Top10answers.com browser hijacker (Free Guide)
Top10answers.com browser hijacker Removal Guide
What is Top10answers.com browser hijacker?
Top10answers.com is a web address related to a browser-hijacking app
If you notice an URL takeover in your web browser, such as Top10answers.com replacing your default search engine on Google Chrome, Mozilla Firefox, or MS Edge, it's likely that a potentially unwanted application has been installed on your system, often in the form of a browser extension. While these apps may not be particularly dangerous, it's incorrect to assume they are beneficial. In addition, they often exhibit suspicious and deceptive behavior, making their removal a priority.
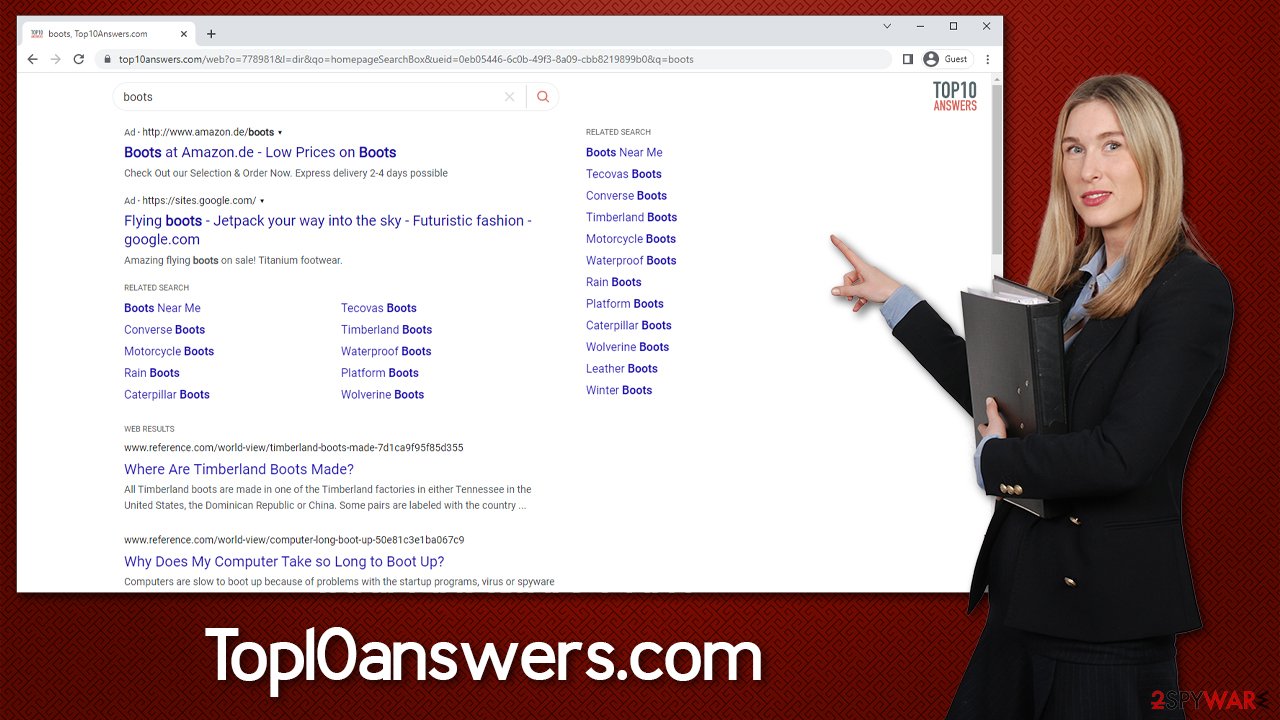
In the case of Top10answers.com, not only will it take over your default search engine, but it will also alter the search results you receive. Instead of genuine links that relate to your search query, you'll be exposed to all sorts of ads and clicks that benefit the hijacker authors. This can impede your ability to find what you're looking for and may even direct you to websites that promote questionable content.
If you've noticed Top10answers.com or any other URL takeover in your browser, it's important to take action to remove the potentially unwanted application as soon as possible. These types of extensions can cause disruptions to your browsing experience, as well as compromise your online privacy and security.
| Name | Top10answers.com |
| Type | Browser hijacker, potentially unwanted browser extension |
| Distribution | Software bundles, ads, redirects |
| Symptoms | Redirects searches through alternative providers; shows irrelevant links, inserts ads into searches and elsewhere |
| Risks | Data tracking from various third parties, exposure to malicious ads, redirects to phishing sites |
| Removal | You can eliminate the browser hijacker by adjusting your browser's settings. Scanning your system with SpyHunter 5Combo Cleaner security software will confirm that there is no adware or malware running in the background |
| Other tips | After removing all potentially unwanted applications, we recommend you employ the FortectIntego utility to clean your web browsers and repair any damaged system files |
How browser hijackers spread and how to avoid them
The success of distributing browser hijackers and more severe infections often depends on the distribution methods used. Developers resort to deceptive techniques, although not illegal since most users would avoid installing potentially unwanted programs (PUPs) if they knew what these apps are capable of.
Many users prefer to download free software from third-party websites, where most PUPs come from. However, they often neglect the installation process and blindly click through the steps without reading the instructions, allowing optional components to slip in. To avoid this, follow these tips:
- Whenever possible, download software from official sources.
- Install reputable anti-malware software, such as SpyHunter 5Combo Cleaner or Malwarebytes, to receive a warning about PUPs and malware.
- Read the instructions for each step of the installation process, including the fine print, uncheck pre-ticked checkboxes, and be wary of misplaced buttons.
- If available, always choose Advanced/Custom settings instead of Recommended/Quick settings.
