Yourtopleveldefence.site ads (scam) - Free Guide
Yourtopleveldefence.site ads Removal Guide
What is Yourtopleveldefence.site ads?
Yourtopleveldefence.site pop-ups are bogus: here's what you should know

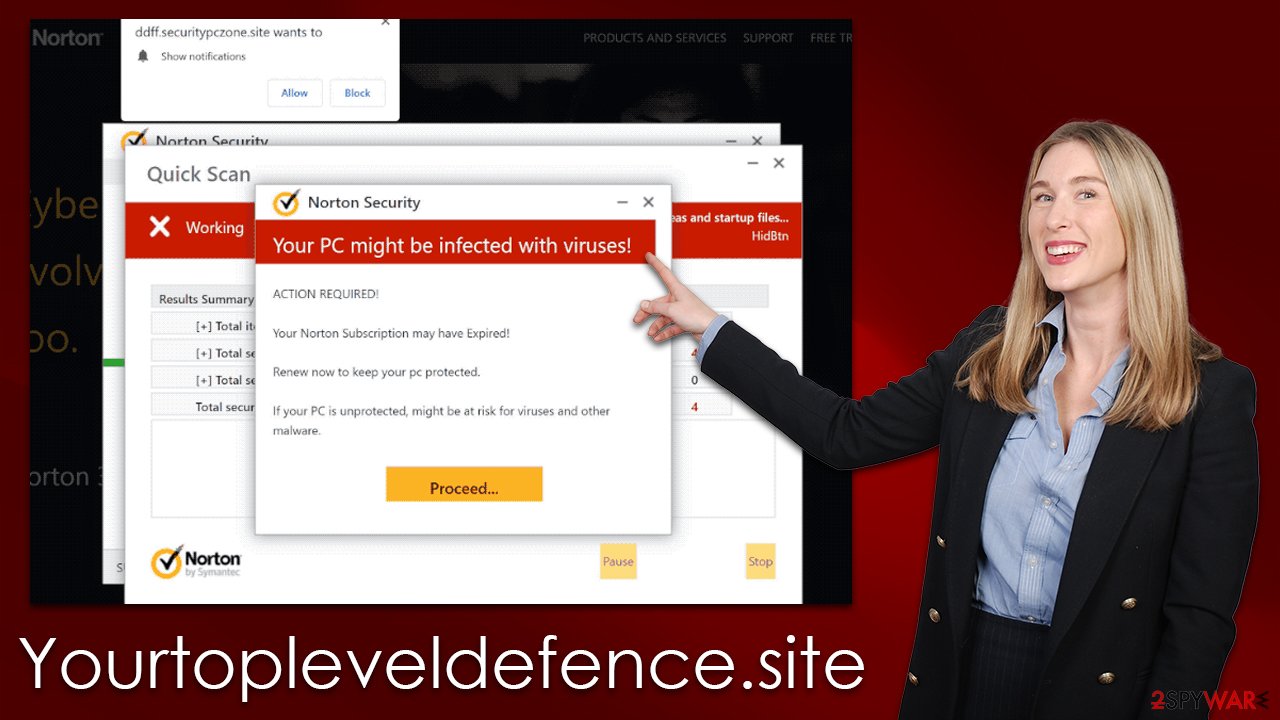
Yourtopleveldefence.site is a malicious website crafted by cybercriminals for financial gain. Users unwittingly stumble upon this page, either after being redirected by adware or tricked into clicking on a fake link from another site. To add to its credibility, the scam mimics a security scan rendered by Norton anti-malware software, and within moments displays alarming results that purport to be true.
In actuality, this is a widely-used scam tactic employed by numerous fraudulent websites. The purpose of the Yourtopleveldefence.site creators is to persuade users to believe that their devices are infected with viruses and then convince them to purchase security software licenses and subscribe for further services since an apparently reliable vendor has detected infections on your computer system. This is a classic example of scareware, which aims to exploit people’s fear of malicious software.
| Name | Yourtopleveldefence.site |
| Type | Scam, phishing, redirect, fraud, fake alert |
| Scam content | Claims that the antivirus software license has expired and that the computer is exposed to various malware |
| Distribution | Redirects from other malicious websites, adware |
| Risks | Those who have malicious software installed on their systems are more likely to encounter dangerous websites, resulting in financial losses, malware infections |
| Removal | Interacting with the scam content is dangerous, as scammers may promote fake versions of antivirus software. Instead, use reputable tools for your system safety |
| Other tips | FortectIntego can help you when dealing with leftover adware files, for example, you can get rid of various browser trackers and fix system damage automatically |
How the scammers operate their scheme
Yourtopleveldefence.site may display fake scan results with details about supposed infections found on the user's system, such as Trojans, backdoors, and other malicious code that can be removed only after buying their service.
Cybercriminals are becoming more sophisticated in their efforts to manipulate and deceive users, often relying on fear-inducing tactics. Seemingly harmless timers, warnings of grave consequences for inaction, threats of identity theft, and other forms of scaremongering can be overwhelming enough to make unsuspecting users take drastic measures, such as downloading malicious software disguised as a security tool.
The message may look like this:
Your PC is infected with 5 viruses!
ACTION REQUIRED
Your Norton Subscription Has Expired!
Renew now to keep your PC protected.
If your PC is unprotected, it is at risk for viruses and other malware.
Clicking on the “Proceed” button will redirect users to Norton's antivirus purchase website, although this may not always be the case. Criminals take advantage of affiliate marketing plans, and Norton has nothing to do with this scam. Therefore, please refrain from downloading any software or entering personal information on Yourtopleveldefence.site.
Other tactics used by cybercriminals include phishing, where victims are tricked into revealing personal information such as credit card numbers and passwords. Phishing is particularly dangerous because it can be difficult to identify a legitimate email from one sent by a cybercriminal. Additionally, hackers may use social engineering techniques to obtain confidential information or access systems and networks without permission.
