Skeeyah (Virus Removal Guide) - 2021 update
Skeeyah Removal Guide
What is Skeeyah?
Skeeyah is the trojan that can open backdoors and let any attacker access your computer
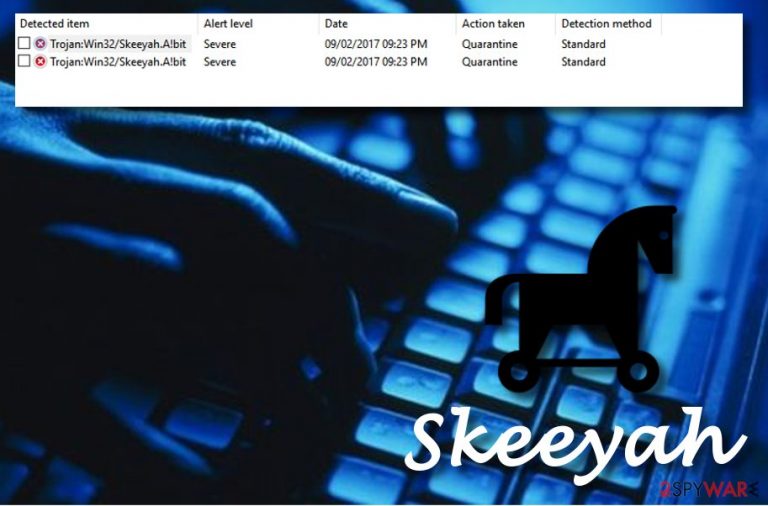
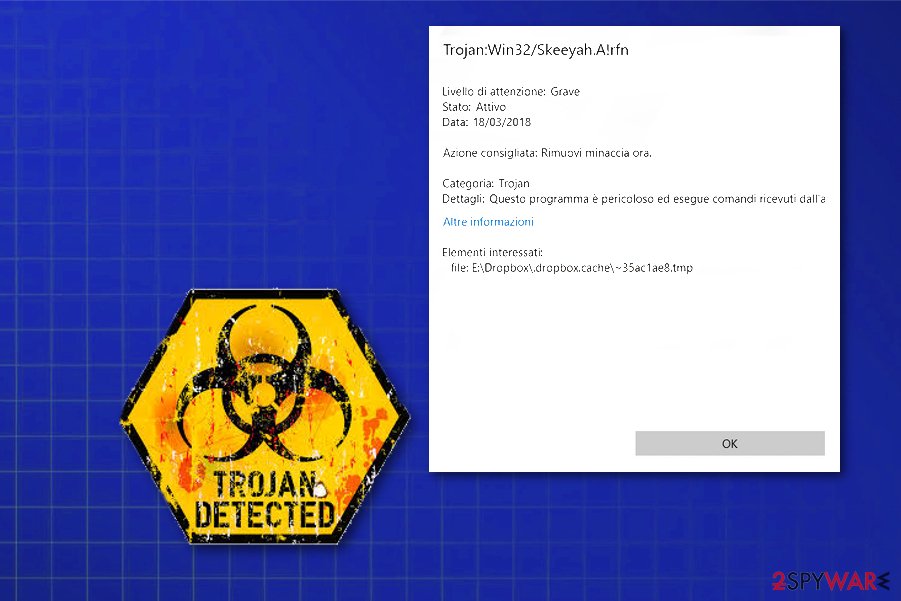
Skeeyah is malware behind a detection name Trojan:Win32/Skeeyah.A!plock that appears on the screen when AV tools detect anything even suspicious or potentially dangerous. The notification about it appears seemingly out of nowhere, so it often leaves users baffled about where it is coming from. In fact, those that do not have a sufficient security program installed would never notice the infiltration of the stealthy trojan.
While the detection can be triggered on Windows Defender or another security tool due to an active malware attack, another option is when the leftovers of the virus are not eliminated properly. This usually happens due to some Windows file corruption, thus a scan with another security software might be necessary.
Skeeyah malware spreads around on its own and can run in the background for a while without the victim noticing the activity. The cyber threat is a backdoor Trojan horse that might easily steal your personal information. You need to run a proper scan with an anti-malware tool, so you can clean the machine and eliminate any traces of this or another virus.
