Tally Tab browser hijacker (Tutorial) - Free Guide
Tally Tab browser hijacker Removal Guide
What is Tally Tab browser hijacker?
Tally Tab is a browser-hijacking extension that inserts ads into your searches
Tally Tab is a browser hijacker presented as a handy calculator widget for all Chromium-based browsers. While it ostensibly offers a quick-access calculator function, its true nature surfaces post-installation as it significantly modifies browser settings. Users typically notice a change in their new tab page and frequent redirections to Bing or other search engines. However, the most insidious alteration comes in the form of intrusive advertising.
The extension strategically positions ads and sponsored links at the top of search results, compromising the organic browsing experience. More worryingly, these ads do not always uphold security standards, posing potential threats to user privacy and system security. Though it can be downloaded from legitimate sources, Tally Tab commonly proliferates via software bundling and deceptive ads. This distribution method can often lead to inadvertent installation, making users unintentionally vulnerable to its intrusive behaviors.
Tally Tab is just one of the thousands of potentially unwanted applications that might seem harmless initially but do not bring anything but a negative impact on users' browsing experience and even their computer security. To delete the app and find out more about it, please check subsequent sections of this article.
| Name | Tally Tab |
| Type | Browser hijacker, potentially unwanted application |
| Distribution | Fake ads, software bundles |
| Symptoms | Homepage and new tab address hijacked by the extension; promotional links are displayed as top search results; intrusive ads on various visited websites |
| Risks | Installation of other potentially unwanted programs/malware, personal data disclosure to unknown parties, monetary loss |
| Removal | You can eliminate the browser hijacker by adjusting your browser's settings. Scanning your system with SpyHunter 5Combo Cleaner security software will confirm that there is no adware or malware running in the background |
| Other tips | After removing all browser hijackers and other PUPs from your computer, clean your web browsers and repair any damaged system files. You may accomplish everything automatically with FortectIntego |
Spreading techniques
This app, along with many other browser hijackers, chiefly spreads through software bundling, a strategy employed predominantly by third-party websites. This technique involves packaging the hijacker with other software, usually free or trial versions, thus, users unknowingly install Tally Tab along with the primary software they intended to download.
The bundling process is often intricate and intentionally designed to mislead, making it hard for users to notice and deselect the additional unwanted programs, a factor that significantly boosts Tally Tab's propagation.
Another common avenue of distribution is through misleading websites, which prompt users to install this browser extension as a prerequisite to access specific content. These deceptive prompts can often persuade unsuspecting users to unintentionally install the app, resulting in a compromised browsing experience.
While some users might voluntarily install Tally Tab, enticed by its calculator widget function, the hidden repercussions heavily outweigh this superficial benefit. It negatively affects browsing by altering browser settings, inserting persistent and often irrelevant ads, and potentially tracking user data. This intrusive behavior not only disrupts the user's online experience but also potentially threatens their privacy and security, highlighting the hidden dangers behind seemingly useful tools.
How dangerous are browser hijackers?
While browser hijackers may not pose the same degree of threat as certain computer viruses, they are not to be taken lightly, particularly if installed inadvertently. Their primary disruption is the alteration of users' online browsing experience, which includes changes in search function and internet accessibility.
Browser hijackers such as Tally Tab primarily promote non-organic results and links, often camouflaged as “ads” or similar at the top of search results. Unwary users may click on these top results, not noticing the markers, and potentially encounter misleading or inaccurate information.

Interestingly, it's not uncommon for browser hijackers and other potentially unwanted programs (PUPs) to promote themselves as beneficial tools. They often use enticing language, promising “enhanced,” “fast,” or “secured” searches. However, these are deceptive tactics employed by PUP creators to catch user attention. In reality, these tools usually alter the search engine and search results to insert additional ads, thereby boosting their pay-per-click revenue.
In essence, while browser hijackers may not directly harm your system, they can considerably disrupt web browsing activities, especially if users are not meticulous. Furthermore, the increase in advertisements and potential tracking by another third party adds to the nuisance. Despite their guise of utility, the adverse impacts on user experience and privacy cannot be underestimated.
Tally Tab removal and other tips
While browser hijackers like Tally Tab may not be as damaging as malware, their potential to degrade a user's browsing experience and compromise privacy through data tracking techniques makes them undesirable. These applications should not be overlooked or allowed to linger in the background. Purging all potentially unwanted applications from the system is universally beneficial. Even if the hijacker is not inherently malicious, it does not confer any positive benefits for users.
Tally Tab, like other hijackers, is often distributed as a browser plugin, making its removal a straightforward process once located. However, before proceeding with the extension removal, it's advisable to conduct a thorough system scan for more dangerous malware. Tools such as SpyHunter 5Combo Cleaner or Malwarebytes can accomplish this efficiently and promptly. After ensuring that your computer is free from any harmful viruses, you can confidently proceed to remove the extension, thus restoring your browser's functionality and safeguarding your privacy.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

MS Edge
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Internet Explorer
- Open Internet Explorer, click on the Gear icon (IE menu) on the top-right corner of the browser
- Pick Manage Add-ons.
- You will see a Manage Add-ons window. Here, look for suspicious plugins. Click on these entries and select Disable.

In addition to its intrusive behavior, a browser hijacker like Tally Tab might also leave behind cookies and other trackers that continue to monitor your online activities even after the main application is removed. These trackers persistently store information about your browsing habits, potentially compromising your online privacy. To fully eradicate these remnants, it's essential to clear your browser's cache.
This can be done manually by navigating through the browser's settings or by employing a robust PC repair and maintenance utility like FortectIntego. This tool not only aids in thorough browser cleanup but also ensures overall system health, offering a comprehensive solution to lingering browser hijacker impacts.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

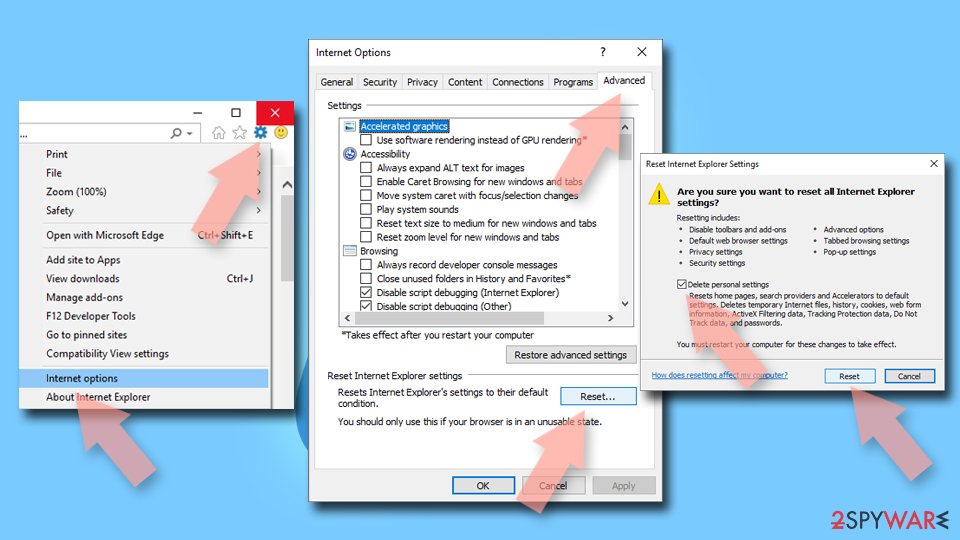
Internet Explorer
- Click on the Gear icon > Internet options and select the Advanced tab.
- Select Reset.
- In the new window, check Delete personal settings and select Reset.
How to prevent from getting browser hijacker
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
