Un1que ransomware (Virus Removal Instructions) - Bonus: Decryption Steps
Un1que virus Removal Guide
What is Un1que ransomware?
Un1que ransomware is the file-locking virus that derives from another famous malware family – IEncrypt ransomware
Nevertheless, the Un1que ransomware virus damages such files with additional processes that get to be launched in the background. It manages to affect particular security functions, features that could be helpful for data recovery or virus removal. This threat can install programs, disable the ones that already run on the machine, or install secondary malware payload on the already infected system, so it damages even more than the encryption does.
| Name | Un1que ransomware |
|---|---|
| Family | IEncrypt ransomware |
| main target | Large businesses and companies |
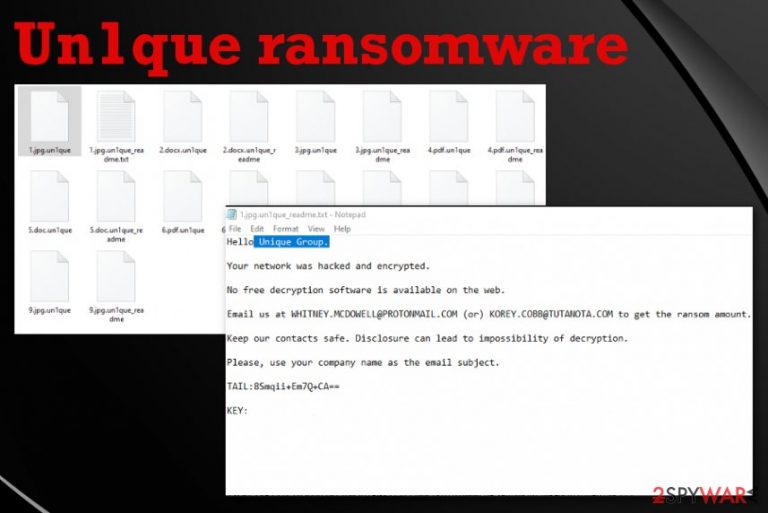
| File marker | .un1que is the extension that appears on every encrypted file after the encoding process, so all affected files have distinct appendix coming after the original name and the file-type extension. These files become unopenable when the virus changes the original code of data |
| Ransom note |
un1que_readme.txt is the file that contains a ransom message from virus developers. Typically it includes the particular ransom demand or contact information, further instructions for payments, and ways to get cryptocurrency. In this case, the note is brief and only ensures people that there is no other way to get their files back but to pay for the alleged decryption tool. Additionally, some of the encrypted files can get a particular ransom note files titled like the original data (1.jpg.un1que_readme) |
| Contact emails | WHITNEY.MCDOWELL@PROTONMAIL.COM and KOREY.COBB@TUTANOTA.COM |
| Distribution | Ransomware payload file gets added as the file attachment on legitimate-looking emails posing as notifications from companies or services. Malicious macros[1] get enabled by opening the file and allowing additional content, so cryptovirus is launched directly after the email is opened |
| Elimination | You need to employ anti-malware tool to remove Un1que ransomware from your machine fully, so all the traces of this virus or any additional threats get deleted |
| Repair | Threats that can access the system folders and settings manage to alter those parts of the machine and damage the device, sometimes even permanently. You should get a system program like FortectIntego and run the tool to find and possibly fix virus damage without causing additional issues |
Even though previous versions of the same family only targeted companies and businesses, Un1que ransomware appears to also spread on the systems of simple users. The main target still remains companies al over the globe. Once it gets on the system and those photos, documents, videos, databases, and other files get encrypted, the ransom message file appears on the desktop and in some of the folders with encoded data.
Un1que ransomware virus developers write their message in un1que_readme.txt file that contains particular contact emails and claims that there are no other options besides paying for the alleged decryption tool. To determine the particular ransom amount and receive further instructions, people need to contact those criminals as soon as possible until those files haven't gotten permanently damaged.
Typical Un1que ransom note:
Hello Unique Group.
Your network was hacked and encrypted.
No free decryption software is available on the web.
Email us at WHITNEY.MCDOWELL@PROTONMAIL.COM (or) KOREY.COBB@TUTANOTA.COM to get the ransom amount.
Keep our contacts safe. Disclosure can lead to impossibility of decryption.
Please, use your company name as the email subject.
TAIL: –
KEY: –
When people contact Un1que ransomware developers they need to indicate the name of their company and the particular key included in the ransom note. This ID is unique per each target and determines the victim for developers. This unique victims' key is needed for the decryption too when researchers develop such tools or when the ransom gets paid, and the victim receives a tool capable of recovering those files.
