(Solved) Win32:Evo-gen explained. Thorough removal guide for 2020
Win32:Evo-gen Removal Guide
What is Win32:Evo-gen?
Win32:Evo-gen – is the threat indicator that can be triggered on Windows devices
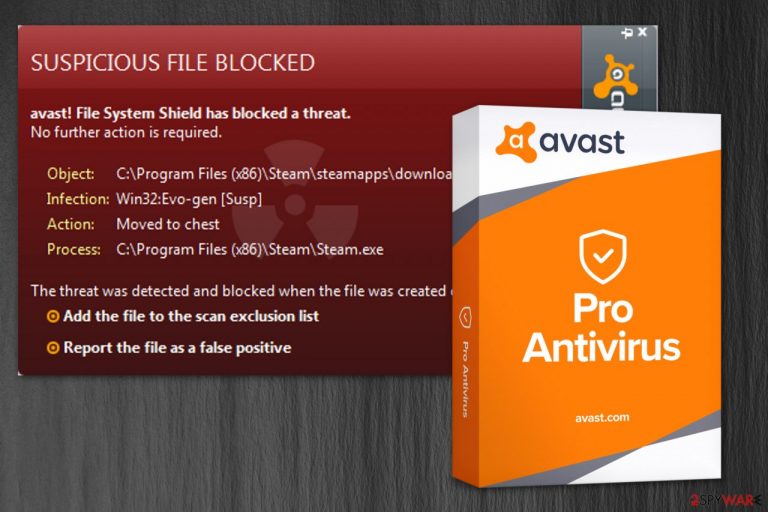
Win32:Evo-gen is a heuristic detection name used by anti-malware tools on Windows OS devices – it shows up when a trojan horse is found on the system, or a file/ application appears to have trojan-like features or such behavior. This broad classification is used by the Avast Behavior Monitor feature that finds exhibits of suspicious behavior and categorizes those detections as potentially malicious indications.
Alternatively known as Win32:Evo-gen [Susp], Win32:Evo-gen is an infection code used by Avast antivirus software. The threat can be either a potentially unwanted program or a Trojan horse,[1] so the term does not describe the virus accurately and can report any program or process that is running on the machine.
Besides, the heuristic code can also be used in false positives, so you should double-check the file before removing it from the system. This is the reason why symptoms, distribution methods in damage level can vary. Either way, you need a full system scan using anti-malware tools to diagnose the issue further.
| Name | Win32:Evo-gen |
|---|---|
| Type | Heuristic detection name/ trojan |
| Meaning | This detection indicates potentially malicious behavior of processes or programs, files. It can report the trojan infiltration or a potentially unwanted program |
| Possible symptoms | Commercial content, system slowdowns, other malware infiltrations, crashes, or freezes. Malware infections cause suspicious processes in the background and appearance of files or programs installed without your permission |
| Main danger | Malware can use your computer for fraud or malicious processes like cryptocurrency mining. Hackers may access information stored on the device, remotely manage the system, or inject the computer with serious malware like cryptovirus |
| Distribution | Pirated software, torrent sites, malicious files. Fake software and such installations can deliver malicious files and programs to the system |
| AV tool | Avast is the software that uses this detection name for a general indication of malcious behavior |
| Diagnosis/ elimination | You should scan the machine with a professional anti-malware tool to know if you need to remove the threat or analyzed further instead to avoid system corruption issues |
| repair | Recover any functions that get altered with the help of FortectIntego |
Win32:Evo-gen might appear as an infection detection, but later on after the proper system scan it is not blocked because of the in-depth analysis that shows the real purpose of the file or a program in question. Always check it further with a reputable anti-malware tool if you have any suspicions about the file or program before you delete it completely.
Since this is the generic detection that can mean many scenarios and different malware infections, such malware can install itself by copying its executable to the system folder. Once those files get added malware becomes more persistent. Also, such infections alter registry keys, one that can be associated with the malicious activity that may appear on your device: HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run. It is supposed to run the executable at each system reboot.
The initial Win32:Evo-gen payload can be designed to:
- download and spread other malware;
- use resources of your device;
- record keystrokes and steal that data;
- send information from your machine to a remote hacker;
- give remote access to a malicious actor;
- show commercial content to generate ad revenue.
All these actions can appear on the screen alongside general slowness and system crashes, but you need to assess these symptoms and further scan the device before jumping to conclusions. The virus removal can be more damaging to your device if you try to delete associated files or even registry keys.
Anti-malware tools are the way to go because those tools can show the purposes of the file and perform termination if needed. If you know the program or file that is suspicious, try to upload it on VirusTotal or a similar malware scanning service. Try SpyHunter 5Combo Cleaner or Malwarebytes as alternate tools.
