Start ransomware (Tutorial) - Virus Removal Guide
Start virus Removal Guide
What is Start ransomware?
Start ransomware – a new form of Dharma ransomware that displays a ransom-demanding pop-up named starter@cumallover.me
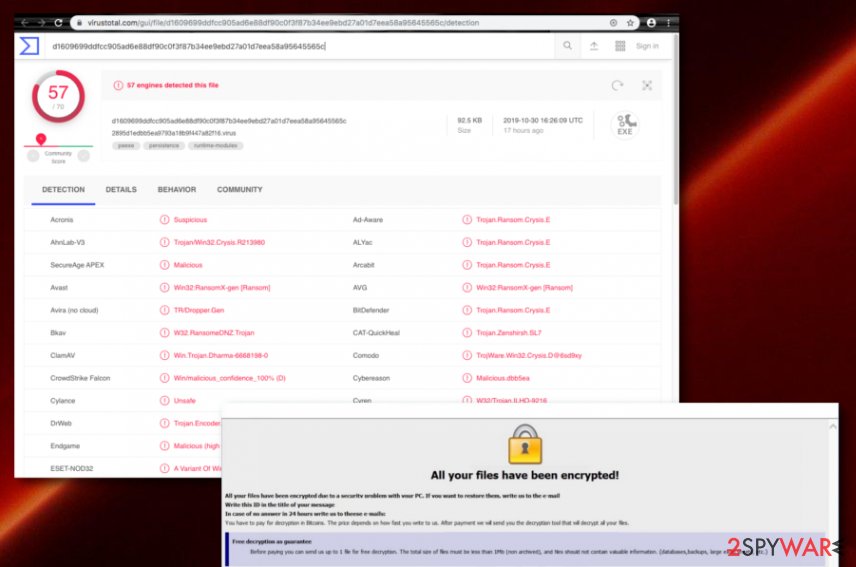
Start ransomware, also known as [Starter@cumallover.me].Start ransomware, is a newly released Dharma ransomware variant that has been first spotted and announced by Jakub Kroustek.[1] He created a Twitter post regarding this new malware variant and provided a VirusTotal hyperlink where the malicious payload has been detected by 57 AV engines out of a total 70.[2] Once files are locked by Start virus, they end up with the .[starter@cumallover.me].start appendix. Continuously, the ransomware displays the starter@cumallover.me pop-up window or the RETURN FILES.txt message which holds information regarding ransom demands and the decryption software.
| Name | Start ransomware |
|---|---|
| Type | Ransomware virus/malware |
| Family | Dharma ransomware |
| Appendix | Once the ransomware virus launches the unique encryption module, all locked files end up with the starter@cumallover.me appendix |
| Ransom note | The malware provides ransom demands via the starter@cumallover.me pop-up window and the RETURN FILES.txt message |
| Detection names | Trojan.Ransom.Crysis.E, Win32:RansomX-gen [Ransom], Trojan-Ransom.Win32.Crusis.to, Ransom.Crysis, etc. |
| Found by | Findings related to Start virus were first released by Jakub Kroustek on Twitter social network |
| Distribution | The infection can be spread via vulnerable RDP configuration (TCP port 3389), p2p networks such as The Pirate Bay, and phishing emails that pretend to come from reliable shipping companies, for example, DHL or FedEx |
| Elimination tips | Download FortectIntego software and try detecting damaged files that are caused by the ransomware. To remove Start virus, you will need an anti-spyware tool |
Start ransomware does not provide particular demands although the money has to be transferred in Bitcoin cryptocurrency in order to ensure the anonymity of the entire process. This decreases the crook's chances of getting caught. However, this also means that the victims will not be able to return their money back also.
Usually, criminals demand a ransom between $100 and $2000 in BTC. However, Start ransomware only offers to send them one small file for free decryption as evidence of the decryption key's existence, provides information on how to get Bitcoins. and threatens the victims not to try self-decrypting data or it might get permanently destroyed:
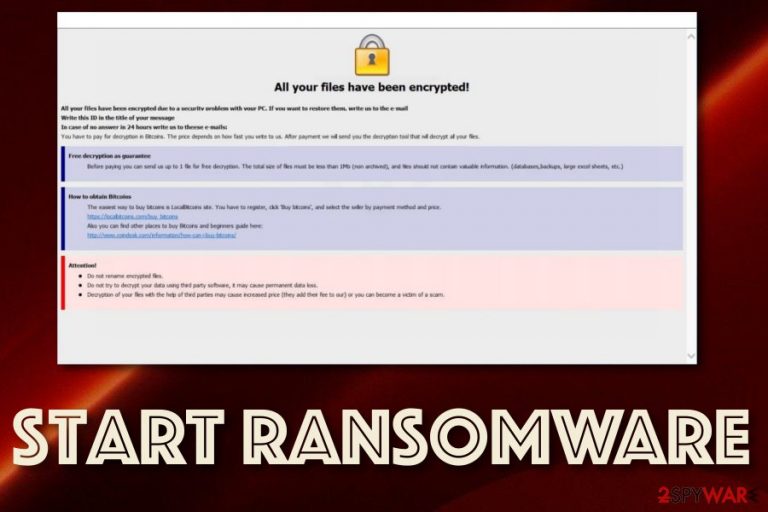
All your files have been encrypted!
All your files have been encrypted due to a security problem with your PC. If you want to restore them, write us to the e-mail starter@cumallover.me
Write this ID in the title of your message
In case of no answer in 24 hours write us to these e-mails: starter@cumallover.me
You have to pay for decryption in Bitcoins. The price depends on how fast you write to us. After payment we will send you the decryption tool that will decrypt all your files.
