CoinImp virus (Virus Removal Instructions) - Free Guide
CoinImp virus Removal Guide
What is CoinImp virus?
CoinImp is a JavaScript miner, which uses the CPU power of website visitors’ PCs to mine Monero coins
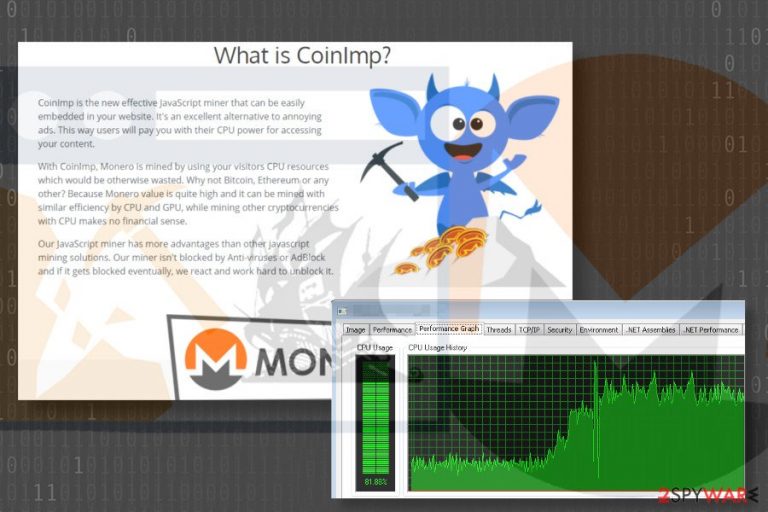
CoinImp is one of the newest digital currency mining[1] services developed and maintained by ABC Hosting LTD. Although it is primarily oriented to experienced webmasters who own websites with the large influx of visitors, all volunteers can try it out. The service allows Internet users to mine XMR or Monero[2] coins by embedding a JavaScript miner into the preferable website. The script then uses visitors’ CPU power to earn Monero coin fractions.
| Name | CoinImp |
| Type | Malware |
| Sub-type | Cryptocurrency miner |
| Cryptocurrency mined | Monero |
| Symptoms | High CPU usage, system's sluggishness, unresponsiveness, freezes, crashes, web browser's redirects to fake websites |
| Distribution | Hacked websites, bundling, PUPs |
| Similar malware | Coinhive Miner, RubyMiner, Minergate virus, Monero Miner, etc. |
| Removal | To immunize CoinImp Miner from the system specialists recommend using professional anti-malware tools. FortectIntego is a reliable tool for this task. |
If used properly, CoinImp miner is not malicious in any sense. Contrary, digital currency specialists point out that this service is noteworthy due to the lowest fee (1%) in the market, the usage of Referral Program, the simplicity of API key, 24/7 customer service, and other features.
Nevertheless, many people refer to this website miner as CoinImp virus. According to its developer, at the moment of writing, the original version of this JavaScript miner is not included into the database of AV engines and is not recognized by adblock utilities since its inoffensive. However, hackers might try to misuse CoinImp Monero miner illegally by injecting it into legal websites without getting permission for that.
Stealthy installation of JavaScript miner[3] severely violates both website visitor’s and webmaster’s rights. Although usage of CoinImp on the site provides ad-free web browsing experience, websites hijacked for cryptocurrency mining utilize the resources (CPU) of the visitor’s PC. Consequently, more extended hours spend on the site embedded with the rogue crypto miner with CoinImp features can result in severe system’s slowdowns, crashes, freezes, unresponsiveness, and similar abnormal behavior.
CoinImp Miner is allowed users to customize the usage of visitor’s CPU resources. Conscientious users of the server do not tend to disable the limited resource usage. In the meantime, hackers opt for disabling all limits to utilize 100% of CPU. High resource consumption, especially on older devices with older fans, can lead to severe system’s crash, data loss, and hardware problems.

