Weknow.ac. 7 steps removal guide provided. 2021 update
weknow.ac Removal Guide
What is weknow.ac?
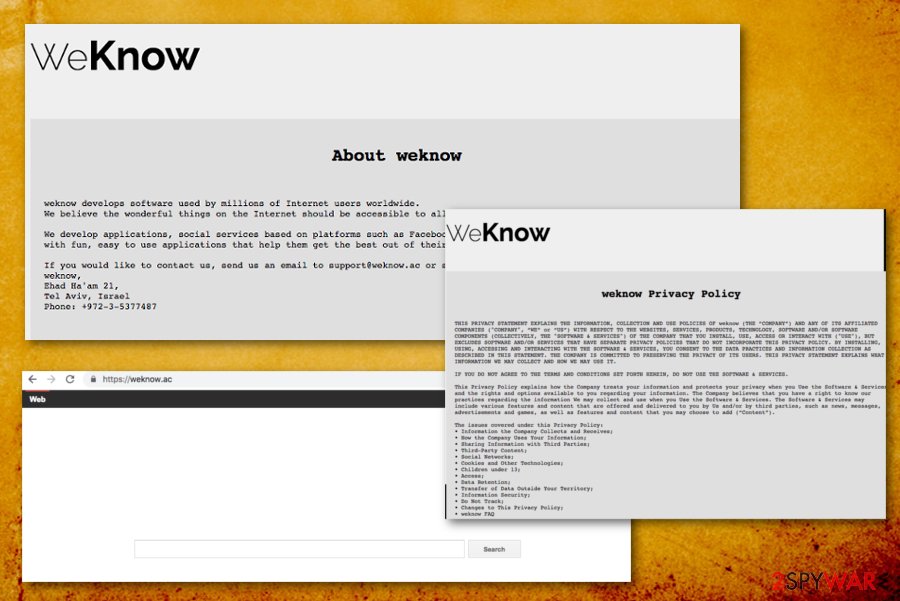
Weknow.ac is the browser hijacker that aims to spread around and promote other PUPs on macOS devices

Weknow.ac is a potentially unwanted program that falls into a browser hijacker[1] category and affects numerous browsers, such as Google Chrome, Safari, and Mozilla Firefox. Initially, PUPs are not considered to be a serious computer threat, but this case is a little different, as the app is known to be distributed via the fake Flash Player installers – a feature that is prevalent in malware.
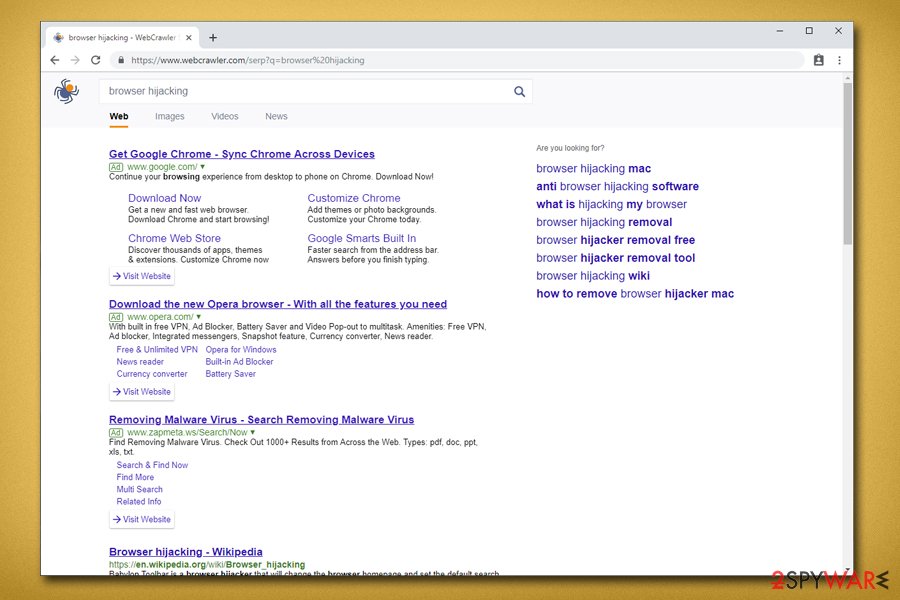
As soon as the PUP is installed, it changes the search engine to Smart Search which redirects to WebCrawler – it brings up search results that are not genuine and littered with sponsored links and ads. For that reason, users often end up on sites that are affiliated with Weknow.ac, bringing the Israeli-based developer profits for each made click.