Free decryption as guarantee
Before paying you can send us up to 1 file for free decryption. The total size of files must be less than 1Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
How to obtain Bitcoins
The easiest way to buy bitcoins is LocalBitcoins site. You have to register, click ‘Buy bitcoins’, and select the seller by payment method and price.
https://localbitcoins.com/buy_bitcoins
Also you can find other places to buy Bitcoins and beginners guide here:
http://www.coindesk.com/information/how-can-i-buy-bitcoins/
Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
Start ransomware is a tricky threat that might hold various infectious modules in its database. This means that the virus might be able to delete Shadow Volume Copies[3] by executing specific PowerShell commands, damaging the Windows hosts file to prevent access to security-related websites and forums.
Besides, Start ransomware places suspicious entries and files in the Windows Task Manager and Registry sections. Also, you might discover random executable files in directories such as %AppData% and %LocalAppData%. Remember that all of this content needs to be wiped during the Start ransomware removal process.
If you do not eliminate all the dangerous products injected, Start ransomware might renew itself within the next computer boot process. Additionally, the malicious infection can result in the infiltration of other malware such as trojans, worms, cryptocurrency mining apps, spyware programs, and other types of computer viruses.
Start ransomware has been designed to attack the most used Windows computer systems such as Windows 7, Windows 8, and Windows 10. Regarding the language which is used in the ransom note, the file-encrypting malware targets English-speaking people or users that are located in English-speaking countries.
If you do not remove Start ransomware on time, you will have to face lots of damaging consequences, including an increasing amount of encrypted files. Additionally, you should try using FortectIntego after the elimination process as this tool might be capable of fixing virus leftover files. Note that it cannot decrypt encrypted files as it is not a decrypter. For that, keep up with StopDecrypter updates.
Keep in mind that you should avoid paying any ransom to Start ransomware criminals as you might get easily scammed by these people and have to face huge monetary losses. Even though there is no official decryption tool released yet, you can try some other data recovery solutions that are added to the end of this article.
The most common ransomware distribution sources
Ransomware infections get through vulnerable RDPs that hold weak passwords or none at all. Hackers misuse ports such as the TCP port 3389 and remotely connect to the targeted computer system to plant the malicious payload.
Also, some cyber criminals get involved in email spam campaigns and camouflage as reliable shipping companies, e.g. FedEx/DHL, or reputable banking organizations, healthcare firms, etc. These people attach malicious files or insert infectious hyperlinks that are supposed to launch the ransomware payload.
Furthermore, malware can get easily distributed through unsecured p2p networks such as The Pirate Bay, by installing fake software updates, various software cracks, infected hyperlinks/advertisements, exploit kits, etc.
Use manual and automatical protection to avoid ransomware attacks
There are more measures for avoiding ransomware infections than you might think of. First of all, get a reliable antimalware product that will guard your computer system 24/7. Do not be afraid to invest in a trustworthy program that will be able to scan your machine regularly, provide safe browsing, and threat detection.
Continuously, you should learn how to correctly sort out all of your emails. First, always check the sender and it looks like a non-existing email address, better delete the message right away. Furthermore, look for grammar mistakes through the entire message text and if you find lots of them, you can be sure that no reliable company will make that much.
Additionally, if you receive any clipped attachments, you should scan each file or document with an antimalware product to ensure that the content is safe for opening or downloading. To continue, you should pay a lot of attention to what types of networks you are visiting as some of them might include malicious objects due to the lack of protection in them.
Furthermore, keep all of your programs regularly updated, especially your antivirus software. Do not get tricked by fake updates as you can check their original releases on official websites and see if it is a true upgrade you are about to make.
Removal of Start ransomware explained in details
Start ransomware removal can be performed only automatically. According to computer specialists from LesVirus.fr,[4] manual elimination is not possible in this case as it is too dangerous to take the entire process in your own hands as you might skip crucial components and leave the malware in the system.
You can remove Start ransomware with the help of SpyHunter 5Combo Cleaner, or Malwarebytes. Once you do so, you need to be sure that no malicious products are left in the system. For this purpose, try using software such as FortectIntego, as the malware might be able to corrupt registry entries and similar components.
Additionally, if Start virus appears hard to remove because it is blocking antivirus access or something else important, you should enable Safe Mode with Networking or activate System Restore to prevent malicious processes from spreading further on your Windows computer.
Getting rid of Start virus. Follow these steps
Manual removal using Safe Mode
Enable Safe Mode with Networking to deactivate malicious processes on your Windows computer system
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Start using System Restore
Turn on System Restore to prevent the malware from spreading further. Use the below-provided steps to achieve this task
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Start. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Start from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Start, you can use several methods to restore them:
Data Recovery Pro might help with file restoring tasks
Try this software if Start ransomware has locked, corrupted, or deleted any of your files
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Start ransomware;
- Restore them.
Employ Windows Previous Versions feature to restore some individual files
Use this tool for file recovery if you have activated the System Restore feature in the past
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Try using Shadow Explorer for file recovery purposes
You can employ this tool if you are looking forward to recovering some data files. However, make sure that the ransomware virus did not eliminate Shadow Volume Copies of locked data, otherwise, this method might seem unuseful
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Currently, no official decryption key has been released for Start ransomware encrypted files
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Start and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Jakub Kroustek. '.start' - 'starter@cumallover.me'. JakubKroustek. Twitter status.
- ^ d1609699ddfcc905ad6e88df90c0f3f87b34ee9ebd27a01d7eea58a95645565c 2895d1edbb5ea9793a18b9f447a82f16.virus. VirusTotal. File detections.
- ^ Shadow Copy. Wikipedia. The free encyclopedia.
- ^ LesVirus.fr. LesVirus. Security and spyware news.







