XiaoBa ransomware / virus (Removal Guide) - updated Jun 2018
XiaoBa virus Removal Guide
What is XiaoBa ransomware virus?
XiaoBa is a file-encrypting virus that threatens users since 2017

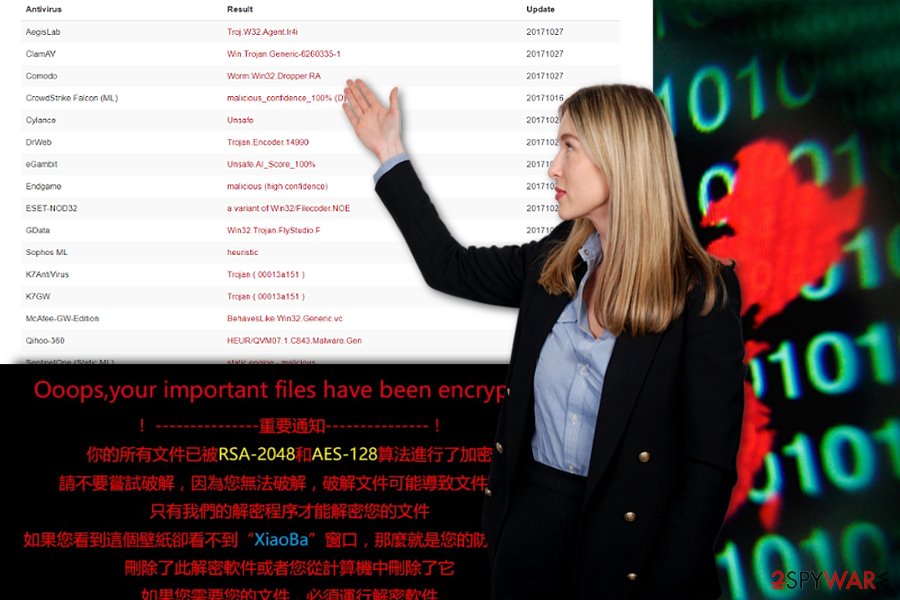
XiaoBa is a file-encrypting virus that started its activity at the end of October 2017. Originally, it aims at Chinese computer users[1] and encodes their files using RSA-2048 and AES-128 cryptography. Encrypted files become unusable due to the appended file extensions – .XiaoBa1 or .XiaoBa34. However, in June 2018, a new variant of the virus has been detected. It seems that developers decided to launch international cyber attacks and aims at English-speaking computer users. The latest version of ransomware locks data with .AdolfHitler file extension.
| SUMMARY | |
| Name | XiaoBa |
|---|---|
| Type | Ransomware |
| Versions |
|
| File extensions | .XiaoBa1, .XiaoBa34 (v 1, 2), .Encrypted[BaYuCheng@yeah.net].XiaBa (v3), .[BaYuCheng@yeah.net].china (v4), .AdolfHitler |
| Ransom notes | _@XiaoBa@_.bmp, _@Explanation@_.hta, # # DECRYPT MY FILE # #.bmp |
| Associated emails | B32588601@163.com, BaYuCheng@yeah.net |
| Distribution | Spam emails, fake updates, etc. |
| Decryption | Unavailable |
| Elimination | Download and install FortectIntego or Malwarebytes |
It seems that XiaoBa virus arrives on the system with the help of malicious spam emails. When users open an obfuscated attachment, malware payload is downloaded and executed on the computer. Following data encryption, ransomware explains how victims can recover their files in two ransom notes – _@XiaoBa@_.bmp and_@Explanation@_.hta (the note greatly resembles the one used by WannaCry ransomware).