To maximize the earnings, hackers are also known for creating fake websites and embed CoinImp JavaScript code on them. Additionally, such sites can be supplemented with malicious scripts which lock the website and do not allow the visitor to leave it. The only way to exit a crypto-hijacked webpage is to quit-force the web browser.
Although the website embedded with the CoinImp virus should stop sucking up CPU, the standard practice shows that it might continue its job by displaying a hidden pop-up under the window on Windows startup.
If you are satisfied with the service and does not spot its associations with untrustworthy parties and malware, you are free to use it as much as you want. However, to prevent hackers from stealing your CPU resources and gaining illegal profit by rendering your PC useless after visiting particular websites for a longer time, NoVirus.uk[4] experts recommend you to remove CoinImp Miner from the system.
Although developers claim that the Monero miner evades anti-virus and adblock detection, try to remove CoinImp website miner with FortectIntego or another reputable security tool. If not added yet, it’s only a matter of time when it will be included in the most popular antivirus databases.
Digital currency miners use stealthy ways to infect PCs
This particular Monero miner is offered as a legitimate free service on the official website. Those who opt for using it has to register to the service and generate unique links via the app. However, if hackers misuse it for illegal Monero mining, the JavaScrip code can be injected stealthily via hacked websites, potentially unwanted programs (PUPs) or even as an independent app.
As we have already pointed out, crooks can hack legitimate websites or create rogue domains, which are embedded with JavaScript cryptocurrency miner by default. People can get redirected to such domains by clicking on related ads or links.
Tech-Support-Scam sites that pop-up in the form of a new tab and completely locks the screen are the best example to illustrate the illegal usage of cryptocurrency mining scripts. Such domains might warn the visitor about the virus, spyware, rogueware and another infection and urge him/her to contact certified technicians.
Potentially unwanted programs, like adware and browser hijacker, are yet another medium allowing crooks to drive visitors traffic to miner embedded web domains. These apps can hide in the system for a long time displaying dangerous ads and links among user’s search results. Usually, PC users start suspecting an unwanted program to be installed when the web browser starts generating such a high number of ads that it becomes difficult to browse.
More often than not, malicious cryptocurrency miners are spread in the form of independent apps. Although you can hardly find them as stand-alone installers, apps like CPU Miner or Coinhive can be found bundled with freeware and shareware.
Learn how to get rid of CoinImp Miner virus
Cryptocurrency miners do not manifest their presence. They do not the corrupt system in a remarkable way. However, if you are a heavy PC user, the symptoms of PC’s sluggishness and unresponsiveness should draw your attention. Besides, you should also notice an excessive number of ads within web browsers, which redirect to unusual, rogue or malicious domains all the time.
To check what is happening with the system, you should open Task Manager and verify what processes are currently running and how much CPU do they take. If CPU consumption exceeds 50%, we would recommend scanning the system with FortectIntego, SpyHunter 5Combo Cleaner, Malwarebytes or another antimalware for crypto miners or other malware.
If all prove points to the JavaScript miner, do not delay CoinImp removal as it may eventually render your PC useless.
Getting rid of CoinImp virus. Follow these steps
Manual removal using Safe Mode
If you cannot perform CoinImp removal because it blocks your antivirus, try to launch the tool when the system is booted with Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove CoinImp using System Restore
If the previous method did not help to remove CoinImp virus, try the following steps:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of CoinImp. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
How to prevent from getting malware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Catalin Cimpanu. Hackers Make Whopping $226K Installing Monero Miners on Oracle WebLogic Servers. BleepingComputer. Technical support site .
- ^ Here’s How Monero (XMR) Could Soon Be At $1,000. Global Coin Report. A news service focused on serving the Crypto Currency trading community.
- ^ Lily Hay Newman. Your browser could be mining cryptocurrency for a stranger. Wired. Online news site.
- ^ NoVirus. NoVirus. Spyware and virus news.







