Trojan/Win64.Meterpreter (Virus Removal Instructions) - Tutorial
Trojan/Win64.Meterpreter Removal Guide
What is Trojan/Win64.Meterpreter?
Trojan/Win64.Meterpreter is not a false positive detection – it's an activity sign of a dangerous Meterpreter banking trojan

Trojan/Win64.Meterpreter is a generic threat detection name that can be brought by any reputable AV engine, but most frequently it's triggered by Windows Defender, Ikarus, and Malwarebytes[1]. Although some discussion forums contain false discussions saying that this detection is false positive, seeing this detection is a serious warning about the presence of a malicious Trojan horse infection.
The Trojan/Win64.Meterpreter is a heuristic name displayed by AV tools, though it directly points to a password-stealing banking Trojan dubbed as Meterpreter. The malware can disguise under legitimate Windows system files, such as explorer.exe to create persistence and prevent removal.
Meterpreter Trojan is a cyber infection developed on the bases of the Metasploit Framework[2]. It may be distributed via infected HTTP servers, fake downloads, cracks, pirated software, or spam email attachments. Once the malicious payload is launched, the Trojan seeks to create persistence, connect to the C2 server, and regularly record data intending to steal passwords, credit card info, and other highly-sensitive credentials.
| NAME | Trojan/Win64.Meterpreter |
| CLASSIFICATION | Banking Trojan, Malware |
| ALSO KNOWN AS | Meterpreter Trojan |
| SYMPTOMS | If the Trojan is silently running on the machine, people should notice a significant decrease in PC's performance, high CPU usage by suspicious processes, Internet speed slowdowns, etc. |
| FILES | Tend to misuse explorer.exe file. The main executable – trabajo.docm |
| DISTRIBUTION | The Trojan spreads via infected HTTP servers, fake software updates, malicious spam attachments, etc. |
| MAIN DANGERS | It seeks to leak users' passwords, credit card details, and other credentials that are required for banking operations |
| REMOVAL OPTIONS | The only way to eliminate a Trojan – fully scan the system with a robust anti-virus program |
| Trojans initiate loads of unauthorized distortions on the machine, including registry removal, disabling of crucial processes, injection of useless files, etc. The system damage may be recovered by FortectIntego software. | |
The Trojan/Win64.Meterpreter detection can be found on the system by various AV tools automatically or when running a full scan with it. In case of a false-positive, you should receive the alert without noticing other system malfunctions, including slowdowns, high CPU, or unknown files running (explorer.exe, trabajo.docm, etc.).
In some rare cases, the Trojan/Win64.Meterpreter virus alarm can be triggered by software inconsistencies. Some people reported that the detection stopped from being reported after eliminating the remnants of security software, for instance, Avast. If you have been using a security tool and uninstalled it inappropriately (without eliminating its registries), the remnants can eventually trigger false positive detections by the new AV engine. In this case, FortectIntego repair tool might help.
However, we recommend people to take precautionary measures and protect their credentials by initiating a full Trojan/Win64.Meterpreter removal. If your AV tool brought you such detection, it's most likely that the system is infected by a malicious Meterpreter Trojan horse, which seeks to steal usernames, passwords, other credentials, or information that is required to perform certain banking operations or launch particular commands.
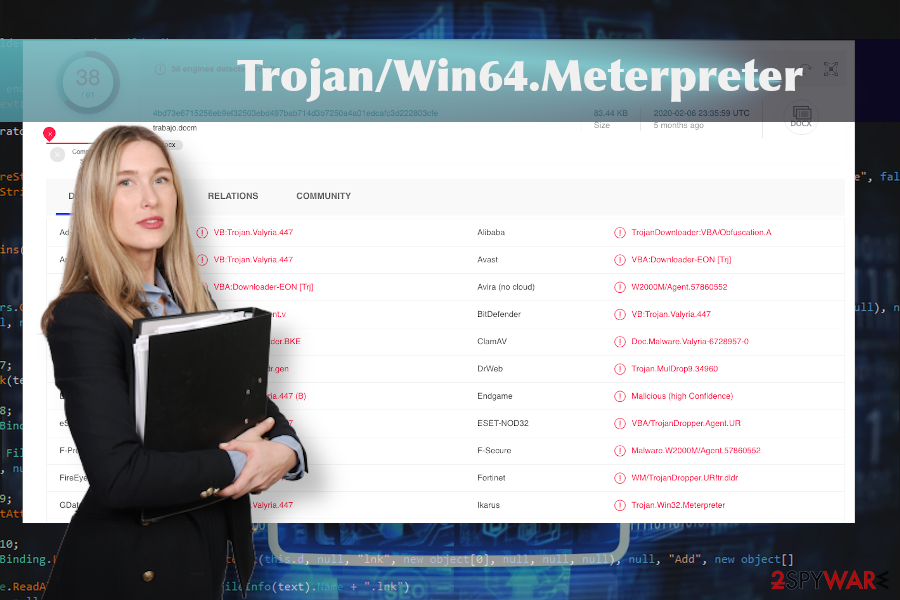
If you cannot decide whether the Trojan/Win64.Meterpreter is a false-positive or Meterpreter virus, we strongly recommend downloading alternative security software and double-checking the machine. At the moment, the Meterpreter-virus related files are identified as malicious by 38 AV engines out of 61. Other detection names indicate the virus as:
- VBA:Downloader-EON [Trj] (AVG)
- VB:Trojan.Valyria.447 (B) (Emsisoft)
- Troj/FatRat-F (Sophos)
- VB:Trojan.Valyria.447 (BitDefender)
- VBA/TrojanDropper.Agent.UR (ESET)
- Trojan:Win32/Meterpreter.gen!C (Windows Defender), etc.
