Solo84.biz (Free Guide) - Removal Instructions
Solo84.biz Removal Guide
What is Solo84.biz?
Solo84.biz is the browser pop-up scam that tricks people into subscribing to nonsense push notifications
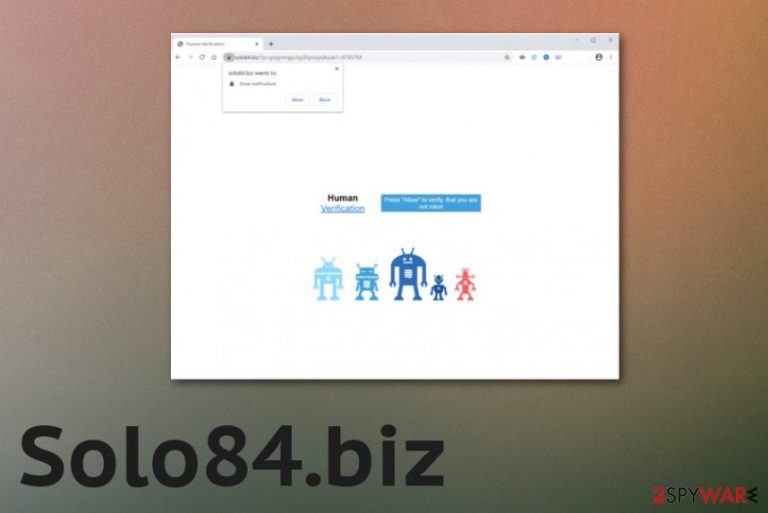
Solo84.biz virus is an adware-type infection that focuses on generating page views, visits, and pay-per-click revenue.[2] This program can even be called push notifications virus because it triggers the subscription of notifications that come directly to your desktop even when the web browsers are closed and not in use. The occurrence of such redirects can also affect mobile devices, tablets, and mobile phones, so you should be aware of such cyber infection. Since the site delivers you various other pages and manages to affect the speed, the more time the PUP has on the computer the more issues it creates.
| Name | Solo84.biz |
|---|---|
| Type | Adware/ redirect virus |
| Tactics | Social engineering[3] methods get used to trick people into subscribing to these push notifications. Verification claims encourage people to click on the banner or a browser pop-up |
| Distribution methods | Freeware downloading sites and malicious pages created with promotional purposes can distribute potentially unwanted programs during the installation of software due to the method called software bundling |
| Symptoms | Pop-ups on the browser state about the need to allow notifications or verify that you are a human to access the material on the page. One-click on the message triggers display of additional pop-ups and redirects |
| Danger | This is the potentially unwanted program that can track, collect and share data about your preferences and habits online because each advertising site contains cookies and other methods designed to obtain such information |
| Elimination | Solo84.biz removal is the important process, so when you use proper anti-malware programs you can fully terminate all the symptoms, and the only issue is to repair the possible damage |
| Repair | PUP can affect performance from the system folders and functions when various files and apps get loaded behind you back. Such damage can significantly diminish your time on the computer, so rely on FortectIntego or a similar program, so this damage can get repaired |
Solo84.biz is one of the thousands of unreliable pages, rogue sites designed to feed visitors unreliable content to generate redirects to additional content online that cannot be considered trustworthy. Users are forced to click on the human verification forms or browser pop-ups to make the needed online traffic reroutes and expose victims to intrusive ads.
Aside from causing those redirects and advertisement campaigns, Solo84.biz PUP can gather data about your device that got affected and particular preferences regarding online browsing and searches or even social medial likes and behavior. This is not the behavior that should require your attention or permission, and cush activities can take place behind your back as many additional PUP functions do.
Even though you notice these pop-ups, banners, redirects, and other symptoms of the infection, Solo84.biz is not only serving as a redirecting program or the site, that shows ads, and that is it. PUP manages to inject files in system folders, disable or add new programs on the device, so some security functions can be managed, and adware evades quick detection, can run on the computer for longer.
This is also the reason why you need to remove Solo84.biz using professional anti-malware tools, so all the potentially related files and programs get to be eliminated and stopped. Your machine can start to work even better than before after such a cleaning process. However, if you decide to wait longer, you may end up with more powerful malware installed or get exposed to a hacker-controlled page. 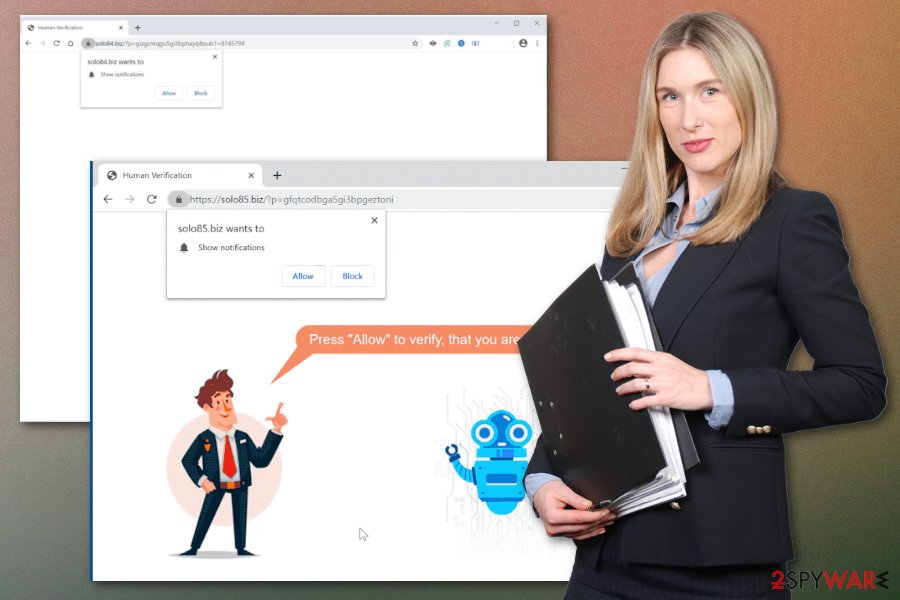
Solo84.biz wants to Show notifications
Click “Allow” to close this window
This window can be closed by pressing “Allow”. If you wish to continue browsing this website just click the more info button
Click Allow to confirm that you are not a robot!