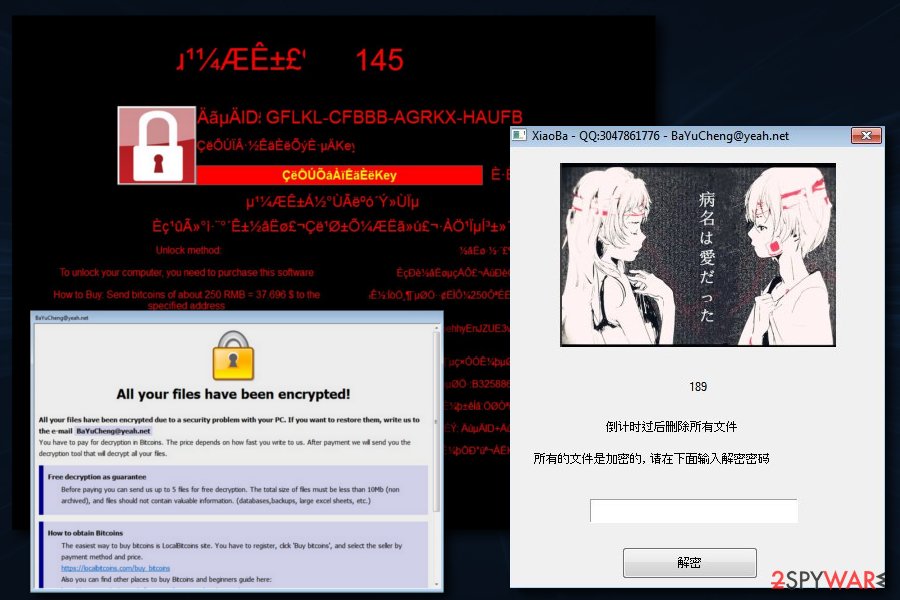
The second variant of XiaoBa ransomware came out later that year in November. Because the virus used FlyStudio[2] adware trojan, this version was also dubbed as FlyStudio ransomware. Victims are asked to pay 250 RMB ($37.7) in BTC and contact cybercrooks via B32588601@163.com email. Once inside the system and finished with its file encryption activity, virus displays such ransom note:
Ooops, your important files have been encrypted!
!—— 重要加密 —— !
你柏所有文件已被 RSA-2048 AES-128 算法進行了加密
請硕縦破解 , 因為您無 眷破解文件可能導致文壊 這可能會損害他們
只有我們的解密辦捕解密您的文件
如果您看到這個壁紙卻看不到 “XiaoBa” 窗口 , 那麼就是您的防病毒軟件
刪除了此解密軟件或葡恣從計算機中刪除了它
如果您需要您的文件I必須運行解密軟件
請找到解密軟件或從防病毒軟件隔雜區還原
運行解密軟件 , 並按照說明進行操作
請向指定地址發送約1200元人民幣=180.81$的比特幣
比特幣錢包:1GoD72v5gDyWxgPuBph7zQwvR6bFZyZnrB
想獲取更多信息請點擊桌面的 _@Explanation@_.hta
E-mail:B32588601@163.com
Though the virus is not as elaborate as WannaCry virus, it is capable of deleting shadow volume copies.[3] What is more, the virus also disables startup repair functions, which only makes XiaoBa removal more complicated.
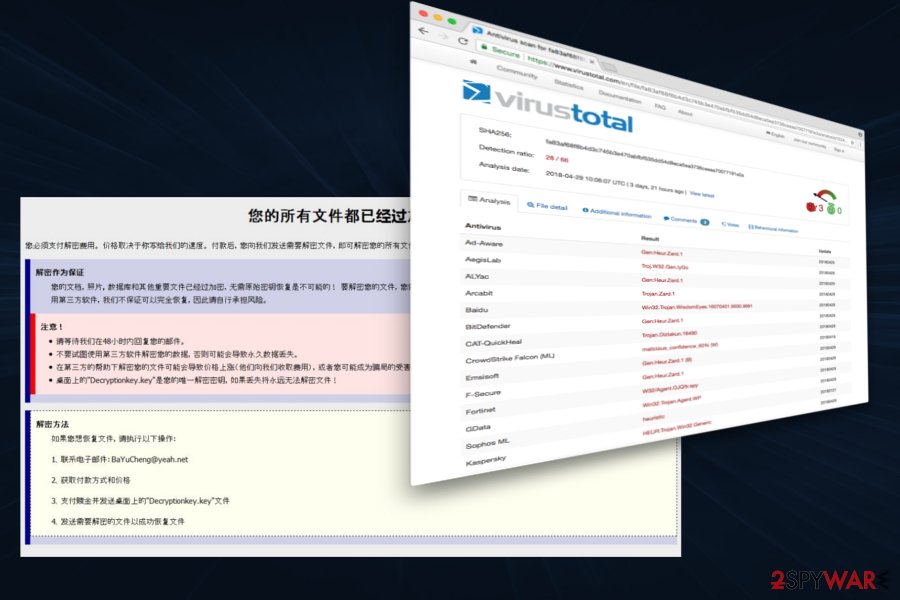
Next, at the end of February 2018, cybersecurity experts detected the third variant of XiaoBa ransomware, which appends the .Encrypted[BaYuCheng@yeah.net].XiaBa file extension to encrypted files. It also generates a ransom note named _XiaoBa_Info_.hta, which introduces the ransomware and indicates how much the victim has to pay for XiaoBa decryptor. Besides, this infection plays a voiceover from a VBA file and distinguishes from the others due to extremely high CPU consumption.
