System Defender (Virus Removal Instructions) - updated Jan 2020
System Defender Removal Guide
What is System Defender?
System Defender is a rogue anti-malware that tries to imitate Microsoft's Windows Defender

System Defender is a malicious program that specializes in showing users fake notifications about virus infections on their systems. The app represents itself as a tool that can protect from online risks, while in reality is malware[1] itself, the goal of which is to scare users with false-positives and make them pay for the licensed version. In other words, System Defender is a scam that performs malicious activities behind users' backs, so it should never be trusted.
Those who decide to pay for a full System Defender license might not only damage their computers due to inadequate changes to it but also expose their credit card information to unknown parties, potentially – cybercriminals. As a result, victims might suffer from money loss or even identity fraud/theft. For that reason, System Defender removal should not be delayed, and no payments are made for scammers.
| Name | System Defender |
| Type | Rogue anti-spyware, malware |
| Other versions | The name of the malicious app was later changed to Security Defender, although the infected users might also be offered identical programs like Malware Defender, Defender PRO 2015, Antivirus Defender 2015, and others |
| Infiltration | Users might get infected with malware in various ways, but System Defender is usually spread as an optional component within a software bundle. Users might also install it after being tricked after visiting a scam site |
| Main dangers | Money loss, installation of other malware, credit card information exposure to cybercriminals, etc. |
| Symptoms |
|
| Removal | Access Safe Mode with Networking and scan your machine with reputable anti-malware software |
| Recovery | System Defender may negatively impact the registry, consequently corrupting Windows OS. This might result in system crashes and unstable performance of the PC. To remediate the damaged Windows, scan it with FortectIntego |
System Defender is a generic application that showed up at the time when the internet was not a safe place at all – users could stumble upon malicious links or JavaScript[2] on various pages accessed via legitimate search results. For that reason, many wanted to protect themselves from online dangers, and cybercrooks were quick to utilize that fact.
Creating malicious programs that act as malware and presenting them as security software is one of the tactics that threat actors use. In most cases, the installation of System Defender virus is unintentional (via software bundles or scam sites), although some users might download it on websites that promote it as a legitimate tool.
It is worth noticing that System Defender tries to imitate the legitimate Microsoft tool Windows Defender that was integrated into and shipped with Windows 7 and later versions, although Windows XP users could have also downloaded it from the official sources. This mimicking is not coincidental as, by imitating a legitimate and trusted software, System Defender increased the chances of users trusting the app.
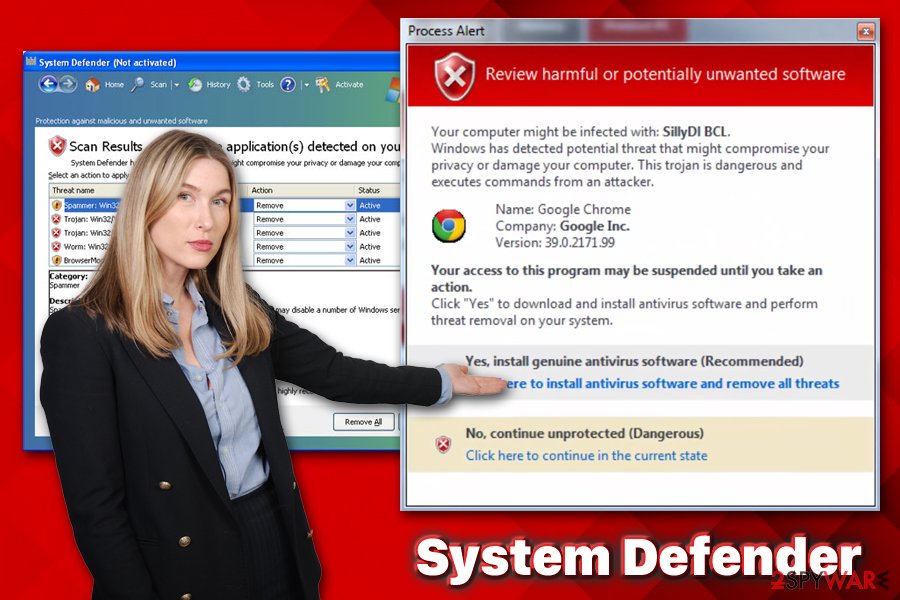
Once installed, System Defender performs a full system scan immediately, although its functionality is utterly bogus – the scan is fake, and so are the results. Users are immediately shown an extensive list of “infections” under names like:
- Win32/Nuqel.E
- Trojan-SMS.J2ME.RedBrowser.a
- Virus.Win32.Faker.a
- Trojan-Spy.Win32.WMPatch
- Trojan-Spy.HTML.Citifraud
- Azero.B
- Trojan-Spy.HTML.Sunfraud.a
- Packed.Win32.PolyCrypt
- Trojan-PSW.Win32.Antigen.a
- BAT.Looper
- Trojan-PSW.Win32.Delf.d, etc.
Additionally, System Defender notifications are riddled with grammar or spelling mistakes:
System scan is complete. Windows has detected 75 critical system objects. This threats may compromise your privacy or damage your computer. Possible consequences of it include:
- Bank details and credit card information can be stolen by trojan programs.
- System executes commands from an attacker. PC will be used for criminal activity.
- Spyware program can tracks your activity and all Web page content.
- Browser add-ons will display pop-up advertisements.
- Spam-bot can use your computer to send spam emails worldwide.
