Surpriseyeahuzlow.rest ads (Free Instructions)
Surpriseyeahuzlow.rest ads Removal Guide
What is Surpriseyeahuzlow.rest ads?
Surpriseyeahuzlow.rest shows misleading ads and notifications to extort personal user information

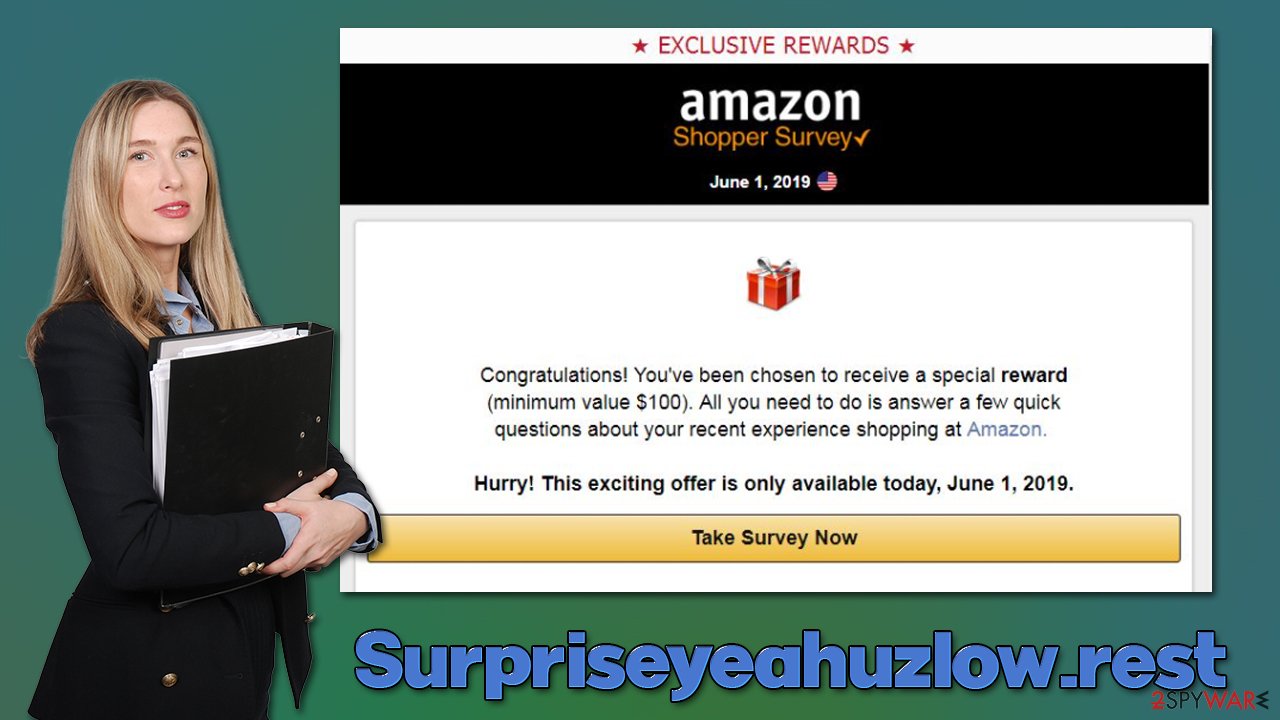
Surpriseyeahuzlow.rest is a scam website that users typically encounter after clicking suspicious links somewhere else – typically, insecure websites such as those that host illegal software installers. Alternatively, those infected with adware or other malicious software can suffer from persistent redirects and intrusive ads.
Immediately upon entering, visitors are presented with a message that encourages users to interact with the page's contents – participate in a survey or pick one of the seemingly free gifts. Generally, Surpriseyeahuzlow.rest can host a variety of different scams, although users most commonly encounter “You've made the 9.68-billionth search,” “Congratulations Dear Amazon User,” or similar messages.
The main goal of these messages is to make people believe that they have won an expensive item, such as a $1,000 Gift Card, iPhone, Samsung TV, PlayStation 5, or similar. All they need to allegedly do is pick one of the treasure chests or gift packages to pick a prize randomly.
