Paymen45 ransomware (Virus Removal Guide) - Free Instructions
Paymen45 virus Removal Guide
What is Paymen45 ransomware?
Paymen45 ransomware is the dangerous much-evolving crypto-extortion threat
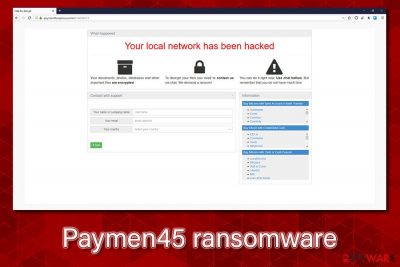
Paymen45 ransomware is a data locking virus that stems from Oled/Makop malware strains. It was first identified in late April 2020, when multiple users started to complain about the infection, which prevents them from opening pictures, music, documents, databases, and other files located on local or networked/NAS devices. Soon after the infiltration, the Paymen45 virus uses a combination of AES and RSA encryption algorithms to lock files and appends a randomized extension to each. Currently, there are two different versions identified by the researchers: g8R4rqWIp9 and KJHslgjkjdfg.
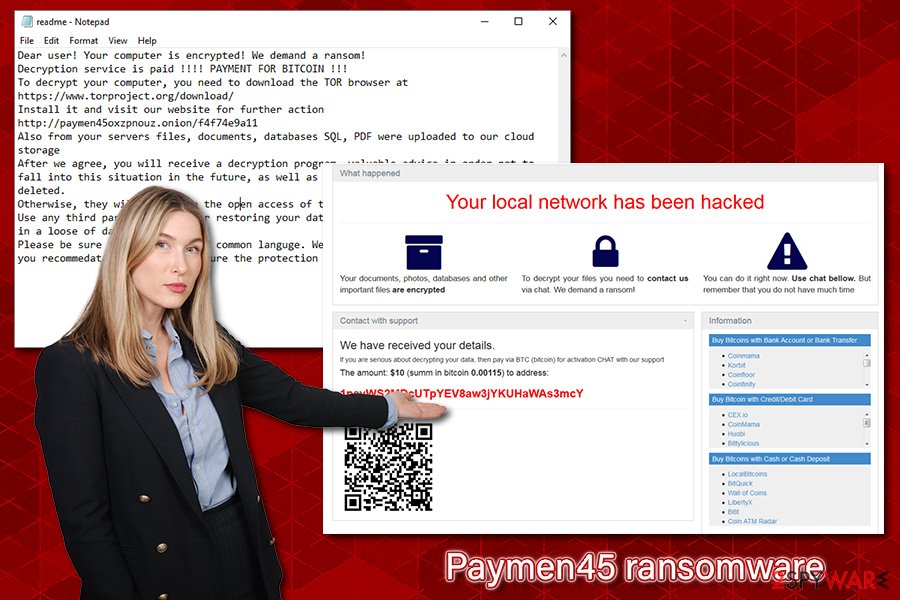
After encrypting data, Paymen45 ransomware also drops a ransom note readme.txt or readme-warning.txt (depending on the version), which explains what happened to users' files and asks them to download a Tor web browser in order to be able to visit a dark web onion webpage. Users are asked to provide the personal ID, and then they are provided with a personal ransom size, which can be as low as $10 in some cases. Threat actors behind this ransomware also threaten to publicly disclose the stolen files if the ransom is not paid.
| Name | Paymen45 ransomware |
| Type | File locking malware, cryptovirus |
| Origination | The malware is a new variant of Oled and Makop ransomware |
| Distribution | Malicious actors can use a variety of methods to deliver the threat to users, e.g., spam email attachments/hyperlinks, fake updates, exploits, software vulnerabilities, weakly protected RDP connections, brute-force attacks, software cracks, and other attack vectors |
| Related | lok.exe, paymen45oxzpnouz.onion |
| Encryption algorithm | The attacks use AES + RSA to encrypt all non-system and non-executable files on the local and networked drives |
| Ransom note | readme.txt or readme-warning.txt is dropped on the desktop, as well as other places on the machine |
| File extensions | This family uses a randomized 10 character file extension which is appended at the back of the file name: .g8R4rqWIp9 or KJHslgjkjdfg. Examples of encrypted files: picture.jpg.g8R4rqWIp9, document.doc.KJHslgjkjdfg |
| Data recovery | Since the cryptovirus uses sophisticated encryption algorithms, recovering data without paying criminals or restoring it from backups is almost impossible. However, in some cases, users might be able to restore at least some data with the help of third-party tools – we provide the instructions below |
| Removal | Before removing the virus from the computer, users who do not have backups should make a copy of all encrypted files and only then use anti-malware software to eliminate the infection safely (note: it will NOT recover your files) |
| System fix | Make use of PC repair software such as FortectIntego if you want to avoid reinstallation of the entire Windows system |
Since Paymen45 ransomware belongs to a relatively new malware strain, there are no clear indications of what methods the attackers sue for its propagation. While some ransomware families, such as the notorious Djvu, use a single attack vector, most cybercriminals resort to multiple techniques when it comes to malicious payload delivery.
