CARLOS ransomware (Tutorial) - Virus Removal Guide
CARLOS virus Removal Guide
What is CARLOS ransomware?
CARLOS ransomware is a damaging cyber threat existing in the cybersphere since the start of February 2020
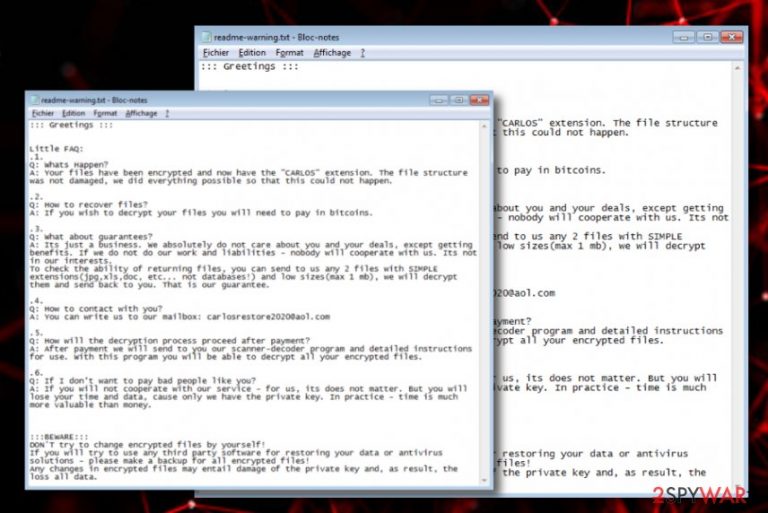
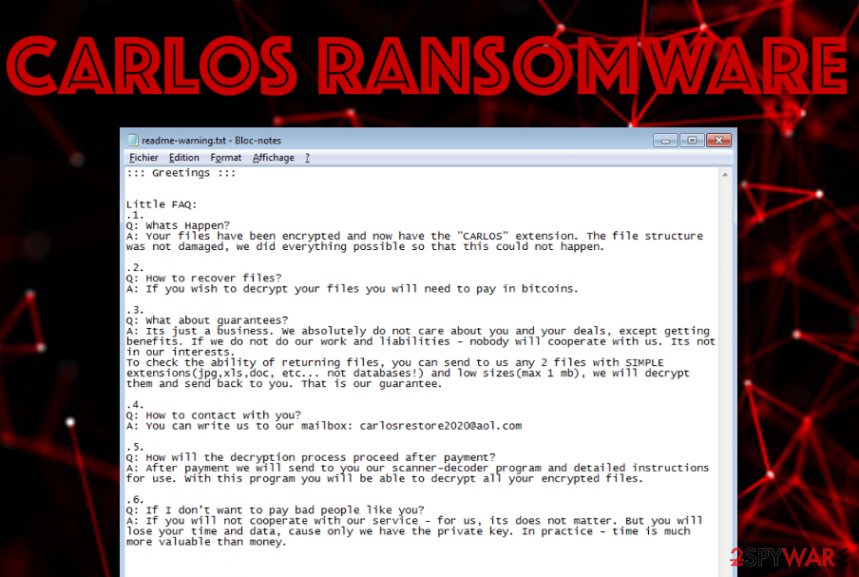
CARLOS ransomware, found by S!Ri[1] in the first half of February, is a complex computer virus that is in the search for encryptable files. The malware developers are seeking to collect monetary income from their victims. First of all, the ransomware virus employs a symmetric or asymmetric encryption cipher and runs it on all components found. This can include images, word documents, audio, video, and other files. When the encryption is finished, CARLOS ransomware drops a ransom note named readme-warning.txt that is written in a Notepad blank. The users are introduced to what has just happened and how to deal with it.
Crooks state that they absolutely do not care about the users (that is true) because it is only a business and they will get their decrypted files back after the payment anyway (not always true). However, CARLOS ransomware developers try to provide some type of evidence of the existing decryption software by allowing the victims to send 2 files that include simple extensions such as .jpg, .xls, or .doc. For cooperation, these people include the carlosrestore2020@aol.com email address where both parties have to talk about the conditions of the payment. Afterward, crooks claim that they will deliver detailed instructions on how to use the decryption software.
