Webhostoid.com virus (Removal Guide) - Jul 2018 update
Webhostoid.com virus Removal Guide
What is Webhostoid.com virus?
Webhostoid is a browser hijacker that redirect users to sponsored sites
Webhostoid is a redirect virus that usually gets installed as a browser plugin or extension on Google Chrome, Mozilla Firefox or Safari browsers. These unwanted applications usually get into the machine via software bundling – the most prominent PUP distribution method. As soon as Webhostoid virus is installed, it starts its activity by redirecting users to sponsored sites, displaying pop-ups, deals, offers, banners, and considerably slowing down the computer.
| Summary | |
| Name | Webhostoid.com |
| Type | Adware |
| Distribution | Software bundling |
| Spreads as | Browser extension or plugin |
| Symptoms | Pop-up ads and redirects to questionable sites |
| Main dangers | Malware infection, personal data leakage |
| Elimination | User FortectIntego or our manual guide below |
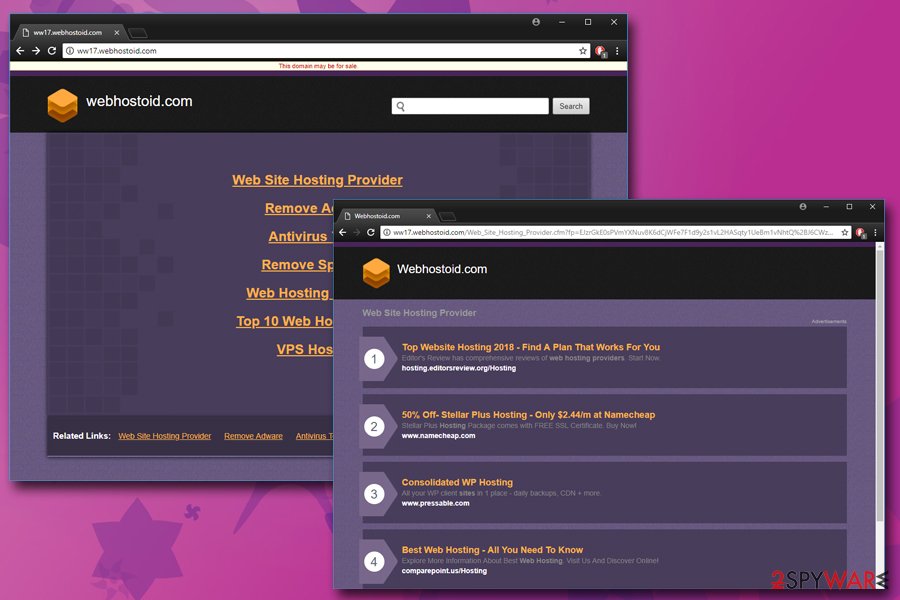
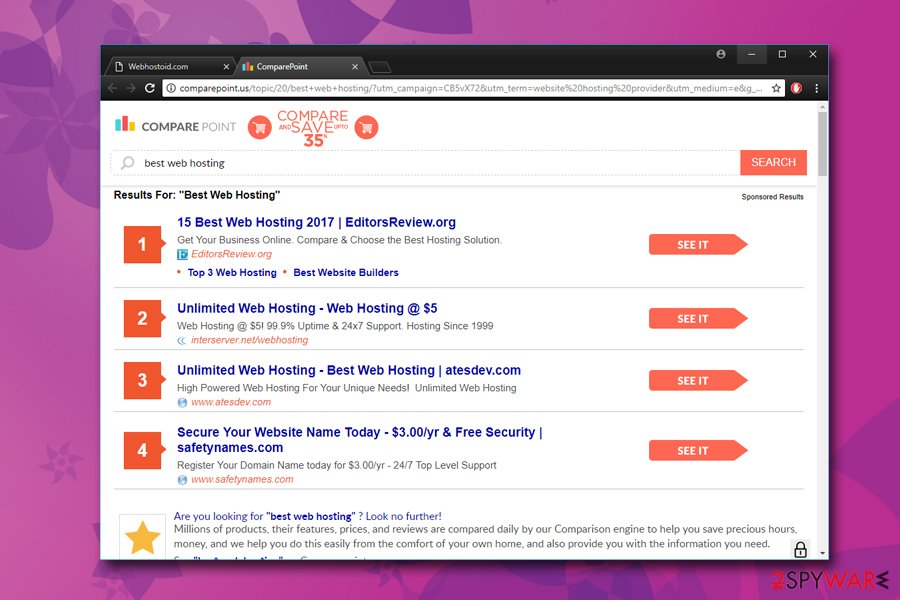
Since Webhostoid is a redirect virus, it connects to multiple different domains, including d2e24t2jgcnor2.webhostoid.com, ww17.webhostoid.com and similar. This type of rerouting increases traffic to questionable sites and boosts their rankings. Therefore, users never gain any benefit from having Webhostoid virus installed on their computers.
It is important to know that it is hazardous to use this website, which seeks to gain revenue from its sponsors from redirecting users to untrustworthy sites. Usually, victims whose computers were infected with this potentially unwanted program complain about frequent and unexpected URL redirects to various suspicious-looking third-party pages.
Bear in mind that this application can lead you to infectious websites, so you should definitely avoid clicking on ads it loads to you and start looking for Webhostoid.com removal methods.