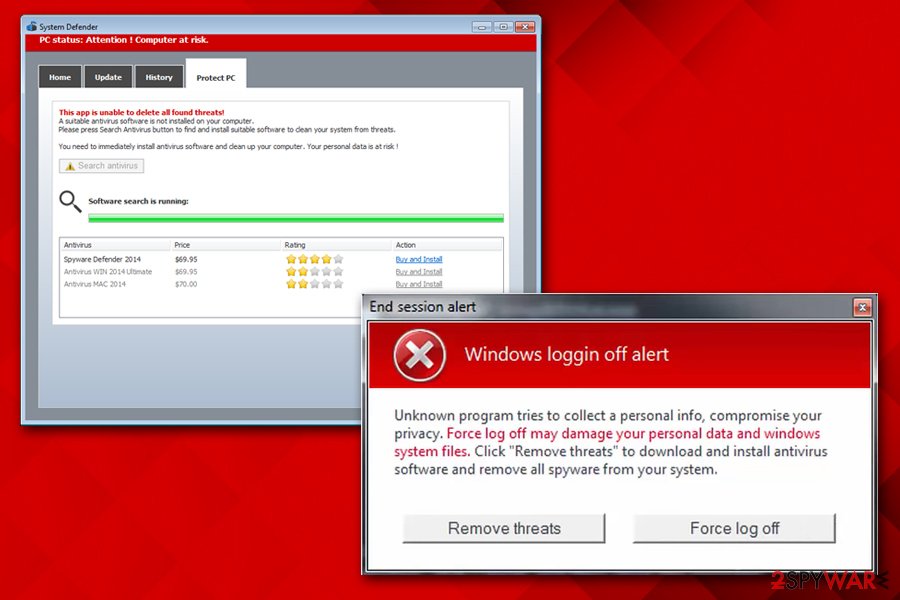
Besides showing fake notifications to users, System Defender malware goes even further and prevents users from installing legitimate anti-malware applications, starting up legitimate programs like Mozilla Firefox, and tampering with their web browsing activities. All in all, you should remove System Defender as soon as possible, as it is high threat to your online safety and computer security. For more details, check our removal section below.
Rogue anti-spyware can find many ways into your computer – avoid it
Fake security programs became a huge business for crooks that employ social engineering[3] in order to make users believe that their computers are infected and need help. While it is true that security software is an essential component for any operating system, rogue anti-spyware is not something that users should rely on.
Not only it shows fake virus alerts, but it also renders the machine vulnerable to real malware attacks. In other cases, poor quality security software can also provide a false sense of security, providing very little protection from online threats.
Thus, it is important to select a reputable anti-malware for your computer and avoid fake security tools completely. To do that, you should be aware of how these malicious programs are propagated:
- Scam websites. Users might stumble upon a scam page at any time, for example, after being redirected from an insecure website. Additionally, those infected with adware ten to see online scams more often than those who are not. In most cases, users are presented with a fake scanner that “detects” malware on a computer and urges them to download software to allegedly eliminate it.
- Software bundles. This is possibly one of the most common methods for unwanted program propagation, as users often skip steps during the installation process. Thus, they should never rush the installation of freeware, pick official sources for downloads, remove ticks from pre-selected boxes, and always opt for Advanced/Custom settings instead of Recommended/Quick ones.
- Malicious websites. Sites that host software cracks and torrents are often infested with malware. Therefore, never download malicious tools like cracks/keygens/loaders and protect your browser with an ad-blocking extension to avoid automatic malware installation.
System Defender virus removal guide
If you are experiencing fake alerts, act now and remove System Defender. For this, we strongly recommend relying on the automatic removal option and avoiding manual removal. When relying on this option, you should just download a reputable anti-spyware, update it, and run a full system scan. If you need a detailed guide explaining how to do that, read this guide.
When trying to remove System Defender, our recommended programs are SpyHunter 5Combo Cleaner and Malwarebytes because they can easily detect every hidden component that belongs to this and other cyber threats. If you experience any system crashes and errors post-termination, scan your machine with FortectIntego.
ATTENTION! As we have already mentioned previously, System Defender may try to block the installation and activity of legitimate security programs. If you can't download or launch any them, try these options:
1. USING SYSTEM RESTORE TO DISABLE VIRUS:
- Go to the Windows 8 Start Screen and type restore point in the Search section.
- Now click on Settings -> Create a restore point.
- When in System Protection tab, select System Restore.
- Click Next button to see your restore points and left click on the entry you need.
- Now select Scan for affected programs -> Close -> Next -> Finish.
- Once your PC reboots, download FortectIntego and run a full system scan after updating it.
2. REBOOTING TO SAFE MODE WITH NETWORKING:
- Click on Windows key and go to the bottom-right corner.
- Select Settings -> Change PC Settings -> General.
- Click the Restart Now button under Advanced Startup.
- Now select Troubleshoot -> Advanced Options -> Startup Settings.
- Now choose Restart and press F5.
- Scan your PC with anti-malware for a full System Defender removal.
3. USING ANOTHER PC FOR DOWNLOADING ANTI-SPYWARE:
- Take another computer that is not infected by this virus and download FortectIntego or SpyHunter 5Combo Cleaner on it.
- After completing the procedure, transfer this anti-malware to the CD/DVD, external drive, or USB flash drive.
- In the meanwhile, kill malicious processes on your infected computer. For that you can use this tutorial.
- Stick the device you used for transferring anti-spyware program to your infected PC and launch it.
How to prevent from getting malware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Josh Fruhlinger. Malware explained: How to prevent, detect and recover from it. CSO Online. Security news, features and analysis about prevention.
- ^ Andra Zaharia. JavaScript Malware – a Growing Trend Explained for Everyday Users. Heimdal. Security blog.
- ^ Social engineering (security). Wikipedia. The free encyclopedia.