Besides, the ransomware has also been found to install these three files:
- _@XiaoBa@_.bmp
- _@Explanation@_.htaa
- xiaoba.exe
The above-given files are associated with the first XiaoBa malware version, while the executable pdf_20180118.exe has exceptionally been found in the third virus version.
While the original version is oriented to Chinese-speaking users, the third version might also seek for Japanese computer users' money as the picture it generates on the desktop features Japanese characters.
The newest variant was discovered by MalwareHunterTeam[4] in early May 2018; it came back with a new extension – .[BaYuCheng@yeah.net].china. Security experts note that it is the first variation of the virus that uses a country name in the file appendix. The ransom note is very similar to the previous version; however, it is written in Chinese only. It seems to be actively spreading via fake Flash updates.
The fact that it is written in a traditional and not simplified version of Chinese, sparks doubts about the initial target.
In case victims run into technical difficulties, they can contact the perpetrators via B32588601@163.com email address. It is not recommended to remit the payment but remove XiaoBa ransomware instead. FortectIntego or Malwarebytes might be of use in this situation. Even if the malware deletes shadow volume copies in advance, you can recover the data with the assistance of online backup copies if you have set up them in advance.
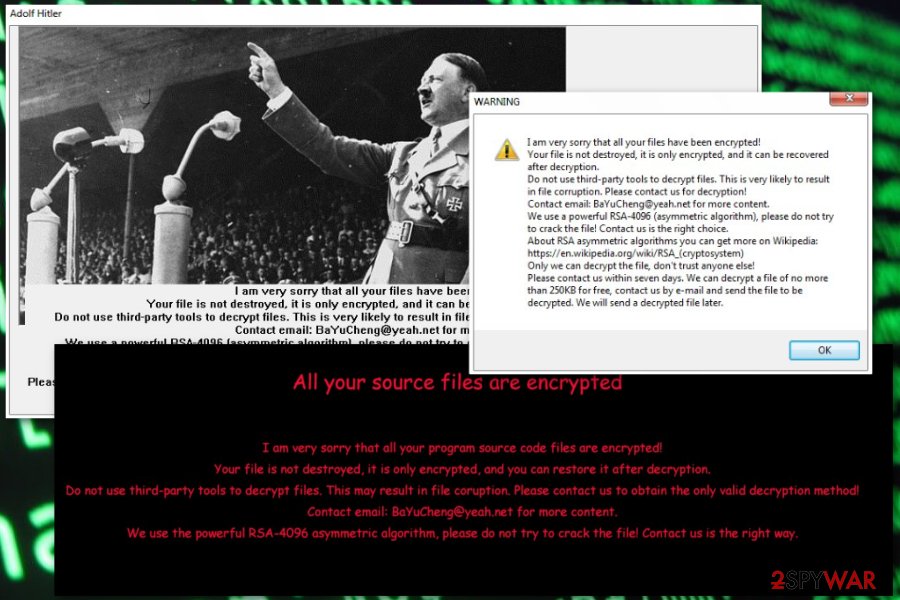
XiaoBa started using .AdolfHitler file extension to victims' personal files
In June 2018, malware researchers reported that new variant of ransomware emerged. Malware is executed from New Folder.exe file which typically is dropped from the malicious email attachment. Immediately it starts scanning the system and looks for the file to encrypt.
This time creators of malware launched a campaign targeted at English-speaking computer users, and use the name of a German historic figure. During data encryption, it appends .AdolfHitler file extension. After that, it provides data recovery instructions in # # DECRYPT MY FILE # #.bmp which becomes affected computer's wallpaper. Additionally, it delivers a pop-up window informing about ransomware attack and plays audio in the background. Thus, this cyber attack is loud and cannot be overlooked.
