Sirefef (Virus Removal Guide) - updated Dec 2019
Sirefef Removal Guide
What is Sirefef?
Sirefef – prolific malware that seeks to open a backdoor on the host machine

Sirefef, or otherwise known as ZeroAccess or max++, is a malware-dropper that is known for its ability to hide itself on the infected computer. Numerous versions of the threat have been released over the years, although its main function is to gather relevant information about the machine and then use it as a tool to insert additional malware payloads. Rootkit.sirefef.spy distribution methods can vary, although it is usually proliferated with the help of other malware, such as Necurs Trojan.
Sirefef virus is a multi-functional malware, meaning that it employs several modules that perform different tasks on the system. For example, one component is set to open a backdoor, another one – block the firewall and security software, the next one can be used for downloading malicious files and updates from the internet, and so on. Besides, Rootkit.sirefef.spy trojan can also intercept and redirect HTTP traffic[1] to pre-determined sites, consequently generating ad revenue for the attackers.
| Name | Sirefef |
| Type | Trojan, rootkit, backdoor |
| Also known as | Rootkit.sirefef.spy, ZeroAccess, Zero Access, max++, Win32/Sirefef, Patched.B.Gen |
| Operating system | All versions of Windows (64 and 32-bit) |
| Distribution | Security researchers noticed various versions of Sirefef being distributed via software cracks/keygens, exploits or by exploiting software vulnerabilities |
| Functionality |
The malware is multi-functional, and can be set to perform a variety of different tasks, including, but not limited to:
|
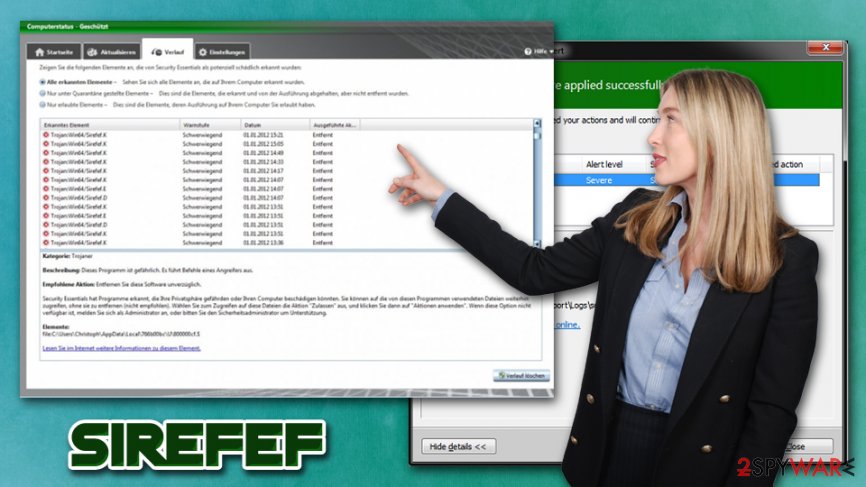
| Symptoms | The only infection indicator is the warnings from security software (if not disabled). In some rare cases, victims might notice increased amount of ads, high CPU/memory usage, crashing programs, etc. |
| Removal | Use most up-to-date security software and perform a full system scan in Safe Mode with Networking |
| Recovery | To restore Windows registry and recover from system crashes post-infection, use FortectIntego |
Because Rootkit.sirefef.spy is a Trojan and its functionality mainly consists of background activities, it can remain on the system undetected for days or even months. However, because some variants of the virus are known to redirect traffic to unknown domains, aggressive ads and redirects on Google Chrome, Mozilla Firefox, Internet Explorer or another browser can serve as a good sign of system compromise.
However, be aware that the Sirefef rootkit is not the only threat that can cause browser redirects, as it is also a functionality of adware, as well as browser hijackers, which are both much lesser threats than Rootkit.sirefef.spy Trojan. The best way to check for malicious activity is to scan the computer with anti-malware software, such as SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable security program.
Other symptoms that might be related to Rootkit.sirefef.spy infection includes (although users will rarely experience anything at all, making the detection and Sirefef removal a much more complicated task):
- High CPU or memory usage
- Crashing applications or Windows
- Overall slow computer operation
It is important to note that Sirefef Trojan can disable some security applications post-infection, which only increases its prevalence n the infected device. Due to this, as well as the low occurrence of signs of the infection, users might not be aware that they are infected for weeks or even months. This is why regular computer scans with anti-malware are so important. As evident, if you have an anti-malware installed and it is not performing pre-determined scans, there is a good chance that malware like Rootkit.sirefef.spy has disabled it.
To remove Sirefef rootkit and to prevent from stopping the anti-virus, experts[2] advise accessing Safe Mode with Networking and performing a full system scan with anti-malware software. The Safe Mode launches with only necessary drivers and system components, disabling malware' functions.
