Torpig (Removal Instructions) - updated Feb 2018
Torpig Removal Guide
What is Torpig?
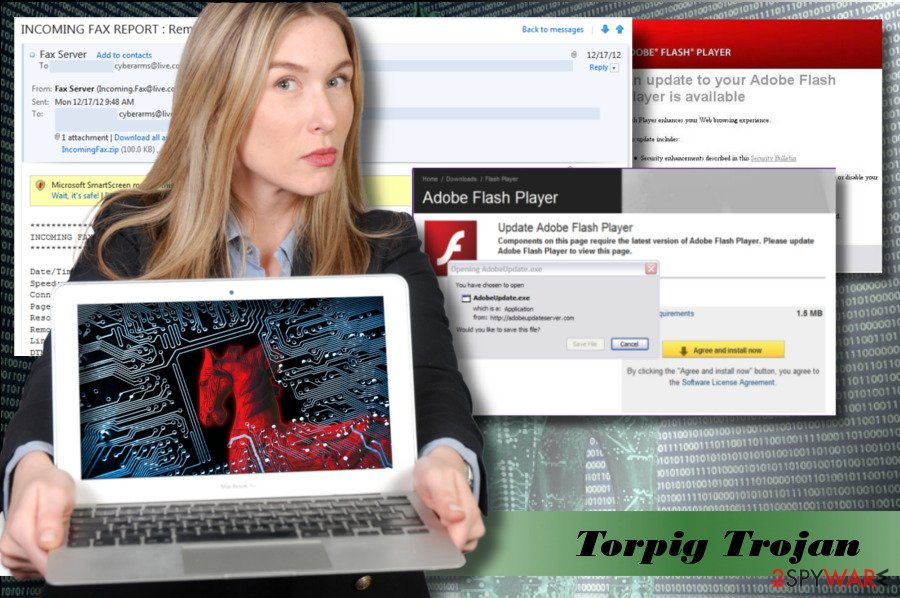
Torpig – a malicious Trojan Horse that can steal sensitive data
Torpig is a severely malicious Trojan Horse,[1] which has been revealed in 2005. Since then, cybersecurity experts managed to keep it shut for ten years, but its developers eventually released the Trojan and started its second expansion wave. It's also known and Anserin or Sinowal family[2] and is responsible for the extortion of personal information, such as credit card details, login details, passwords, and similar information that would later allow hackers to take full control over a target system.
In most of the cases, it spreads via systems compromised by the Mebroot rootkit. Mac OS X users are immune to Torpig virus, but Windows OS users, especially those who use older versions, such as Windows 7, XP, Vista, should be careful with this Trojan.
Torpig malware renders anti-virus software useless, so the first sign of this cyber infection on the system is the inability to launch a scan with your antivirus or to open it at all. It may also block security-related websites on a web browser, abort downloads of anti-virus, anti-malware, and optimization tools with inbuilt AV engines.
The Trojan can also modify data on a target computer. The Trojan can delete some crucial system's files, disable some processes or even change extensions of some personal files (pictures, videos or documents). Not to mention, if the virus manages to detect credentials allowing hackers to access the system remotely, it may initiate massive leakage of personal information. That's why it's a must to remove Torpig Trojan from the system ASAP.
There's a straightforward answer to the question how to get rid of Torpig virus – use a professional anti-virus. Even though it blocks anti-virus, it doesn't mean that the security tool cannot be launched. In most of the cases, people can perform Torpig removal with FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes after they reboot the system into Safe Mode with Networking. Unfortunately, it's not possible to remove this trojan horse manually.
Torpig malware is dubbed as on of the most “successful” Trojan infections
Cybersecurity researchers have initiated an in-depth analysis of this malware. After the investigation, the researchers agreed upon the fact that this cyber threat will enter history as one of the most significant bank account and credit card stealers.[3] Ten years ago it was estimated that Torpig attacked 500,000 online bank accounts and credit and debit cards.
Besides, University of California, Santa Barbara revealed over 70 GB of stolen data.[4] They have also found that Torpig Trojan managed to retrieve login information for 8,310 accounts at 410 different institutions, and 1,660 unique credit and debit card numbers from victims in the U.S. (49%), Italy (12%), Spain (8%), and 40 other countries. It's important to stress the fact that the numbers we've just listed were revealed in 2009, so they might have multiplied within a decade.