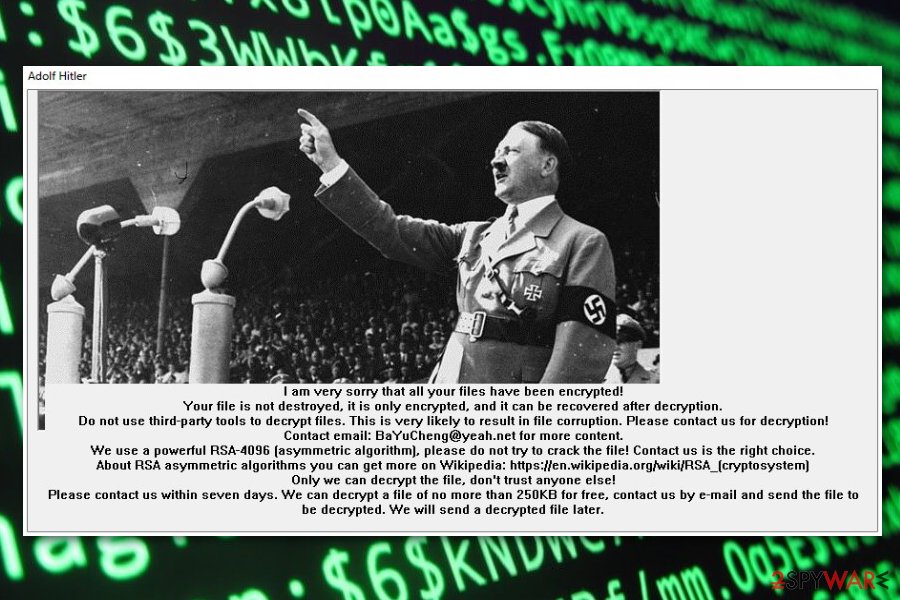
In the pop-up window, authors of the XiaoBa AdolfHitler ransomware informs that files are encrypted using RSA-4096 encryption and can be decrypted only with a specific software. In order to take this offer, victims have to send an email to BaYuCheng@yeah.net in seven days time. The new background picture also provides the same threatening message:
I am very sorry that all your files have been encrypted!
Your file i snot destroyed, it is only encrypted, and it can be recovered after decryption.
Do not use third-party tools to decrypt files. This is very likely to result in file corruption. Please contact us for decryption!
Contact email: BaYuCheng@yeah.net for more content.
We use the powerful RSA-4906 asymetric algorithm, please fo not try to crack the file! Contact us the right way.
However, security specialists do not recommend following hackers' instructions. Crooks may not provide the decryption software once they receive the ransom. Hence, instead of risking to lose the money, remove .AdolfHitler file virus from the machine with anti-malware software.
Cyber criminals might use multiple methods to spread ransomware
The malware is likely to be spread via typical means of distribution.[5] You can get infected with ransomware threats via spam emails, trojans, corrupted apps, and extensions. Exploit kits are also known to help distribute certain ransomware, but at the moment, there is no information whether this particular threat uses the services of these hacking tools.
Therefore, it is crucial to pay attention to the received spam folder. Even if the email urges to open a highly important email attachment, verify the sender before extracting the contents. Cyber villains prefer targeting users with invoices, package delivery notices, etc.
In addition, fortify the overall protection of the device with a few different type applications. Do not download content from websites with no HTTPS protocol or crowded with ads. These tips should assist you in warding off XiaoBa hijack in the future.
XiaoBa ransomware removal guidelines
Make XiaoBa removal your top priority. Since there are no guarantees that you will retrieve the data, it is necessary to eliminate the virus entirely. Since the crypto-virus meddles with the system files, it is not surprising if you may not succeed in eliminating at first attempt.
Reboot the computer in Safe Mode and launch the security tool. It should remove XiaoBa virus within a couple of minutes. If you are not sure what program to use, we suggest using FortectIntego or Malwarebytes. If you did not make online backup copies in advance, you might need to wait for the free decryption tool to be released.
Getting rid of XiaoBa virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove XiaoBa using System Restore
Enter advanced setup settings and perform System Restore, if Safe Mode does not grant you access to the computer. After that, you should be able to run the security tool and remove XiaoBa virus.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of XiaoBa. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove XiaoBa from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by XiaoBa, you can use several methods to restore them:
Use Data Recovery Pro
This tool is designed to help users recover files after an unexpected system crash. On the other hand, it might be a practical tool in the case of XiaoBa hijack.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by XiaoBa ransomware;
- Restore them.
Try Windows Previous Versions feature
This Windows feature allows recovering individual files if System Restore was enabled before ransomware attack.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Use ShadowExplorer if ransomware did not delete Shadow Volume Copies
If ransomware failed to delete shadow copies of the encrypted data, download this tool and start data recovery.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
XiaoBa decryptor is not available yet.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from XiaoBa and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ MalwareHunterTeam. XiaoBa ransomware: a Chinese junk. Twitter. Online source for breaking news and communication.
- ^ Karsten Hahn. Chinese FlyStudio adware trojan combined with ransomware. Twitter. Online source for breaking news and communication.
- ^ Volume Shadow Copy Service. Microsoft Official Site.
- ^ MalwareHunterTeam. Twitter. Social network.
- ^ Jeff Goldman. The Ransomware Epidemic: 23 Million Spam Emails Distribute Locky in a Single Day. eSecurity Planet. Internet security news and analysis.





















