Sulseerg.com ads (fake) - Free Guide
Sulseerg.com ads Removal Guide
What is Sulseerg.com ads?
Sulseerg.com is a malicious website created by scammers to show intrusive ads via a push notification feature

Sulseerg.com is a phishing site that uses push notifications to send ads to your computer screen. This activity may be manifest as long as Google Chrome, Mozilla Firefox, Microsoft Edge, or another browser is running – it doesn't even have to be actively used. As a result, pop-ups may show up when users are watching TV shows or gaming.
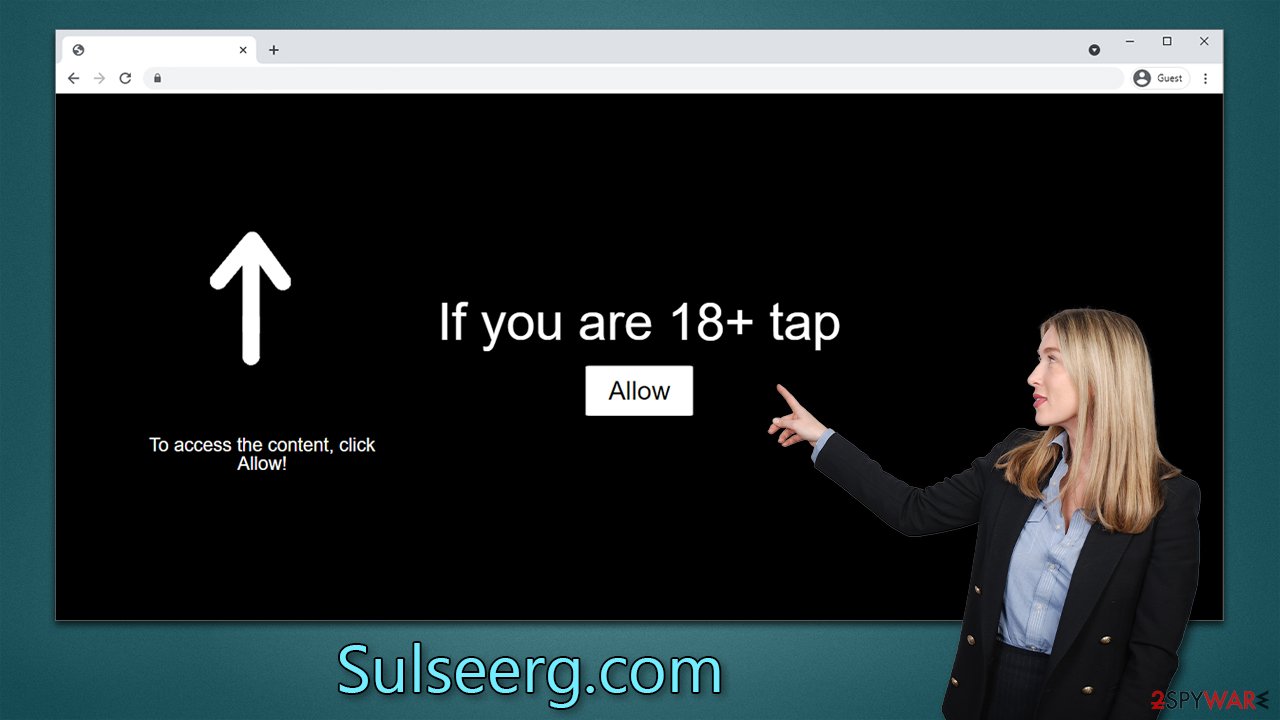
After being tricked into clicking a fraudulent link, users arrive on the Sulseerg.com site to find a fake message prompting them to click “Allow,” and some people do this because the message can be rather convincing. At some point later, users would receive push notifications from the site without warning.