Once all of the existing files and documents are locked by CARLOS ransomware it appends an extension that is completed from three parts to all the filenames of encrypted data. The malware appends a random mix of 7 symbols that can be letters or numbers, crooks' given email address, and the extension – .CARLOS. For example, if you had a file that was named database.xls, after the encryption, it would turn to database.xls.[GY67HU8].[carlosrestore2020@aol.com].CARLOS.
| Name | CARLOS ransomware |
|---|---|
| Type | Ransomware/malware |
| Discoverer | S!Ri |
| Extension | This ransomware virus appends a long extension that contains three parts: a random mix of 7 symbols that are letters and numbers, crooks' email address, and the appendix – .CARLOS |
| Ransom note | The ransomware message provides a text note written in a Notepad blank that is named readme-warning.txt. Here crooks introduce the victims to what has just happened and provide the users with a demand to pay some type of price for receiving decryption software |
| Criminals' email | Crooks include the carlosrestore2020@aol.com email address into the ransom message as a way to make contact |
| Spreading | The ransomware-related payload can get distributed through email spam messages and their malicious attachments, software cracks, exploited OS flaws, vulnerable RDP configuration, etc. |
| Removal | You should get rid of the parasite as soon as you spot the first symptoms of infection. Perform the removal with the help of a trustworthy antimalware program |
| Data recovery | If you are looking for a way to recover your locked files, you should go to the end of this article and take a look at all of the possibilities that are written there |
| Fix tool | If you have discovered any damage in your computer system, try performing a fixing process with the help of FortectIntego |
CARLOS virus is categorized as dangerous and complex malware as it can make a person completely use his files and experience other harmful malware infiltration. Email spam campaigns, cracked software, exploiting OS flaws, and vulnerable RDP configuration create the best conditions for this cyber threat to spread. The potential victims can receive the malicious payload looking like a legitimate file at first and notice that something is wrong just when it is too late.
CARLOS ransomware aims to alter the Windows Registry by adding suspicious keys into it that allow the malware to bring on its malicious module. Also, it performs changes on the Windows Task Manager by injecting malicious processes in order to launch its payload too. Sometimes the included executables might not create any concern as they can come looking as completely normal components of some type of legitimate software.
Furthermore, CARLOS ransomware might disable antivirus programs once it settles on the Windows PC. If this happens, some tools might not be able to detect or remove the malicious software. However, according to VirusTotal,[2] 45 AV engines do spot this malware and provide it as suspicious, malicious, malware, trojan, or ransomware. These types of results are kind of good considering the fact that 45 is out of the total 71 which is more than half.
Additionally, CARLOS ransomware will ensure that its module is launched every time when the computer is booted. This can include scanning the system for encryptable documents once in a while. The threat uses unique encryption keys to lock up all the files that are found on the computer. Afterward, criminals store both encryption and decryption tools on remote servers that are accessible only for their owners.
The ransom note that is provided by CARLOS ransomware will also try to convince you to pay the ransom price. Even though there are no particular demands provided in that message, criminals can ask anywhere from $50 to $2000 or even more if they are very greedy. However, in most of the cases, they urge for Bitcoin or another type of cryptocurrency for the payment to stay anonymous. Here, take a look at the full ransom message:
::: Greetings :::
Little FAQ:
.1.
Q: Whats Happen?
A: Your files have been encrypted and now have the “CARLOS” extension. The file structure was not damaged, we did everything possible so that this could not happen..2.
Q: How to recover files?
A: If you wish to decrypt your files you will need to pay in bitcoins..3.
Q: What about guarantees?
A: Its just a business. We absolutely do not care about you and your deals, except getting benefits. If we do not do our work and liabilities – nobody will cooperate with us. Its not in our interests.
To check the ability of returning files, you can send to us any 2 files with SIMPLE extensions(jpg,xls,doc, etc… not databases!) and low sizes(max 1 mb), we will decrypt them and send back to you. That is our guarantee..4.
Q: How to contact with you?
A: You can write us to our mailbox: carlosrestore2020@aol.com.5.
Q: How will the decryption process proceed after payment?
A: After payment we will send to you our scanner-decoder program and detailed instructions for use. With this program you will be able to decrypt all your encrypted files..6.
Q: If I don't want to pay bad people like you?
A: If you will not cooperate with our service – for us, its does not matter. But you will lose your time and data, cause only we have the private key. In practice – time is much more valuable than money.:::BEWARE:::
DON'T try to change encrypted files by yourself!
If you will try to use any third party software for restoring your data or antivirus solutions – please make a backup for all encrypted files!
Any changes in encrypted files may entail damage of the private key and, as result, the loss all data.