It is worth mentioning that you could unintentionally install a browser hijacker by clicking on a deceptive advertisement or a false update notification while browsing unsafe websites. It is advisable to avoid installing anything from sites that claim your system is incomplete or needs an update, as it could lead to malware infections.
Data tracking issues
Although browser hijackers are typically not considered dangerous, they can still be a nuisance and pose a risk to your privacy. Top10answers.com is one example of a browser hijacker that is known for its intrusive advertisements and data-tracking capabilities. If you have a potentially unwanted program installed on your computer, you may be exposed to ads promoting other browser hijackers or adware.
Top10answers.com can collect a range of data about your browsing habits, including search queries, visited websites, clicked links, timestamps, technical device information, and ISP data. This information can be gathered automatically through tracking cookies or web beacons. While this may not necessarily be harmful, it can raise privacy concerns for some users.
If your browser has been hijacked, the altered settings can be difficult to undo without disabling or uninstalling the program. We recommend the latter, as the app provides no real benefits and can continue to monitor your data and serve unwanted advertisements while running in the background.
Getting rid of the Top10answers.com browser hijacker
Identifying the culprit behind changes in your browser settings can be challenging, particularly if you have numerous applications installed on your device. Although most hijackers can be manually removed, alterations may indicate the presence of a more severe threat.
It's therefore recommended that you scan your system with anti-malware software, which can easily detect the presence of malicious programs that may be challenging for an average user to remove manually.
To remove Top10answers.com, you should start by accessing your browser settings and eliminating the extension named “Top 10 Answers.” However, this may not always be the case, and the application responsible for the browser changes might have a different name altogether.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the window's top-right).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.

MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

If you have not found the reason why your browser has been hijacked within the Extensions section, you should try checking the applications installed on the system level. Note that security software would most certainly find and remove malicious apps installed this way, so you can skip this step if you have already performed a full system scan.
Windows
- Enter Control Panel into the Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

Mac
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Finally, it's important to note that removing the caches, cookies, and other web data from your browser should be the final step in the removal process of an unwanted program. These items collect information about your browsing habits and can continue to be present on the browser even after the program is uninstalled, leading to further data collection.
Therefore, it's recommended to delete these leftover files from your system after removing unwanted applications. To do this, you can use a reliable cleaning tool like FortectIntego or follow the manual steps provided below:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

How to prevent from getting browser hijacker
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