If this Trojan/Win64.Meterpreter virus infiltrates the Windows machine, it performs malicious processes in the background and connects to the remote server to provide the criminals behind the trojan with the collected data. Usually, banking trojans[3] are provided with features recording keystrokes, stealing browser's data, harvesting credentials, installing other malicious programs, injecting intrusive content on the web browsers, and more.
Nevertheless, if you have already noticed a suspicious system's behavior and the symptoms of possible trojan infection, arm yourself with the reputable anti-virus, restart your machine into Safe Mode with Networking, and run a full scan to remove Trojan/Win64.Meterpreter from the machine completely.
You should remove Trojan/Win64.Meterpreter as soon as possible to prevent the malware from causing the damage. The longer it is kept, the more files or functions it can modify. Finally, check the system for any possible damage using a reliable optimization utility, such as FortectIntego. This program has been developed with an intention to maintain Windows OS stability and performance, so take advantage of its advanced scanner regularly.
Infected files and sites often work as a mediator between Trojans and the target machine
Most of the malicious programs that run in the background aim at performing some stealing and hacking activities. Thus, it would be naive that they will ask for permission to get installed directly. To hide malicious infections and inject them suspiciously hackers render various social engineering strategies.
One of the most common ways to seed Trojans onto the machines of unsuspecting users is to complement system cracks, keygens, or other pirated content with the trojan payload. If such a file is downloaded and launched, the virus is activated and starts performing in the background. For this reason, experts[4] recommend staying away from illegal software that is available on torrent sites, p2p platforms, pirating services, and other shady sites.
In addition, domains that are not certified do not feature a secure HTTPs protocol and proof of being protected is an easy target for hackers. Such domains can be injected with malicious javascript codes that can display fake software updates, display infected ads, click-to-download commercials, and other dangerous content.

Automatic Trojan/Win64.Meterpreter removal is the only way that can help
It's important to remove Trojan/Win64.Meterpreter virus if the AV tool warns you about its presence unless you don't mind hackers to be recording your credentials. Running SpyHunter 5Combo Cleaner or Malwarebytes while in Safe Mode with Networking should help to delete the malicious trojan from the system and other programs that pose danger to your PC's security.
In fact, Safe Mode is not crucial, so you can try to launch the scanner while in the regular mode. However, there's a high probability that the Trojan/Win64.Meterpreter removal simply won't work because the AV tool may be left idle by malicious virus-related processes. In this case, Safe Mode disables non-core system files and allows launching the anti-virus.
Getting rid of Trojan/Win64.Meterpreter. Follow these steps
Manual removal using Safe Mode
If you have never booted Windows into Safe Mode, the guide below will help you navigate this procedure easily.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Trojan/Win64.Meterpreter using System Restore
If Safe Mode did not work for you, try to remove Meterpreter trojan virus using the System Restore function.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Trojan/Win64.Meterpreter. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Trojan/Win64.Meterpreter and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ trabajo.docm. VirusTotal. Free file and URL scanner.
- ^ Halis BAS. How to make trojan using metasploit?. Medium. A guide on technology news.
- ^ ThreatList: Banking Trojans Are Still The Top Big Bad for Email. ThreatPost. Virus and spyware news.
- ^ SAUGUMO IR VIRUSŲ NAUJIENOS. Virusai. Virus and spyware news.