Exiting the browser can help right then in there, but the proper Solo84.biz removal process should include the usage of an anti-malware program and the full system scan. This method allows for finding all materials related to the intruder and terminating them once and for all. As for your web browser that gets affected when PUP adds tools, extensions, and applications, you may need help from a guide below.
Web browser settings that manage notifications ay get altered to allow Solo84.biz or any other similar or even related page to send notifications, pop-ups to your screen. You need to change those settings back to default by going to Site settings on the browser and selecting to Block or Remove the site entirely from the preferences list.
Then the only step left to do is the virus damage repair after proper cleaning. When the Solo84.biz is completely terminated, and you are sure that PUP is not running anymore, get a system optimizer or a security tool, and run it on the machine. Applications like FortectIntego can search for issues regarding system files and affected apps or functions and repair such parts of the machine for you. 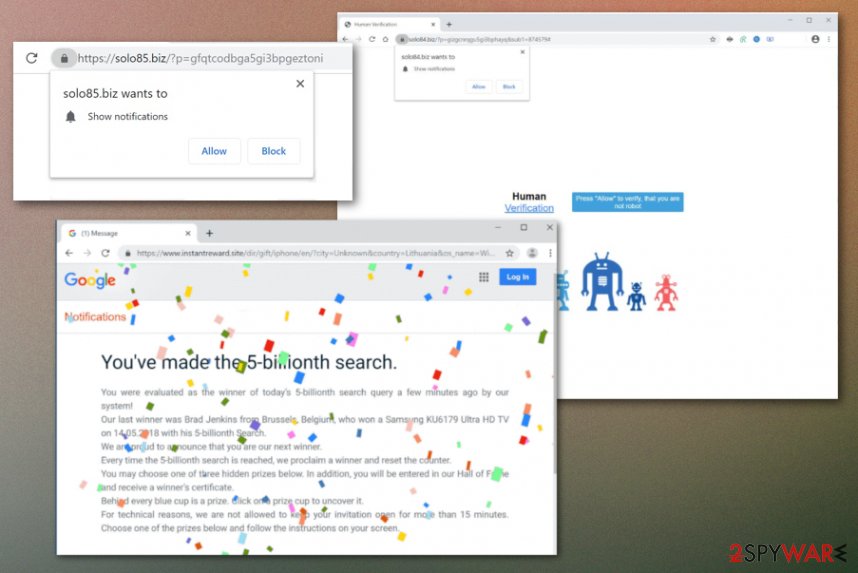
Deceptive messages claiming all sorts of things to trigger PUP installations
Tons of different pages online are designed to display questionable material that encourages to click on a banner, pop-up, or even visit the needed site. There are various tactics that claim for a need for human verification, offer prizes or congratulates on the winning.
When you continuously visit such sites, you get exposed to shady material all the time and cannot even notice the PUP than managed to get added on the system without your permission. This also happens when you install freeware on purpose from unreliable sites, torrent services, and so on.
However, choosing Advanced or Custom options may help you to avoid the issue of the unwanted installation. When you go for Recommended or Quick installation all the included apps get downloaded at once, and when you rely on Advanced methods, you can see the full list with pre-packed programs and de-select anything that seems suspicious.
Solo84.biz PUP elimination steps
The first thing that you need to consider is the Solo84.biz virus capability of installing other files and programs. To clean all the associated applications and browser-based programs, you need to either find them all over the system or run the automatic program that can locate malicious files or potential intruders and quarantine or delete them for you.
This procedure can be achieved with an anti-malware program that is based on dangerous file detection and can remove Solo84.biz itself, the PUP that controls processes and other files scattered throughout the machine. You may try to do that manually, but it takes time, and since some of the changes are made in system folders, you may damage the computer further.
It is advised to go for the automatic Solo84.biz removal method that saves time and provides better results quicker. Anti-malware tools, AV detection engines, and security software can find, detect, indicate and delete any type of cyber threat, so your device after such a process may start to work even better than before.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Solo84.biz. Follow these steps
Delete from macOS
Clear the system from any traces of the program and Solo84.biz virus
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Go through settings of the Chrome or reset the browser fully to default
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Solo84.biz registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Potentially unwanted programs. Wikipedia. The free encyclopedia.
- ^ Everything You Need to Know About PPC. Disruptiveadvertising. Social media advertising.
- ^ Social engineering. Techtarget. Search security.
