Allwownewz.com (Easy Removal Guide) - Chrome, Firefox, IE, Edge
Allwownewz.com Removal Guide
What is Allwownewz.com?
Allwownewz.com is a dubious website that attempts to trick you into accepting its notifications
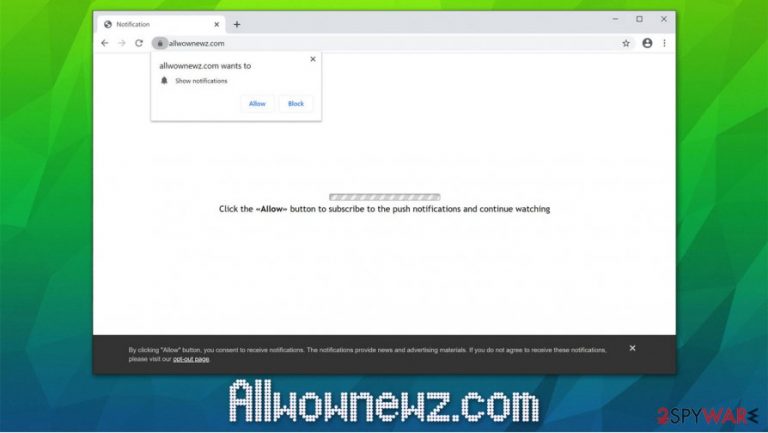
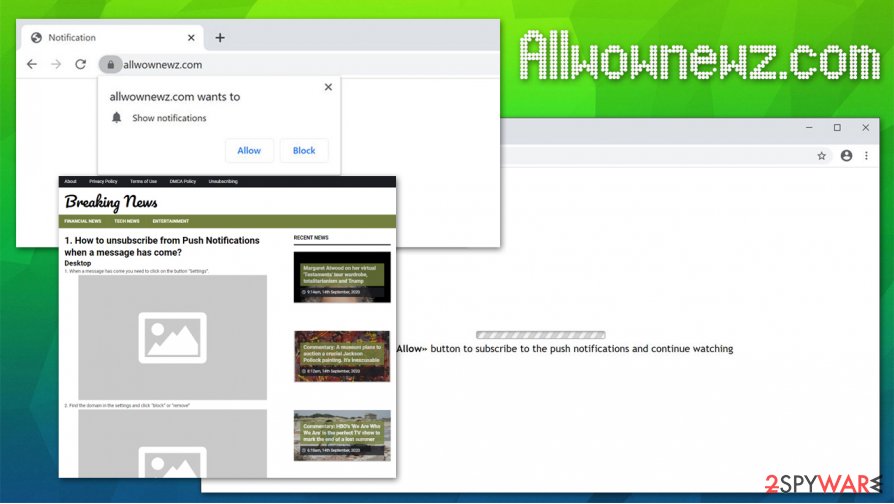
Allwownewz.com is a website that users might encounter at any time when browsing the web on Google Chrome, Mozilla Firefox, Safari, or another browser. While initially, it may seem that the site specializes in publishing articles in tech, entertainment, and financial sections, its main goal is to use deceptive or even scam techniques in order to make users allow notifications to be shown. As soon as users click “Allow,” Allwownewz.com would begin to deliver intrusive ads directly to their desktops, regardless if the web browser is in operation.
Allwownewz.com ads can also pose a serious danger to users, as they can display links to click-bait, phishing,[1] fake update on similar malicious websites. As a result, users might infect their computers with potentially unwanted programs or malware, provide personal information to unknown parties, and suffer financial losses due to frequently-encountered scams.
| Name | Allwownewz.com |
|---|---|
| Type | Rogue website, push notification virus |
| Related | Yourniceposts.com, Thewowfeed.com |
| Appearance | Notifications are enabled as soon as the “Allow” button is pressed; adware can be distributed via various deceptive sources, including software bundles, fake update prompts, deceptive ads, and other methods |
| Dangers | If you allowed the notifications to be shown, you are not in danger as long as you click on the presented links. However, the delivered ad links can lead to malware-laden, scam, phishing, and other malicious websites |
| Symptoms | Intrusive popup ads can be shown at any time, even when the web browser is turned off – these notifications often advertise suspicious services and show scam messages in order to trick users in various ways |
| Removal | You can get rid of the notifications by accessing your web browser settings – check the instructions below |
| Additional checks | If you noticed unsolicited browser changes, such as frequent redirects and intrusive ads, you should check your system for adware either manually or by scanning it security software such as SpyHunter 5Combo Cleaner or Malwarebytes. After you delete the infection and encounter system stability issues, you should attempt to fix them with a repair tool, such as FortectIntego |
The site notification feature was first introduced by Google on the Chrome browser back in 2012. Initially advertised as a useful addition to daily browsing, users were soon fed up with intrusive popups on most sites that they visit.[2] To make matters worse, deceptive and phishing websites began to abuse the feature in order to promote advertisements to users on a massive scale.
