Virtumonde (Virus Removal Guide) - Free Instructions
Virtumonde Removal Guide
What is Virtumonde?
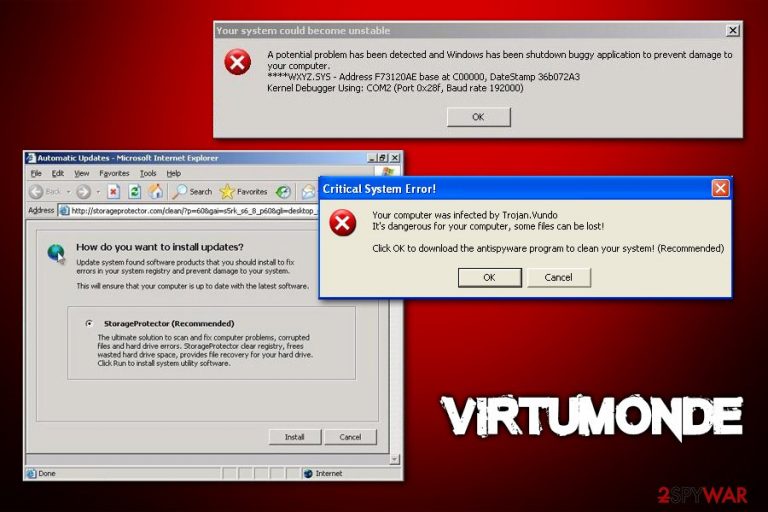
Virtumonde is a Trojan that is designed to make users install rogue anti-spyware programs by showing fake alerts
Virtumonde, otherwise known as Trojan Vundo, is a multi-functional Trojan virus with worm-like features that was developed in the late 2000s. The malware mainly spreads via contaminated spam email attachments or through a web browser or plugin, such as Java, exploits – these techniques ensured the large size of infections across the globe. Once inside the system, malware changes several Windows functions to be able to operate as intended, and users begin to experience virus infection symptoms immediately.
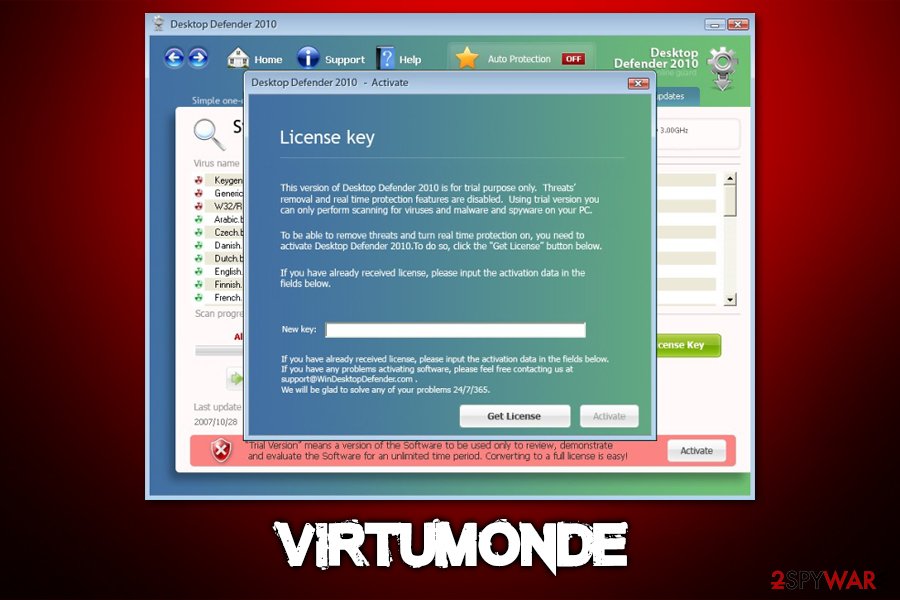
Over the years, Trojan was tweaked and improved, although its primary function was to show users malicious and fake pop-ups that advertised rogue anti-malware programs such as WinFixer, AntiSpywareMaster, SysProtect, and many others. Once installed, these malware apps would cause an array of additional problems to victims, deteriorating the user experience and system functions even further. Later, Trojan.vundo was also used to perform DDoS (Distributed Denial-of-Service)[1] attacks and proliferate other malware such as rootkits and ransomware.
| Name | Virtumonde / Vundo |
| Aliases | Vundo, Virtumondo, Trojan.vundo, Troj.vundo, Trojan:Win32/Vundo |
| Type | Trojan with worm-like capabilities |
| Functions | The malware can be employed to perform a variety of functions on the host machine, including other malware proliferation, fake alert display that promotes malicious software, DDoS functionality, etc. |
| Promoted rogue software | WinFixer, AntiSpywareMaster, SysProtect, WinAntiSpyware, AntiSpywareExpert, Desktop Defender 2010, XPAntiVirus, and many others |
| Symptoms | Intrusive pop-up alerts about allegedly infected/damaged system, inability to update Windows, inaccessible websites, system freezes/crashes, disabled anti-virus software, fake blue screen of death warnings, etc. |
| Risks | Vundo can render the system vulnerable to malware, so users might be infected with other infections over time. Consequently, users might have their financial or other sensitive information stolen. Also, due to a variety of processes that the malware initiates, users might not be able to use their computers normally, constantly experiencing system crashes and lags |
| Related | Virtumonde.dll, slmnvnk.dll, |
| Removal | Perform a full system scan with the help of reputable anti-malware software, such as SpyHunter 5Combo Cleaner or Malwarebytes |
| System fix | The infection might completely destroy some Windows system files. In order to avoid OS reinstallation process, we suggest using FortectIntego to fix virus damage and remediate the computer, bringing it back to a pre-infection state |
Rogue anti-spyware tools were extremely widespread during the 2000s, mainly because of a lack of regulations related to internet and application safety. As a result, thousands of malicious apps that were presented as legitimate security tools were developed and distributed in various deceptive ways, including the Vundo Trojan.
