Abaddon RAT (Removal Instructions) - Virus Removal Guide
Abaddon RAT Removal Guide
What is Abaddon RAT?
Abaddon RAT is the malware that uses the Discord app as a command & control server
Abaddon RAT is the intruder with a ransomware feature and gets instructions from creators via the Discord application. Threat actors are known for abusing the Discord platform because its popularity helps to distribute malware around. This RAT[1] relies on a remote host that is a method to receive commands for execution on the infected machine. Once processes start on the targeted computer, trojan automatically steals information from the PC: cookies from Google Chrome browser, saved credit card credentials, other information, steam logins, and a list of games installed, Discord tokens, MFA information, file listings, information about the system. Additional commands can be received via the same Discord C&C server.
| Name | Abaddon RAT |
|---|---|
| Type | Remote access trojan |
| Issues | The trojan can steal data from the machine, access files, programs, control processes, and install other malware on the system |
| Distribution | The threat can be distributed via infected email attachments, malicious sites online, and even during social-engineering campaigns or with the help of other viruses |
| Features | The threat can steal credentials, files, directories. It also manages to execute commands that trigger additional infections. The feature that allows attackers to deploy ransomware is in development also |
| Elimination | Abaddon RAT removal process can be difficult because of the shady infiltration methods and persistence, so anti-malware tools are required |
| Repair | You should consider virus damage and run a tool like FortectIntego for the PC repair |
After analyzing, researchers revealed that Abaddon RAT virus could get commands to steal files or directories, add an open reverse shell that allows attackers to execute commands, launch ransomware, send collected information to threat actors. Such collected details can be used in later attacks.[2]
This connection with the command and control server happens every 10 seconds, so the Abaddon RAT is active and executing new tasks all the time. It might trigger issues with the machine's speed or performance, but generally, victims can't notice the intruder or spot that there are any issues with the computer.
Abaddon RAT has many tasks, and one of them is to run a basic ransomware virus. This threat encrypts computer with the help of a basic algorithm and claims to decrypt files after the ransom is paid. The feature is in development, according to experts. However, ransomware is extremely dangerous, so this feature will most definitely be completed and executed, so malicious actors can make a profit easily.
Abaddon RAT is used to collect sensitive information and trigger other malware infiltrations, so ransom gets paid for encrypted file recovery, or stolen credentials get used in later attacks against users. It is possible to suffer huge losses of money after credit card credential usage for direct transfers.
You need to remove Abaddon RAT as soon as possible, so you can ensure that additional commands cannot get executed and your machine is safe. Various issues can be caused by this malware piece and other intruders that trojan injects into the system behind your back.
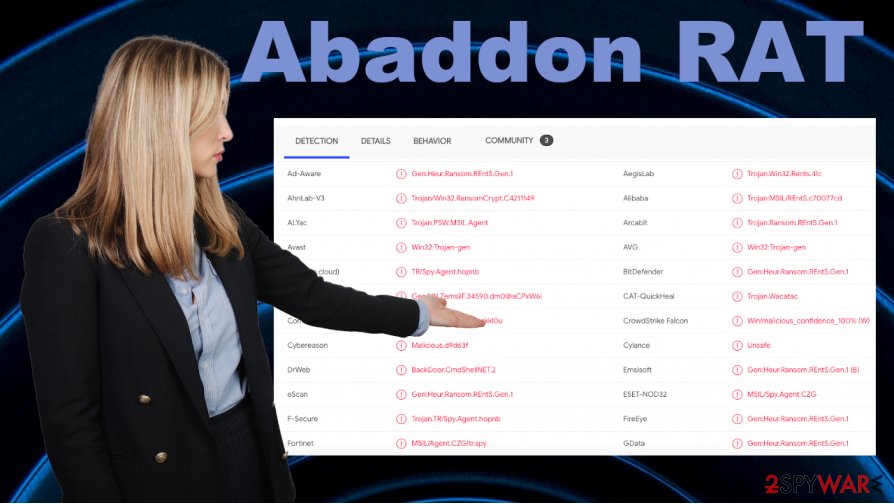
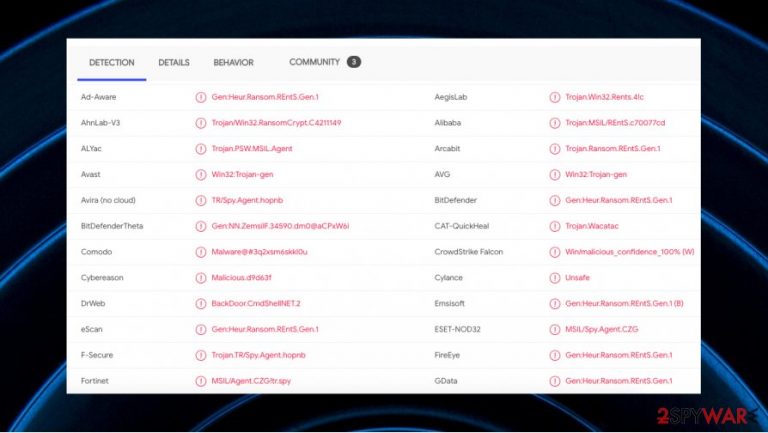
