Sticky Notes browser hijacker (virus) - Free Instructions
Sticky Notes browser hijacker Removal Guide
What is Sticky Notes browser hijacker?
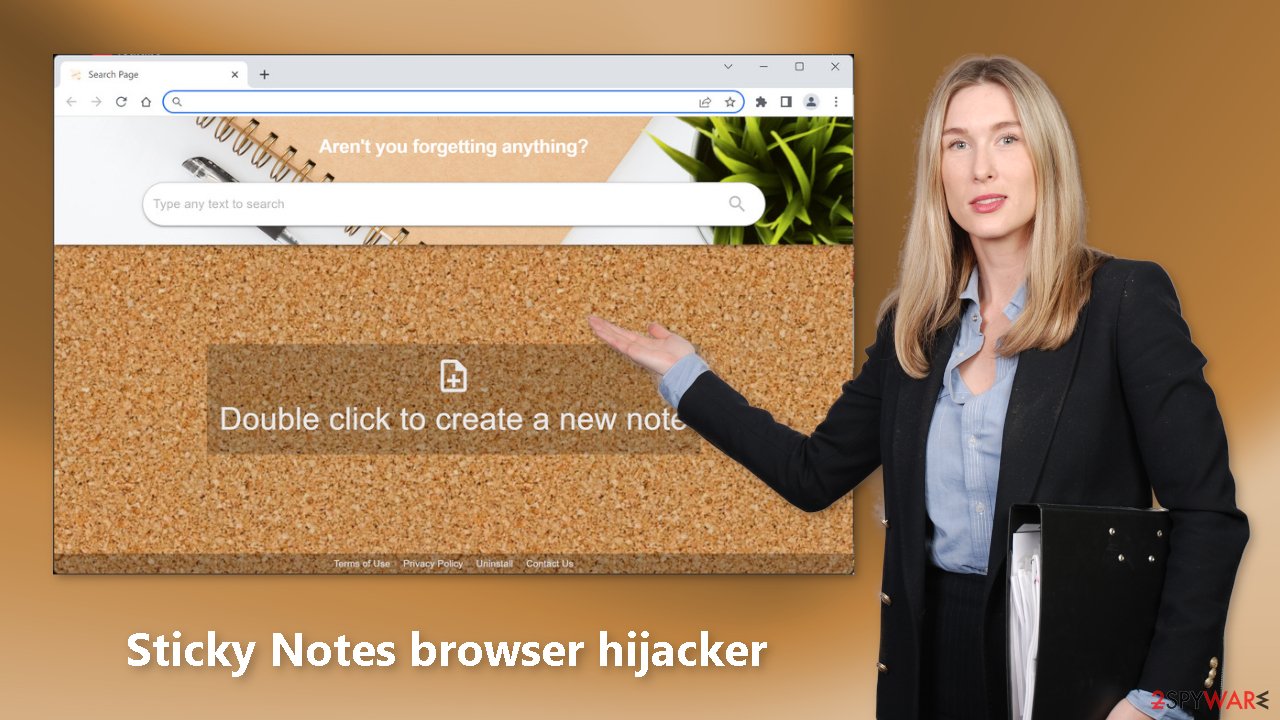
Sticky Notes is a browser extension that may collect browsing information in the background

Sticky Notes is a fraudulent browser extension that claims to be a useful plugin that allows users to add sticky notes to their browser's homepage. However, the plugin modifies the browser's default settings, such as the homepage, new tab address, and search engine. Users are forced to browse only through specific channels, raising numerous privacy and security concerns.
The majority of hijackers are designed to collect sensitive information or generate revenue through pay-per-click advertising. Browser plugins can also cause redirects to other pages. Unfortunately, crooks may use rogue advertising networks to direct victims to fraudulent websites.
| NAME | Sticky Notes |
| TYPE | Browser hijacker; potentially unwanted program |
| SYMPTOMS | The main settings of the browser get changed, like the homepage, new tab address, and search engine |
| DISTRIBUTION | Shady websites, deceptive ads, software bundling |
| DANGERS | The extension may lead to dangerous websites; display misinformation, and inaccurate search results; track browsing, and collect data |
| ELIMINATION | Remove the extension by going to your browser settings |
| FURTHER STEPS | Use FortectIntego to fix any remaining damage and optimize the machine |
Distribution methods
Browser hijackers are frequently distributed via bogus download pages. Crooks create deceptive websites that trick people into thinking they are downloading something when they are not. To avoid such sites, avoid clicking on random links and advertisements, even if they appear to promote legitimate products and services.
Because illegal streaming websites are unregulated, use legitimate streaming platforms instead. They can also show bogus “Download” and “Play” buttons that take you to bogus download sites. Netflix and Hulu have low monthly subscription fees and allow users to watch as much content as they want.
When adding new plugins, it is best to use official web stores. Apps that are listed on digital marketplaces must go through a rigorous review process. You should, however, conduct your own research by reading the reviews, examining the rating, and examining the number of users. You should select apps with a lot of positive feedback and thousands of users.
Privacy issues
Sticky Notes and many other browser extensions frequently collect information about users' browsing habits. Cookies[1] are used to store information such as your IP address, geolocation, websites visited, links clicked, and items purchased online. It can then be resold to ad networks or other third parties.
That is why security experts advise clearing browsers on a regular basis. You can use a maintenance tool like FortectIntego to automatically delete cookies and cache. This powerful software can also repair system errors, corrupted files, and registry problems, which is especially useful following a virus infection.
How to remove an unwanted extension?
You can remove browser add-ons by going to your settings. Find the list of extensions installed in your browser and remove the Sticky Notes hijacker. Follow the guide below for instructions:
How to prevent from getting browser hijacker
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Dusan Vasic. What Are Cookies? The Good and the Bad of Browser Cookies. Dataprot. Security Solutions.
- ^ Potentially unwanted program. Wikipedia, the free encyclopedia.
- ^ Tim Fisher. What Is Freeware?. Lifewire. Internet, Networking and Security Blog.










