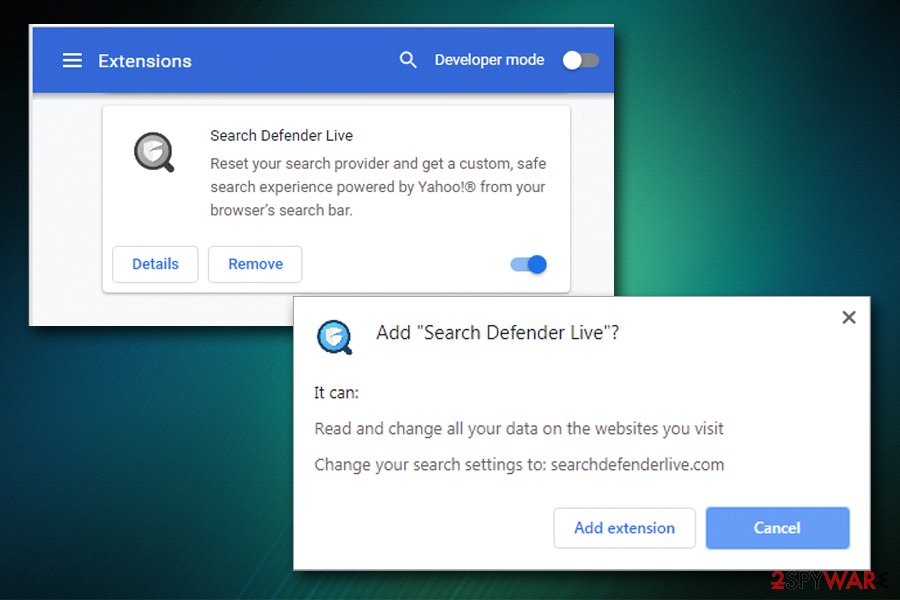
Search Defender Live is the application that causes numerous changes on Google Chrome, Mozilla Firefox, MS Edge, or another browser. The first sign of a browser hijack is that its homepage and new tab URL get set to hxxps://www.searchdefenderlive.com, and a customized engine applied. All the search queries are then redirected to search.yahoo.com, and the search results are not genuine – users will see multiple sponsored links at the top. This way, Searchdefenderlive.com hijacker alters the way users browse the web.
| Name | Searchdefenderlive.com |
| Type | Browser hijacker, potentially unwanted program |
| Associated app | Search Defender Live |
| Developer | Femto Media |
| Offered functionality | The browser extension offers users an indication markings for harmful websites |
| True purpose | There are no criteria that are used to allegedly indicate harmful sites, making the functionality of the app questionable. Additionally, Search Defender Live tracks various user browsing-related activities in order to show ads and promote affiliated sites for profits |
| Infiltration | Potentially unwanted programs are either installed via bundled software packages or after being tricked by an attractive ad or fake update |
| Symptoms |
|
| Removal | You can check the instructions on how to terminate the PUP manually below; additionally, we recommend scanning the machine with anti-malware software to check for other unwanted apps or malware |
| Recovery & optimization | To recover from infections and prevent system crashes and errors, we recommend resetting all the installed browsers and run a scan with repair tool FortectIntego |
Despite claiming to focus on users' privacy and security, Search Defender Live tracks users' anonymous and personal information obtained during the registration process. Searchdefenderlive.com removal is highly recommended, as the traits of a potentially unwanted program make this hijacker an unneeded addition to the system.
As stated on the Searchdefenderlive.com official site, the following data might be collected:[1]
We gather Personal Information and Non-Personal you provide to us directly or that is obtained from you use of our Services. “Personal Information” means information, such as your first and last name, email address, physical address, telephone number, billing information, or social security number, that is able to personally identify you. “Non-Personal Information” means information that is not capable of personally identifying you.
Besides, the collected information can be shared with commercial and third-parties for various purposes, including the distribution of advertising material via e-mail or other means. Such data is tracked and collected with the help of monitoring tools like Flash Cookies, web beacons, web server log information, and other methods. In other words, Searchdefenderlive.com turns the collected details into profits by sharing it with affiliates that provide you with ads as long as Search Defender Live is installed on your browser. Without a doubt, information tracking can cause serious privacy and security issues to end-users.

Additionally, inserted browser cookies and other tracking means might be still present even after you remove Searchdefenderlive.com hijacker from your machine. For that reason, we highly recommend resetting your browsers as per the instructions below.
Because Search Defender Live is distributed via software bundling, there is a high chance that other potentially unwanted programs or malware might be present on your machine. To ensure it is not the case, experts recommend performing regular scans with anti-virus software. After termination of such infections, however, computers might experience slow response times due to such issues as the corruption of certain registry files. To prevent system crashes and fix virus damage, we advise scanning the computer with FortectIntego.
Avoid potentially unwanted programs by following simple security tips
Potentially unwanted programs usually enter users' machines unnoticed, i.e., they are not installed deliberately. Even if they are, users are mostly unaware of underlying tasks (such as unwanted ads display) that the app can create post-installation. In other words, potentially unwanted programs are truly unwanted, although they cannot be called malware as users generally install them deliberately themselves (note that malware uses completely different infiltration techniques, including malicious installers, spam emails, exploits,[2] weak RDP connections, and similar). Despite that, the installation process of third-party programs is often deceptive, as the developers or/and host site owners consciously try to hide optional components from users.
Although, users are also to blame, as they often do not pay close attention to the installation instructions of bundled applications, and end up with tools they never wanted to install in the first place, and not all of them perform browser changes as browser hijackers do, so the intrusion might not always be apparent. All in all, it is best to avoid PUPs in the first place – here are some tips from security researchers:[3]
- Before installing any application, read up on it online – check out reviews, blog posts, tech forums, etc.;
- Make sure the app provides access to Privacy Policy and Terms of Service before proceeding;
- When prompted, always go for Advanced/Custom installation settings that often reveal the underlying programs;
- Beware of tricks used by bundled software installers: watch out for misplaced buttons, misleading deals, fine print text, pre-ticked boxes, etc.;
- Employ a security application that specializes in PUP detection and removal.
Remove Search Defender Live and other PUPs and use reputable tools that provide additional browsing safety
If you are looking for a tool that can enhance your web browsing experience and protect you from potentially malicious websites, Search Defender Live is not the application you should be going for, as all your web browsing activities will be tracked and used for marketing purposes. There are plenty of other free programs and browser extensions that do not engage in such activities and are capable of providing relevant information when it comes to online safety. In fact, many AV vendors include such functionality in their comprehensive plans.
If the Searchdefenderlive.com virus managed to hijack your computer, you should hurry up with Search Defender Live removal. As we previously mentioned, its functionality is questionable at best, as it does not provide any details on how the extension works – which criteria the websites are marked as insecure.
You can remove Searchdefenderlive.com relatively easily if you opt for a browser reset – all the extensions will be deleted. However, because the PUP might not be the only one on your machine, we highly recommend a scan with anti-malware software.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Searchdefenderlive.com. Follow these steps
Uninstall from Windows
To get rid of potentially unwanted programs on Windows, follow these steps:
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
The instructions for Mac users as follows:
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Don't forget to reset Mozilla Firefox after you terminate Searchdefenderlive.com hijacker:
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Searchdefenderlive.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting browser hijacker
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Privacy Policy. Search defender live. Official website.
- ^ Exploit (computer security). Wikipedia. The free encyclopedia.
- ^ Utanvirus. Utanvirus. Comprehensive security advice.