Allwownewz.com uses social engineering to make users allow notifications to be shown. In essence – the notification is a scam, as it shows claims that are completely not true. First of all, upon entry, users will be prompted with the following statement:
Click the “Allow” button to subscribe to the push notifications and continue watching
It is evidently implied that the site is attempting to show some type of video, and users need to press “Allow” in order to continue watching it. However, there is no video to be viewed, and users will be shown on the main page of the domain, promoting various news articles. In some other cases, Allwownewz.com might use different tactics to make users allow notifications, e.g., “Confirm that you are not a robot” prompts are also extremely common.
Unfortunately, most who agree to these notifications are not quite sure how the feature works and are typically unaware of how to perform Allwownewz.com removal. While many believe that they simply allowed the browser to show a video, it could not be further from the truth – they will never be shown what they promised, but instead would be shown intrusive popup notifications that include suspicious links.
These popups might not be shown right away, so users might not be aware that they just allowed the site to inject ads directly to their screens. Once they see the pattern, however, they do not know how to remove Allwownewz.com notifications from their system. If you are one of such individuals, you can check detailed instructions on the notification deletion below.

While some users might believe that intrusive notifications are caused by some type of infection (hence users might call it the “Allwownewz.com virus”), it is not technically true. Allowing notifications will not infect your system or browser with anything, although clicking on promoted links can end up badly. Nonetheless, if you keep getting redirected to suspicious websites, you should keep in mind that your machine might indeed be infected with adware or other potentially unwanted software.
For that, you can use reputable anti-malware tools, such as SpyHunter 5Combo Cleaner or Malwarebytes. Alternatively, you can also check the installed program list and eliminate unwanted programs manually. Finally, you can also reset web browsers and improve your system performance with a repair program such as FortectIntego.
Online fraud is relatively common – don't let crooks fool you
Thanks to the rise of cybersecurity awareness and improved security features implemented by such tech giants like Google, the internet is much safer today if comparing it with 20 years ago. Nonetheless, it does not mean that the internet is a completely safe place to be, as threat actors keep coming up with new methods of how to infect users with malware, make them install potentially unwanted programs, or provide their personal information that might later be misused by various parties.
Threat actors abuse the infrastructure and built-in components in order to reach their goals. For example, software vulnerabilities and exploits[3] are often used to inject malware into users' machines automatically (this can easily be prevented by ensuring that all software is up to date, although this does not apply for 0-day flaws). Despite this, sophisticated delivery methods are not the only threats that regular computer users might encounter.
For example, fake Flash updates are commonly used to introduce potentially unwanted programs to millions of computers worldwide. This flawed plugin is no longer required, so users should always ignore prompts that ask them to update or download Flash Player.
Push notifications should also not be accepted from various websites, despite what the content claims – there is no video to view, and you will not be provided with underlying content. Additionally, you should also stay away from torrent and similar sites that allow users to download cracked software and similar unsafe installers.
Get rid of Allwownewz.com notifications once and for all
If you have encountered the so-called Allwownewz.com virus for the first time, you should not worry too much, as long as you did not click on any links that were provided within the popups. Otherwise, your system might get infected with all kinds of malicious software, so you should check the machine with anti-malware software at once. As previously mentioned, software vulnerabilities can cause malware to be installed automatically, without user inputs.
If you frequently encounter redirects to other sites, you should check your web browser for suspicious extensions, as well as the installed program list manually. You can also reset the web browser settings, which would also remove Allwownewz.com notifications from your screen.
Nonetheless, if you do not experience any issues apart from intrusive notifications, you can perform Allwownewz.com removal via the web browser settings.
Google Chrome
- Pick Menu > Settings > Advanced
- Go for Site Settings > Notifications
- In the Allow section, locate the site URL
- Choose More Actions and select Block
Mozilla Firefox:
- Choose Menu > Options
- Select Privacy & Security > Notifications > Settings
- Find the unwanted URL
- Click on the the drop-down menu and select Block
- Save Changes
MS Edge (Chromium)
- Go to Menu > Settings
- Pick Site permissions
- Click Notifications
- Find the unwanted website's address, and select More actions
- Pick Block.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Allwownewz.com. Follow these steps
Uninstall from Windows
To uninstall unwanted applications from Windows systems, please follow these steps:
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
You can get rid of Allwownewz.com notifications by resetting Google Chrome web browser:
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Allwownewz.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting viruses
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Phishing. Wikipedia. The free encyclopedia.
- ^ Frederic Lardinois. Firefox can now block those annoying notification requests. Tech Crunch. Startup and Technology News.
- ^ Wendy Zamora. What are exploits? (And why you should care). Malwarebytes Labs. Security research blog.