However, no one that knows about cryptocurrency extortion-based viruses can offer to pay for these criminals behind the dangerous Un1que ransomware virus. Experts[2] in various countries claim that there is no reason to pay the demand because criminals cannot guarantee that the decryption tool is going to reach you after that. In most cases, even large governments and companies stay away from such options.[3] 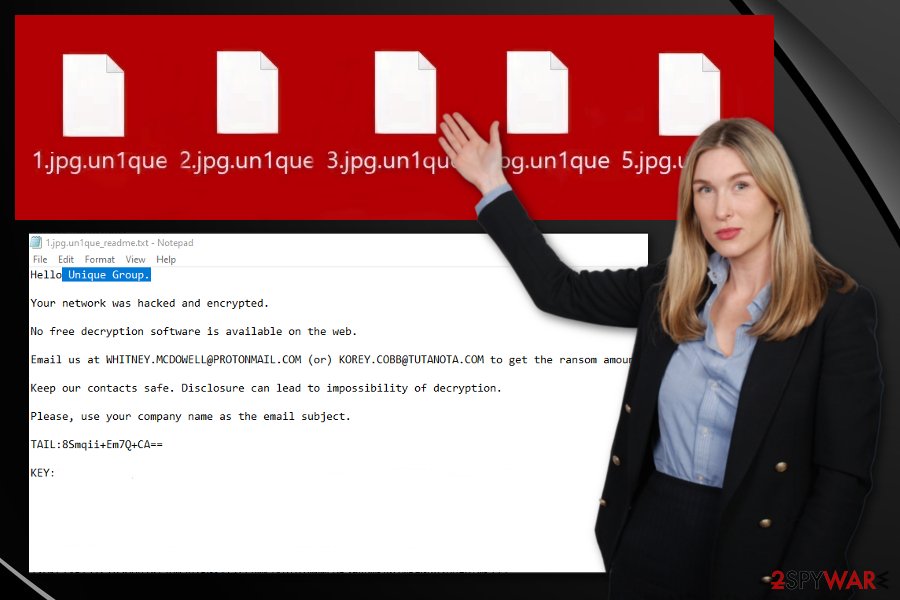
- Trojan.Generic.D1F79138;
- Win32.Trojan.Delshad.Dwiw;
- W32.Ransom.Bitpaymer;
- Trojan.Encoder.28586;
- etc.
You need to remove Un1que ransomware regardless of the particular name. The best way to remove the threat like this is to get a professional anti-malware program. This is a powerful malware that targets large networks of businesses, so it can be persistent enough to avoid detection and security tools. Make sure to choose an official source for the tool if you decide to get a new program.
You should reboot the machine in a Safe Mode before you run the anti-malware tool on the machine to eliminate Un1que ransomware. This way, malware can be found easier and deleted from the computer fully. Also, remember about all the changes threat makes on the system and get proper repair tools like FortectIntego that could find and fix affected files and repair things like registry entries.
Since Un1que ransomware interacts with the system and damages such functions like file or system recovery or startup, you need to take the settings back to normal, so the virus is no longer accessing removable storage devices or network shares and cannot create additional processes or install programs. As for file recovery, the best option is to get files from backups on external devices or cloud services. This is how you can replace encoded files with safe ones without causing additional damage. If you don't have that option – read below the article. 
Social engineering strategies included in ransomware spreading campaigns
Email messages and hacker-controlled sites get employed for spreading the payload of cryptovirus globally. This is how threat actors can target companies and businesses at the same time as everyday users – everyone receives emails. Visitors get confused into thinking that the message is legitimate and sent from an institution or company.
Emails include either link to a malicious website where the payload is triggered and dropped after interaction with the content or the file directly attached to the email itself, so the person needs to download the document and open it on the machine. Then additional pop-up encourages the victim to enable malicious macros or different payload dropper.
Infected files with ransomware payload also get uploaded in packages with pirated software on torrent sites and file-sharing services. You cannot notice the infection this way, especially when you choose wrong installation methods that allow every application or file included to get loaded on the system.
Pay attention to emails you receive, look for red flags, do not trust ransom senders. Also, rely on proper software providers, do not pirate or download cheats, cracks of games or software. This is the only way to avoid malware. As for companies and businesses – data backups and secure networks should be a priority.
Terminate the Un1que cryptovirus and repair the damage
Un1que ransomware removal is not the process that could be achieved manually and quickly. Remember that this malware includes modules that allow the virus to keep persistent on the infected machine and avoid detections bu injecting existing processes with malicious codes and creating additional entries in registry or memory.
There are a few additional things about Un1que ransomware virus that should be indicated: malware can load data-stealers on the system, and obtain information about the device, steal other files with personal and useful information. Since this threat can get on the network of a company, such devices may store crucial information.
Make sure to remove Un1que ransomware before it is too late, and the threat hasn't loaded secondary payloads or malware on the machine. This is how you avoid permanent damage. Rely on security and system tools like FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes and clean the machine fully before recovering data.
Getting rid of Un1que virus. Follow these steps
Manual removal using Safe Mode
Reboot the machine in Safe Mode with Networking and then run the AV tool to delete Un1que ransomware from the system
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Un1que using System Restore
System Restore feature is helpful for Un1que ransomware removal because it can restore the machine in a previous state when the virus was not active yet
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Un1que. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Un1que from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Un1que, you can use several methods to restore them:
Data Recovery Pro is the option for people who don't have particular file backups
Try Data Recovery Pro for your files encrypted by Un1que ransomware or accidentally erased data
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Un1que ransomware;
- Restore them.
Windows Previous Versions is the method allowing the file recovery after Un1que ransomware virus attack
When you enable System Restore, you can choose Windows Previous Versions as a method for file restoring
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer is the feature of an operating system that allows users to restore encoded files
This is the alternate file restoring method that can work for encoded data when Un1que ransomware is not affecting Shadow Volume Copies
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Decryption is not possible yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Un1que and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Macro virus. Wikipedia. The free encyclopedia.
- ^ Lesvirus. Lesvirus. Spyware related news.
- ^ Scott Ferguson. Ransomware Increasingly Hits State and Local Governments. Bankinfosecurity. News and resources.
- ^ Ransomware detection rate. VirusTotal. Online malware scanner.







