Blowislandnext.top ads (spam) - Free Instructions
Blowislandnext.top ads Removal Guide
What is Blowislandnext.top ads?
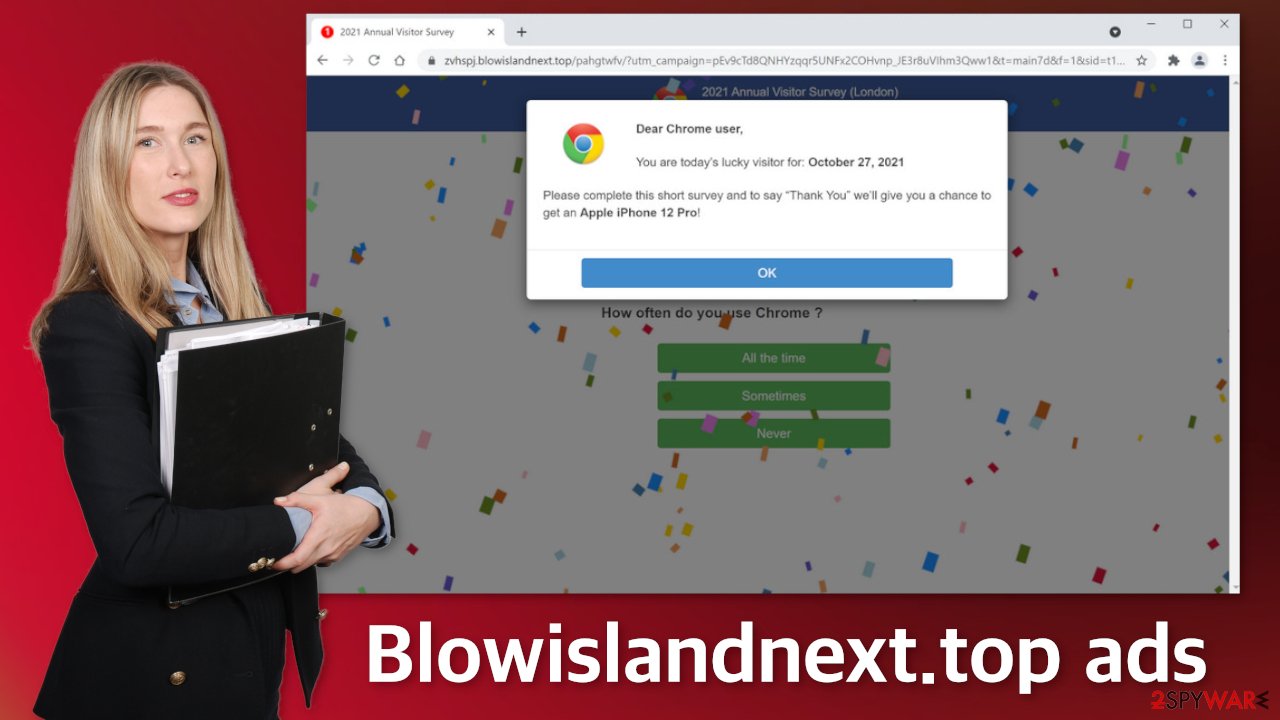
Blowislandnext.top makes visitors think they have a chance to win a new phone
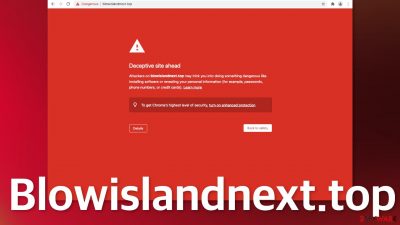
Blowislandnext.top is already marked by Google as a deceptive site. It uses Google Chrome as bait to lure users in. People are told that if they complete some kind of survey, they will have a chance to win a new Apple iPhone 12 Pro. What the page is probably trying to achieve is to get users to subscribe to push notifications or collect their personal information. If you provide your information to shady sources that may even lead to financial losses or identity theft. You could also be fooled into downloading PUPs (potentially unwanted programs) or malware.