Thus, the ransomware might be delivered in one (or multiple) of the following ways:
- Spam email attachments or embedded hyperlinks;
- Fake updates or scam websites;
- Drive-by downloads and software vulnerabilities;[1]
- Brute-forcing combined with weakly protected RDP (Remote Desktop) attacks;
- Illegal program installers and software cracks;
- Etc.
Most of these techniques can usually be prevented by using security software and other precautionary measures – you can find more tips in our article below. As for now, you should focus on ransomware virus removal and data recovery. Do not try to restore data without cleaning the machine beforehand. It can affect the recovery and even damage your data significantly.
Before performing data encryption, Paymen45 ransomware firs needs to prepare the system for the process. Thus, the malware modifies the Windows registry database by setting new keys for persistence, creates new processes that help malware function during the infection, starts a new service, deletes Shadow Volume Copies to prevent easy data recover, etc.
Once the preparations are complete, Paymen45 ransomware begins the data encryption task. In most cases, users do not notice how the process is performed, and only realize that something odd happened after they try to open a personal file or see a ransom note. Malware targets most common file types, such as .pdf, .sql, .doc, .rar, .jpg, and many others. After the process, each of the files receives one of the following extensions: g8R4rqWIp9, KJHslgjkjdfg, or another randomized string.
After data is locked, users can see a ransom message from the attackers, which states:
Dear user! Your computer is encrypted! We demand a ransom!
Decryption service is paid !!!! PAYMENT FOR BITCOIN !!!
To decrypt your computer, you need to download the TOR browser at https://www.torproject.org/download/
Install it and visit our website for further action http://paymen45oxzpnouz.onion/f4f74e9a11
Also from your servers files, documents, databases SQL, PDF were uploaded to our cloud storage
After we agree, you will receive a decryption program, valuable advice in order not to fall into this situation in the future, as well as all your files on our server will be deleted.
Otherwise, they will fall into the open access of the Internet!
Use any third party software for restoring your data or antivirus solutions will result in a loose of data.
Please be sure that we will find common languge. We will restore all the data and give you recommedations how to configure the protection of your server.
Paying cybercriminals is not recommended, as they might not contact you after the payment. We suggest not paying the attackers unless it is an absolute last choice and none of the alternative methods we provide below work for you. Note that you should make a copy of your hard drive, including the registry database and the encrypted files (unless you have backups – then you can remove the ransomware as soon as possible).
To eliminate the malware, use powerful security tools, such as SpyHunter 5Combo Cleaner or Malwarebytes. Nevertheless, some file locking viruses eliminate themselves after encrypting files, so your anti-malware may not find anything if that is the case. However, keep in mind that other malicious software might have been installed along with Paymen45 ransomware, so a scan is a mandatory process. After you are sure that the infection is gone, you can also use FortectIntego to remediate Windows computer and fix virus damage.
Known Paymen45 ransomware versions
While first sightings of Paymen45 virus were spotted on April 30, two different versions have been released within the first two weeks of its operation – g8R4rqWIp9, and KJHslgjkjdfg. The naming is based on the file extension that is generated to encrypt data, although researchers believe that the string is random and can consist of 10 randomly-generated alphanumeric characters.
g8R4rqWIp9 ransomware
Once inside the system, g8R4rqWIp9 ransomware performs several changes to the Windows system and encrypts all data on local and networked drives. This way, PDF files, MS Office documents, databases, and other files are appended with .g8R4rqWIp9 extension, and can no longer be accessed. Once that is complete, users are asked in readme.txt file to download the Tor browser and visit the http://paymen45oxzpnouz.onion/ address for further communication. In some cases, users were also provided a contact address – repairhost1@protonmail.com email.
We do not recommend contacting or paying g8R4rqWIp9 ransomware authors, and instead of performing g8R4rqWIp9 virus removal with anti-malware, and then using alternative methods for data recovery.