However, be aware that rootkits and other malicious software might permanently damage system components on Windows. To repair that damage done by viruses, we suggest employing a PC repair tool FortectIntego.
Infection routine
As previously mentioned, there have been multiple Sirefef variants released over the years, and each possesses some differences from another version, and distribution, prevalence, and obfuscation techniques may vary.
Some of the variants were noticed to come as an executable GoogleUpdate.exe – it is very common for malicious actors to disguise the primary executable under legitimate names to prevent users from being suspicious. The executable is placed into a newly created folder inside the %ProgramFiles% and %APPDATA% directories, begging the infection routine.
Rootkit.sirefef.spy also initiates changes inside Windows registry,[3] modifying the following keys:
HKCU\Software\Microsoft\Windows\CurrentVersion\Run
HKLM\Software\Classes\clsid\{5839fca9-774d-42a1-acda-d6a79037f57f}\InprocServer32
Sirefef also creates a separate folder here multiple files are dropped, and the malicious code inside is used to communicate with other infected devices as well as attackers' servers via peer-to-peer. This ensures that hackers can enable new functions or update malware when desired remotely.
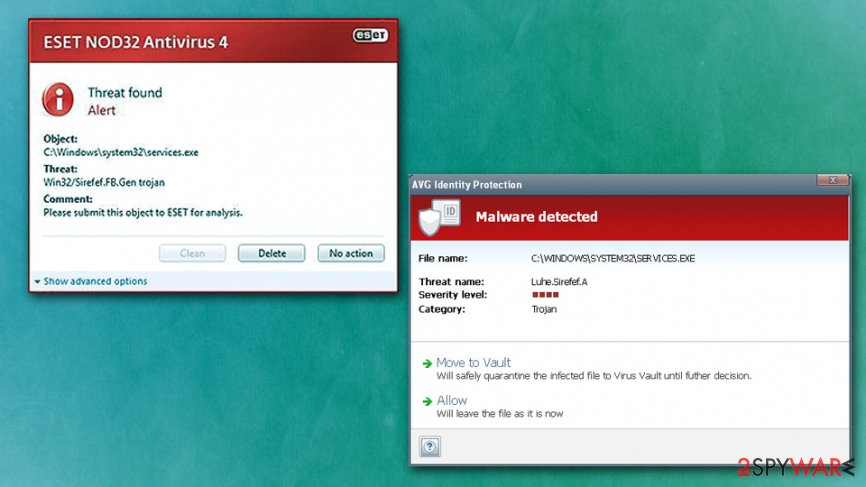
Rootkit.sirefef.spy tampers with system drivers by replacing legitimate ones with malicious ones. These drivers might be picked up by AV vendors as Virus:Win32/Sirefef or TrojanDropper:Win32/Sirefef.B. Additionally, the malware turns off various system components that are vital to secure OS, including Windows Firewall, Windows Update, RemoteAccess, etc.
Pirated software installers and software vulnerabilities are the most common attack vectors
Most of the users will come close to malicious attacks when using Windows computers, but whether they infect them with malware depends on multiple factors, and the most important one is awareness. As evident, acting responsibly online and secure the OS with powerful anti-malware software will bring the best results.
First thing's first: do not download pirated software, as well as keygens/cracks that can enable full version of the program that is otherwise not free. Torrent and similar P2P networks are known to be insecure as not much effort are put into protecting users on those sites. In fact, some website owners allow malicious actors to insert JavaScript-based ads that would download and install malware automatically (by exploiting software vulnerabilities).[4]
To avoid the latter, you need to ensure that all your browsers and the operating system are running the latest versions. For that, you should never delay the updates and rather enable the auto-update feature.
Access Safe Mode to remove Sirefef virus
Trojans are very malicious cyber threats, so it is important to remove Sirefef from your computer because it may not only use it and your Internet resources for illegal purposes, it can also try to delete your valuable files, steal your sensitive information and so on. Additionally, it may open a remote control connection to your PC and let additional threats inside your computer.
When trying to perform Sirefef removal on your system, it may kill your anti-spyware and its processes. The easiest way to bypass this functionality is by entering Safe Mode with Networking, as explained in the instructions below. Once inside, you should employ the most up-to-date anti-malware tool and run a full system scan.
Getting rid of Sirefef. Follow these steps
Manual removal using Safe Mode
Rootkit.sirefef.spy can disable various anti-malware tools, along with other security components, in order to prevent its removal. Access Safe Mode with Networking and perform a full system scan:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Sirefef and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Elie Bursztein. Understanding the prevalence of web traffic interception. Elie. Security blog.
- ^ Bedynet. Bedynet. Security advice from Russia.
- ^ Tim Fisher. What Is the Windows Registry?. Lifewire. Tech Untangled.
- ^ Vulnerability (computing). Wikipedia. The free encyclopedia.














