Seon ransomware (Virus Removal Guide) - updated Jan 2019
Seon virus Removal Guide
What is Seon ransomware?
Seon ransomware – data locking malware that is using GreenFlash Sundown exploit kit for propagation

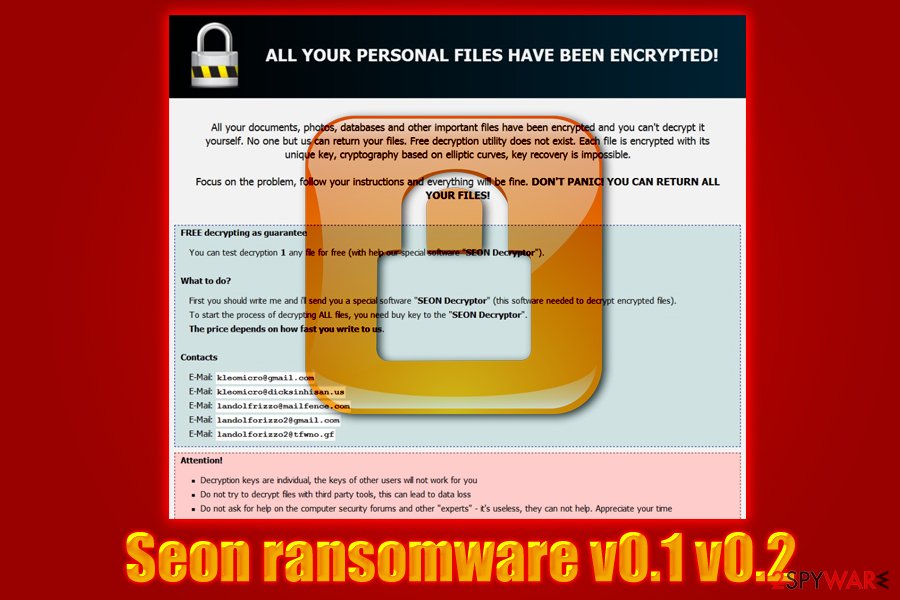
Seon ransomware is a typical crypto malware that uses the AES encryption algorithm to lock data and then demands a ransom to be paid for the decryptor. It was first spotted in November 2018 and appended .FIXT file extension to documents, pictures, videos, databases, and others, although it skips system files. Seon virus dropped YOUR_FILES_ARE_ENCRYPTED.txt ransom note that disclosed contact emails of crooks: kleomicro@gmail.com and kleomicro@dicksinhisan.us. While the initial infection used phishing emails[1] and similar methods for distribution, hackers came up with the Seon ransomware 0.1 and 0.2 on January 1st, 2019, and started circulating the malicious payload with the help of GreenFlash Sundown exploit kit. The newest variants do not differ much from their predecessor, although victims are also presented with a readme.hta along with the text ransom note. Additionally, criminals provided as three new contact email addresses for the communication.
| Name | Seon |
|---|---|
| Type | Ransomware |
| Versions | Ver 0.1, ver 0.2 |
| Extension | .FIXT |
| Files locked | Videos, photos, audios, databases, word documents, PDFs, PPTs, etc. |
| Ransom message | YOUR_FILES_ARE_ENCRYPTED.txt, readme.hta |
| Ransom type | Criminals ask for BTC or another type of currency |
| Given email addresses |
kleomicro@gmail.com, kleomicro@dicksinhisan.us, landolfrizzo@mailfence.com, landolforizzo2@gmail.com, landolforizzo2@tfwno.gf |
| Distribution sources | GreenFlash Sundown EK, spam emails, unprotected RDP, etc. |
| Elimination | Get rid of the virus ASAP. Detect all damaged components with FortectIntego |
Seon ransomware was first distributed with the following ransom note:
SEON RANSOMWARE
all your files has been encrypted
There is only way to get your files back: contact with us, pay and get decryptor software
We accept Bitcoin and other cryptocurrencies
You can decrypt 1 file for free
write email to kleomicro@gmail.com or kleomicro@dicksinhisan.us
As evident, cybercriminals are asking for Bitcoin or other cryptocurrencies[2] in exchange for the decryption tool. The usage of digital wallets is preferable by hackers, as it helps them to remain anonymous while illegally asking money from their victims. Seon ransomware authors should not be trusted, as, even after transferring the payment, they might simply ignore the victim and keep the money.