However, as soon as the alleged gift is picked, users are then redirected to a page where personal details, such as name, email, home address, or even credit card details, must be provided in order to reclaim the item. By doing so, users are providing their personal information to malicious actors and can be targets of further phishing attacks.
| Name | Surpriseyeahuzlow.rest |
|---|---|
| Type | Scam, phishing, adware, redirect |
| Goal | Make people provide personal information, subscribe to useless services, download malicious software or subscribe to push notifications |
| Distribution | Redirects from other malicious websites, adware |
| Dangers | Those who have malicious software installed on their systems are more likely to encounter dangerous websites, resulting in financial losses, malware infections, etc. |
| Removal | To uninstall unwanted apps manually, you can follow our removal guide below. If the unwanted ads and other disruptive behavior does not stop, you should scan your computer with SpyHunter 5Combo Cleaner security software to delete all threats automatically |
| Other steps | Cleaning web browsers is one of the secondary things you should do after PUP/malware removal to secure your privacy. You can use FortectIntego to do it quickly |
Phishing and social engineering[1] are the main reasons why users end up losing millions of dollars yearly. Technical support scams are among the most profitable online fraud types out there, with survey scams being a close second. If you have encountered a scam and are wondering what the consequences of it are, the answer to this question can vary greatly, depending on your actions.
In most cases, just accessing a fake message would not result in any type of harm to your computer or you personally. The only way that would be possible is if you would have vulnerable[2] software installed on your device and the Surpriseyeahuzlow.rest would host a malicious script that would abuse the flaw to install malware automatically. This is quite rare, however, and can be stopped by the security software, software updates, and additional tools like ad-blockers.
If you have interacted with the scam page, you should immediately scan your system with SpyHunter 5Combo Cleaner or Malwarebytes security software to ensure it is not infected. Disclosing personal information such as email address or phone number might result in you being a focus of phishing attacks in the future, so be aware. Likewise, if you have disclosed your password, make sure you change it on all accounts it is used (never reuse passwords in the first place, as it's one of the biggest security threats!).[3]
Step 1. Remove unwanted programs
First, you should check the list of the installed programs on your system. It is important to note that adware is rarely installed in such a way nowadays (adware is usually spread as browser extensions), although some media players, PDF converters, system optimizers, and similar apps are known to also show intrusive ads.
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till the uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Mac
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
Step 2. Scan for malware
If you haven't already, make sure you scan your device with security software regardless of whether or not you have interacted with potentially dangerous websites. Anti-malware software can check all the system components and ensure they are not infected; if something is found, the security application can immediately quarantine and delete the malicious files.
Step 3. Clean your browsers
Your next task is ensuring that tracking processes are no longer taking place, and for that, you need to clean web browsers. The easiest way to do so is by using FortectIntego software – it can remove cookies and other web data automatically for you within just a few seconds, get rid of malware leftovers, and also repair system damage that could have been sustained due to the infection, fixing crashes, errors, and other post-infection issues. Alternatively, you can follow the guide below:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
MS Edge (legacy)
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.
![Clear Edge browsing data Clear Edge browsing data]()
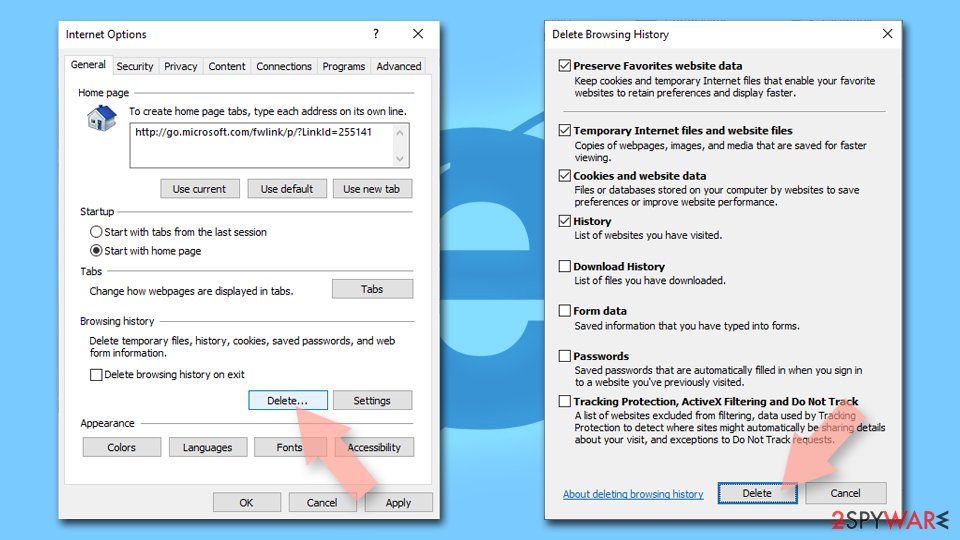
Internet Explorer
- Press on the Gear icon and select Internet Options.
- Under Browsing history, click Delete…
- Select relevant fields and press Delete.
![Clear temporary files from Internet Explorer Clear temporary files from Internet Explorer]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Social Engineering. Imperva. Application and data security.
- ^ Thomas Holt. What Are Software Vulnerabilities, and Why Are There So Many of Them?. Scientific American. Science Magazine.
- ^ Nathan Benedicto. What is password reuse, and why is it a security problem?. UC Davis. Information Technology professionals.