It is important to note that, in some cases, adware on people's computers can result in more frequent encounters with phishing[1] sites. Therefore, we will provide instructions not only on how to remove the annoying push notifications but also deal with computer infections that may be present on your system without your knowledge.
| Name | Sulseerg.com |
| Type | Push notifications, ads, scam, pop-ups |
| Distribution | After the “Allow” button in the notification prompt is clicked on the site |
| Symptoms | Notifications show up at the bottom-right corner of the screen – these include fraudulent content and links to potentially dangerous websites |
| Risks | Once enabled, notifications from malicious websites would bring misleading or other suspicious content to your screen. These links could lead to malware-laden, scam, phishing, or similar malicious sites |
| Removal | You can stop unwanted notifications by accessing web browser settings. If you suspect adware infection, you should use SpyHunter 5Combo Cleaner security software to get rid of it |
| Other tips | Remove caches and other web data to prevent data tracking – use the FortectIntego repair and maintenance tool. You can also repair damaged system components with it |
More about the feature
Push notifications are commonly used by legitimate websites and apps to alert users of new content or updates. They are typically sent to a user's smartphone or computer through a web browser or mobile app. They can be useful for alerting users to important updates or notifications from their favorite apps or websites.
However, scammers can also use this technology to send fake notifications that appear to come from a trusted source. These notifications often include a sense of urgency or a compelling offer to entice the victim to click on the link or provide sensitive information.
Thus, the push notification feature, which is embedded into every modern web browser, was created for legitimate uses, although it was quickly “stolen” by cybercriminals to profit from advertisements deliberately inserted into users' devices and them having no control over when they show up, and Sulseerg.com authors' goal is precisely that.
It's best if you steer clear of ads from Sulseerg.com, as they may be misleading or even dangerous. You might come across get-rich-quick schemes, warnings about supposedly discovered malware, or fake claims that you've won valuable prizes. If you're gullible enough to fall for one of these scams, you could end up downloading harmful software or malware, losing money out of pocket, or giving access to your personal information to cybercriminals.
How scammers create an illusion of necessity
Unexpected redirects to push notification scam sites are a common tactic used by scammers to achieve their goals. Distracted users are more likely to make mistakes and fall for these scams.
Once redirected to these fake sites, users may encounter a request to verify that they are human or that they are over the age of 18. These types of verification techniques are not uncommon, and many users have encountered them before.
This familiarity makes it easier for scammers to use social engineering[2] tactics to trick users into providing sensitive information or clicking on malicious links. It is important to be cautious when encountering these types of requests and never to provide personal information unless you are certain the request is legitimate.
You should always check the URL of the website that's showing you some type of request, as it usually points at something fishy. If you were tricked by Sulseerg.com or another similar website, you shouldn't worry too much because you can get rid of push notifications rather easily.
Removal of unwanted push notifications
If you want to get rid of push notifications, there are two ways: reset your browser settings or block the website from showing push notifications. The second option is more practical. To do this, follow these steps:
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
Computer infections and how to deal with them
It is important to scan your system for adware and other possible infections. It is possible that you clicked on a malicious link that directed you to Sulseerg.com, but there is also a chance that adware could be causing this issue. Often, adware developers use deceptive methods such as bundling to spread their infection, so the user may not even be aware of it. It is better to be cautious and scan your system to ensure it is free from any potential threats.
To ensure that all adware and malware are detected and removed, it is recommended to scan your system using a powerful anti-malware tool such as SpyHunter 5Combo Cleaner or Malwarebytes. It is also important to have a security tool running on your system at all times, as this can provide the best protection against ransomware and other malware attacks.
In addition to removing any viruses and adware from your system, it is important to protect your privacy. Small tracking files may be installed on your device when you browse the internet, which can put your personal information at risk. Cookies,[3] for example, can track the websites you visit, the links you click, your device technical data, IP address, and more. To protect your privacy, it is important to remove these tracking files as soon as possible.
To ensure that your device is clear of cookies and other tracking files, we recommend using the FortectIntego repair and maintenance tool. This app is also effective at resolving any issues that may arise after malware removal, such as system crashes or errors. Using it will help to protect your privacy and maintain the performance of your device.
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ What is Social Engineering?. Knowbe4. Security awareness and training solutions.
- ^ Cookies and Web Beacons. NTT. NTT Communications.