KJHslgjkjdfg ransomware
KJHslgjkjdfg ransomware showed up just a week later after the initial Paymen45 release. Users reported that all their personal files were appended with .KJHslgjkjdfg file extension and even NAS backups were encrypted as well. In other words, if malware manages to penetrate a company, it will most likely to encrypt all servers and machines connected to the same network. If that is the case, each of the infected computers and other devices should be immediately isolated from the network.
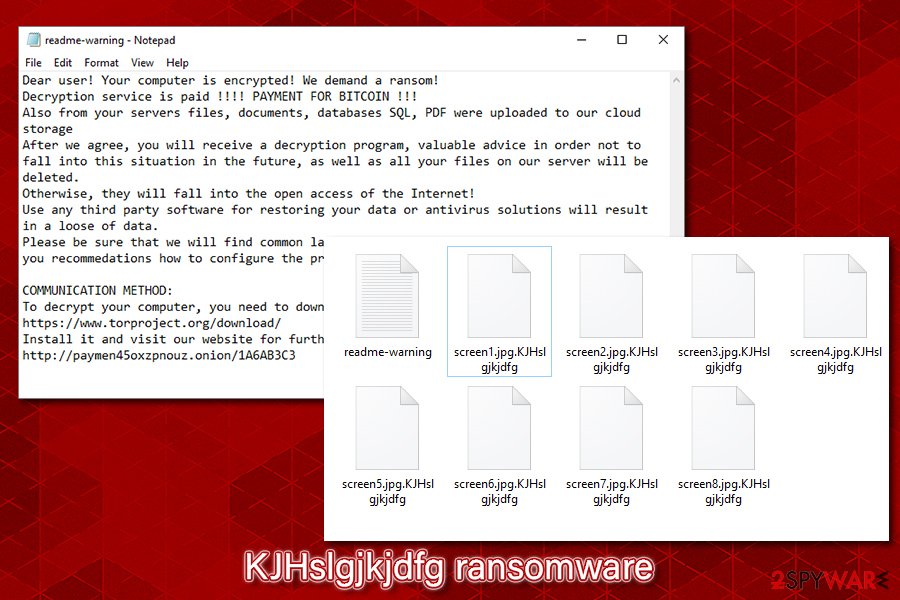
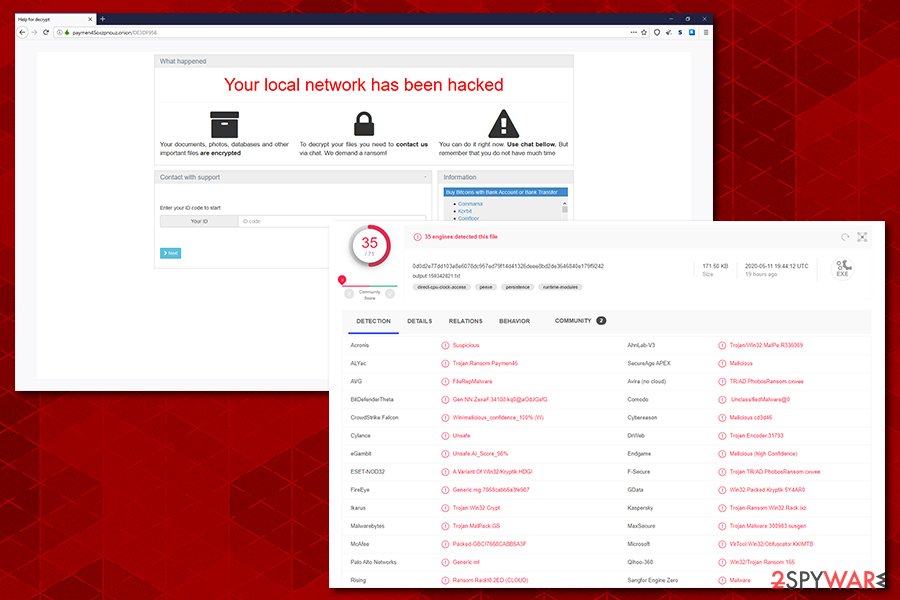
One of the malware samples analyzed by researchers was an output.159342821.txt file, which is highly likely to trigger the infection. It is detected by various security solutions under the following names:[2]
- Gen:NN.ZexaF.34108.kq0@aOdJGsfG
- Trojan.Encoder.31793
- Win32.Packed.Kryptik.5Y4AR0
- VirTool:Win32/Obfuscator.KK!MTB
- Packed-GBC!7668CABB5A3F
- Trojan.MalPack.GS, etc.
Also, KJHslgjkjdfg ransomware is using a different ransom note – readme-warning.txt, contents of which slightly vary from the initial version:
Dear user! Your computer is encrypted! We demand a ransom!
