Zeussec1337 ransomware (Free Guide) - Chrome, Firefox, IE, Edge
Zeussec1337 virus Removal Guide
What is Zeussec1337 ransomware?
Zeussec1337 is a malicious Windows program designed to extort money from innocent users

Zeussec1337 is a type of ransomware that uses a sophisticated encryption[1] code to lock all personal files on your computer. This includes photos, videos, documents, databases, and other important data – all of them acquire a randomly-generated extension, which is appended at the end of the file name. The damage could be devastating if you don't have backups for these files, and they're important to you.
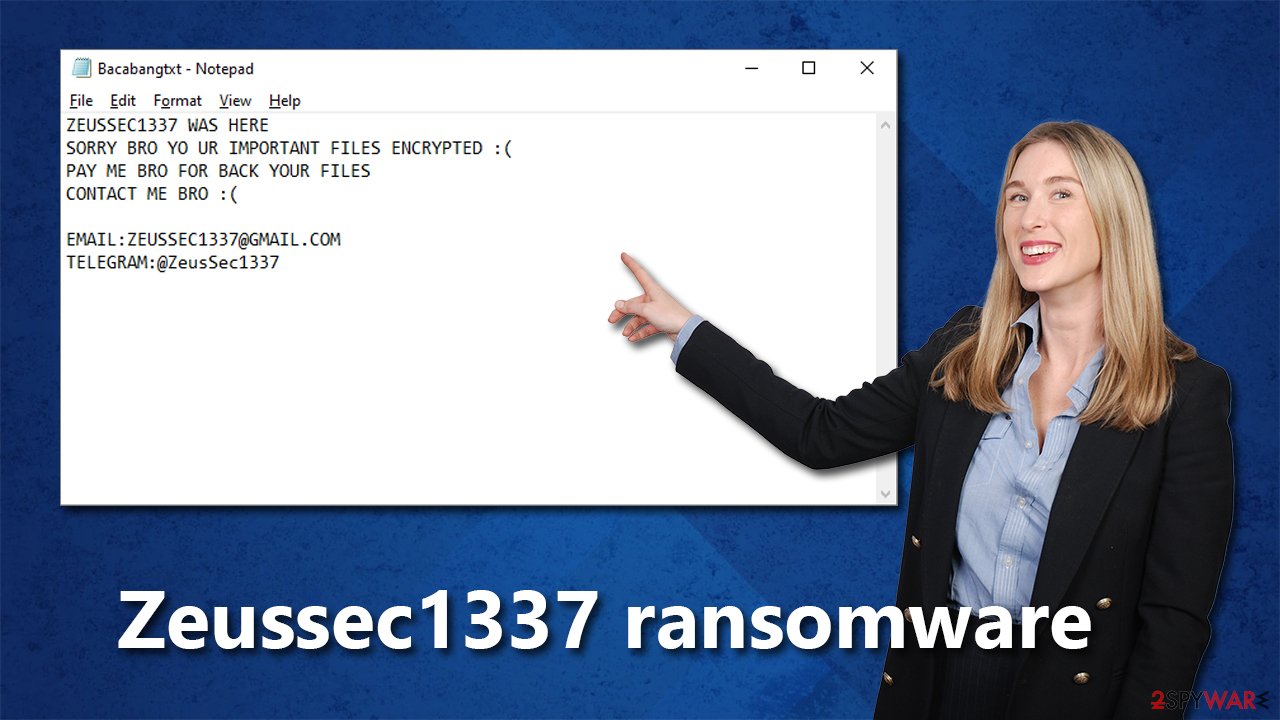
As soon as the Zeussec1337 virus finishes its encryption process, it delivers a ransom note, Bacabangtxt, and changes the wallpaper of the desktop, which includes basic information about what happened to users' files and what they need to do to retrieve them. Both of the messages claim that victims need to contact cybercriminals via the zeussec1337@gmail.com email or Telegram @ZeusSec1337.
We do not recommend making contact with the attackers, as they may never deliver the promised decryption tool. Instead, follow the instructions below to remove malware from your system and attempt file recovery using alternative methods.
| Name | Zeussec1337 ransomware |
|---|---|
| Type | Ransomware, data locking malware, cryptovirus |
| Family | Chaos |
| File extension | Random string, for example, .3ynt |
| Ransom note | Bacabangtxt |
| Contact | zeussec1337@gmail.com email or Telegram @ZeusSec1337 |
| File Recovery | If no backups are available, recovering data is almost impossible. Nonetheless, we suggest you try the alternative methods that could help you in some cases – we list them below |
| removal | Before proceeding with data recovery solutions, make sure you first scan your system with SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable anti-malware software |
| System fix | Malware can wreak havoc on Windows systems, causing errors, crashes, lag, and other stability issues even after it is terminated. To fix the operating system, we recommend scanning it with the FortectIntego repair tool. |
Crooks ask to pay in Indonesian currency
Zeussec1337 ransomware comes from a broad malware family known as Chaos, which is known for other versions, such as Flame, Phreaker, OkHacked, and many others. Unlike other ransomware families, such as Djvu, this one has relatively variable ransom notes, demands, and other characteristics.