A piece of advice would be to stay away from contacting CARLOS ransomware developers. As these people already mentioned, they do not care about the victims as they are orientated toward their own business. When you proceed with the payment and it reaches the crooks, you can get scammed. Simply, hackers might provide you with a fake tool or just take the money and leave you with no decryption software at all.
It might be hard to understand that your files can get permanently lost, but there are always some alternatives that you can try. First, focus on CARLOS ransomware removal that you need to complete as soon as you see encrypted files and the provided ransom note. You should use reliable antimalware software that will scan your system fully and get rid of all malware-laden components that were brought to your computer.
However, if you are having trouble with the elimination or if the virus is blocking your anti-spyware program, you should run your machine in Safe Mode with Networking or activate the System Restore feature that could help you to fix things. When you successfully remove CARLOS ransomware from your Windows computer and the malware is no longer causing any problems, go to the end of this article and there you will find some data recovery tips.
Beware that CARLOS ransomware might have deleted your Shadow Volume Copies of the encrypted software, so a particular tool that requires the Shadow Copies to remain safe might not work. Also, if the virus managed to damage your Windows hosts file in order to prevent you from visiting security-related sources, you should delete this file while eliminating the ransomware virus, otherwise, the access will remain blocked.
Exploited OS vulnerabilities distribute ransomware
This ransomware can have different types of distribution sources. However, experts have discovered that the ransomware virus is widely distributed by misusing operating system flaws. This includes products such as Microsoft Office, web browsers, the operating system itself, and other third-party applications.
Furthermore, crooks' can pretend to be from reliable shipping companies and decide to spam you with fake order delivery or shipping information notifications. It can look like the message is coming from a reputable source but it truly is not. Do not open any attached files or documents before scanning them with antimalware software. In addition, ransomware can get distributed through other sources such as:
- Cracked software. These products appear on p2p networks such as The Pirate Bay, eMule, and BitTorrent.
- Vulnerable RDP.[3] If the configuration does not include a reliable password or includes none security codes at all, the hackers can easily access the port.
- Malvertising ads. If you are a frequent visitor of third-party networks and like clicking on various advertisements, there is a risk to get infected with malware.
According to cybersecurity experts from Virusai.lt,[4] all computer systems need to include reliable antimalware protection. The more the security features the anti-spyware has, the better it is for the device. Also, do not forget to update the product regularly, otherwise, it cannot be able to operate properly and might include flaws.
CARLOS ransomware deletion steps and data recovery alternatives
We have introduced you to all the unwanted effects that ransomware infections can bring, and now it is time for you to get rid of the cyber threat before more damage appears. You should remove CARLOS ransomware with the help of anti-spyware software and avoid trying manual steps because this type of process can relate in making dangerous mistakes.
If you are having trouble with CARLOS ransomware removal, try booting your computer in Safe Mode with Networking or activating the System Restore feature to diminish all malicious activities. When you get rid of the malware, scan your system with SpyHunter 5Combo Cleaner or Malwarebytes to find if there is any damage. If you discover any altered components, try repairing them with FortectIntego. Also, below you will find some data recovery alternatives that might be helpful for restoring your files.
Getting rid of CARLOS virus. Follow these steps
Manual removal using Safe Mode
To deactivate malicious changes on your Windows computer and bring the system back to normal, you should boot the machine in Safe Mode with Networking like shown in the following instructions.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove CARLOS using System Restore
To diminish all malware-laden activities and deactivate the ransomware virus itself, you should reboot your device via System Restore. The below-provided steps should help you succeed in such a task.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of CARLOS. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove CARLOS from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by CARLOS, you can use several methods to restore them:
Try employing Data Recovery Pro for file restoring.
If the ransomware virus has locked your files and documents, you can try restoring them with this piece of software.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by CARLOS ransomware;
- Restore them.
Windows Previous Versions feature might allow you to recover some files.
If you have booted the computer in System Restore in the past, this method might help you to bring some files back.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Shadow Explorer software might work for your files.
If the ransomware virus did not permanently destroy or erase the Shadow Volume Copies of your encrypted files, try using this technique for the recovery process.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
The .CARLOS files decrypter is not available yet.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from CARLOS and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ S!Ri. .CARLOS #ransomware. Twitter. Social Platform.
- ^ 45 engines detected this file. Virus Total. Detections.
- ^ Remote Desktop Protocol. Wikipedia. The free encyclopedia.
- ^ Virusai.lt. Virusai. Security and spyware news.







