CommonBusiness mac virus (Free Guide)
CommonBusiness mac virus Removal Guide
What is CommonBusiness mac virus?
CommonBusiness is a Mac virus that has adware and hijacking capabilities
CommonBusiness is a potentially unwanted program (PUP)[1] with hijacking and adware[2] features. The homepage, new tab address, and search engine can all be changed from the default browser options. Additionally, it has the ability to create and insert commercial material including pop-up ads, banners, surveys, and links that could lead users to dangerous websites.
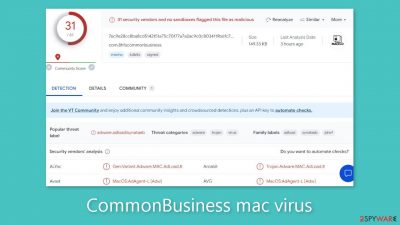
This particular PUP is a member of the Adload malware family, designed specifically to target Mac machines. Notably, this strain of adware exhibits a higher level of aggressiveness when compared to its counterparts targeting Windows systems. It can autonomously download PUPs and malware without the user's awareness.
Surprisingly, the Mac malware has the ability to trick Apple's XProtect security program. Because of this, users usually only become aware of it after it has already established itself in their system. By this time, the malicious program has probably managed to get authorization to gather user information and make changes to the operating system as well as web browsers.
The “Applications” folder is where users can find the Mac malware. Adload's multiple adware iterations, such as BasicTransaction, ElementForce, and EfficientRecord, have all been discussed previously. It's interesting that these variations all have the same icon, which is a magnifying glass against a green, teal, or grey background.
It's important to remember, though, that getting rid of CommonBusiness might be difficult. It disguises its malicious files as common system files and spreads them throughout the system. Additionally, it has the ability to recognize virus eradication attempts and quickly create new files in response. Therefore, it is best to avoid such intrusions in the first place to prevent problems.
| NAME | CommonBusiness |
| TYPE | Adware, browser hijacker, mac virus |
| MALWARE FAMILY | Adload |
| SYMPTOMS | Different homepage and new tab addresses; redirects to some other search engine and shady websites; decrease in performance |
| DISTRIBUTION | Fake software updates, deceptive ads, installing programs from torrent sites |
| DANGERS | Altered search results can lead to dangerous websites; pop-up ads might be promoting scams; the virus can install other PUPs or even malware in the background |
| ELIMINATION | Eliminating this Mac virus manually can be quite complicated if you do not have prior experience. The easiest and most effective way would be to open a professional security tool and scan your system to delete every related file |
| FURTHER STEPS | FortectIntego should be used to completely wipe out any data left and fix the remaining damage |
Distribution methods
Fake Flash Player upgrades or installations are one of the most common sources of Adload infestations, including CommonBusiness. Social engineering techniques are used by crooks to trick people into thinking that their Flash Player needs to be updated. To provide the idea that failing to install the most recent version may prevent access to multimedia content, they use deceptive notifications.
It's worth noting that many individuals remain unaware that Flash Player was discontinued in 2020 and replaced by HTML5. Should you encounter any website asserting otherwise, it is advisable to promptly exit. Another critical point of awareness is the risk associated with torrent[3] websites and peer-to-peer file-sharing platforms. These platforms lack regulation, making them fertile grounds for malware proliferation. Consequently, it's impossible to ascertain whether the program you intend to install is safe or concealed as a Trojan or another form of malware.
The best course of action is to only go to websites you know and trust. Instead of using illegal sources, use official web stores and developer websites. Applications that are displayed in digital markets must pass strict evaluation procedures. However, it's still a good idea to do your own research, read reviews, evaluate ratings, and take the user base into account.
Maintaining an updated operating system and software is also crucial. To spread their harmful software, hackers may take use of software flaws. Software developers regularly publish security patches to prevent this. As a result, timely upgrades are essential to ensuring security.

Removal of CommonBusiness mac virus
If you don't know what you're doing and what kinds of files need to be deleted, you shouldn't attempt to do this yourself. .plist is the extension for a standard settings file, commonly referred to as a “properties file,” used by macOS programs. For many programs, it contains attributes and setup settings. Additionally, the software makes use of numerous persistence strategies and scatters numerous files throughout the system, making browser extension and application removal challenging.
To keep your mind at peace, we recommend using professional anti-malware tools SpyHunter 5Combo Cleaner or Malwarebytes, which can detect unwanted programs and eradicate them. You also do not know if the virus installed any additional malicious programs, so this is the safest way to ensure the system is clean.
If you still want to try and delete it manually, proceed with these steps:
- Open Applications folder
- Select Utilities
- Double-click Activity Monitor
- Here, look for suspicious processes related to adware and use Force Quit command to shut them down
- Go back to the Applications folder
- Find CommonBusiness in the list and move it to Trash.
If you are unable to shut down the related processes or can't move the app to Trash, you should look for malicious profiles and login items:
- Go to Preferences and select Accounts
- Click Login items and delete everything suspicious
- Next, pick System Preferences > Users & Groups
- Find Profiles and remove unwanted profiles from the list.
There are likely to be more .plist files hiding in the following locations – delete them all:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
The manual elimination process might not always result in full virus removal. Therefore, we still strongly suggest you perform a scan with security software.
Remove the browser extension
CommonBusiness also introduces a browser extension that initiates a range of undesirable activities. This extension potentially gathers sensitive information and transmits it to tracking servers. Among the data that could be exposed are the IP address, username, macOS version, browser versions, computer ID, contents of the “Applications” folder, a roster of agents, daemons, and system configuration profiles.
Once the hazardous files have been removed from your system, it is advisable to promptly uninstall this add-on. You can automatically clear cookies and cache using FortectIntego, a helpful tool. Additionally, it can rectify damaged files and address system errors, leading to an enhancement in your machine's performance.
If you prefer doing this yourself without additional help, here are the instructions. You will find guides for Google Chrome and Mozilla Firefox at the bottom of this article:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Cookies and website data:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
The simplest and quickest solution to this is completely resetting Safari:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.
![Reset Safari Reset Safari]()
Getting rid of CommonBusiness mac virus. Follow these steps
Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Chris Hoffman. PUPs Explained: What is a “Potentially Unwanted Program”?. Howtogeek. Technology Magazine.
- ^ Lucian Constantin. What is adware? How it works and how to protect against it. Csoonline. Home Security.
- ^ Brad Haddin. 4 risks of using torrents. Creative. Tech Blog.











