AMMYY (Removal Guide) - Jun 2018 update
AMMYY Removal Guide
What is AMMYY?
Ammyy scam – a possible phone scam that might ask users to install remote access tools for malicious activities
Ammyy scam is an old hoax that targets Windows OS users at least since 2013.[1] Scammers call random people and present themselves as Microsoft specialists. They claim of detecting important issues or infections on their computers and ask to install a remote tool to fix them. Of course, this service is not free. People are asked to pay $200.
| Summary | |
|---|---|
| Name | Ammyy |
| Type | Phone scam |
| Targets | Windows OS users |
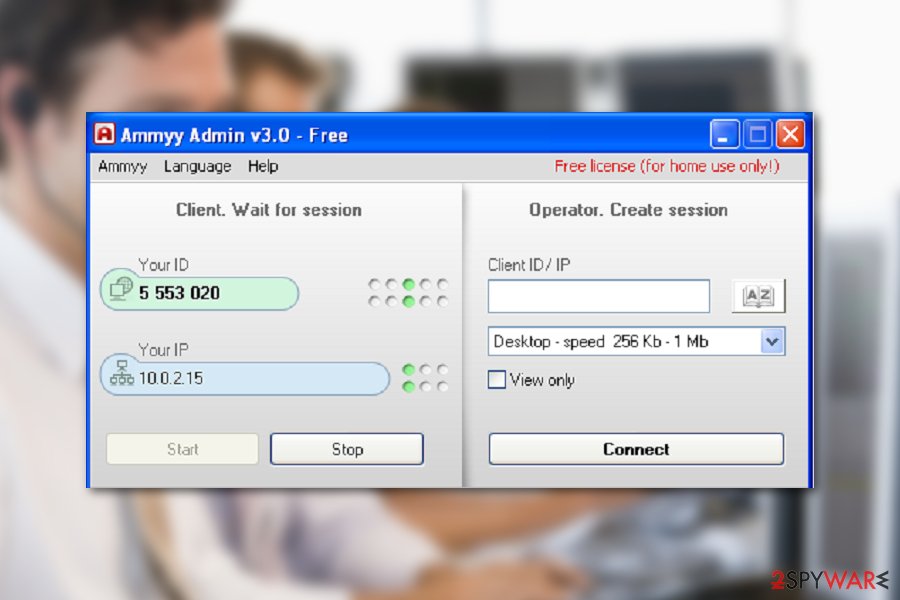
| Operation | Scammers call potential victims and ask to install a remote access tool in order to fix computer-related problems or clean from viruses |
| Used remote access tool | Ammyy Admin |
| The swindled sum of money | Around $200 per victim |
| Elimination | You can uninstall Ammyy as an ordinary program, but it's important to scan the device with antimalware like SpyHunter 5Combo Cleaner to clean possibly installed malware or spyware. To fix PC damage after the virus infection use FortectIntego |
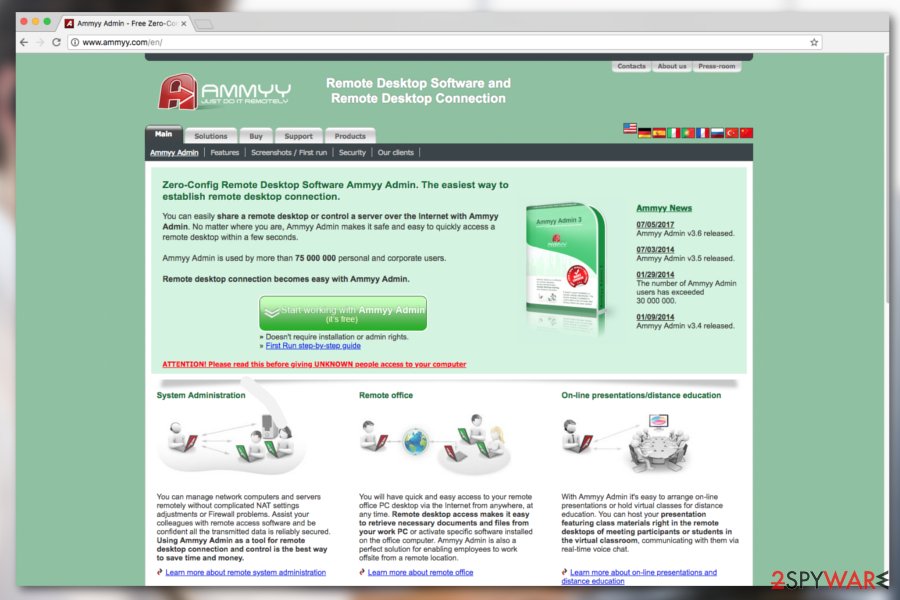
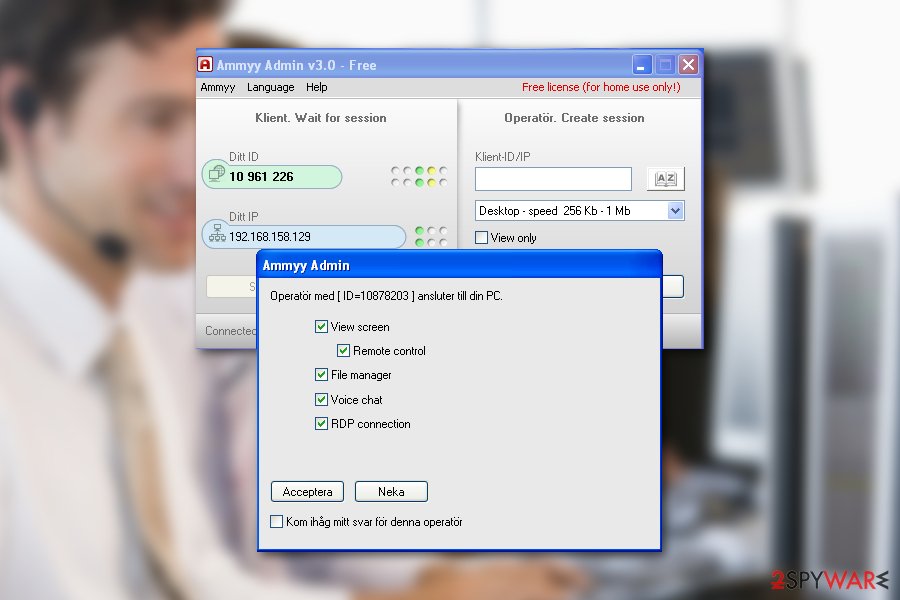
Scammers ask to install Ammyy admin software that allows establishing a remote desktop connection and get access to the victim’s computer. Therefore, the name of the program explains the title of this hoax.
