Trojan.Mdropper.AC (Free Guide) - Virus Removal Instructions
Trojan.Mdropper.AC Removal Guide
What is Trojan.Mdropper.AC?
Trojan.Mdropper.AC is yet another Trojan virus that affects the machine from the inside
Trojan.Mdropper.AC is the malicious malware piece that infiltrates the machine and can act as a dropper for other infections. This is the threat that runs in the background and can launch processes, install ransomware, and other more damaging viruses behind your back. The virus is used since 2005 and can be employed as a tool for the trojan or different types of infection distribution. You can notice the particular detection on the machine and mainly out of nowhere. If so happens – make sure to remove it as soon as possible.
| Name | Trojan.Mdropper.AC |
|---|---|
| Type | Trojan |
| Issues | This malware acts as a vector for other threats |
| Distribution | Malicious email attachments or dangerous sites can be the way to spread these threats around |
| Elimination | You should eliminate this malware by following the guide below or employing an anti-malware tool |
| Repair | Malware can alter various parts of the machine, so make sure to repair damage with FortectIntego |
Trojan.Mdropper.AC is the dropper malware, hence the name. It means that the virus itself is not causing any symptoms, in most cases. It focuses on running processes that can open backdoors for other intruders or dropping the code directly on the machine by connecting to a remote server that criminals control.
This parasite spreads itself and infects other computers using Microsoft Excel Unspecified Remote Code Execution Vulnerability (BID 33870). It creates a rundll.exe executable file that has the ability to download additional malware and execute it onto the infected computer. It is obvious, that this infection should be removed, otherwise it can do more harm to the system.
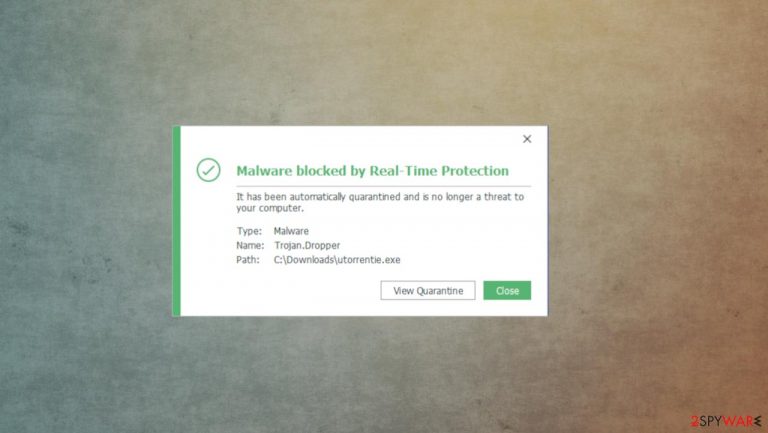
Trojan.Mdropper.AC can load itself or additional files on the memory of the PC, so you not only need to remove the virus using SpyHunter 5Combo Cleaner or Malwarebytes, but you need to repair such damage. Remove anything that security tools detect and indicate as malicious for you. The best way to recover from malicious installations and all the setting changes or virus damage is to rely on the application like FortectIntego.
Trojans can be easily disguised as other files
The main issue with this trojan, worm, and other silent malware types – distribution ways that do not require users' consent or permission. Malicious pieces can be added to email notifications, injected on dangerous websites, or acting as commonly found files on the machine.
Trojans can be used to spread infections while disguised as doc or xls, exe, dll files. You can get the malicious files from the email attachment or during the pirated software installation. Unfortunately, there are no indications that the file is malicious if your AV tool is not detecting any suspicious features about the piece.
You can avoid such infections by paying attention to details like senders, company names, emails that these notifications come from. If you spot anything suspicious – do not open the email and do not download the attached file. As for software and pirating – always go for official sources and do not skip installation steps, so you can see all the included pieces.
Make sure to eliminate any trojans and other malware with AV tools
You should tackle the infection properly and clear any intruders by fully scanning the system. It can be done using anti-malware tools like SpyHunter 5Combo Cleaner or Malwarebytes, so you should run a tool like this and remove Trojan.Mdropper.AC. You can't find all the pieces manually, so automatic elimination is the only way
Since the particular threat is malware infecting the machine in stages, there are various files and processes, programs planted in different parts of the system. You should follow the guide below that shows additional methods helping with the proper Trojan.Mdropper.AC removal. Then you can run a tool like FortectIntego and repair any virus damage.
Getting rid of Trojan.Mdropper.AC. Follow these steps
Scan your system with anti-malware
If you are a victim of ransomware, you should employ anti-malware software for its removal. Some ransomware can self-destruct after the file encryption process is finished. Even in such cases, malware might leave various data-stealing modules or could operate in conjunction with other malicious programs on your device.
SpyHunter 5Combo Cleaner or Malwarebytes can detect and eliminate all ransomware-related files, additional modules, along with other viruses that could be hiding on your system. The security software is really easy to use and does not require any prior IT knowledge to succeed in the malware removal process.
Repair damaged system components
Once a computer is infected with malware, its system is changed to operate differently. For example, an infection can alter the Windows registry database, damage vital bootup and other sections, delete or corrupt DLL files, etc. Once a system file is damaged by malware, antivirus software is not capable of doing anything about it, leaving it just the way it is. Consequently, users might experience performance, stability, and usability issues, to the point where a full Windows reinstall is required.
Therefore, we highly recommend using a one-of-a-kind, patented technology of FortectIntego repair. Not only can it fix virus damage after the infection, but it is also capable of removing malware that has already broken into the system thanks to several engines used by the program. Besides, the application is also capable of fixing various Windows-related issues that are not caused by malware infections, for example, Blue Screen errors, freezes, registry errors, damaged DLLs, etc.
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe

- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process

- The analysis of your machine will begin immediately

- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.

By employing FortectIntego, you would not have to worry about future computer issues, as most of them could be fixed quickly by performing a full system scan at any time. Most importantly, you could avoid the tedious process of Windows reinstallation in case things go very wrong due to one reason or another.
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Trojan.Mdropper.AC and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