Webhostoid.com is an adware program, which is considered to be a potentially unwanted program (PUP). All adware programs seeks financial benefit and brings no actual use for the end user, making the dubious app completely useless.
Once Webhostoid slithers into the computer of a victim, it sneaks into your computer registry and alter proxy settings[1] to cause repetitive redirects to webhostoid domain. It might also install plug-ins to all your web browsers, and these might replace your current homepage with a suspicious search site.
The search engine provided by Webhostoid.com redirect virus can display search results that may also contain hazardous hyperlinks. As you can see, this PUP seeks to redirect you to particular websites; and these websites belong to questionable third-party companies.
Besides, Webhostoid.com might start to track your activity while you browse the Internet. The recorded data typically includes:
- Technical information
- Installed programs
- IP address
- Search queries
- Links clicked
- Bookmarks, etc.
Finally, we must warn you to be careful after noticing the described URL appearing in your browser. Websites you might access through it are definitely not trustworthy and in the worst case you can be tricked into installing dangerous software that can work as a keylogger[2] and track your keystrokes and steal your personal and sensitive information. For example, your credit card details, passwords, logins, and similar information that can be stolen and lead to financial loss. Do not risk losing such information and take care of your security and privacy as soon as possible.
Some computer security experts claim that Webhostoid virus is closely related to the Genius Box adware, RocketTab hijacker, and BrowserSafeguard. Researchers from Zondervirus.nl[3] say that it can install proxy servers on the victim’s computer. Such activity of Webhostoid should not be tolerated.
If you do not want to experience data leakage, financial tear-off or similar dangers, you should remove Webhostoid.com ASAP. The best solution is to install a professional anti-malware program; and for that, we strongly recommend FortectIntego.
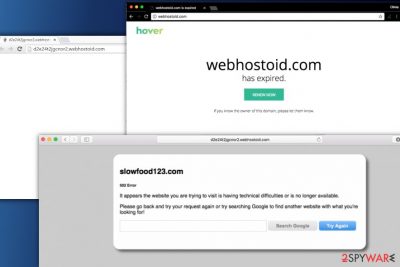
Update September 2017. It seems that Webhostoid.com is no longer used for serving myriads of annoying ads. Instead, the victims might run into “Webhostoid.com has expired” page. That is a sign that your computer is still infected with a redirect virus, so we strongly recommend you to follow the provided directions and erase the cyber parasite causing these redirects immediately.
Protect your computer from PUP threats
You should know that you have to think about your safety and be aware all the time when you use your computer and browse the web. Remember that there are thousands of hackers on the cyber-network that seek to catch naive and inexperienced computer users and gain income from them.
We want to provide you a list of important things you should remember while browsing online that can help to prevent silent installation of critical programs or viruses on your computer:
- Research. Before installing any program to your computer, try to find as much information about the program and also investigate the website that provides the download link. Read user comments and reviews on various forums – it can also help you to understand if the program you are about to install is reliable.
- Stay attentive. You should always be cautious and suspicious of e-mails from unknown senders; you should immediately delete e-mails from unknown companies. Most important thing is to NEVER open the attachments from letters that fall into Junk or Spam mail categories. Take note that cyber-criminals try to conceal themselves by using e-mail addresses that look like they belong to reliable companies. For example, Name@hm.bing.com does not mean that the sender works for Bing.
- Install carefully. You should always install new programs using Advanced or Custom installation settings because only these options let the user review and opt out unwanted software components.
- Safety first. Do not surf through unreliable websites that contain suspicious offers. Do not let your curiosity make you experience severe consequences later. Such sites sometimes can place hidden hyperlinks that require only one click to launch an infected program on your computer.
Remove Webhostoid.com redirect virus for good
If you have been experiencing redirects through the described domain, now it is time to think about Webhostoid removal options. There are two options you can choose from. You can either remove Webhostoid.com virus using the anti-malware program that we have mentioned before or use manual elimination steps.
Manual elimination is considered to be an alternative removal method which does not require installing additional software on the system. The steps provided below the article explain how to get rid of Webhostoid redirect problem completely.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Webhostoid.com virus. Follow these steps
Uninstall from Windows
First of all, uninstall suspicious software that was recently added to your computer system without your knowledge. We strongly suggest deleting RocketTab, GeniusBox, BrowserSafeGuard and other questionable programs.
First of all, you should reboot your computer in Safe mode. To start your computer in this mode, simply restart your computer and while its loading, repeatedly tap on F8 button on your keyboard. If asked to select a preferred mode, choose Safe Mode from the menu that appears on your screen.
- Now, click on Start menu and use Windows search to find regedit (Registry Editor). Open it and then navigate to HKEY_CURRENT_USER > Software > Microsoft > Windows > Current Version > Internet Settings.
- Now, look on your right and find ProxyEnable and ProxyServer keys. Click twice on ProxyEnable key and set Value data to 0. Click OK.
- Then right-click on ProxyServer key and choose Delete option.
- Open Start menu again and search for msconfig. Open it and select Normal startup in the General tab. Then go to Startup panel and deselect suspicious startup services and click OK.
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Delete unwanted extensions using the provided guide.
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Webhostoid.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ How to configure client proxy server settings by using a registry file. Microsoft. Microsoft Support Pages.
- ^ Keystroke logging. Wikipedia. The Free Encyclopedia.
- ^ Zondervirus. Zondervirus. Malware and Spyware News.