The program is free and is available to download on the official website. We want to point out that this tool itself is not malicious and cannot do the damage. The company is also aware of the issue and warns users to be careful with suspicious phone calls.[2] Attackers can only get access to your device if you let them. In this case, Ammyy removal is a must.
When you give scammers access to your computer via remote access tools, they can do whatever they want. They might install malware, spyware, keyloggers, or delete your files. This activity can lead not only to data loss but emptied bank account or stolen identity too. So, Ammyy admin removal has to be completed immediately.
Ammyy scam fix requires not only uninstalling the program via Control Panel but checking the system for other cyber threats too. The latter task is extremely important if you let scammers access your PC. In this case, we highly recommend scanning the computer with FortectIntego or another anti-malware to make sure that attackers haven’t installed any malware.

The purpose of Ammyy scam – to make people pay for useless service
Researchers from NoVirus.uk assume that Ammyy admin scam is operated from India.[3] Callers usually have a strong Indian accent. Though, an unusual English accent is the first warning sign that you are not talking with Microsoft technicians. Why do they keep calling and report about invented computer problems? The answer is very simple – they seek to scare people into paying $200 for their useless service.
I got scammed by this yesterday. They called saying they were from microsoft and my computer was a host of some nasty viruses and was sending out illegal information(!). I should have known better but they were extremely persuasive, I let them in via the ammyy remote access and they started messing around with things – to show me all the ‘errors’ in my computer.[4]
Usually, scammers try to convince people that they work for Microsoft,[5] scammers start reporting about various PC problems and offer to let them access the system. We highly recommend avoiding such suggestions because by doing so you can easily give attackers the ability to steal your logins, passwords, and other personally identifiable information.
In addition, they may also try to infect your machine with malicious programs, redirect you to malicious sites, and initiate similar issues. Please, keep in mind that Microsoft has never been calling for people in order to ask them to pay for computer repair services. If you were involved in Microsoft Ammy hoax, follow the guide below and prevent additional problems.
The way how scammers reachers potential victims
Differently than regular tech support scams spreading on the web, this hoax does not require downloading any potentially unwanted program (PUP) or clicking a suspicious ad. Scammers usually use random phone numbers and can call anyone all over the world.
Hence, you may receive a call from AMMYY accidentally. Beware that these scammers always do their homework before they start contacting people, so they know who they are calling for. By using public phone directories and other sources, they can not only tell a full victim's name. They may also tell you where you live, your marital status, and other personal details.
We want to remind one more time that Microsoft does not make such phone calls. Thus, you should quit the conversation and block the number if possible. Scammers tend to call the same people again and again in order to reach their goal.
Ammyy scam fix: uninstall remote access program and check the system with anti-malware software
If you become a victim of the cam, you need to act immediately. If you are still talking on the phone with a scammer, hang up immediately. Then disconnect your computer from the Internet and uninstall the program. In order to remove Ammyy from a Windows computer, follow these steps:
- Click Start -> Control Panel -> Programs (or Add/Remove Programs) -> Uninstall a Program.
- Here, look for AMMYY, Ammyy Admin, and other unknown entries, and select Uninstall/Change.
- Follow the guide on screen and click OK to save the changes.
Once you perform these steps, you should immediately download one of these programs and scan the system: FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes. They will not only help you to make sure that your computer is free of malware. They will also help you to find its hidden components and remove them in order to prevent the loss of your personal information.
After Ammyy removal, you should also monitor your banking transactions and inform the bank if you notice any suspicious activities on your account. Additionally, you should change all your passwords. You cannot be sure if the attackers managed to steal credentials or not. Make sure that you set strong and unique passwords for each account.
How to prevent from getting malware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Paul King. Ammyy Admin scam and scammers. The IT Baby. The blog about technology.
- ^ Ammyy Admin - cases of malicious use. Official WARNING. Ammyy. The official website.
- ^ Vayarasa. Vayarasa. Indian cyber security news.
- ^ I fell for the ammyy scam. Malwarebytes forums. The official forum and online community.
- ^ Brandon Vigliarolo. Microsoft: Tech support scams rose by 24% in 2017, costing some victims thousands of dollars. TechRepublic. News, tips, and advice for technology professionals.