Decryption service is paid !!!! PAYMENT FOR BITCOIN !!!
Also from your servers files, documents, databases SQL, PDF were uploaded to our cloud storage
After we agree, you will receive a decryption program, valuable advice in order not to fall into this situation in the future, as well as all your files on our server will be deleted.
Otherwise, they will fall into the open access of the Internet!
Use any third party software for restoring your data or antivirus solutions will result in a loose of data.
Please be sure that we will find common languge. We will restore all the data and give you recommedations how to configure the protection of your server.COMMUNICATION METHOD:
To decrypt your computer, you need to download the TOR browser at https://www.torproject.org/download/
Install it and visit our website for further action http://paymen45oxzpnouz.onion/1A6AB3C3
Paying attention to particular details can significantly affect the security of a PC
File locking viruses are possible one of the most devastating types of malware due to their functionality. Once files are encrypted, only a unique key, which is generated during the infection process, can decipher them and allow users to re-access them. Unfortunately, this key is sent off to a Command & Control server that is controlled by the attackers, and they are not willing to giveaway it for free. While sums can vary, regular consumers are typically asked for lesser sums than corporations, where ransoms can reach hundreds of thousands of dollars.
Ransomware authors also came up with another devastating tactic (started by Maze ransomware gang) to make users and companies to pay ransoms. Before encrypting data, they copy everything located on the network/server/computer and place copies to their own server.[3] This allows the attackers to threaten victims by claiming that the data will be publicly exposed if the demands will not be met on time.
Thus, getting infected with this type of infection can cause various negative consequences, such as permanent data loss on private information exposure to malicious parties. To avoid such outcomes, it is crucial to take care of cybersecurity and not ignore industry experts' advice.[4]
First of all, the computer should be equipped with comprehensive security software that has real-time protection feature and can protect the whole network from intrusion. However, careful online behavior is just as important as security tools, so users should also:
- backup data on a regular basis;
- apply Windows and application updates as soon as new patches are released;
- never download software crackers or pirated program installers;
- employ VPN for RDP connections and limit the access to individuals who actually need it;
- use secure passwords for Remote Desktop connections;
- never reuse passwords for different accounts;
- do not click on random links on social media or other platforms;
- never allow spam email attachment to run macro function;
- scan unknown files with anti-malware software or online scanning services like Virus Total.
Eliminate the threat by removing all Paymen45 ransomware virus related files
As previously mentioned, some crypto-malware might erase themselves after the file encryption process, so Paymen45 ransomware removal might not be necessary. However, since there might be other payloads installed on your system (ransomware is sometimes distributed with info-stealers like AZORult), you should still perform a full system scan with a powerful anti-malware program. While we recommend using SpyHunter 5Combo Cleaner or Malwarebytes, there are several other security tools that could also help you with the process.
However, you should not remove the malicious virus before you back up all the files that were encrypted, along with the Windows registry database. If you do not perform these backups, malware might reinstall itself even after its termination in some cases.
In case the Paymen45 virus is tampering with your security software, you can access Safe Mode with Networking, and perform the scan from there. After that, you can proceed with data recovery methods we provide below (note that there is no guarantee that any of them will work, but you should try them out regardless).
Getting rid of Paymen45 virus. Follow these steps
Manual removal using Safe Mode
If malware is interfering with your security software, go to Safe Mode with Networking as explained below:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Paymen45 using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Paymen45. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Paymen45 from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Paymen45, you can use several methods to restore them:
Make use of Data Recovery Pro
Data recovery software cannot decrypt files that were affected by ransomware. Instead, it tries to extract working copies from within the hard drive. However, the more the infected computer is used after the infection, the less chances there are for such software to successfully retrieve data.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Paymen45 ransomware;
- Restore them.
Windows Previous Versions Feature might be useful to some users
Windows Previous Versions Feature is a built-in method that can help some users to recover files one-by-one.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer might work for you
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryption tool is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Paymen45 and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Vulnerability (computing). Wikipedia. The free encyclopedia.
- ^ 0d0d2e77dd103a8e6078dc957ed79f14d41326deee8bd2de3646840e179f9242. Virus Total. File and URL analysis.
- ^ Tristan De Souza. Ransomware operators now publicly leaking victim data. Cyjax. Search Results Web result with site links Threat Intelligence and Incident Response Services.
- ^ Lesvirus. Lesvirus. Cybersecurity news and malware insights.





















