Searchtown.net (Free Guide) - Virus Removal Instructions
Searchtown.net Removal Guide
What is Searchtown.net?
Searchtown.net – a browser hijacker also recognized as Patriot PDF Converter for Macs
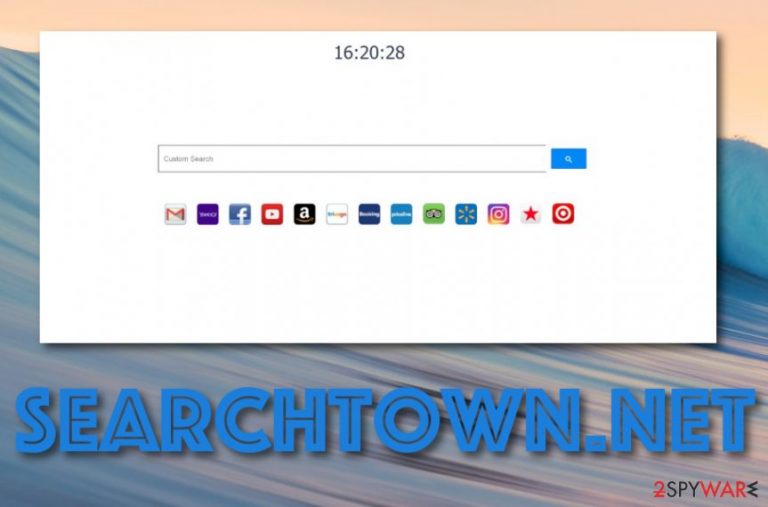
Searchtown.net, also known as Patriot PDF Converter, is a browser-hijacking application that attacks Mac computers and their browser apps. Mac users have already been complaining about this potentially unwanted program appearing on their Apple machines.[1] Once Searchtown.net virus reaches browsers such as Safari, Chrome, or Firefox, it sets the homepage to Searchtown.net, the new tab search zone to Searchtown New Tab Search, and modifies the default search provided to https://searchtown.net. In addition, this browser hijacker is linked to the 141.8.225.124 IP address.
| Name | Searchtown.net |
|---|---|
| Alternative name | Patriot PDF Converter |
| Type | Browser hijacker/potentially unwanted program |
| Search settings | This browser hijacker is capable of changing the default search engine to https://searchtown.net, the homepage to Searchtown.net, and the new tab search to Searchtown New Tab Search |
| Serving IP | 141.8.225.124 IP address is where this domain comes from |
| OS-based | This potentially unwanted program has been created to target Mac OS X users and their machines/browser apps |
| Activities | The hijacker promotes the advertising of rogue products, redirecting the user to affiliate networks, collecting browsing-related data, etc. |
| Found in | You can find browser hijackers on your computer system after completing unsecured downloads, installing fake Flash Player updates, or visiting unsafe sources such as Torrent websites |
| Identification | Use software such as FortectIntego to identify all suspicious strains on your Mac computer that might be related to the browser hijacker |
Searchtown.net should not be categorized as malware itself but it sometimes gets the name of “virus” due to unwanted performance of bogus activities and the stealth installation process that it promotes. Mostly, hijackers appear while performing free software downloads, through fake flash player updated, or torrent-based websites.
Once the infiltration happens, Searchtown.net will hijack one or multiple web browser applications and might even provide some beneficial-looking features which truly are just a trick to lure you into using the app more often. Usually, developers insert fast access to various communication platforms such as Facebook and Instagram, and some news/weather sources.
However, do not get too satisfied with these features as it is only a small glimpse throughout the entire unwanted activity flow that will definitely approach you later. Searchtown.net will supposedly start redirecting you to affiliate sources some of which might turn out to be potentially dangerous and seek to infect you with dangerous malware such as a Trojan virus, or similar.
In addition, you might start receiving intrusive advertising content from Searchtown.net domain while completing browsing sessions and online activities. The browser hijacker might support bogus products and services and try to convince you to spend your money on purchasing some questionable computer repair software.
By the way, browser hijackers such as Searchtown.net are known to fill settings with browser helper objects (BHO) such as extensions, plug-ins, and similar. In addition, the PUP might insert tracking cookies into your web browsers that allow the developers to spy on your online sessions and track what kind of deals are relevant to you at the moment.
All in all, as you can see Searchtown.net Mac promotes a big variety of activities that can be performed all at once. Due to the big intensity of these processes, you might start facing regular browser slowdowns, crash downs, and struggle to maintain full-quality browsing. Besides, search results that come from this domain might be provided by a legitimate search service such as Yahoo or Bing so there is no actual need for using the browser hijacker instead.
Finding yourself troubling to maintain browsing processes, annoyed by intrusive notifications and redirects, leads only to one option – Searchtown.net removal. This type of task can be carried out by using our step-by-step guidelines that can be found at the end of the article or by employing automatical software for full computer cleaning.
However, if you are a less-skilled computer user or just do not put your effort towards manual elimination, you should definitely choose to remove Searchtown.net with trustworthy antimalware. Before you begin, download and install FortectIntego software and search for all browser-hijacker related objects that might be hidden on your Mac system.
Browser hijackers can be found in mysterious places all over the web
Experts from NoVirus.uk website claim that potentially unwanted programs, including browser hijackers, are distributed by using more than one silent technique. However, most often, developers inject suspicious products into freeware/shareware packages, place infectious hyperlinks or ads on third-party websites such as torrents, fake flash player updates. If you want to keep your computer protected from such bogus components, you should:
- Opt for the safest installation option. Make sure to choose Custom/Advanced settings instead of Quick/Recommended configuration. The first variant allows tracking all incoming downloads and deselecting all unwanted objects.
- Prevent yourself from accessing unsafe pages. Avoid visiting third-party networks, especially, p2p networks such as The Pirate Bay and Torrents where downloading links might include infectious objects.
- Keep your programs always updated. Make sure to regularly update all of your software and do not get tricked by false app updates such as Flash Player.
- Install antimalware security. Always have an AV engine running on your computer system that will ensure safe browsing, protect you from potential malware, and allow you to perform regular system check-ups.
Virus removal instructions for Searchtown.net virus
Searchtown.net removal is a process that can be carried out by using anti-malware software or manual step-by-step guidelines. We have provided some instructions below for your Mac OS X system and web browser applications such as Google Chrome, Mozilla Firefox, and Safari.
However, if you find it to hard to remove Searchtown.net on your own, you should employ reliable antivirus programs to perform the process for you. These tools are capable of finding all infected locations on your computer system and cleaning them in a few minutes of time.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Searchtown.net. Follow these steps
Delete from macOS
In order to make the browser hijacker removal complete, you need to eliminate all entries that it has added to your Mac OS X system. You can accomplish this task by performing the following:
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Mozilla Firefox (FF)
If you have found some questionable extensions, plug-ins, or add-ons in Mozilla Firefox, you can remove this type of content with the help of these guidelines:
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Our experts have also provided instructions on how to clean Google Chrome and reverse the web browser back to its previous position:
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Eliminate all bogus changes on your Safari web browser app that have been performed after the hijack. Use these steps if help is needed:
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Searchtown.net registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting browser hijacker
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Gilgelad. Nuisance - Searchtown.net. Discussions. Apple forums.
