Win32/Heri (Free Guide) - Removal Instructions
Win32/Heri Removal Guide
What is Win32/Heri?
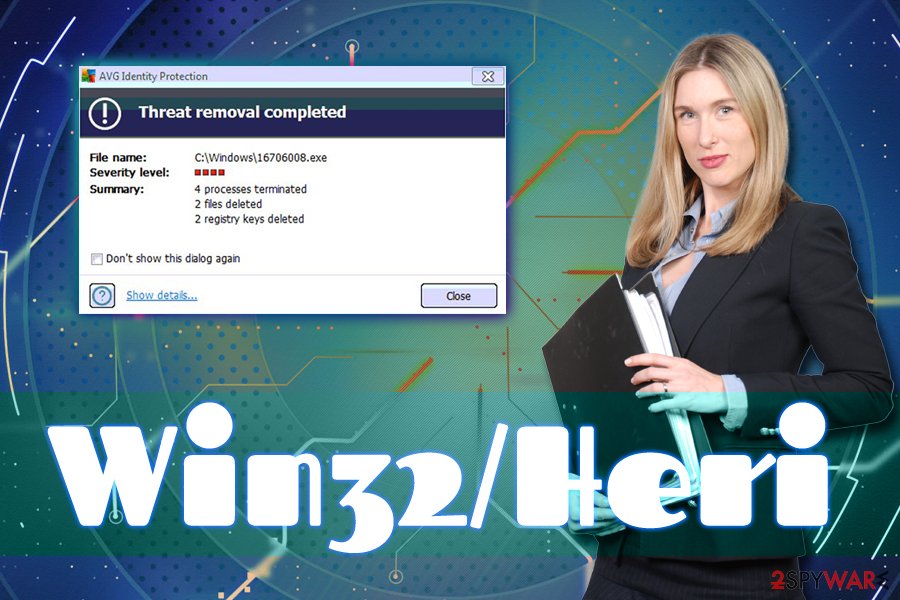
Win32/Heri is a name for a virus detection used by AVG security software

Win32/Heri is a heuristic detection used by AVG anti-malware software. While heuristic detection is an effective way to track never-before examined viruses, flag up and quarantine them, it can often result in false positives. Multiple users complained that certain games or Google Chrome[1] browser was blocked by the AV engine and then Win32/Heri was detected. If you encountered these blocks by your anti-virus software, it is important to perform certain steps before adding the file to the exceptions list, as the Win32/Heri might be associated with such threats like Zbot.
| Summary | |
| Name | Win32/Heri |
| Type | False positive or a worm |
| Associated malware | Zbot |
| Distribution | Malicious websites, backdoor |
| Elimination | Use security software like FortectIntego or SpyHunter 5Combo Cleaner to determine if the infection is false positive |
A false positive is when your security software detects a file being malicious, while, in reality, it is useful and desired. In such a case, users could be misled by their AV software, making them believe that their systems are infected with malware. However, if your AVG software flagged Win32/Heri virus, do not instantly assume that it is a false positive.
Even though it is highly unlikely, but Win32/Heri can be associated with malware such as:[2]
- TR/Crypt.XPACK.Gen
- Backdoor/Win32.Shiz
- TROJ_BAMITAL.SMK
- Mal/Zbot-AV
- Trojan/Worm, etc.
Trojans like Win32/Heri usually use deceptive methods to enter the system. Malware can be hidden in malicious or hacked websites, transferred via the backdoor, incorporated into a spam email attachment, or installed as fake updates. Unfortunately, the infiltration of the virus cannot be noticed, unless certain system settings are checked. For example, Zbot copies its executable into %System%\sdra64.exe and adds several registry keys to force the system to execute the malicious script with every system boot.
Trojan horses are one of the most dangerous infections, among ransomware and rootkits. If Win32/Heri virus enters the machine, it can perform various malicious actions, such as download and install additional malware, spawn and shut down processes, access video camera, record keystrokes, and similar. Therefore, It is vital to take care of Win32/Heri removal before sensitive information is stolen.
However, you should not remove Win32/Heri if a legitimate file is detected. For example, some users complained that Battle.net-Setup.exe (official Blizzard application),[3] FantasyGrounds.exe[4] (a virtual tabletop) or even Google Chrome is detected as Win32/Heri. In such a case, you should add the legitimate program as an exclusion.
We suggest you scan your machine with a different anti-malware software (such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes) to make sure that Win32/Heri is a false positive.
Trojan infection can be prevented with comprehensive online security measures
Trojans and worms are sneaky infections that are programmed to do everything to avoid detection. For that reason, many users are not aware for months or even years that their machines are infected. Therefore, it is vital to have reputable security software installed on your computer at all times and make sure it is always up to date (heuristic detection is used for viruses that have not been examined before by the vendor).
To avoid trojans and other malware, experts recommend the following:
- Install anti-malware software and keep it updated;
- Always scan unknown files with security software;
- Do not casually click on links or open attachments inside the spam email;
- Avoid installers from third-parties and torrent sites;
- Do not click on suspicious advertisements and pop-ups.
Remove Win32/Heri if it is a genuine virus
Before your remove Win32/Heri, you need to make sure it is not a false positive. To do that, you should uninstall AVG antivirus software, enter safe mode with networking and install reputable security program. Update it to the latest version and perform a full system scan. If the AV engine detects any suspicious activity, it will flag it and then assist with Win32/Heri removal.
As we already mentioned, there is a high chance that the Win32/Heri virus detection is a false positive. In such a case, you should add the application or executable that is being detected to exceptions. To do that, follow these steps:
- Open AVG Internet Security and select Options
- Click on Advanced
- In the newly opened window, left pane, pick Exceptions
- Click on Add Exception
As soon as you do that, false Win32/Heri notifications should stop.
Getting rid of Win32/Heri. Follow these steps
Manual removal using Safe Mode
To remove Win32/Heri and make sure it is not a false positive, enter Safe Mode with Networking the following way:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Win32/Heri using System Restore
You can also make use of System Restore to stop the virus:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Win32/Heri. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Win32/Heri and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ CAN'T OPEN CHROME BECAUSE OF WIN32/HERI VIRUS. Google Chrome. Help Forum.
- ^ Virus Profile: W32/Bamital.h!55E12B9D738F Threat Search. McAfee. Security blog.
- ^ Win32/Heri. Blizzard. Technical support forums.
- ^ Win32/Heri Virus Found!. Fantasy Ground. Virtual tabletop.







