.ufwj file virus (Bonus: Decryption Steps) - Recovery Instructions Included
.ufwj file virus Removal Guide
What is .ufwj file virus?
Ufwj ransomware is a virus created by criminals claiming to have the only file recovery tool which costs $980
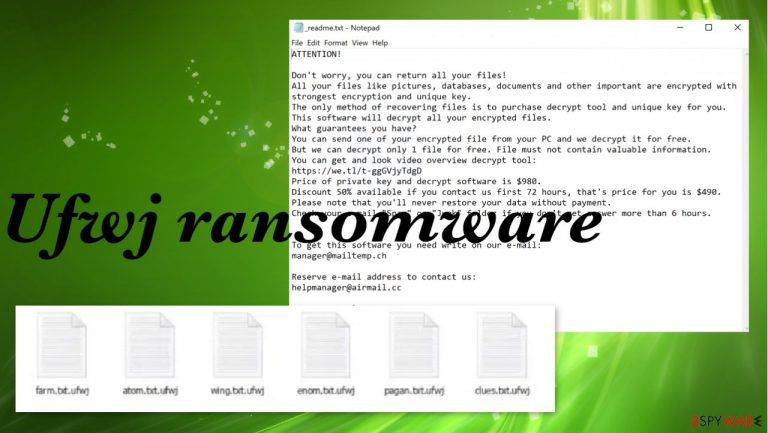
Ufwj ransomware is a virus that encrypts your files and demands payment for the decryption key right away. The infection usually goes unnoticed until it causes havoc on one's computer and the ransom note appears on the screen. The _readme.txt piece gets placed in various folders with affected data and even put on the desktop, so users read the message once the encryption is done.
This cyber infection starts making changes to system settings without asking permission or informing you beforehand of its nefarious intentions and affects the speed. Otherwise, the infiltration is unnoticed for a while. However, the encryption happens quite quickly and malware can affect your files immediately after the infiltration, so you might trigger the launch of the virus, but the reaction cannot be speedy enough.
This is the Djvu ransomware version. These viruses work by attacking unsuspecting victims with various silent methods that leave no trace behind once executed successfully. Ufwj ransomware is the threat listed as one of the 300 versions. Creators release at least one a week for the past year, and not much is changed about each of them. The file-encrypting malware uses encryption algorithms to lock commonly used files and then marks them with a unique .ufwj appendix.
The ransomware is a cryptocurrency extortion-based virus, so creators are only aiming to get money from victims. Paying them or following steps listed in ransom note _readme.txt is useless and dangerous. You risk getting another malware sent to you and losing not only your files but your money.
Ufwj ransomware is a sophisticated new version of malicious software that extorts you for money. File-locking is the main function, but you need to worry about the security of the PC first. Recovering files before virus termination can be crucial. If the malware is still active, all newly added files can be encoded and locked permanently.
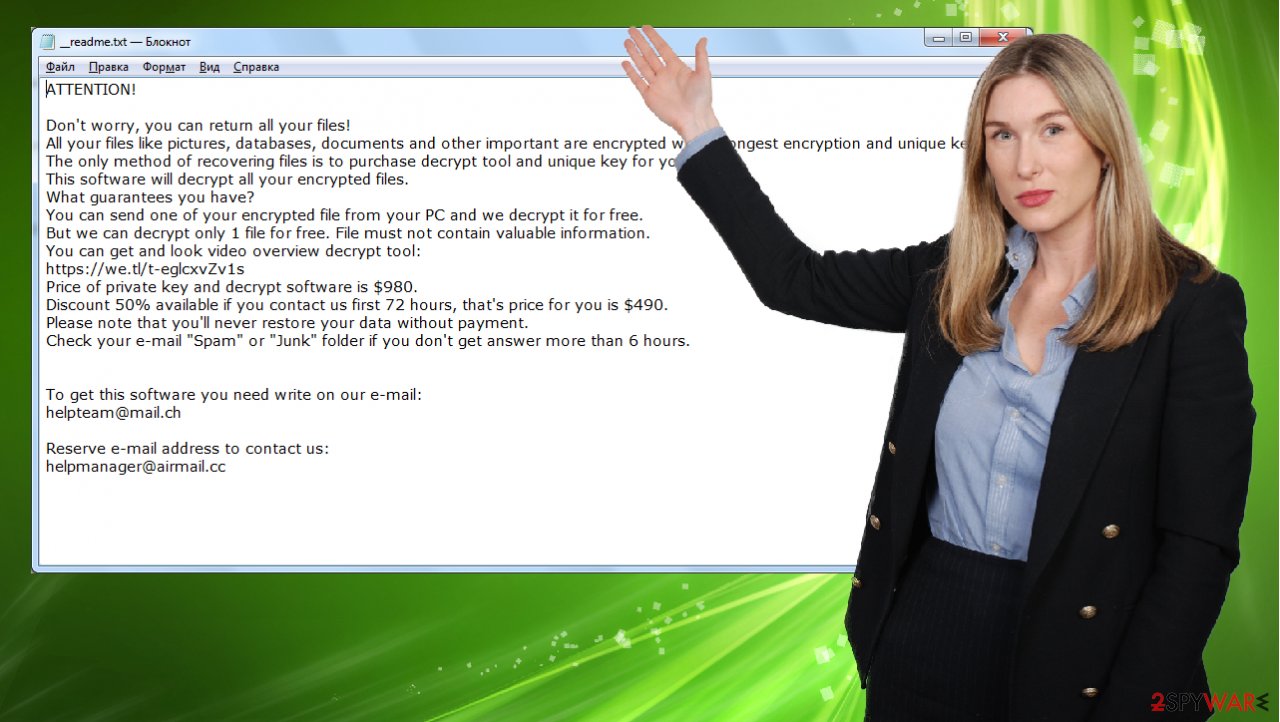
The _readme.txt file that gets placed in different places where encoded files get stored reads:
ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-tkon5qUcfl
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
manager@mailtemp.chReserve e-mail address to contact us:
helpmanager@airmail.ccYour personal ID:
One of the features of this kind of malware is that if you reboot your machine after encryption, even in Safe Mode with Networking or any other mode with networking background enabled – but no network connection – it continues to run its functions and processes.
