CapitalProjectSearch Mac virus (Free Guide)
CapitalProjectSearch Mac virus Removal Guide
What is CapitalProjectSearch Mac virus?
CapitalProjectSearch is a dangerous computer virus that can install additional malicious components without asking
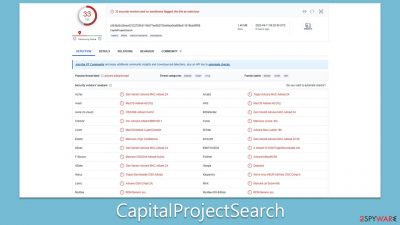
CapitalProjectSearch Mac virus is a malicious application that is part of the Adload malware family and is designed to hijack web browsers on Mac systems. It spreads through deceptive methods such as pirated software installers and fake Flash Player updates, which are unfortunately effective in infecting hundreds of users every day.
Once installed, the CapitalProjectSearch virus can expose users to insecure online content, including phishing messages, fake giveaways, and get-rich-quick schemes. Users may also experience constant harassment from pop-ups, auto-play videos, banners, and other ads while browsing the web through hijacked browsers such as Safari, Chrome, or Firefox.
If you have noticed that CapitalProjectSearch has infiltrated your device, you should take appropriate steps to remove it, and we explain how to do just that below. We also provide additional information about the malware family and how to avoid getting infected in the future.
| Name | CapitalProjectSearch |
| Type | Mac virus, adware, browser hijacker |
| Malware family | Adload |
| Distribution | Third-party websites distributing pirated software, software bundles, fake Flash Player updates |
| Symptoms | A new extension is installed on the browser, along with an application of the same name; search and browsing settings altered to an alternative search provider; new profiles and login items are set up on the account; intrusive ads and redirects |
| Removal | The easiest way to remove Mac malware is to perform a full system scan with SpyHunter 5Combo Cleaner security software. We also provide a manual guide below |
| System optimization | By cleaning web browser caches and web data, you would ensure that third parties can no longer track you – use FortectIntego for this task |
Adload malware is prevalent among Mac users
The Adload malware family is one of many aggressive adware strains that frequently infect Mac systems. Macs, although traditionally believed to be less susceptible to more dangerous types of malware like ransomware and rootkits, have seen a significant increase in adware targeting due to their growing popularity. In fact, adware targeting Macs, on average, tends to be more aggressive compared to that targeting Windows.
Adload is known for its distinctive magnifying glass icon, usually on a blue, teal, green, or gray background. Once installed, it changes browser settings in various ways, depending on the version of the virus. This can include changing the homepage to insecure pages, rerouting traffic, assigning alternative search providers, and displaying intrusive ads at the top of search results and elsewhere.
CapitalProjectSearch is one such version of Adload that poses a particularly challenging threat. It uses AppleScript to bypass Apple's built-in defenses, allowing it to install extensions with elevated permissions and harvest sensitive information such as credit card details and account passwords. This puts users' privacy and computer security at risk, making it crucial to promptly remove the infection and avoid entering personal information while the virus is active.
Given the aggressive nature of Adload and its variants, including CapitalProjectSearch, it is important for Mac users to take proactive measures to protect their systems, such as using reputable antivirus software, being cautious while downloading software or updates from untrusted sources, and promptly addressing any signs of adware infection to ensure the security of their Mac systems.
Removal of CapitalProjectSearch malware
Removing regular applications from a Mac is typically straightforward – just move them to Trash, and there are usually no remnants or issues left behind. However, when it comes to computer infections like Adload and its variants, the story is entirely different. These infections are intentionally designed to be difficult to remove, as the longer they stay on users' machines, the more lucrative it can be for cybercriminals.
Given the potential damage caused by Adload malware and its persistence, it is crucial to remove it as soon as possible. However, simple methods may not be enough due to the stubborn nature of Adload. Therefore, we highly recommend using reputable security software SpyHunter 5Combo Cleaner or Malwarebytes for its removal. Keeping your security software up-to-date and performing a full system scan can effectively detect and remove the Adload infection.
If you prefer to attempt manual removal steps, we provide the necessary information below. However, it's important to note that regardless of the removal method you choose, it's advisable to clean your affected browser caches, such as Safari or others, to ensure the complete removal of any remnants left behind by the malware.
Manual removal steps of the main app
It's not unusual for malware to utilize background processes to carry out its intended actions as designed by its creators. Therefore, before proceeding with the removal of the main malware application, it's important to check if these background processes are active and could potentially hinder your removal efforts. To do so, you can access the Activity Monitor on your Mac and shut down these processes using the following steps:
- Open the Applications folder and go to Utilities
- Double-click the Activity Monitor and shut down all the suspicious processes.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
![Uninstall from Mac 1 Uninstall from Mac 1]()
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
Your next task is to remove all the virus-related Login items and new Profiles that could be used by it.
- Go to Preferences and pick Accounts
- Click Login items and delete everything suspicious
- Next, pick System Preferences > Users & Groups
- Find Profiles and remove unwanted profiles from the list.
Small configuration files known as PLIST can hold various settings information. They might prevent the virus from being removed properly.
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and delete all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
Removing the malicious extensions and cached files
To ensure that third parties stop tracking you after removing adware from your device, it's crucial to clear cookies and other trackers from your browser. These items can linger on your system even after adware is removed, allowing continued tracking by third parties. The easiest and most effective way to accomplish this is by using a reliable maintenance tool FortectIntego. However, if you prefer manual methods, you can also do it manually.
If you have not yet deleted the browser extension (if using manual removal), it's important to do so first. Once the adware is removed, clearing cookies and other trackers from your browser will help protect your privacy and prevent further tracking by third parties.
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Clear cookies and other web data from your browsers:
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
In some cases, resetting the browser is the best choice once all adware is deleted from your Mac:
Safari
- Click Safari > Preferences…
- Go to the Advanced tab.
- Tick the Show Develop menu in the menu bar.
- From the menu bar, click Develop, and then select Empty Caches.
![Reset Safari Reset Safari]()
Google Chrome
- Click on Menu and select Settings.
- In Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.
![Reset Chrome 2 Reset Chrome 2]()
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.