How to check your system for infections
Despite the fact that Yourtopleveldefence.site scam's checks are all wrong (it provides every user with the same result), it is still essential to perform system scans to make sure there isn't any malicious or potentially unwanted software working in the background.
If you have downloaded anything from their website, your device could possibly be compromised by an adware virus; even if you didn't download anything, it would still pay off to check just in case users may have been exposed to phishing material due to this program being present on your computer.
To guarantee that the most malicious, stealthy infections are removed at once, you must first conduct a full system scan with an effective anti-malware program like SpyHunter 5Combo Cleaner or Malwarebytes. Additionally, installed unwanted programs can be manually scanned for; however keep in mind they may not always appear on the list of installed applications. By doing this, all adware and malware will be identified and eradicated.
Your next task is to clean browser caches – cookies and other trackers might be used to track you. You can easily achieve that by running a scan with FortectIntego repair or following these steps:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Finally, if you have enabled push notifications from Yourtopleveldefence.site, you might start receiving intrusive pop-up messages that would disturb whatever you are doing on your PC at the time. These notifications can include links to malicious websites, so it is vital you don't interact with them in any capacity. To remove these pop-ups, you have to block the website that's sending them via the browser settings:
Google Chrome
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and choose Block. This should remove unwanted notifications from Google Chrome.

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

How you end up on malicious websites and how to avoid that
People are frequently exposed to phishing and other malicious content when visiting websites like torrents, adult-oriented video converters, and illicit streaming platforms. These sites are notorious for harboring inappropriate or even illegal material, making them a breeding ground for cybercrime due to their lack of oversight. This makes them prime targets for malicious actors to insert phishing links and other forms of malware.
To avoid this, it is important to always check the website you are visiting before downloading or streaming content there. Make sure that the site does not have any suspicious elements like pop-ups or requests for personal information. Additionally, be aware of any ads that could be connected to the site – these can also contain dangerous links. Finally, only download content from reputable sources with good ratings and reviews. This will help ensure your safety while browsing the web.
It is also important to utilize up-to-date anti-virus software when downloading or streaming any type of digital content. This can provide real-time protection against any malicious links or harmful programs that may be present.
t is essential to be aware of phishing scams and other malicious activity in order to stay safe when interacting with the internet. Doing so can help ensure that your data remains secure and that you have a pleasant experience navigating the internet.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