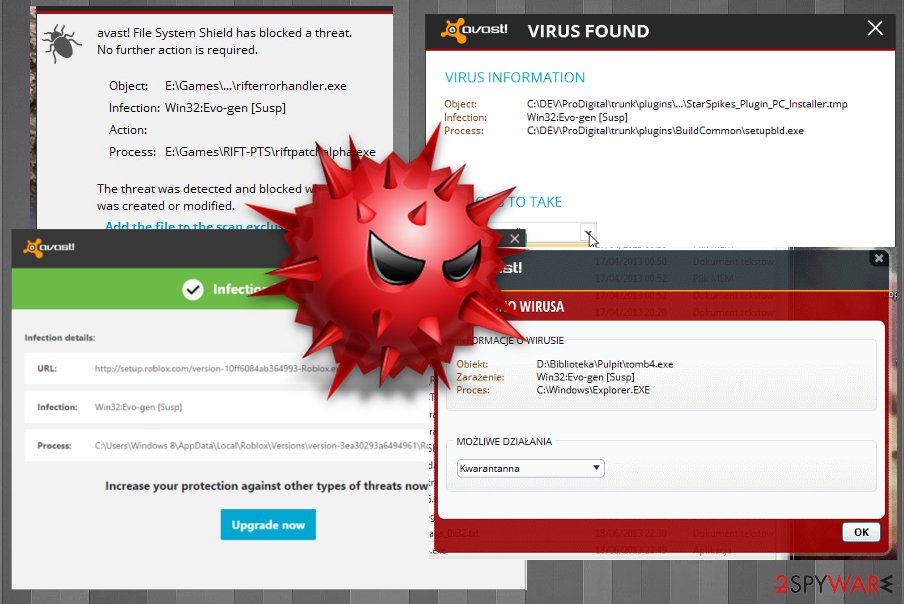
Win32:Evo-gen is the detection alert that Steam users and online gamers encounter more often than other internet browsers. Such services, in general, get to be indicated as malicious or harmful while they are not. It seems suspicious, but when you block the file installation or delete the suggested program, some functions may not work anymore. You need to either inspect the file or application more or simply restrain from using the given or service.
If the security alert actually identifies a Trojan Horse on your computer, it might initiate typical activities, such as dropping a keylogger to track the victim's online activity and log the keystrokes. This way, criminals can take over credentials like account logins, passwords, and other valuable information, leading the victim to money loss or even identity theft.
Moreover, Win32:Evo-gen might indicate an infection that can lead to the installation of other high-risk computer threats, such as ransomware or malware. Programs with Trojan-like viruses can exploit backdoors[2] which help to find system vulnerabilities to infect your PC. Likewise, you might lose your date due to the infiltration of file-encrypting viruses as well.
Thus, we strongly recommend you to immediately check your system with different antivirus software and remove the infection. Note that regular computer users are not experienced enough to tell whether their systems are at risk. Likewise, we advise you to use FortectIntego to run an entire computer scan.
Additionally, BedyNet.ru[3] team recommends you using professional anti-malware software after Win32:Evo-gen removal as well. This way, you will be fully protected from all potentially dangerous computer hazards in the future, and any executables or different files related to the intruder can get deleted completely. ![The illustration of Win32:Evo-gen [Susp] alert The illustration of Win32:Evo-gen [Susp] alert](https://www.2-spyware.com/news/wp-content/uploads/virusai/win32evo-gen-susp-alert-might-be-false-positive_en.jpg)
Freeware sources need to be reliable to avoid unwanted applications
Usually, a malware detection alert appears when the user downloads a suspicious file or software from shady websites. Since the security software is not sure whether the application is actually malicious, you can simply avoid this infection alert by downloading software only from official pages. Many users[4] reported that they encountered such alert after YouTube Downloader installation or during a video game cracking. These activities are involving pirated software sites, torrent services, promotional content.
Also, change Quick/Recommended parameters of the installer to Advanced/Custom if they were pre-selected. Always choose Custom installations because the previous setup is designed to skip many essential steps of the installation procedure, which increases the risk of infiltrating potentially unwanted programs (PUPs).
Afterward, attentively seek any checkmarks which have been ticked before and de-select them. Those marks allow installing additional software on your computer that might be malicious and put your computer's security at risk. Likewise, you should be careful when installing third-party software on your PC.
Keep your anti-malware tools updated because outdated programs or tools that use old virus databases can show false positive detections and indicate games or files that are harmless and safe as malicious or dangerous. Before terminating any file or program that seems suspicious, run a system scan to be sure about the purpose of the one in question.
Learn how to get rid of Win32:Evo-gen [susp] from the system
To help you remove the intrusive virus from the system, we highly recommend employing professional malware removal software. It will scan your computer for cyber infections and will help you get rid of malicious files within several minutes. You can use FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes to uninstall this malware from your computer or double-check the warning and make sure that it is a false positive.
Besides, you can always opt for the help of a certified IT technician, security expert, or simply use Avast Antivirus or Avast Internet Security as Win32:Evo-gen [Susp] removal tool.
Also, we kindly ask you NOT to try performing Win32:Evo-gen removal by yourself. Typically, high-risk computer infections use deceptive tricks to hide their presence. One of them is disguising as a legitimate system process. If you terminate vital processes or uninstall important files of your PC, it might cause permanent damage.
If you can't launch any security software because malware is blocking you, you should try rebooting your computer to Safe Mode with Networking or using System Restore:
Getting rid of Win32:Evo-gen. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Win32:Evo-gen using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Win32:Evo-gen. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Win32:Evo-gen and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Computer Trojan Horse Virus Information. BullGuard. IT News.
- ^ Margaret Rouse. Backdoor (computing). TechTarget. Computer Glossary, Computer Terms.
- ^ BedyNet. BedyNet. Security and Spyware News.
- ^ What is Win32:Evo-Gen[Susp] from steam?. Reddit. Online forum.