The newest variants of the Djvu file virus are designed to be impossible for victims' files to ever be recovered. This is because they were created using not offline but online keys, which will only work on one specific version of a given strain. The most recent variant has an upgraded code that prevents any decryption from occurring whatsoever! It doesn't matter if you have access to your PC's hard drive or not; this new encryption technique cannot be broken. At least for now.
| Name | Ufwj ransomware |
|---|---|
| Type | File-locking virus, crypto-malware |
| Family | Djvu/STOP ransomware |
| Appendix | .ufwj gets added at the end of the original filename and file type indicator after the encoding |
| Ransom note | _readme.txt |
| Contact information | manager@mailtemp.ch, helpmanager@airmail.cc |
| Distribution | Files that spread malware payload can be added to malicious emails as attachments and come via pirating of software, game cracking |
| Removal | You need to eliminate the threat as soon as it is possible, and anti-malware tools can work for that the best |
| Recovery | You can restore some of the files with the media file tool, but decryption is impossible for this version. Alternate methods include previously known decryptors, data recovery software. Malware damage and virus leftovers can be restored with FortectIntego |
There are a few rare occasions when the encryption happens with the help of offline IDs, so users get their files back and help others with the provided decryption key. However, there are few options for advanced ransomware victims. You can try the existing decryption tool and check if your files can possibly be restored.
Ufwj file virus is a new version in this long-running family. Therefore, it is vital that you follow an effective data recovery guide at all times and back up your files correctly to avoid the risk of losing them accidentally. Data backups can be useful in such cases and in other incidents when files get affected unexpectedly.
Possible .ufwj file recovery option
Even if you don't know if the Ufwj file virus is using online or offline keys, you should try using Emsisoft decryptor for Djvu/STOP versions. It is important to mention that this tool will not work for everyone – it only works if data was locked with an offline ID due to malware failing to communicate with its remote servers.
Even if your case meets this condition, somebody from the victims has to pay criminals, retrieve an offline key, and then share it with security researchers at Emsisoft. As a result, you might not be able to restore the encrypted files immediately. Thus, if the decryptor says your data was locked with an offline ID but cannot be recovered currently, you should try later. You also need to upload a set of files – one encrypted and a healthy one to the company's servers before you proceed.
- Download the app from the official Emsisoft website.
- After pressing Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe should show up – click it.
- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.

- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although you can also do it by pressing Add folder at the bottom.

- Press Decrypt.

From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID, decryption is impossible” – you are unable to decrypt files with this tool.
Encryption is not the only thing that ransomware does when the machine gets infected
Besides inflicting large amounts of potential harm onto your computer, there are also certain signs that appear within your infected system, which help you find out if it has already been affected by the Ufwj file virus. After studying its activities closely, there is a chance for corruption of some personal information and system data on your hard drive.
Threat directly encodes photos, videos, documents, but system data gets affected too. Altered system files, corrupted registry entries, or DLLs can cause major damage to essential system functions. Experts[1] always note that cryptovirus is one of the most damaging. Here are some ways you can use proper tools to get rid of this damage.
We highly recommend using a one-of-a-kind, patented technology of FortectIntego repair. The application can also fix various Windows-related issues that are not caused by malware infections, such as Blue Screen errors, freezes, registry errors, damaged DLLs, etc.
- Download the program.
- Click on the ReimageRepair.exe
- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process

- The analysis of your machine will begin immediately
- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you automatically purchase the license and fix the.

Removing the virus takes time but cannot be skipped
After reading all of the above, you may conclude that recovering your files is a long shot. If so, we hope that you do have an offline backup handy – because the rest of this article describes how to use it in order to get data back. BUT. The most important step is to remove the infection fully from your device.
Ufwj virus not only encodes those common files but also disables functions, damages programs to keep you from removing the threat easily. If you want to remove the threat from your computer for good, make sure it's gone with a trustworthy anti-virus program first like SpyHunter 5Combo Cleaner. Once that pesky cryptovirus is eliminated without any issues, go ahead and undertake recovery options; just be careful since leftover malware can cause problems even after this step!
Once the machine is clean from all threats or infections, you may go through any recovery options. Double-checking is strongly advised. The ransomware virus is spreading across the world, and it's not just encrypting data found on a system but also can lead to total file and money loss. Paying criminals is also very risky, as they might not fulfill the promises and never send back the required decryption tool.[2]
While this might sound terrible, not all is lost – data recovery software might be able to help you in some situations (it highly depends on the encryption algorithm used, whether ransomware managed to complete the programmed tasks, etc.). Since there are thousands of different ransomware strains, it is immediately impossible to tell whether third-party software will work for you.
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.
- Follow on-screen instructions to install the software.

- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered.
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.

Sometimes malware ensures that users can't access any environment that allows network connections. An infected host file might have blocked the function on your computer – this is what's keeping you from visiting security-related sites or downloading trustworthy anti-malware software.
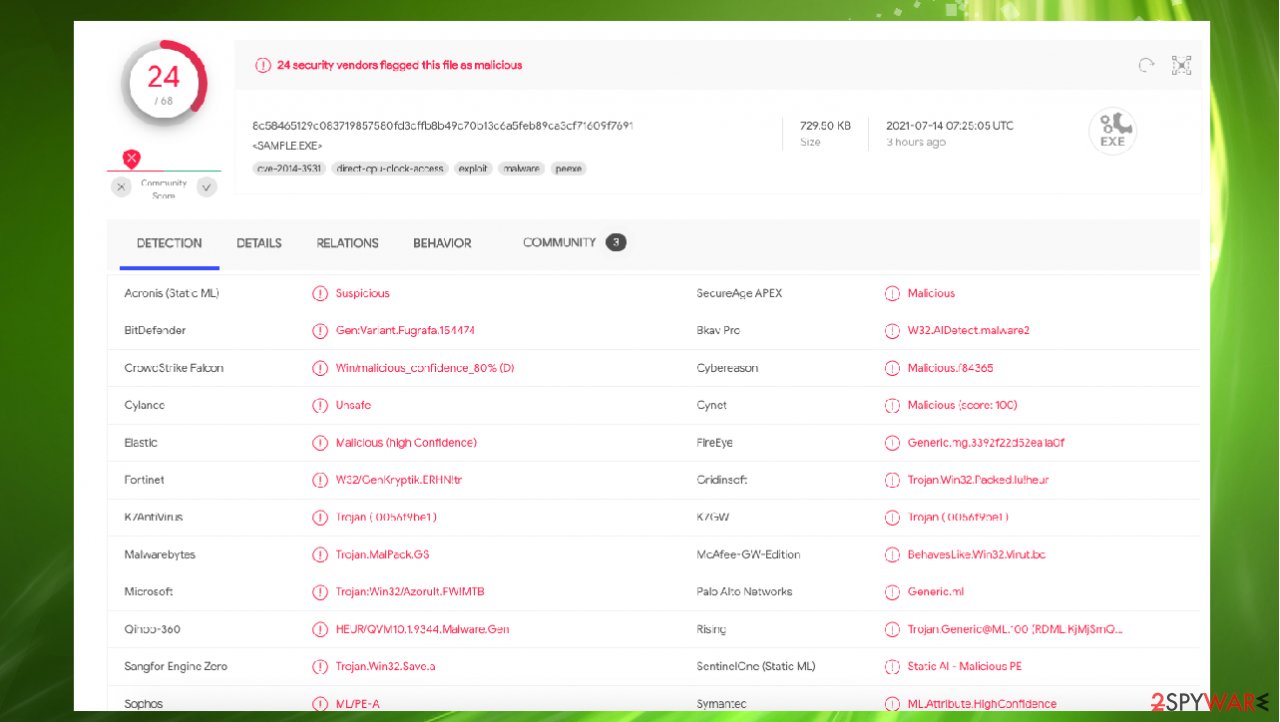
Ufwj makes many changes on the machine and can damage the computer significantly, so we always note that elimination is the most important step here, before any data recovery options. Threats can be eliminated based on detection[3] rate and using proper anti-malware tools like SpyHunter 5Combo Cleaner or Malwarebytes, so all threats get located. Do not go straight to file restoring, and remember to backup files more frequently.
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Zondervirus. ZOndervirus. Spyware related news.
- ^ Bryce Bearchell. Ransomware: the anatomy of paying a ransom to decrypt hostage files. Coalfire. Cybersecurity solutions.
- ^ Virus detection. VirusTotal. Online malware scanner.
