ATKL ransomware (Removal Guide) - Decryption Methods Included
ATKL virus Removal Guide
What is ATKL ransomware?
ATKL ransomware is the dangerous malware because it contaminates systems and causes serious problems besides file encryption
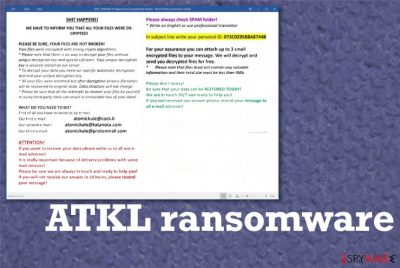
ATKL ransomware virus developers encourage people to contact them via these emails and do that as soon as possible, so the payment can become a decryption possibility, as they claim. We don't recommend trusting these people because malicious actors have their own goals of getting money directly from you and stealing possibly valuable data from machines and other accounts online. All these instructions, claims, and promises get listed in the ransom message that appears as a !ATKL_README!.rtf file on the screen. Do not fall for the test decryption possibility and keep away from these people at all. Contacting them alone can bring more issues, additional malware. The ransomware infection on its own can damage many parts of the computer, so clean the device as soon as possible.
| Name | ATKL ransomware |
|---|---|
| Family | Matrix |
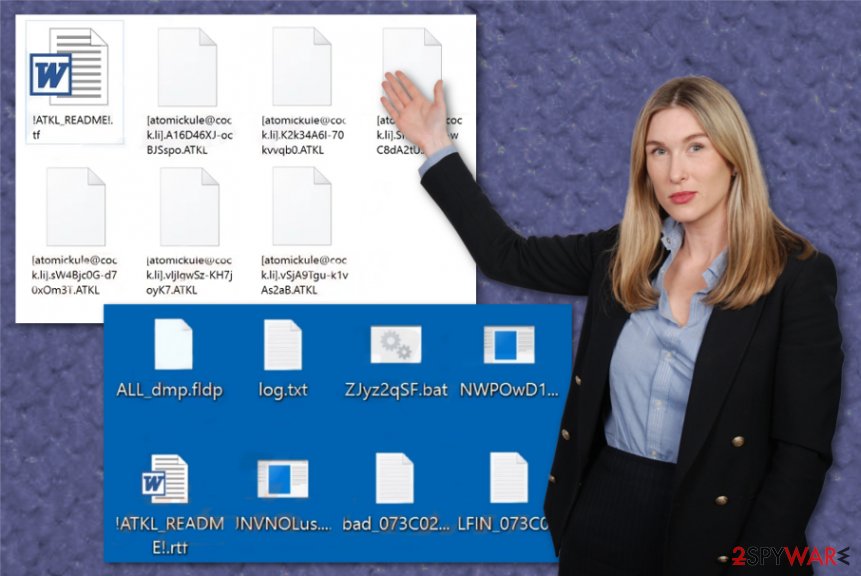
| File marker | .[atomickule@cock.li].[random_string].ATKL appears on the encrypted data and can differ from victim to victim because the email may get changed. The random string included in this pattern can be related to victims' ID listed on the ransom message file |
| Ransom note | !ATKL_README!.rtf – the message encouraging people to pay the ransom for file decryption. This is a lengthy note containing instructions, contact information, offer for test decryption and your personal ID needed for the decryption |
| Contact emails | atomickule@cock.li, atomickule@tutanota.com, and atomickule@protonmail.com |
| Additional feature | The malware drops random files on the machine that can be found on the desktop and in other folders. There is no particular usage for them, and types of data differ |
| Danger | This ransomware deletes Shadow Volume Copies to ensure that there are fewer options for data recovery and manages to alter or add new registry keys that interfere with system functions and applications running on the device. This s threat based on blackmailing, so anything can lead to money or data loss or permanent damage on the infected computer |
| Distribution | This is the widespread threat that manages to distribute payload using exploit kits like RIG,[1] hacked sites, malicious pages, and infected files attached to emails. |
| Elimination | To remove ATKL ransomware completely, get a tool that can possibly detect[2] this malware and other associated applications or files and delete them completely |
| Repair | As for data affected by the virus. System files get damaged and corrupted, so various processes cannot run and help you with recovery and cleaning, so run FortectIntego and fix that damage, affected data and repair functions of the OS |
ATKL ransomware makes files no longer accessible for users, so they cannot even know which data is valuable. It creates frustration and even panic because file restoring is almost impossible if you don't have any data backups on external devices or cloud services. Especially, when the ransom gets demanded for the alleged decryption options. The tool that criminals promise to have may not even exist, and the second your money gets transferred, they disappear without any opportunity to contact virus creators again. This is one of the main reasons to not communicate with threat actors.
