2021 update. How to remove Trotux in 7 easy steps
Trotux.com virus Removal Guide
What is Trotux.com virus?
Trotux is a browser hijacker that uses stealthy techniques to stay on the system and collect browsing-related information

Trotux is a browser hijacker that has been affecting computer systems since 2016. It infiltrates the system without any notice and then alters target web browsers to redirect its victims to www.trotux.com. If you try to modify these settings back to normal, the virus uses Windows services and its own components to recover these settings. As a result, numerous tech forums have been filled with questions about the removal of this virus.[1] However, at the moment of writing, this potentially unwanted program[2] is detected as safe. Nevertheless, you should not deal with Trotux virus as it starts causing redirects and pop-up ads right after it settles down on the system. Additionally, it silently tracks your browsing habits and personal information like IP address, location, email address, etc.
| Name | Trotux |
|---|---|
| Type | Browser hijacker |
| Category | Potentially unwanted program |
| Detected as | Adware/ShortcutHijacker (Malwarebytes antimalware) |
| Symptoms | Alters system settings, causes redirects and pop-up ads, fails to leave the system when asked |
| Distribution | Software bundles, fake ads, misleading official site |
| Main danger | Collects various information about the user, redirects to possibly malicious sites |
| Elimination | Use FortectIntego for general system cleaning |
Trotux browser hijacker can easily infiltrate your compute without your permission which is a clear indicator that there is something suspicious about this program. However, stealthy system hijack is just the beginning.
As soon as Trotux.com hijack is finished, this virus immediately goes for your browser and starts altering its settings. Therefore, it is likely that the first thing you will notice when this virus settles on your system will be the changes in your browser. Do not be surprised if one day, after opening your browser, you will find this hijacker instead of your regular search engine.
It is also important to remember that this virus will try to remain on your browser for as long as possible by altering your DNS settings [3] and installing additional software, such as toolbars and extensions. Besides, Trotux collaboration with another hijacker, which is called iwatchavi.com, is another reason for mistrusting this program.
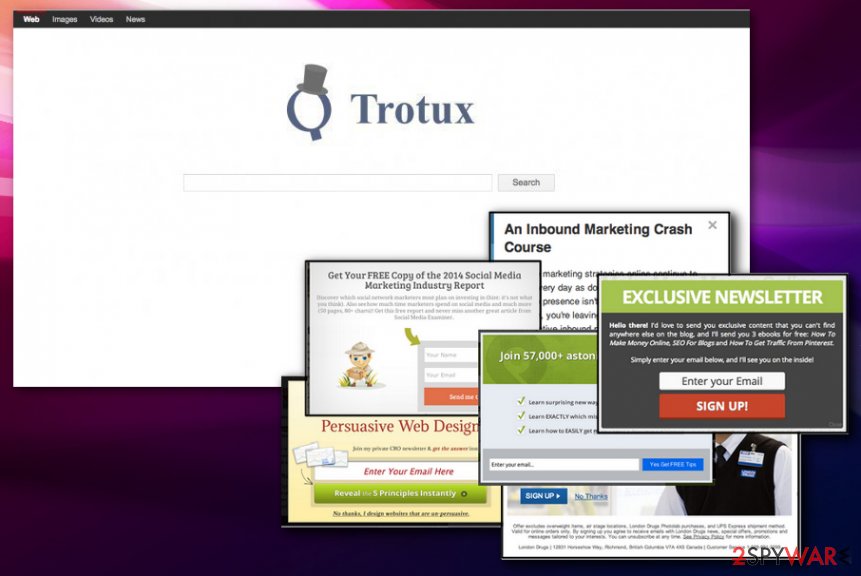
As we have already discussed, this browser hijacker adjusts homepage plus the new tab page settings and redirects users to a particular search engine page that is shown in the picture above. If you click the “About” link provided at the bottom of this site, it will open the author’s note which introduces this search engine as a useful and innovative web browsing tool.
The note claims that Trotux virus compiles “results from many of the Web's major search properties, delivering more relevant and comprehensive results. The search results you receive include the top commercial (sponsored advertising) [results] and non-commercial (algorithmic) results from the most popular search engines on the Web.”
However, according to our research, other shady search engines, such as safehomepage.com, nuesearch.com or dogpile.com also promise the same thing. Sadly, all these search tools are associated with browser hijackers which are actively distributed all around the web. Many users complain about these search tools and are actively looking for their removal tutorials, including Trotux removal.

Besides hijacking of the browser’s settings, the virus also causes redirect issue on every target computer system. is also one of the most concerning features worth mentioning when talking about the program’s malicious tendencies. Each time you enter the web browser your home page is redirected to Trotux.com and every click on the browser and pop-up windows opens at least a few news windows or tabs. This search engine reportedly delivers rigged search results, which hold vague and questionable hyperlinks.
Once activated, these hyperlinks can reroute the user to highly suspicious Internet sites and, consequently, puts user's privacy and computer security in danger. These web pages that promote themselves via such shady search engines can be filled with dangerous content, so it is advisable to stay clear of them.
It is important to remove Trotux engine from your browser because it is a pure gateway for the potentially unwanted programs to enter your PC. Since the main technique of distribution is software bundles there is a possibility of already installed unwanted programs or tools:
- rogue optimization tools;
- browser extensions;
- background processes;
- adware programs;
- bookmarks;
- toolbars.
If the question “why Trotux keeps coming back” is your primary concern, you should look at Trotux removal guidelines provided at the end of this article. Our spyware research team has prepared this virus elimination tutorial for users who do not have an anti-spyware program or just wish to eliminate this hijacker manually. [4] If you really do not wish to be bothered with the elimination of this browser parasite, just scan your system with Malwarebytes. Additionally, run FortectIntego to make sure that your PC is clean from spyware and malware infections automatically.