Probably the most unique aspect of Zeussec1337 is that the virus authors ask users to pay them in Indonesian currency, known as Rupiah. In most cases, cybercriminals behind ransomware usually ask to deliver a particular sum in bitcoin[2] instead, although it is likely to be the case. Here's what the text message from cybercriminals looks like:
ZEUSSEC1337 WAS HERE
SORRY BRO YO UR IMPORTANT FILES ENCRYPTED 🙁
PAY ME BRO FOR BACK YOUR FILES
CONTACT ME BRO 🙁EMAIL:ZEUSSEC1337@GMAIL.COM
TELEGRAM:@ZeusSec1337
The same information can be found on the desktop wallpaper, which is changed right after users' data is encrypted. It depicts a masked person next to a computer – a hacker. The message reads:
ZEUSSEC1337 WAS HERE
OPPS YOUR IMPORTANT FILES ENCRYPTED CONTACT ME FOR BACK YOUR FILES AND PAY FOR ME 100$ IN INDONESIAN CURRENCY
CONTACT ME
EMAIL:ZEUSSEC1337@GMAIL.COM
TELEGRAM:@ZeusSec1337
Contacting cybercriminals is not recommended, as it may end up in financial losses. There are plenty of examples where people did not receive the promised decrytpion tool after losing money by paying the ransom. Besides, paying encourages crooks to create more malware and infect more people in the future.
Removal of malware
It's crucial to take remediation actions in the correct order, or you might lose your data forever. As mentioned before, trusting cybercriminals isn't a good idea, as it often leads to more losses. Your first goal should be making sure that malware doesn't have an active connection via the network or internet anymore, so you should disconnect your device immediately. You can either unplug the Ethernet cable or disconnect the WiFi connection. Or follow these steps:
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet
![Network and internet Network and internet]()
- Click Network and Sharing Center
![Network and internet 2 Network and internet 2]()
- On the left, pick Change adapter settings
![Network and internet 3 Network and internet 3]()
- Right-click on your connection (for example, Ethernet), and select Disable
![Network and internet 4 Network and internet 4]()
- Confirm with Yes.
After the files have been completely encrypted, some ransomware can self-destruct. Malware may still leave other modules behind in these situations that steal data or collaborate with other dangerous apps installed on your device previously. Thus, we recommend running a scan with SpyHunter 5Combo Cleaner or Malwarebytes security software, which can ensure that all threats are eliminated at once.
Antivirus software does a great job of finding and deleting harmful files, including any other potential risks that may come with it. Sometimes viruses can make it hard for security software to run properly, so in this case, you should restart your computer in Safe Mode and delete the virus from there.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.
![Windows XP/7 Windows XP/7]()
Windows 10 / Windows 8
- Right-click on the Start button and select Settings.
- Scroll down to pick Update & Security.
- On the left side of the window, pick Recovery.
- Now scroll down to find the Advanced Startup section.
- Click Restart now.
- Select Troubleshoot.
- Go to Advanced options.
- Select Startup Settings.
![Startup settings Startup settings]()
- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
To avoid any future issues, we recommend checking if the Windows system is damaged after you confirm that the malware is gone. Ransomware (and other types of malware) can corrupt files on your system, which may cause problems even after it's removed. This happens because security software is unable to repair them.
Consequently, you may experience a myriad of stability problems, such as DLL[3] missing errors, Blue Screen of Death crashes, registry issues, and beyond. To restore your operating system and fix broken files, we recommend using FortectIntego PC repair tool – software that can handle both malware-related and non-malware computer problems.
Data recovery options
Unlike a password which can be used on multiple accounts, the key to unlock ransomware only works for one person. Ransomware gains access to your personal files and encrypts them with a sophisticated encryption algorithm, meaning that you cannot open these files without the decryption key. The randomization of this long alphanumeric string is what makes Zeussec1337 so dangerous – it means that even if someone else was infected with the same strain of ransomware, they would not be able to use your key to decrypt their own files.
If you have backups available, malware can't do nearly as much damage because you can restore all your files. However, if you do not have backups, the chances of restoring files without paying are rather slim. Nevertheless, we still recommend trying to decrypt your files without paying first. Before proceeding with the steps below, please make sure you make a copy of your important files, as they might be corrupted in the process otherwise.
- Download Data Recovery Pro.
- Double-click the installer to launch it.
![Zeussec1337 ransomware Zeussec1337 ransomware]()
- Follow on-screen instructions to install the software.
![Install program Install program]()
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
![Recover files Recover files]()
Security experts are known to work on decryption tools for major ransomware strains. In some cases, flaws within the encryption process can be found or criminals' servers seized by the lay authority agencies. In any case, you could look for decryptors on the following pages, although keep in mind it might take a while until there's a working one made.
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Encryption. Investopedia. Sharper insight, better investing.
- ^ Jake Frankenfield. What is Bitcoin? How to Mine, Buy, and Use It. Investopedia. Source of financial content on the web.
- ^ What is a DLL. Microsoft. Documentation.