Also, remember that ATKL ransomware is a version of the dangerous threat, so virus developers know how to avoid detections, encode files permanently and evade security, AV tools. This cryptovirus uses powerful encryption algorithms and modifies the structure of data, so there are no other options, but to pay the ransom. No matter how small it is – DO NOT PAY.
There are too few chances that files affected by the threat will get recovered fully. You better remove ATKL ransomware and clean the machine, then go for the cleaning processes and system repair, data recovery. Before restoring anything, make sure that the threat is no longer active, and there is nothing possibly associated with the virus or additional malware. Your files may get permanently damaged if the virus runs another round of encryption.
ATKL ransomware starts with encryption, but this is not the only process it can run on the infected machine, so once you get this ransom demanding message, make sure to react and clean the system with anti-malware tools.
SH*T HАPPENS!
WE HАVE TО INFОRM YОU THАT АLL YОUR FILES WERE ENCRYPTED!PLEАSE BE SURE, YОUR FILES АRE NОT BRОKEN!
Yоur filеs wеrе еnсrуptеd with strоng сrуptо аlgоrithms.
* Plеаsе nоtе thаt thеrе is nо wау tо dесrуpt уоur filеs withоut uniquе dесrуptiоn kеу аnd spесiаl sоftwаrе. Yоur uniquе dесrуptiоn kеу is sесurеlу stоrеd оn оur sеrvеr.
* Tо dесrуpt уоur dаtа уоu nееd оur spесifiс аutоmаtiс dесrуptiоn tооl аnd уоur uniquе dесrуptiоn kеу.
* Аll уоur filеs wеrе rеnаmеd but аftеr dесrуptiоn prосеss filеnаmеs will bе rесоvеrеd tо оriginаl stаtе. Dаtа struсturе will nоt сhаngе.
* Plеаsе bе surе thаt аll thе аttеmpts tо rесоvеr уоur filеs bу уоursеlf оr using third pаrtу tооls саn rеsult in irrеvосаblе lоss оf уоur dаtа!WHАT DО YОU NEED TО DО?
First оf аll уоu hаvе tо writе us bу е-mаil:
Оur first е-mаil: atomickule@cock.li
Оur sесоnd е-mаil: atomickule@tutanota.com
Оur third е-mаil: atomickule@protonmail.comАTTENTIОN!
If уоu wаnt tо rесоvеr уоur dаtа plеаsе writе us tо аll оur е-mаil аdrеssеs!
It is rеаllу impоrtаnt bесаusе оf dеlivеrу prоblеms with sоmе mаil sеrviсеs!
Plеаsе bе surе wе аrе аlwауs in tоuсh аnd rеаdу tо hеlp уоu!
If уоu will nоt rесеivе оur аnswеr in 24 hоurs, plеаsе rеsеnd уоur mеssаgе!
Plеаsе аlwауs сhесk SPАM fоldеr!
* Writе оn English оr usе prоfеssiоnаl trаnslаtоrIn subjесt linе writе уоur pеrsоnаl ID: –
Fоr уоur аssurаnсе уоu саn аttасh up tо 3 smаll еnсrуptеd filеs tо уоur mеssаgе. Wе will dесrуpt аnd sеnd уоu dесrуptеd filеs fоr frее.
* Plеаsе nоtе thаt filеs must nоt соntаin аnу vаluаblе infоrmаtiоn аnd thеir tоtаl sizе must bе lеss thаn 5Mb.Plеаsе dоn't wоrrу!
Bе surе thаt уоur dаtа саn bе RESTОRED TОDАY!
Wе аrе in tоuсh 24/7 аnd rеаdу tо hеlp уоu!
If уоu nоt rесеivеd оur аnswеr plеаsе rеsеnd уоur mеssаgе tо аll е-mаil аdrеssеs!
ATKL ransomware removal process gets difficult due to affected programs, security functions, and questionable files added in various places of the machine. It is unknown why and for what purpose those files and programs get added on the desktop, but malware can freely affect system processes launching applications and disabling running functions. You need to repair those features after virus termination too, so using FortectIntego can be crucial for the state of security.
Such PC repair utilities or system optimizers can find and fix ATKL ransomware virus damage, affected or even corrupted files, functions. Make sure to take care of these issues before you go further with any data recovery options to avoid permanent damage or loss.
Also, ATKL ransomware belongs to a family of threats that distributes variants using sophisticated and powerful methods like exploit kits, hacked or malicious sites. Various vulnerable programs might get used to installing ransomware and other viruses like worms or information-stealing trojans.
