AccessibleInput Mac virus (Free Guide)
AccessibleInput Mac virus Removal Guide
What is AccessibleInput Mac virus?
AccessibleInput is a malicious application stemming from one of the largest Mac malware families
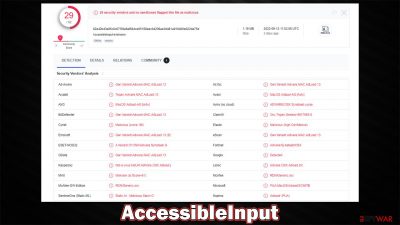
AccessibleInput is a dangerous Mac application created to hijack web browsers, deliver bothersome ads, and make it difficult to remove with lasting methods. The virus belongs to a large family of Adload malware, and the cybercriminals behind it have already published hundreds of variations that are all laden with malicious features.
Malware often uses simple but effective methods to spread, such as pirated software installers and fake Flash Player updates. Even though these techniques are not very sophisticated, they work well, infecting hundreds of users with AccessibleInput adware and other variants every day.
When running on the device, the virus constantly subjects users to various online threats, including phishing messages claiming malware infections, fake giveaways, and get-rich-quick[1] schemes. Furthermore, users would be regularly harassed by pop-ups, auto-play videos, banners, and other ads while browsing the web through Safari, Chrome, Firefox, or another browser that's been hijacked.
| Name | AccessibleInput |
| Type | Mac virus, adware, browser hijacker |
| Malware family | Adload |
| Distribution | Pirated software installers, fake Flash Player updates, misleading ads |
| Symptoms | Installs a new extension and application on the system; changes homepage and new tab of the browser; inserts ads and malicious links; tracks sensitive user data via extension |
| Removal | Although not recommended to novice users, manual elimination of Mac malware is possible. We recommend performing a full system scan with SpyHunter 5Combo Cleaner and removing all the malicious components automatically |
| System optimization | If you don't keep your browser clean of cookies and other web data, ads you've seen before will reappear, or your data could continue being tracked. But FortectIntego can help stop that |
How Adload spreads and how to avoid it
When it comes to the distribution of Adload versions, they use mostly Flash Player installers that have been repacked (Player.app is one of the most common package names used by it). For example, you may come across an ad that claims that the plugin is outdated and is needed to play the multimedia content on the current or next page.
Since Flash is such a notorious plugin, many people still have plenty of associations about it. However, it was discontinued a few years ago[2] due to it being prone to vulnerabilities[3] that hackers so often exploit. Therefore, all requests to update Flash are now fraudulent, and you are likely to infect your Mac with it.
Adload is also distributed through software cracks and pirated software installers, which are both illegal. People who go to peer-to-peer networks and similar locations are considerably more likely to be attacked by malware, therefore, we recommend avoiding these in general.

How to remove the AccessibleInput virus
Because Adload versions are installed without users' knowledge, they often provide elevated permissions for the app when confirming the installation by entering their AppleID. This leaves them vulnerable to exploitation via built-in AppleScript, which allows AccessibleInput to drop malicious files onto the system and stay running at all times, regardless of removal attempts.
New components, such as Login items or Profiles, are created within the user account. This allows the virus to prevent its easy removal. If you value your time and don't want to waste it attempting manual removal (which is by no means guaranteed to be successful), we recommend using SpyHunter 5Combo Cleaner or Malwarebytes security software to get rid of the virus automatically. If you still would like to perform these steps manually, follow the instructions below.
Before proceeding with the elimination of the main app, you have to find malicious processes it is running in the background, as it may prevent a smooth elimination process otherwise.
- Open Applications folder.
- Select Utilities.
- Double-click Activity Monitor.
- Here, look for suspicious processes and use the Force Quit command to shut them down.
- Go back to the Applications folder.
- Find the malicious entry and place it in Trash.
![Uninstall from Mac 1 Uninstall from Mac 1]()
Login items ensure that the app starts as soon as the computer boots, and Profiles are used to manage various account settings. Get rid of malware-related components:
- Go to Preferences and pick Accounts.
- Click Login items and delete everything suspicious.
- Next, pick System Preferences > Users & Groups.
- Find Profiles and remove unwanted profiles from the list.
Finally, you should get rid of the leftover files. The PLIST files are small config files, also known as “Properly list.” They hold various user settings and hold information about certain applications. To remove the virus, you have to find the related PLIST files and remove them.
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
Cleaning your browsers is equally as important for the AccessibleInput removal
The extension plays a vital role in the virus' operation cycle. This component makes sure that browser settings are changed (homepage, new tab address, and the search provider) and that users always have a steady flow of ads.
Furthermore, the extension can be used to collect personal information about anyone who has it installed. This is possible because the virus requests elevated permissions during installation. Clearly, this presents serious privacy issues and can lead to identity theft. Thus, uninstalling this extension is essential. Note that security software would get rid of the browser extension component automatically for you, so you can skip this step if it's no longer there.
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Once you uninstall the extension, be sure also to delete all its cached data from your local folders, or it may continue to track your activities. FortectIntego is a great tool for automating this process and can also remove other junk from your system to improve performance. If you prefer doing this manually, follow these steps:
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
If you can't remove malware components from your web browser, resetting it is a good option. Your bookmarks and other settings will not be deleted.
Safari
- Click Safari > Preferences…
- Go to the Advanced tab.
- Tick the Show Develop menu in the menu bar.
- From the menu bar, click Develop, and then select Empty Caches.
![Reset Safari Reset Safari]()
Google Chrome
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.
![Reset Chrome 2 Reset Chrome 2]()
Getting rid of AccessibleInput Mac virus. Follow these steps
Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Get rich quick scams. SRA. Solicitors Regulation Authority.
- ^ Tim Brookes. Adobe Flash is Dead: Here’s What That Means. How-to Geek. Site that explains technology.
- ^ What is a Software Vulnerability?. JFrog. Software Supply Chain.