PUP infiltration can be avoided
There are numerous ways computer viruses can enter computers. However, every family of cyber threats has their typical ways of spreading [5]. Speaking of distribution methods used to spread potentially unwanted programs, the most frequently used technique is called software bundling. Briefly said, PUPs secretly install with other programs without the user’s consent.
To avoid being tricked into installing potentially dangerous software, always read through the EULA [6] and other software documents. In the downloaded program’s setup choose “Advanced” installation mode and inspect all the programs in the software package content list. If you see some suspicious applications, cancel them immediately and proceed with the installation as usual.
Trotux removal FAQ:
Question by Allen, 21: Hey. I was wondering what antivirus software would be most suitable for the Trotux removal? I am currently a college student so I cannot afford expensive antivirus suites. Can you suggest any free or some inexpensive solutions I could try?
Answer: Dear Allen. We are glad you are concerned about the health of your system. Despite the common misconception, you do not necessarily need expensive software to keep your computer clean and protected. There are free anti-malware utilities like SpyHunter 5Combo Cleaner that may help you keep on top your computer's security and remove any undesirable malware, including Trotux with a couple of mouse clicks.
Question by Daniele, 34: In your articles, you claim that it is necessary to reset the browser after you remove Trotux from the computer. Does this condition remain when malware removal is carried out automatically, i.e. using some sort of antivirus or anti-malware program?
Answer: Thank you for your question, Daniele. No matter what methods you use to get rid of Trotux from your computer, it is absolutely necessary to reset all browsers that have been infected by this hijacker. Please remember that hijackers may install additional browser extensions, toolbars or other components on your browser in order to secure their place in your system. Antivirus utilities may remove them from the computer, but it will not uninstall these browser add-ons from your browser; therefore, you may continue to experience interruptions and other inconveniences when browsing the web. Thus, we highly recommend dedicating a few minutes of your time to clean your browsers and start fresh.
Question by George, 49: Can Mac OS X be infected with Trotux? I mean, what should I do if I find this site on Safari?
Answer: Dear George. Unfortunately, Mac OS X users are regularly reporting infections even though this virus was initially thought to be exclusively Windows-based. This means that your Safari browser is not longer safe from this malware and can get infected. If this happens to your Web engine, do not panic — you can take the hijack under your control. Antivirus utilities such as Malwarebytes can fix the problem in just a few minutes, but if you do not wish to invest your money into malware-fighting equipment, you may as well delete Trotux manually.
Trotux elimination require professional help
There are two ways to banish potentially unwanted programs, such as this browser hijacker, from the infected device one and for all. More experienced users usually take the manual approach. However, if you have not dealt with virus elimination before, the whole Trotux removal process may seem quite intimidating. it is more advisable to use anti-malware programs and PC repair tools to clean your system thoroughly.
Luckily, you can delete this infection from your computer automatically as well. With respectable antivirus utilities, you will be able to achieve that in just a few clicks. Additionally, the software will scan your whole computer to find other malware, potentially hiding in your system.
Nevertheless, if you wish to remove Trotux virus manually, read through the instructions provided below this article to avoid elimination errors. If you encounter any uninstall issues, do not hesitate to contact us, and we will do our best to help you get rid of this clingy virus.
As we have already mentioned, this browser hijacker may try to mess up your DNS settings. If you want to make sure that they are fine, follow these steps right after uninstalling Trotux:
- Go to “Control Panel”-> “Network and Internet” -> “Network and Sharing Center”-> “Change Adapter Settings”. here, you should reveal your active Internet connection.
- Right-click this option and select “Properties”.
- Look for “Internet Protocol Version 4 (TCP/IPv4)”, select it and click on “Properties” one more time.
- Once “Properties” window shows up, make sure that “Obtain an IP address automatically” and “Obtain DNS server address automatically!” are selected. As we have already warned you, this hijacker may try to change these settings.
- Select “OK” to save changes.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Trotux.com virus. Follow these steps
Uninstall from Windows
If your Windows OS was hijacked by Trotux Search virus, you need to uninstall all entries that could be related to this browser hijacker.
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
To fix Mac OS X, you need to uninstall everything that is related to this hijacker.
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
If Trotux has breached your Microsoft Edge protection and installed itself on this browser, you should remove it immediately. We have prepared a tutorial below to help you with the elimination.
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
If your Mozilla Firefox is affected by this hijacker, we highly recommend removing Trotux add-on and other entries from this browser by following these steps:
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Trotux elimination from Google Chrome is explained in detail below:
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Trotux.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting browser hijacker
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Need help to remove Trotux. Cnet Computer Help forum.
- ^ What does Potentially Unwanted Program (PUP) mean?. Technopedia. IT Dictionary.
- ^ Definition of DNS. PC Magazine. complete guide to PC computers, peripherals and upgrades.
- ^ Craig Snyder. How To Clean A Hijacked Web Browser. Makeuseof. Technology, Simplified.
- ^ How Do Computers Get Viruses?. Top Ten Reviews. Expert Product Reviews.
- ^ What is EULA?. Wikipedia. The free encyclopedia.