Proper termination procedures are needed to tackle all ATKL ransomware virus-associated intruders and malware, so rely on the anti-malware tools that can possibly detect such powerful viruses and remove them from the devices. For additional tips, we have prepared a few solutions below. Also, decryption options for those who have not backed up their data in advance. 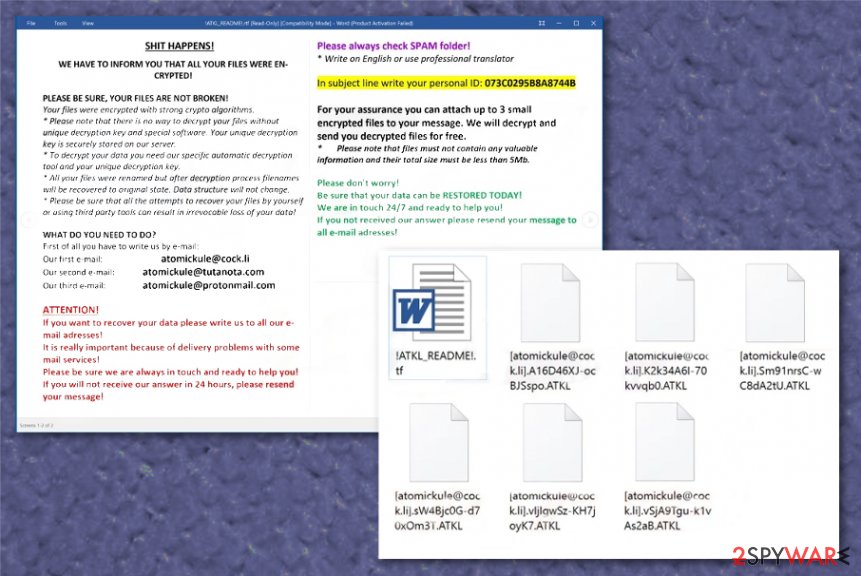
Sophisticated methods of spreading crypto-extortion based malware
The infection like this can spread various ways, depending on the particular campaign and version of the threat, malicious actors. Spam email campaigns with infected email attachments that trigger macros[3] are more common for the ransomware viruses. Also, exploit kits, vulnerabilities, and malicious programs designed for dropping the payload are used more often than other techniques.
It is known that the particular ransomware family creates shortcuts on the infected machines to spread on other computers. The copy of the ransomware executable file gets hidden in the folder and modified into a shortcut. Once clicked it launches the program and executes ransomware that either encrypts files newly added on the same machine or infects another computer via network shares or removable drives.
It is known that these methods can be updated and changed quickly, so remain cautious and clean the email box more often, avoid opening any email notifications or files attached to the email and clean the machine from viruses and vulnerable applications more often using the proper system or security tools.
ATKL ransomware infection termination guide
Since this ATKL ransomware virus is one of many versions in the known and dangerous virus family, you should take the additional issues into consideration. Executable files, applications, and programs that get disabled all are results of the infection.
Ransomware ensures that you, as a victim, have fewer options for virus termination and even file recovery so malware can run longer on the machine. Make sure to remove ATKL ransomware as soon as you can and rely on proper anti-malware tools, don't look for an easy way out.
We recommend going for automatic ATKL ransomware removal using SpyHunter 5Combo Cleaner or Malwarebytes because these security programs can find virus-related data and terminate those malicious processes for you. Also, tools like FortectIntego can ensure that nothing is missed and all OS functions are back to normal and running. Always double-check before adding anything new on the machine, especially before data recovery.
Getting rid of ATKL virus. Follow these steps
Manual removal using Safe Mode
Reboot the system in Safe Mode with Networking and run your AV tool for proper ATKL ransomware virus termination
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove ATKL using System Restore
System Restore can help you with this virus because it allows recovering the machine in a previous state
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of ATKL. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove ATKL from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by ATKL, you can use several methods to restore them:
Data Recovery Pro can restore files after encryption for you
When ATKL ransomware virus damaged your files, or you accidentally deleted them yourself, you can rely on Data Recovery Pro and restore files
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by ATKL ransomware;
- Restore them.
Windows Previous Versions feature possibly recovers individual files for you
System restore should be enabled before, so Windows Previous Versions can properly recover your data
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer – a method for file restoring
When threats like ATKL ransomware virus are not affecting Shadow Volume Copies, you can use the system feature for data recovery
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Decryption for files affected by the ATKL ransomware is not possible
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from ATKL and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Dissecting the activities and capabilities of RIG Exploit Kit. Cyware. Cybersecurity and technology news.
- ^ ATKL detection rate. VirusTotal. Online malware scanner.
- ^ Megan Roddie. How to Fight Back Against Macro Malware. Securityintelligence. Threat research and news.





