By spreading the browser hijacker to hundreds of users, its developers ensure a stable income. Therefore, this intruder retains persistence when users are trying to get rid of it, and the hijacker is using many tricks to prevent its removal, for example, it changes Chrome's group policies. Some advanced methods need to be used to eliminate the hijack – we provide more details below.
| Name | weknow.ac |
|---|---|
| Type | Browser hijacker |
| Danger level | High. Actively affects computer systems |
| OS affected | Mac OS X, macOS |
| Affiliates | WebCrawler, Smart Search, MacKeeper, etc. |
| Browsers affected | Chrome, Firefox, Safari |
| Details gathered |
|
| To avoid | Stay away from dubious sites, do not use secondary installers, download and install an antivirus. |
| Spreads by | Software bundles, malicious ads promoting fake Adobe Flash player, etc. |
| Deletion process | Use anti-malware tools to get rid of the PUP completely |
| Repair | The system can run smoothly when files affected by the virus can be restored using FortectIntego |
As soon as Weknow.ac malware establishes itself, it will engage in promotional campaigns that push unsafe tools for Macs, such as the notorious MacKeeper. You should never download and install the fake system optimizers, as they can bring more trouble to your device and will only result in the waste of money.
Unlike most other browser hijackers, this one only affects macOS users, although it does not mean that developers will not create a version compatible with Windows-based systems. Browser-hijacking applications such as weknow.ac come with fake ads or bundled software. Here is one of the examples[2]:
While browsing with Chrome two days ago, I made the idiotic mistake of clicking on a Flash download popup and immediately noticed signs of infection by this malware.
However, software bundling is the most prominent PUP[3] distribution method. To create revenue, developers of Weknow.ac virus employ various tracking technologies, such as beacons, tracking cookies, JavaScript, and similar. With the help of these tools, various non-personal details are transferred to the app's authors. The information contains:
- Information regarding the victim's device;
- Apps used;
- Bookmarks;
- Search queries;
- Websites viewed and the length of the visit;
- User's interaction on social networks;
- Links clicked;
- IP address;
- Internet service provider (ISP), etc.
While most of such data is personally non-identifiable, personal information is also collected:
While it is not our intention to collect any personally identifiable information (“PII”) (except for registration and user support purposes as set forth in this Privacy Policy), the data collected may include PII.
This data includes email address, Social Security Numbers, Credit Card numbers, Login information, and other data. Such information is sensitive and should not be retained by unknown third-parties, as it can result in its leak – cybercriminals might use it for malicious purposes, such as identity fraud.[4] Therefore, it is essential to keep your personal information safe and not to disclose it inside third-party websites like this could redirect you to shady services from questionable websites.
To avoid such data leakage, perform Weknow.ac removal by manually eliminating the threat or using professional security software. We suggest using SpyHunter 5Combo Cleaner, Malwarebytes, although you can use any other anti-malware software of your liking.
Additionally, the hijack can result in numerous redirects to suspicious websites. This kind of pages may even contain harmful components (such as keyloggers, ransomware, crypto-miner or trojan horses). In some cases, you might end up infecting your machine with these malicious programs and harming system files, which can result in personal data loss.

All in all, we recommend you remove Weknow.ac fromm your computer as soon as possible. The annoying ads, system slowdowns, and even potential information leakage is something you could experience on a daily basis. Thus, you are better off without the unwanted application on your PC.
However, in some situations, you might face issues related to fixing your system as We Know malware tends to modify Chrome policies or Safari bookmarks to make them launched once the browser is started. In this case, reinstalling the web browser works the best.
Relations are found between weknow.ac and other browser hijackers
The app appears to be not the only one of its kind. Other similar versions which share an identical search engine have been discovered. The operating principle of these threats is always the same – to approach web browsers secretly and modify their settings for bogus activity promotion. Read all about the PUPs down below.