With the 0.1 and 0.2 versions, seems like criminals decided to develop the Seon ransomware even further, as it now started to be propagated with the help of GreenFlash Sundown EK, and included a more professionally-looking readme.hta ransom note. Additionally, while file extension remained the same, crooks provided five contact emails that, in addition to previous two emails, included landolfrizzo@mailfence.com, landolforizzo2@gmail.com, and landolforizzo2@tfwno.gf.
Remove Seon virus from the computer as soon as possible in order to avoid further damaging consequences. You can get rid of the threat only by downloading and installing reliable anti-malware tools. These programs will ensure you that all virus-related components are deleted and successfully removed from the system. Moreover, try using software such as FortectIntego as it can help you detect the damage that might have been done by the ransomware virus.
Performing the Seon ransomware removal is necessary if you want to recover your data. After you take care of the cyber threat, you can try using our below-provided data recovery techniques. If you carry out each step carefully, you will have a chance of recovering encrypted files such as photos, videos, audios, databases, text documents, and others.
Beware of spam emails and patch your system with security updates
Keeping your system up to date might save you from ransomware infections. Exploit kits are designed to abuse flaws in the code of software, which makes outdated machines vulnerable. All those users have to do is visit a malicious website or get redirected, and, in a matter of seconds, the infection spreads throughout the system. Thus, do not postpone any updates and immediately patch your apps and system.

According to technology experts from NoVirus.uk[3], ransomware viruses are distributed via phishing emails – attachments or malicious links. Hackers employ bots that send out thousands of phishing emails to thousands of users. While spoofed emails can be easily recognized by most, there will always be those who will fall for the trick and open contaminated attachment or click on a malicious link. Therefore, experts advise being extremely careful when handling emails from unknown sources, especially if the attached document is asking to enable macro function.
Furthermore, rogue websites can also distribute ransomware. For example, P2P networks[4] sometimes might include virus-related components injected into links or somewhere else. This happens because such pages do not fit the security requirements and often lack protection. If you have accidentally overcome a questionable-looking website, make sure that you close it the same second and do not think of returning.
Delete Seon virus with the help of this guide
There is only one possible way to remove Seon virus – by installing a reputable antivirus program. These automatical tools are created for such kind of purposes and allow the user to carry out the removal in a safer way. Furthermore, we suggest choosing a program such as FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes, as these tools can detect all rogue components that might have been hiding in the computer system.
Moreover, after you take care of the Seon ransomware removal, perform some system backups to ensure that the cyber threat has been disabled properly. Additionally, taking about locked files, you might have a chance of recovering them by looking thru the below-provided data recovery methods. However, all of them have their conditions that they can work under, and if you perform all steps as required, you might restore your files.
Getting rid of Seon virus. Follow these steps
Manual removal using Safe Mode
Disable the cryptovirus by enabling the Safe Mode with Networking option:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Seon using System Restore
Use System Restore to deactivate the ransomware virus:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Seon. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Seon from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Finding files with the .FIXT appendix means that Seon ransomware has infiltrated your computer and encrypted all files. In order to restore your data back, try our below-given tools and complete the data recovery process.
If your files are encrypted by Seon, you can use several methods to restore them:
Data Recovery Pro tool might help you recover some files:
This method might be truly helpful and let you get important files back if you use it exactly as shown in the instructions.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Seon ransomware;
- Restore them.
Use Windows Previous Versions feature for data recovery purposes:
If your files have been corrupted in a particular way, try out this tool. However, note that it might not work if you did not enable the System Restore feature in the past.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Shadow Explorer might let you restore data:
If the ransomware virus did not erase Shadow Volume Copies of encrypted files, this method might let you recover your documents.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Experts are currently working on the Seon ransomware decryption tool.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Seon and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Phishing. Wikipedia. The free encyclopedia.
- ^ Cryptocurrency. Investopedia. Worldwide definitions.
- ^ NoVirus.uk. NoVirus. Malware news.
- ^ P2P. Tech terms. Tech-related information.