Users infected with trojan would see pop-ups, alerts, and other misleading notifications about their allegedly infected/damaged computers every time they open the web browser, no matter if it is Internet Explorer, Google Chrome, or Mozilla Firefox. The notifications often claim that malware Win32/Virtumonde was found on their computers and that they need to download the recommended tool for its termination.
While the messages claiming that the computer is infected with malware, the reason for these to appear is the infection. The virus may use several different malware names (fake or real) in order to make users believe that they need to download advertised software. In installed, these rogue tools will compromise the PC further, which might complicate the trojan removal even further.
Another danger of trojan promoted programs (besides being non-functional and harmful) is that users will be constantly asked to purchase a “full” version to delete malware on the system. Those who agree to proceed with the payment might be handing their credit card information directly to cybercriminals, which might result in financial losses and even identity fraud/theft. Thus, if you have been seeing these misleading Trojan.Vundo alerts, do not download, install, or pay for anything.

Besides showing users false-positives and other malicious messages, Virtumonde virus might also display the following (visible) symptoms:
- Changed desktop wallpaper and screensaver – fake errors and BSODs shown instead;
- Websites fail to load or do that very slowly;
- Some Windows functions disabled, such as the Task Manager, Registry Editor, etc.;
- Explorer.exe crashes;
- Deleted network connections;
- Blue screen of Death (BSOD)[2] errors and system shutdowns, etc.
Trojan also possesses several persistence functions as well. In order to prevent users from detecting and eliminating the malware easily, it greatly weakens and disables certain built-in Windows defenses. For example, it prevents users from downloading the latest security updates, and might sometimes disable legitimate anti-malware software altogether. Also, some versions prevent users from visiting security-related websites (this is typically achieved by modifying Windows “hosts” file).
The newest versions of malware also incorporate rootkit[3] functionality, which makes it very difficult to remove malware from the infected computers. Essentially, this feature allows threat actors to execute commands remotely, download malware updates, and change system configuration files with admin-level privileges. Generally, detecting and removing rootkits is very difficult, hence not all security software can accomplish that.
For this reason, a specific rootkit removal software might be required to eliminate this version of Vundo malware. There are plenty of tools available for this particular function – they use behavior-based and memory dump analysis techniques, as well as signature scanning.
Nevertheless, versions of this trojan without rootkit functionality can be eliminated relatively easily with the most up-to-date, modern security software. We recommend using tools like SpyHunter 5Combo Cleaner or Malwarebytes, although there are plenty of others you could choose from based on your personal preferences.
In many cases, users infected with Vundo virus are forced to reinstall Windows, as, even after malware removal, they still experience system crashes, lags, BSODs, and similar. This is because anti-malware software is not capable of fixing some damaged system files. For that purpose, we recommend using FortectIntego – it can replace malware-affected system components with working Windows files.
Update your software on time and watch out for suspicious emails with attachments
While Troj.vundo is an old malware, it does not mean that it is not present in cyberspace. Despite the overall awareness and security is increasing among computer users, there are millions of vulnerable devices that are not protected by anti-malware software or/and are running unsupported Windows versions. These machines are perfect targets for old malware, so it is important to take precautionary measures in order to avoid it.
The first step into a secure computer is ensuring that it is running a supported operating system (i.e., Windows 10, Windows 8, or Windows 8.1), which is constantly being patched with the latest security updates. Additionally, all the installed applications, browsers, and plugins (especially Java and Flash, as these often suffer from vulnerabilities and are abused by hackers) should be set to an automatic update function. The operating system should also be protected by a high-end anti-malware software that is capable of stopping old and new threats at all times.
Another very important security measure is avoiding spam emails that carry macro-embedded attachments. While previously, users were simply sent executable files that would install malware directly, nowadays, more advanced methods are used, and the infection can be triggered by PDF, .doc, and similar files. In most cases, body text claims that there is an urgency to open the attachment (it can be presented as a bill, tax refund form, application, etc.); the attackers also often use well-known company names, such as Amazon, UPS, JPMorgan Chase, and similar.
Remove Trojan from your machine and fix Windows system files
Since the virus is a multi-functional and can heavily modify Windows system configuration settings and files, Virtumonde removal can be a very difficult task. Nonetheless, there are several different versions of the malware – older variants are likely to lack the advanced functionality, such as rootkit capabilities. Besides, anti-malware makers are now employing advanced techniques for malware detection and termination, so it is highly likely that you would be able to remove Vundo by performing a full system scan with security software.
If you encounter difficulties with virus termination, you should access Safe Mode with Networking, as explained below, and perform a full system scan. Also, you could try System Restore if the malware did not disable it during the infection process. As previously mentioned, you might have to use an anti-rootkit application that is specifically developed to find malware.
Getting rid of Virtumonde. Follow these steps
Manual removal using Safe Mode
To access Safe Mode with networking, follow these steps:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Virtumonde using System Restore
If System Restore was not disabled by Vundo Trojan, you could use it to eliminate the infection:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Virtumonde. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Virtumonde and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ What is a DDoS Attack?. Cloudflare. The Web Performance & Security Company.
- ^ Blue screen of death. Wikipedia. The free encyclopedia.
- ^ What is a Rootkit? How Can You Detect it?. Varonis. Security blog.