Keep the system updates to protect from Trojan attacks
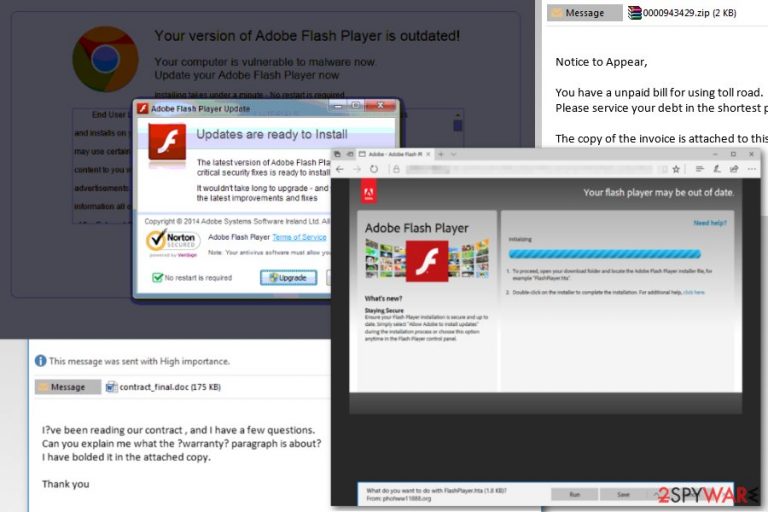
The prevailing strategy used by developers of this Trojan Horse is snap emails that contain malicious .DOCX attachments. The virus is activated as soon as the PC's user agrees to enable Macros.
Apart from malspam campaigns, hackers may spread this Trojan via malicious advertisements, which exploit outdated versions of Java, Acrobat, Flash, Shockwave, and other software. This method is known as drive-by-download since it does not require user's intervention. If the software recognizes software vulnerability, the virus is executed even if the user does not interfere with the advertisement in any way. To prevent this from happening, cyber security experts from NoVirus.co[5] recommend people to update software regularly.
Not to mention, malware can also be distributed via malicious update offers, such as to update Java or Flash Player. Do not fall for such tricks. If you have doubts that your software is out-of-date, navigate to the official website and download it directly.
Learn how to remove Torpig virus easily
The first stage of Torpig virus attack is the most important. The malware managed to transmit the bulk of targeted credentials (credit card details, passwords, name, email account logins, FTP credentials, Windows account password, etc.) within twenty minutes of the attack. If your PC restarted all of a sudden after opening an email attachment or browsing on the doubtful web browser, there's a risk that a Trojan forced your PC to reboot to finish up execution.
If you have a slightest suspect, try to scan your PC with a professional anti-malware (e.g. FortectIntego, Malwarebytes) and remove Torpig virus from the system. The sooner you get rid of it, the lower the risk of data leakage will be. Most of AV engines recognize this malware as Troj/Torpig-A, but it can also be recognized as crapware or spyware.
You may ask how to get rid of Torpig virus if it blocks your antivirus. It's a fact that you won't be able to remove it manually. All you have to do to get rid of this malware is to unblock your security tool, and the below-given guide will help you to do so.
Getting rid of Torpig. Follow these steps
Manual removal using Safe Mode
If Torpig blocks your antivirus, you may need to restart your PC in Safe Mode with Networking and then try to start your anti virus again.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Torpig using System Restore
If the previous method did not work, try the following steps:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Torpig. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Torpig from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Torpig, you can use several methods to restore them:
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Torpig and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Torpig. Carnegie Mellon University.
- ^ Andra Haharia. Top 10: Most Dangerous Malware That Can Empty Your Bank Account. Heimdal Security. Software developer.
- ^ Ryan Naraine. Botnet hijack: Inside the Torpig malware operation. ZDNet. 24/7 news coverage and analysis on the trends.
- ^ Mary Landesman. Trojan Horse Malware. Lifewire. Practical advice on how to live better with technology.
- ^ NoVirus. NoVirus. Spyware and Virus News.