Abaddon RAT removal success depends strongly on the detection rate and the anti-malware tool that you use for the procedure. Detection names that appear on the screen when you indicate the threat can be very different because AV tools use various malware databases. These are some of the possible names for this trojan:
- Spyware.DiscordStealer;
- Trojan.Malware.73593052.susgen;
- BackDoor.CmdShellNET.2;
- TScope.Trojan.MSIL;
- W32.Trojan.Gen;
- HEUR:Trojan.MSIL.Agent.gen;
- Win32.Trojan.Ransom.Ebqg;
- BackDoor.CmdShellNET.2;
- Trojan.Ransom.REntS.Gen.1.[3]
Rely on proper tools that can find this threat and additional intruders that Abaddon RAT malware installed once received such a command. The manager of this threat can steal various data and trigger damage to your computer. Do not hesitate when it comes to eliminating such threats, and do not forget to fix virus damage with tools like FortectIntego.
Malicious files hide serious malware payload
The payload of such threats mainly gets distributed with the help of email campaigns and even social engineering because people get tricked into opening a link to a hacked page or downloading executable, another type of file that triggers the C&C server connection and the drop of RAT, malware, worm. You can catch such intruder from:
- torrent sites;
- hacked pages;
- pirated software packages;
- email attachments.
The main issue with such infiltration methods is the fact that users cannot control the installations or notice the drop in the first place, so all the activities can run without users' knowledge. You can avoid these infections if you pay close attention to details, avoid getting anything suspicious from the internet.
Get rid of the Abaddon RAT virus and clear the system properly after the virus termination procedure
Since Abaddon RAT is silent and shady, you cannot find the file that triggers all the functions yourself. The best option for the proper system clearing procedure is a proper scan of the infected device, so tools designed to fight viruses can detect and eliminate all threats related or not associated with this trojan.
To remove Abaddon RAT, you need tools like SpyHunter 5Combo Cleaner or Malwarebytes, so the machine is checked for any suspicious or malicious pieces. Once the system scan is triggered, you can see the list with intruders and get rid of the infection or any possible threats. Tools like anti-malware or PC security programs can indicate active infections and clear any viruses for you.
However, Abaddon RAT removal is not the process that can ensure that your system is safe and works as it is supposed to. You need to repair the damage that trojan triggers on your machine, and the best way to do so – with system tools like FortectIntego. You might benefit from features that the Windows OS devices have, so follow the guide below.
Getting rid of Abaddon RAT. Follow these steps
Manual removal using Safe Mode
You might benefit from the reboot in Safe Mode with Networking that allows running a proper Abaddon RAT termination
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Abaddon RAT using System Restore
System Restore feature should help because it recovers the machine in a previous state
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Abaddon RAT. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Abaddon RAT and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting remote administration tools
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ RAT. Howtogeek. IT and security terms explained.
- ^ Pierluigi Paganini. Is the Abaddon RAT the first malware using Discord as C&C?. Securityaffairs. Security news.
- ^ Payload file detection rate. VirusTotal. Online malware scanner.