Searcreetch
Searcreetch.com is a browser-hijacking application that appears on a particular web browser, e.g. Chrome, Firefox, Explorer, Safari, Edge after the SearCreetch extension is installed. Furthermore, unwanted changes begin and you will find your search engine changes to http://searcreetch.com/.
What is the worst part of Searcreetch.com browser hijacker is that you are forced to use the modified web browser engine, homepage, and new tab zone unless you remove the virus from your system and browsers entirely. In addition, you will supposedly be bombarded with loads of annoying advertisements and experience intrusive redirects during browsing tasks.
Searchmine
Searchmine.net is another browser hijacker that relates to weknow.ac regarding the same engine shared. Most often, this potentially unwanted program reaches the system through bundling or unprotected networks and plants itself in some type of web browser. In addition, bogus entries are also added to the Windows Registry section.
Once infected with this rogue application, be prepared to deal with unpleasant activities such as advertising and redirecting during browsing sessions. Besides, Searchmine.net might aim to gather information about your browsing activities and use it for income-related purposes. Usually, such type of data is gathered in order to create beneficial-looking offers.
Browser hijacker infiltration techniques and ways to avoid it
According to tech professionals[5], PUPs spread bundled in freeware or shareware packages.[6] These free applications obtain online can contain optional components that could be removed before the installation is complete. Unfortunately, developers often fail to disclose the information how to do so, and deceptively ask users to use Recommended or Quick installation modes.
In order to avoid browser hijacker infections, follow these guidelines:
- When installing free software, always opt for Advanced or Custom installation settings. Then, remove all the optional components before the installation of the desired application is finalized;
- Avoid browsing questionable websites, as well as file-sharing domains;
- Download and install an antivirus program on your computer. If kept up-to-date it can detect even the most recent threats;
- Finally, be attentive and do not trust everything that is suggested to you on the internet.
Check our Weknow AC removal guide on YouTube
Weknow.ac removal might be challenging – we already mentioned that the browser hijacker uses advanced persistence techniques in order to stay inside the infected computer as long as possible. Therefore, moving the unwanted app into the Trash folder is usually not enough.
If you are a novice computer user or find it difficult to follow written guides – we prepared a comprehensive video that will help you terminate the browser hijacker and stop it from showing alternative search results on all browsers, as well as displaying intrusive pop-up ads on all websites that you visit.
Eliminate the Weknow.ac fake search engine quickly
If you want a fast we.know.ac virus removal, consider downloading and installing an anti-malware program. Pick one of the programs mentioned below, download it and bring it up to date. These tools will get rid of the cyber threat within a couple of minutes.
To remove the virus manually, you should eliminate all browser extensions and questionable applications that you do not recognize. For that, follow our step-by-step guide below this article. Make sure that execute each step with great caution. If you make mistakes, Weknow.ac virus might return.
However, users mentioned that even after removing Weknow AC malware from the system as well as browsers, the hijacked search engine would not go away on Google Chrome, as the PUP modifies the policies of the browser. Here's what to do to fix that (advanced removal):
- Go to the Application folder on your Mac;
- Select Utilities and double-click on Terminal to open it;
- In the command prompt, type in the following lines and hit Enter after each:
defaults write com.google.Chrome HomepageIsNewTabPage -bool false
defaults write com.google.Chrome NewTabPageLocation -string “https://www.google.com/”
defaults write com.google.Chrome HomepageLocation -string “https://www.google.com/”
defaults delete com.google.Chrome DefaultSearchProviderSearchURL
defaults delete com.google.Chrome DefaultSearchProviderNewTabURL
defaults delete com.google.Chrome DefaultSearchProviderName
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of weknow.ac. Follow these steps
Uninstall from Windows
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of weknow.ac registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting browser hijacker
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ What Does a Browser Hijacker Do?. Solvusoft. Malware encyclopedia.
- ^ weknow.ac in Chrome complaint. Discussions. Apple customer forum.
- ^ Definition of: PUP. PC encyclopedia. Tech definitions.
- ^ Identity fraud. Wikipedia. The free encyclopedia.
- ^ Odstranitvirus CZ. Professional tech tips.
- ^ Liam Tung. Google: Unwanted bundled software is way more aggressive than malware. ZDNet. Technology news, analysis, comments and product reviews.