Push notifications are pop-ups that appear in the corner of the screen, and if you are receiving them from this site, they can also be unsafe. Links embedded in the notification prompts can also lead to questionable sites as the creators of this page do not care about user security or privacy. They can generate revenue from every link you click on,[1] so they do not filter what ads you receive.
| NAME | Blowislandnext.top |
| TYPE | Push notification spam; adware |
| SYMPTOMS | Pop-up ads start appearing in the corner of the screen; how often the ads show up depends on the settings that the creators have configured |
| DISTRIBUTION | Shady websites, deceptive ads, redirects, freeware installations |
| DANGERS | Links embedded in the notification prompts can lead to dangerous websites where users can be tricked into providing their personal information or downloading PUAs and malware |
| ELIMINATION | Block push notifications in your browser settings; additional removal methods are included in the blog |
| FURTHER STEPS | Use a maintenance tool FortectIntego to try to fix any remaining damage to your system and optimize it |
Survey scams are still spread around the Internet
Usually, pages like this are not found in the search results. They are promoted on other shady sites that are full of deceptive ads and redirects. You should not ignore security expert advice and click on random links on the Internet or browse through websites that engage in illegal activities because often they are unregulated.
The developers of such sites often use well-known companies to gain users' trust. In this case, Google Chrome is used to make the scam look more legitimate. The name of the page displayed is “2021 Annual Visitor Survey” which also makes the page seem more real. This is what the full message in the pop-up says:
Dear Chrome user,
You are today's lucky visitor for: October 27, 2021
Please complete this short survey and to say “Thank You” we'll give you a chance to get an Apple iPhone 12 Pro!
This can give a rush of adrenaline and a lot of emotions that make people act without thinking. Social engineering techniques[2] are used exactly for this reason. As we always say – if it seems too good to be true, it probably is. Although such scams are not as common as in the early days of the Internet, you can still encounter them if you browse through pages you probably should not. We wrote about a couple of pages that use similar methods – You've made the 9.68-billionth search, 2018 Annual Visitor Survey, and Amazon Membership Rewards.
Other types of schemes include scareware or fake software updates. Scareware is a type of scam that says that your system is infected and in danger, so you need to install a tool that will get rid of it. The site also uses clever tactics to make the message seem legitimate. You might see that your IP and location are “exposed”. You should know that every website is able to see this information so it would be able to provide good services.
Stop the intrusive pop-up ads
Push notifications are based on a subscription model, so users can go to their settings and block them anytime. If you do not know how, this is how you do it:
Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate Privacy and security section and pick Site Settings > Notifications.
![Stop notifications on Chrome PC 1 Stop notifications on Chrome PC 1]()
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
![Stop notifications on Mozilla Firefox 1 Stop notifications on Mozilla Firefox 1]()
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
MS Edge:
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.
![Stop notifications on Edge 1 Stop notifications on Edge 1]()
- Toggle the switch to the left to turn notifications off on Microsoft Edge.
MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
Internet Explorer:
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
- Locate web address in question under Allowed sites and pick Remove.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
Perform a scan to make sure your system is safe
After an encounter with such a website, you could have installed a PUP by accident, so we recommend using professional security tools like SpyHunter 5Combo Cleaner or Malwarebytes to scan your system and remove them if you find any. These types of programs can perform various processes in the background without your knowledge. Adware[3] can generate ads on your machine, like banners, surveys, pop-ups and redirects.
They could be disguised as handy tools, so manual removal can be difficult to achieve. The program could have any name and icon. You can also remove virus damage with FortectIntego. This repair tool can clear your browsers, fix corrupted files, system errors, registry issues, etc.
If you want to try to perform manual removal, you can follow the instructions posted below for Windows and Mac systems:
Windows 10/8:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Windows 7/XP:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.
![Uninstall from Windows 7/XP Uninstall from Windows 7/XP]()
- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Mac:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Pay-per-click. Wikipedia. The Free Encyclopedia.
- ^ What is Social Engineering?. Webroot. Cybersecurity Resources.
- ^ Adware. Malwarebytes. Types of Cybersecurity Threats.