Once this dangerous virus is in your computer system, it installs another malware that lets the criminals steal sensitive data that is kept on the infected PC, such as banking info, credit card details, email passwords, logins, and so on. Nevertheless, cyber crooks who spread the virus for their own bad purposes can use your accounts such as Facebook, Instagram, etc., to attack your friends or other innocent people. This type of activity might get you looking like the guilty one. However, trojans have a wide range of negative features, and they need to be removed as quickly as possible before more damage has been done.
| Name | Skeeyah |
|---|---|
| Type | Backdoor trojan |
| Also known as | Trojan:Win32/Skeeyah.A!plock |
| Dangers | Can steal personal information and misuse it for bad purposes, also, this virus might use your private Facebook (or another type) account to commit attempts against your friends |
| Symptoms | Barely any. However, you might recognize high CPU usage, struggling applications, dubious registries in the Windows Registry, and so on |
| Prevention | Avoid opening questionable emails, install antivirus software, do not enter rogue-looking websites |
| Delete it | Remove the virus permanently with an anti-malware tool that can clear any of the threats completely |
| Repair | Your machine might be affected by this threat to a stage that particular programs or features cannot run. Use FortectIntego to detect all harmful components and possible damage |
Skeeyah trojan has been spreading through different computer systems, and users have been talking about this activity. Victims, who reported this virus have claimed that Windows Defender finds Trojan:Win32/Skeeyah.A!plock, but apparently it is not that easy to get rid of[1].
However, this dangerous backdoor[2] is known for stealing private data such as banking details, account passwords, and so on. If you hesitate to eliminate the threat and wait for this malicious activity to happen, you might face the consequences of data misusage.
Cybercriminals can sell this data on the dark web, then other hackers can use such credentials in direct scam campaigns.[3] Moreover, if the infection manages to enter some of your online accounts, note that they might also be misused for attacking others. This might put the guilt on you.
Nevertheless, such trojans can inject illegal content, e.g. child or teenage porn, straight into your computer, and as you know, such a thing is a very big crime. Sadly, trojans show barely any symptoms and might be too hard to spot on time, but some signs might be a signal about this malicious program.

These symptoms include high usage of your CPU, sometimes it can reach even to 100%! Furthermore, you might start experiencing software crashes, discovering entries, or apps you did not install. If you spot any of this suspicious activity, scan your PC with reputable anti-malware to check what is wrong. If the backdoor appears to be guilty of this, remove Skeeyah virus immediately.
Also, we recommend downloading and installing programs such as Malwarebytes or SpyHunter 5Combo Cleaner. This computer software might be helpful for detecting damaged programs and other components. Performing Skeeyah removal is crucial because various other applications may run beside the initial trojan and cause even more damage than this trojan.
Make sure you proceed with the process at the same minute you recognize the cyber threat, so there is not much time for the malware to run on the computer. Moreover, take a look at the precautionary measures that we have provided below. They might help you avoid similar infections in the future.
Remember that Skeeyah is a backdoor trojan and criminals developed this virus as a malware-dropper. The main purpose is to infect the targeted system further, so any applications installed on your PC need to get terminated to end all the symptoms you experience.
Malicious sites, deceptive content and other malware leads to trojan infection
Cybersecurity experts from NoVirus.uk[4] recommend being very careful while performing an online activity. A Trojan horse can hide in many rogue websites and secretly install only with one click. If you overcome suspicious web pages, they should be eliminated immediately in order to avoid possible virus infiltration. Moreover, always check what you are downloading from the Internet. Do not skip any installation steps and make sure you install only original software.
It is commonly known that various malware infections, including Trojan horses, are widely spread through phishing email messages[5] and their hazardous attachments. Crooks often attach the dangerous payload to the dubious letter and send it to numerous random users. Be careful while opening questionable messages – some of them might be sent for bad purposes.
Another piece of advice would be to run a reliable antivirus tool on your computer daily. Do not be afraid to invest in such type of software because a reputable program will bring these benefits:
- Regular system scans will show all computer-related problems;
- The antivirus will keep the PC safe while you are performing computing work;
- It will help you get rid of various issues that might occur over time.
Prepare to clear the system fully to remove the Trojan:Win32/Skeeyah.A!plock
Performing the virus removal requires a lot of attention and effort because this is a virus that you cannot see working. This is the main reason why we suggest users to use reputable anti-malware software to complete the process.
Furthermore, tools such as FortectIntego, SpyHunter 5Combo Cleaner, Malwarebytes might also help as they can detect malware-related content and fix virus damage. Make sure you take care of the cyber threat properly even if the elimination might take a while. Skeeyah virus may be more persistent than you think.
After you remove Skeeyah, make sure to refresh the entire computer system and check if all trojan-related components are gone. When the computer is fully cleaned, you can use it normally again. However, you should not forget all the avoiding tips you have read as they might be very careful and let you prevent backdoor trojans from entering your computer system again.
Getting rid of Skeeyah. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Skeeyah using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Skeeyah. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Skeeyah and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Trojan:win32/Skeeyah.A!rfn. Microsoft community forum. Questions and answers.
- ^ Prakash Prasad. What is trojan and backdoor?. Quora. Worldwide info.
- ^ Sextortion Scam Uses Recipient’s Hacked Passwords. Krebsonsecurity. In-depth security news and investigation.
- ^ NoVirus.uk. NoVirus. Malware removal tips.
- ^ Email spam. Wikipedia. The free encyclopedia.







